Why SharePoint is a strong home for incident response
SharePoint works well for incident response because it handles several things IR programs need constantly: one source of truth, version control, permissions, structured records, and traceability.
| SharePoint strength |
Why it matters for IR |
| document libraries |
good for controlled runbooks, templates, and communications drafts |
| version history |
prevents confusion about which runbook is current |
| permissions |
lets you share the right content with responders, leaders, auditors, or privacy teams |
| lists |
great for incidents, decisions, actions, and lessons learned |
| auditability |
helps prove who changed what, when, and why |
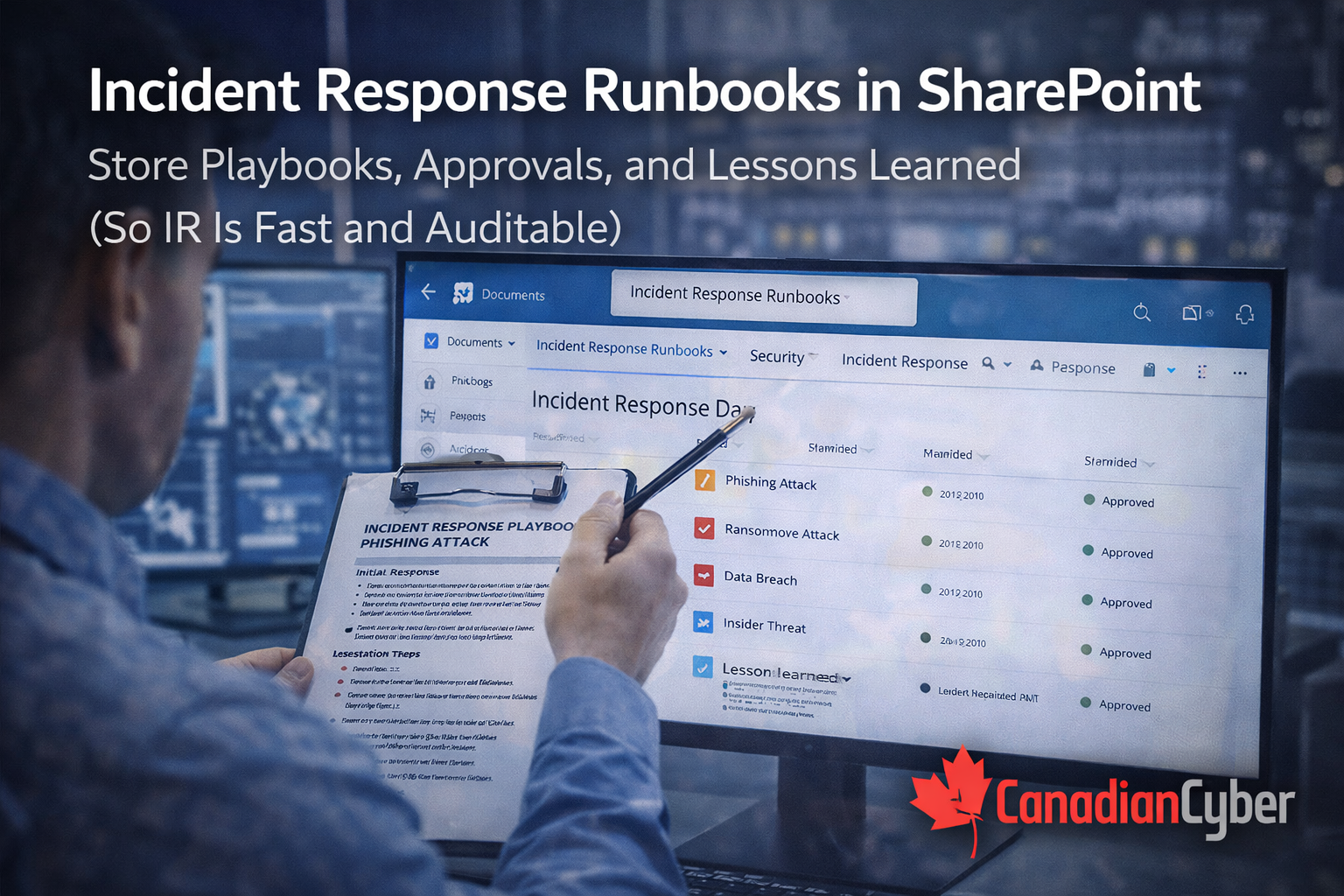
The SharePoint IR model that works
Keep the operating model simple. Think in four components:
1) Runbook Library
The playbooks responders actually use.
2) Incident Register
The record of what happened and when.
3) Approvals & Decisions
The “who authorized this” trail.
4) Lessons Learned
The improvement loop through PIRs and actions.
If you build these four well,
your IR program becomes much faster to run and much easier to audit.
1) Runbook Library: store playbooks like controlled procedures
Create a document library called Incident Response Runbooks. This should hold scenario-based runbooks that are short, current, and usable under pressure.
Typical runbooks to include
- ransomware containment
- business email compromise
- privileged account compromise
- cloud credential leak
- data exfiltration or suspicious bulk export
- SaaS breach notification workflow
- vendor incident response
- lost or stolen device with sensitive access
- DDoS or availability incident
- malware on server or workstation
- insider data misuse, if relevant
Recommended runbook format
- trigger conditions
- severity level
- roles involved
- containment steps for the first 30–60 minutes
- evidence preservation actions
- eradication and recovery steps
- decision points and escalation triggers
- customer or regulator considerations
- post-incident steps and PIR link
Settings that make this audit-friendly
- enable version history
- require approval for publishing approved runbooks
- add metadata: runbook type, owner, last reviewed, next review, status
2) Incident Register: a SharePoint list that becomes your timeline
Create a SharePoint list called Incident Register. This becomes the structured record of what happened, what was affected, who responded, and where the linked evidence lives.
| Recommended field |
Purpose |
| Incident ID |
consistent tracking and folder naming |
| date and time detected |
timeline anchor |
| detected by |
tool or human source |
| severity and status |
current response state |
| affected systems |
technical scope |
| data involved / customer impact |
business and privacy impact |
| Incident Commander |
named owner of the response |
| links to runbook, evidence, approvals, PIR, and actions |
connects the incident record to the full response trail |
Why this matters:
in audits and investigations, you need a clean sequence of what happened, when, who decided, what was done, and what changed.
If your team still reconstructs incident timelines from memory, chats, and screenshots after the fact, the Incident Register is the first thing to fix.
3) Approvals and decisions: capture the authorized response trail
Incidents involve high-stakes decisions: disabling accounts, taking systems offline, notifying customers, engaging forensics, invoking insurance, or approving emergency services. Those decisions need a record beyond chat messages.
Useful approval patterns
- Teams Approvals for key decisions
- a SharePoint Decision Log list
- signed approval PDF for sensitive actions
- saved email approval in the incident evidence folder
- Decision ID
- Incident ID
- Decision type
- Approver name and role
- Time of decision
- Short summary
- Conditions, if any
- Evidence link
Why auditors like this:
it shows governance and authorization, not improvisation and memory.
4) Evidence folder structure: one place to store what you’ll need later
Create a library called Incident Evidence and use a consistent folder structure so every incident has a single evidence home.
Suggested structure
Incident Evidence /
IR-2026-001 /
IR-2026-002 /
Inside each incident folder, store screenshots or exports, log references, approvals, comms drafts, forensic files, PIR notes, and corrective action references.
Metadata to add
- Incident ID
- Incident type
- Severity
- Evidence type
Important handling rule
Keep sensitive content access-restricted by default, especially logs, forensic outputs, and anything that could expose customer or employee data.
Lessons learned: turn “we should fix that” into a closed loop
Strong IR programs are not judged by having zero incidents. They are judged by how they respond and whether they improve afterward.
Post-Incident Review library and template
A good PIR should include
- what happened
- impact
- root cause
- what worked well
- what failed or slowed response
- corrective and preventive actions
- owners and due dates
- verification method
Corrective action linkage
PIRs should create actions in a Corrective Action Register, not just recommendations in a document.
Corrective Action Register fields
- owner
- due date
- evidence required to close
- effectiveness check
The auditor view approach
During ISO 27001 or SOC 2 audits, you do not want to expose raw chat logs, sensitive forensic material, customer PII, or unnecessary security tool detail. A curated auditor view solves that.
Good contents for an Auditor View
- IR policy and approved runbook list
- one tabletop exercise record
- one redacted incident sample if applicable
- PIR summary with corrective action closure evidence
- proof of incident logging process from the Incident Register
The 7 SharePoint views that make IR usable
Saved views make the system operational. Without them, the site becomes storage. With them, it becomes a dashboard.
Open Incidents
Status is not closed.
High Severity Incidents
Rapid view of critical activity.
Incidents This Quarter
Useful for reporting and audits.
PIRs Due
Find closed incidents missing PIR completion.
Corrective Actions Overdue
Stops “lessons learned” from going stale.
Incidents by Type
Group ransomware, BEC, malware, and more.
Lessons Learned Themes
Group PIR action items by theme so recurring weaknesses become obvious.
Common mistakes and how to avoid them
- Runbooks exist but are not reviewed → add review dates and reminders
- Approvals happen in chat only → log decisions or save approval artifacts
- Evidence is unstructured → use the incident evidence folder pattern every time
- PIRs are skipped → make PIR completion part of incident closure
- Lessons learned do not become actions → link PIRs to corrective actions with owners and due dates
Next steps
If your incident response content is scattered across email, Teams, PDFs, and random folders, the fix is not more documents. The fix is a cleaner operating structure.
Final takeaway
SharePoint is not a replacement for detection tooling or forensic platforms. But it is an excellent place to make incident response structured, repeatable, and auditable.
When runbooks are current, incidents are logged in a structured register, approvals are linked, evidence is stored consistently, and PIRs produce tracked actions, response gets faster and audit pain drops sharply.
In one line
The best IR SharePoint setup does not just store documents. It stores how your team responds, decides, proves, and improves.
Follow Canadian Cyber
Practical cybersecurity + compliance guidance: