The goal of an ISMS handover
A successful handover should do more than transfer files. It should preserve the operating logic of the ISMS so recurring controls, evidence, and decision-making continue without guesswork.
Continuity
Recurring controls still happen on time.
Retrievability
Anyone can find evidence in minutes, not hours.
Decision clarity
Risk acceptances, scope decisions, and priorities are documented.
Simple rule:
if your handover does not achieve these three outcomes, it is not complete.
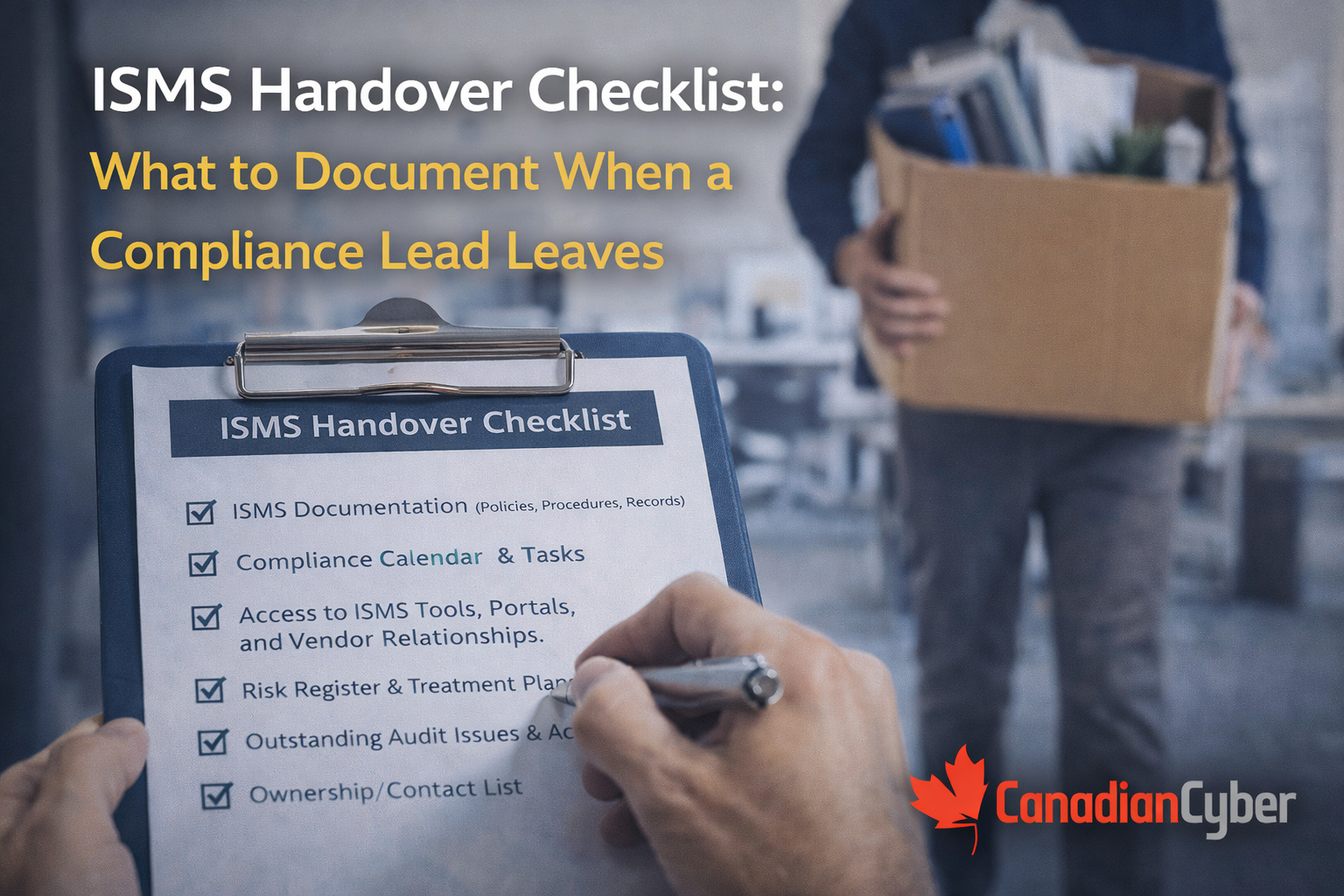
The ISMS Handover Checklist
1) ISMS at-a-glance one pager
Start with a single page that gives the next owner, leadership, and auditors an immediate orientation. This is usually the most valuable page in the whole package.
Include:
- ISMS scope: what is in and out
- standards and frameworks in play
- audit status and next key dates
- top 5 current risks
- top 5 open corrective actions
- evidence location and top links
- key internal and external contacts
2) Scope and system boundary decisions
Scope logic is often tribal knowledge. That makes it one of the most dangerous things to lose when a compliance lead leaves.
Document the decisions behind the scope
- in-scope systems and environments
- out-of-scope systems and why
- data types in scope
- tenant model and isolation assumptions if multi-tenant
- cloud responsibility boundaries
- scope carve-outs and compensating controls
Include a simple architecture diagram and a system inventory link.
3) Control register and ownership map
The next owner should not have to reverse-engineer who runs what. Control ownership must be visible and current.
| What to provide |
Why it matters |
| control register link or snapshot |
lets the next owner see the whole program quickly |
| owner and backup owner for every critical control |
prevents silent failure when one person is absent |
| control frequency and evidence produced |
tells the team what should exist and when |
| evidence storage location |
connects the control map to actual proof |
4) Compliance calendar
This is what stops drift. Without a visible schedule, the ISMS usually does not fail immediately it simply starts missing important dates one by one.
Include a 12-month calendar covering:
- internal audit schedule
- management review dates
- external audit milestones
- quarterly access reviews
- critical vendor review dates
- incident tabletop date
- DR and restore testing dates
- policy review deadlines
- monthly evidence review cadence
Add reminders, escalation paths, and the list of who receives those reminders.
If recurring reviews have no reminders, no backup owners, or no obvious evidence location, your ISMS is probably more person-dependent than it looks.
5) Evidence map and where things live
This is the most common failure point after transition. If the evidence structure is not obvious, audits and questionnaires slow down immediately.
Provide:
- SharePoint site map
- evidence folder structure by quarter or month
- naming conventions
- auditor view location if one exists
- tagging rules such as control ID, period, and owner
Minimum evidence links to include
- latest management review minutes
- latest internal audit report and findings tracker
- latest quarterly access review pack
- critical vendor review pack
- incident tabletop record
- backup and restore test evidence
- change management samples
6) Risk register and treatment plan status
The next owner needs both the current risk picture and the logic behind what is being treated now versus later.
Include:
- risk register link and latest snapshot
- top current risks and why they matter
- treatment plans with owners and due dates
- risks pending review in the next 30, 60, and 90 days
- risk scoring model and risk appetite statement if defined
7) Risk acceptances and exceptions
These are the hidden landmines. They often become findings after turnover because the exception logic existed only in one person’s memory.
Document every active exception with:
- reason for the exception
- expiry date
- compensating controls
- approver
- what needs to happen to close it
Be explicit about patch SLA exceptions, unsupported systems, vendor assurance gaps, logging gaps, and temporary admin access arrangements.
8) Corrective action register and open findings
Corrective actions often lose momentum immediately after turnover unless the status, owners, due dates, and closure evidence are obvious.
- corrective action register link
- all open findings with owners and due dates
- the evidence needed to close each item
- which items still need effectiveness verification
- which findings are repeat findings and what is being done about recurrence
9) Policies and procedures: what is current, what is due
A handover should make it obvious which policies are current, which are due, and how approvals and acknowledgements work.
Provide links to
- approved policy library
- procedure and runbook library
- drafts or policies in flight
Also document
- policies due for review in the next 90 days
- how approvals work
- where acknowledgements and training records live
10) Audit history and relationship notes
This section saves future pain. It prevents the next owner from re-litigating how evidence has been presented, what the auditor previously accepted, and what is still open for the next cycle.
- last audit results and open themes
- auditor preferences such as sampling style or evidence format
- agreed interpretations around scope or control evidence
- open questions flagged for the next cycle
11) Security questionnaire and trust asset library
If the ISMS supports sales, do not lose the assets that help deals move. These are often forgotten during transition even though the commercial impact is immediate.
- standard questionnaire response library
- trust package and assurance summaries
- subprocessor list location
- retention and deletion statement
- security contact process and NDA sharing workflow
12) Access and tooling inventory
The next owner cannot operate the ISMS if they cannot access the systems that run it. Make the tooling map explicit.
List the systems needed to run the ISMS
- GRC tool, if any
- SharePoint sites
- ticketing systems
- cloud consoles and logging tools
- identity admin portals
- vendor management systems
- training platform
- password vault or secret manager access process
Also include who has admin access, where credentials are managed, how access is requested, and any break-glass procedures.
The handover package deliverable
If you want the handover to be clean, assemble a single package rather than leaving the next owner to hunt through multiple folders and email threads.
A clean handover package should contain:
- ISMS at-a-glance one pager
- 12-month compliance calendar
- control register snapshot with owners
- risk register snapshot with top risks
- exceptions list with expiry dates
- corrective actions list with due dates
- evidence map with top evidence links
- audit history notes and next steps
If you can produce this package cleanly,
your ISMS is much less likely to be person-dependent.
Red flags that mean your ISMS is at risk right now
- evidence is stored in personal drives or email
- recurring reviews have no owners or reminders
- exceptions have no expiry dates
- the control register is not current
- only one person knows how to produce an audit pack
- questionnaire answers change depending on who replies
These are all solvable usually quickly when you treat the ISMS as an operating system rather than a set of documents.
Next steps
If you want to make your ISMS handover-proof, the goal is to preserve continuity before a transition becomes a control failure.
Final takeaway
The real risk in leadership transition is not just the temporary vacancy. It is the loss of operating memory where evidence lives, why scope decisions were made, which exceptions are active, and what reviews must still happen on time.
A strong ISMS handover makes that operating memory visible, retrievable, and reusable. That is what keeps ISO and SOC readiness alive when the person who carried the program is no longer there.
The best handover is the one that makes your ISMS operate like a system, not like one person’s memory.
Follow Canadian Cyber
Practical cybersecurity + compliance guidance: