Integrating a vCISO with Your IT Team
How Virtual Security Leadership Strengthens (Not Replaces) Your Internal IT & MSP
One of the biggest concerns companies have before hiring a vCISO is this:
“Will they step on our IT team’s toes?”
It’s a fair question.
Your internal IT staff is already stretched. Your MSP handles infrastructure. Your developers are shipping fast.
The last thing you want is tension, confusion, or duplicate work.
A strong vCISO does not replace IT.
A strong vCISO makes IT stronger.
When integrated correctly, the relationship becomes one of the most powerful security upgrades an organization can make.
First, Let’s Clarify Roles
Most security confusion comes from unclear responsibility. Here’s the difference:
| Role | Primary Focus |
|---|---|
| IT Team | Keep systems running |
| MSP | Maintain infrastructure & support |
| vCISO | Lead security strategy, governance, and risk oversight |
IT executes. The MSP supports. The vCISO leads and aligns.
This distinction prevents friction.
Why IT Alone Shouldn’t Carry Security Strategy
Your IT manager is likely responsible for:
• User onboarding/offboarding
• Device management
• Cloud administration
• Vendor tickets
• Backup checks
• Firewall and endpoint upkeep
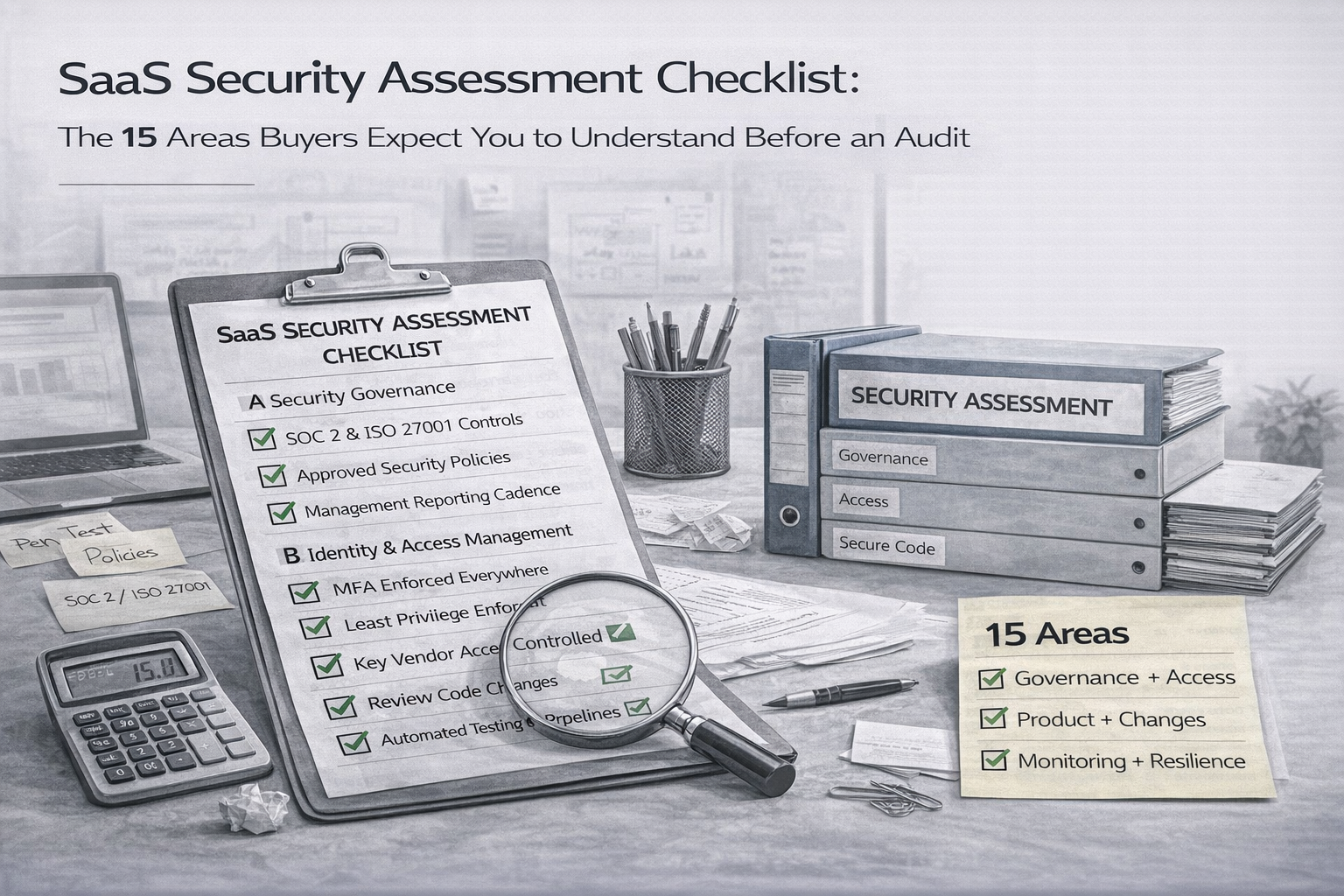
Security leadership requires a different focus:
• Risk management oversight
• Compliance alignment (ISO 27001, SOC 2)
• Policy governance and control ownership
• Executive reporting and board communication
• Incident readiness planning
• Vendor security evaluation
Not more technical. More strategic.
The Wrong Way to Integrate a vCISO
Here’s where things go wrong:
• The vCISO bypasses IT and speaks only to leadership
• IT feels audited instead of supported
• MSP responsibilities aren’t defined
• Security initiatives are imposed, not aligned
• Nobody owns follow-through
This creates resistance. And security programs fail quietly.
The Right Way: A Collaborative Model
1️⃣ Establish Clear Responsibility Boundaries
Define who owns implementation, monitoring, and reporting and who approves risk decisions.
Example:
• IT implements MFA and patches systems
• MSP monitors infrastructure alerts
• vCISO defines policy, reviews effectiveness, and reports risk posture
2️⃣ Make the vCISO a Strategic Advisor to IT
The vCISO should help IT prioritize work based on risk and business impact not pressure.
Instead of: “Why haven’t you fixed this?”
It becomes: “Here’s how we prioritize this based on risk and business impact.”
That change in tone is what makes collaboration work.
3️⃣ Build a Governance Rhythm
Successful collaboration requires cadence.
• Monthly security governance meeting
• Quarterly risk review
• Regular cloud configuration review
• Annual internal audit support
No surprises. No last-minute audit panic.
A Real-World Example
A 75-person Canadian SaaS company engaged a vCISO. Their IT manager was skeptical.
He thought: “This person will just add paperwork.”
Instead, the vCISO:
• Mapped security tasks into a structured roadmap
• Automated recurring access reviews
• Reduced spreadsheet tracking
• Built executive dashboards
• Took audit prep off IT’s plate
“For the first time, security feels organized instead of chaotic.”
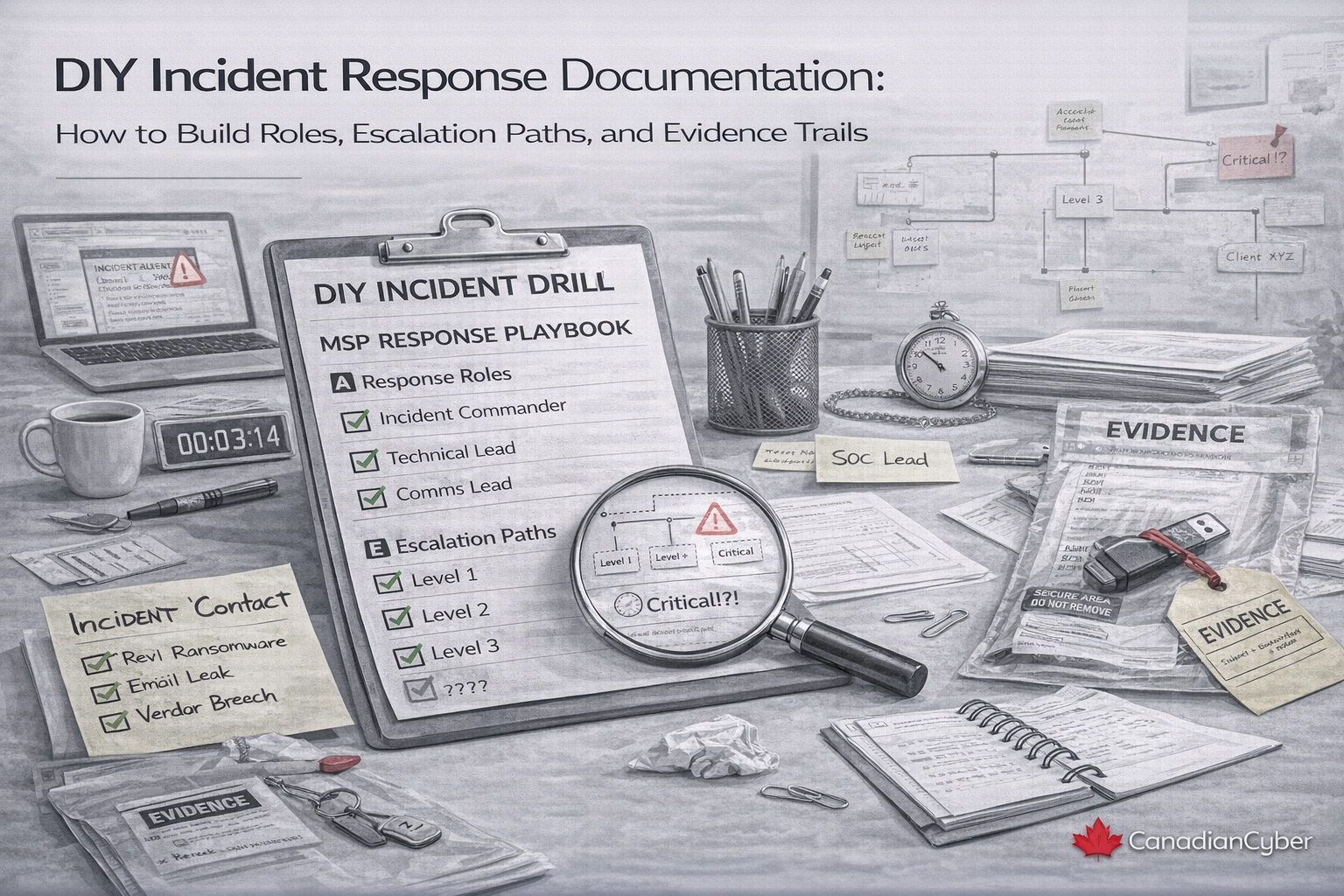
How a vCISO Supports MSP Relationships
MSPs focus on availability and support not governance. A vCISO ensures:
• Security clauses embedded in MSP contracts
• Monitoring responsibilities defined clearly
• Escalation paths documented
• Compliance evidence captured continuously
• SLAs aligned with risk tolerance
Without this oversight, critical assumptions go undocumented. And auditors notice.
The Hidden Benefit: Protecting Your IT Team
When incidents happen, leadership asks: who approved this risk, and where’s the documentation?
With a vCISO, risk decisions are documented, executive approvals are recorded, and governance is defensible.
Accountability becomes shared not dumped on IT.
Signs Your vCISO Integration Is Working
• IT tasks align with documented risk priorities
• No duplicate work is happening
• Audit evidence is organized continuously
• Security reviews happen on schedule
• Leadership understands risk in business terms
How Canadian Cyber Integrates vCISO with IT Teams
Canadian Cyber’s vCISO model is built around collaboration. We:
• Work directly with IT and MSPs
• Define clear responsibility (RACI) models
• Align controls to ISO 27001 and SOC 2 requirements
• Implement governance structures inside Microsoft 365
• Use SharePoint-based ISMS platforms to centralize documentation
• Provide executive-ready reporting and audit readiness support
We don’t replace your IT team. We amplify it.
Get a clear integration plan that reduces friction, defines roles, and improves audit readiness.
The Strategic Question
Is your IT team leading security strategy or just reacting to issues?
If they’re buried in operational tickets, they don’t have time for governance. A vCISO fills that gap without friction or politics.
Ready to Integrate Security Leadership Smoothly?
Security leadership should feel structured not disruptive. Let’s map roles, cadence, and responsibilities in 15 minutes.
Stay Connected With Canadian Cyber
Follow us for vCISO insights, ISO 27001 readiness tips, and cybersecurity leadership guidance: