Master your ISO 27001 risk assessment with our free template. Learn Clause 6.1 requirements, scoring methodology, and how to build a compliant risk register that auditors trust.
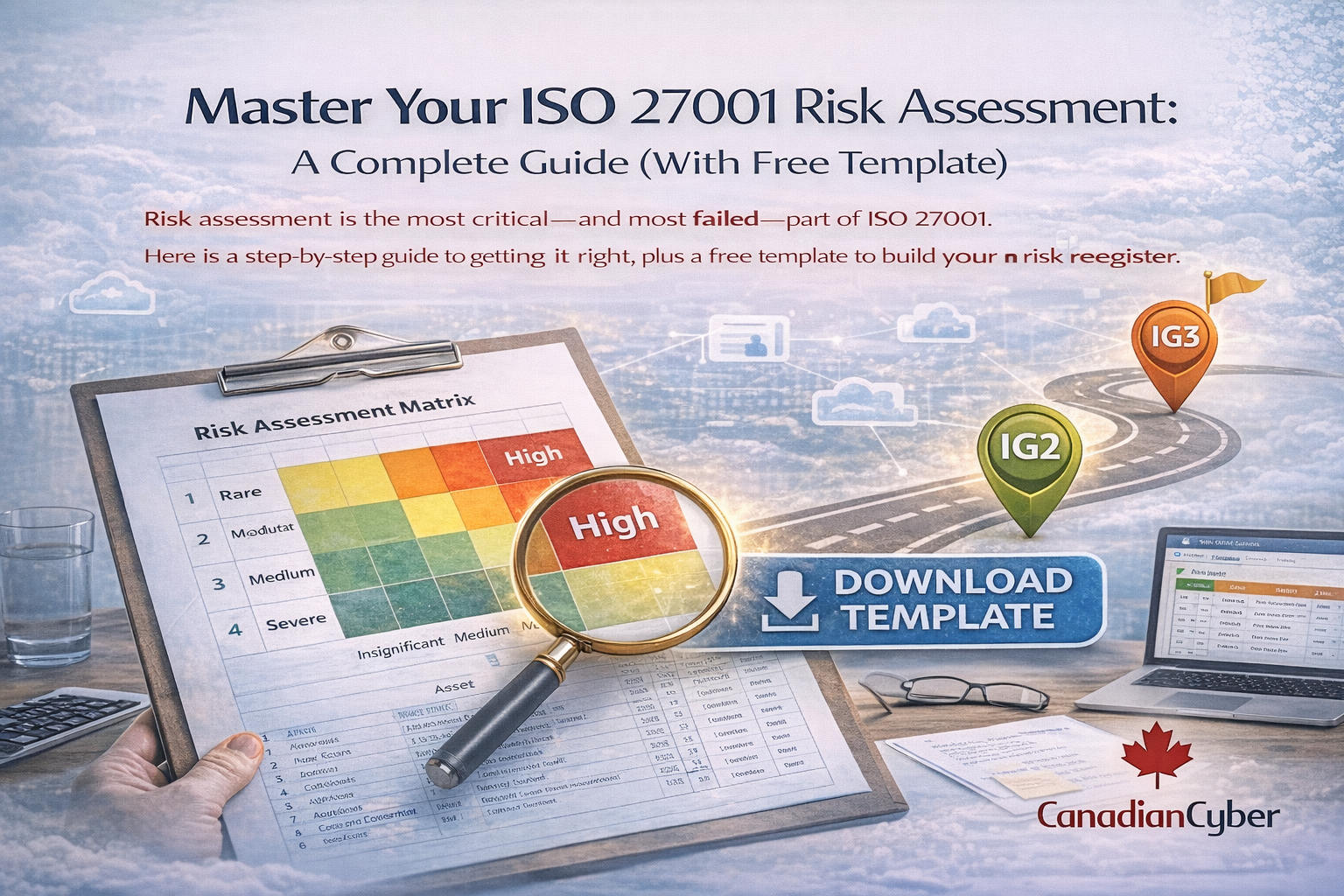
Risk assessment is the most critical and most failed part of ISO 27001. Here is a step-by-step guide to getting it right, plus a free template to build your risk register.
“Show me your risk assessment.”
It’s the first question every ISO 27001 auditor asks. And how you answer determines the entire trajectory of your audit.
Risk assessment isn’t just a checkbox. It’s the engine that drives your entire Information Security Management System (ISMS).
Every control you select, every policy you write, every investment you make all of it flows from how you identify, analyze, and evaluate risk.
Yet it’s also the most misunderstood and poorly executed part of ISO 27001. Common mistakes include:
That’s exactly why we created our free ISO 27001 Risk Assessment Template. It provides a structured framework to document, score, and manage risks in a way that satisfies auditors and improves your security posture.
| Section | What You’ll Learn |
|---|---|
| Understanding ISO 27001 Risk Assessment | What the standard actually requires (Clause 6.1) |
| The 5-Step Risk Assessment Process | A practical methodology you can implement today |
| Common Pitfalls to Avoid | Why most risk assessments fail audits |
| Using the Template | Step-by-step instructions for our free template |
| Beyond the Template | How to build a living risk management program |
Before diving into the template, clarify what ISO 27001 actually requires.
Clause 6.1 (Actions to Address Risks and Opportunities) mandates that your organization must:
| Requirement | What It Means |
|---|---|
| Establish risk assessment criteria | Define how you’ll score likelihood and impact |
| Ensure consistent, repeatable results | Your methodology must produce consistent scoring over time |
| Identify risks to CIA | Confidentiality, Integrity, Availability impacts must be considered |
| Analyze and evaluate risks | Score inherent risk and evaluate existing controls |
| Select treatment options | Modify, retain, avoid, or share risks |
| Produce a risk treatment plan | Document actions, owners, timelines, and controls |
| Obtain risk owner approval | Each risk must have accountable ownership and sign-off |
Key insight: ISO 27001 doesn’t prescribe one “correct” methodology. It requires that you have one and that you follow it consistently.
That’s exactly what the template helps you do.
Before identifying a single risk, document the rules of the game:
Pro tip: Keep it simple. A 4×4 matrix (Very Low → Very High) works well for most SMEs.
Create a manageable inventory of:
Don’t list every server or laptop. Group assets by type (customer data, identity infrastructure, public applications) to keep it practical.
For each scenario, score:
The template calculates inherent scores automatically so your scoring stays consistent and auditable.
This step is where many organizations lose the plot. Auditors want to see that you understand: what’s already in place and what risk remains.
A high inherent risk with strong controls may be acceptable. A medium inherent risk with weak controls often needs immediate action.
For risks above your appetite:
Important: Your Statement of Applicability (SoA) should flow directly from these treatment decisions.
If your SoA isn’t connected to risk, auditors will feel it immediately.
Build an audit-ready risk register without reinventing the wheel. This template includes scoring methodology, a risk register with calculated inherent/residual scores, a treatment tracker, and SoA mapping.
No email required. No sales call. Just a practical tool to help you succeed.
The template is designed to keep your methodology consistent, your fields complete, and your evidence defensible.
Here’s what’s inside and how to use it without overcomplicating the process.
| Sheet/Tab | Purpose |
|---|---|
| Instructions | How to use the template quickly and correctly |
| Methodology | Define scoring criteria and risk acceptance thresholds |
| Asset Inventory | List asset groups (keep it practical, not exhaustive) |
| Risk Register | Document risks with auto-calculated scoring |
| Treatment Plan | Track remediation actions with owners and dates |
| SoA Mapping | Link risks to Annex A controls |
| Dashboard | A quick view of risk posture and progress |
Pro tip: The template is a starting point not the finish line. For most SMEs, it’s enough for your first certification cycle.
When you’re ready to mature, you can move the same structure into a SharePoint-based ISMS with automation and dashboards.
| Pitfall | Why It’s Dangerous | The Fix |
|---|---|---|
| Stale risk register | Updated annually (if ever) → auditors see it as “paper compliance” | Schedule quarterly reviews and record outcomes |
| Inconsistent scoring | Process looks subjective and non-repeatable | Use dropdowns and defined criteria, not free text |
| Missing risk owners | “IT owns everything” → nothing gets closed | Assign named owners with deadlines and approvals |
| No control mapping | Can’t prove controls address risks → SoA looks detached | Link each treatment to relevant Annex A controls |
| Undocumented accepted risks | Leadership hasn’t approved residual exposure | Document acceptance decisions with signatures and rationale |
A spreadsheet no matter how good is still a snapshot. Mature organizations move toward continuous risk management.
| Maturity Level | Description |
|---|---|
| Level 1: Ad-hoc | No formal process; risks are in people’s heads |
| Level 2: Defined | Spreadsheet-based, updated periodically |
| Level 3: Managed | Automated workflows, quarterly reviews, leadership visibility |
| Level 4: Continuous | Real-time risk monitoring integrated into operations |
Our free template gets you to Level 2. When you’re ready for Level 3, consider:
Canadian Cyber’s SharePoint ISMS platform is built for this upgrade path turning risk management into a living system inside your Microsoft 365 tenant.
Ready to build your risk register? Get the template and start documenting risk in a way auditors love and leaders can use to make better decisions.
Need help tailoring your methodology or moving to an automated ISMS? We offer everything from a one-hour consult to vCISO-led risk governance.
Canadian Cyber helps Canadian organizations achieve ISO 27001 certification efficiently through practical tooling, clear guidance, and sustainable compliance programs.
Let’s build something secure together.
Follow us for practical insights on ISO 27001, risk management, and audit readiness: