Case Study: From Spreadsheets to ISO 27001 Certification in 6 Months
How a 50-person Canadian SaaS company became audit-ready without a security team by scoping smart, using templates, and building a repeatable ISMS system.
Note: This company is fictional but the journey is real. Every decision and obstacle below is drawn from what Canadian SMEs experience when enterprise customers require ISO 27001.
“We didn’t just get certified. We built a system.”
That’s how the CEO described it after certification.
And that sentence explains the difference between companies that pass one audit…
and companies that stay audit-ready year after year.
The Situation
Toronto-based SaaS company
• 50 employees
• ~$8M ARR
• No dedicated security team
• No formal ISMS
• Policies and evidence scattered across docs and spreadsheets
Then came the email that changed everything:
“We cannot proceed without ISO 27001 certification.”
A major enterprise deal was blocked.
The sales team had a window.
Timeline: 6 months not “when we start”… but from that day.
The Real Starting Point (What Most SMEs Look Like)
Security existed.
Documentation did not.
• Controls were practiced — but inconsistently
• Access was managed — but not reviewed formally
• Risks were understood — but not structured
• Security knowledge lived in people’s heads
For ISO 27001, undocumented equals non-existent.
The 5 Obstacles
• No formal ISMS
• No dedicated security team
• Skeptical leadership (cost + distraction concerns)
• Overwhelming scope (ISO 27001:2022 includes 93 controls)
• A hard six-month deadline
Most companies slow down here.
This one didn’t.
The 5 Decisions That Changed Everything
1) They assigned ownership
Not a full-time CISO.
A fractional compliance lead 20 hours per week who could drive structure, documentation, and momentum.
Why it worked:
ISO 27001 is mostly governance and process.
Without a dedicated driver, projects drift.
2) They scoped smart (and aggressively)
They did not certify the entire organization.
They scoped only what mattered to customer trust and audit requirements.
| In Scope | Out of Scope (for now) |
|---|---|
| Product development + engineering workflows | Sales and marketing tooling |
| AWS production environment | Finance systems |
| Customer data systems | Internal HR systems |
| Git repositories + incident response | Non-critical internal systems |
Result: Scope reduction cut workload by more than 50%.
They protected the deal first and planned to expand scope later.
3) They chose a platform over chaos
Instead of building everything manually in spreadsheets, they implemented a structured ISMS platform.
They needed:
• Policy templates
• Risk register with scoring
• Annex A control mapping
• Evidence repository
• Workflow automation
• Task reminders and ownership
With structure, ISO becomes manageable.
Without it, it becomes overwhelming.
4) They created a governance rhythm
• Weekly compliance sprints (execution + evidence)
• Monthly steering committee (executive decisions + risk)
• Quarterly management review (metrics + continuous improvement)
No guessing.
No drifting.
Just consistent execution.
5) They treated internal audit as a dress rehearsal
They hired an independent internal auditor before certification.
Internal audit outcome:
• 3 minor findings
• 0 major findings
• Closed in 2 weeks
The certification audit was smooth because the internal audit surfaced gaps early when fixes were still easy.
In 15 minutes, we’ll map your starting point, define your minimum viable ISMS scope, and outline the fastest path to certification.
👉 Book a 15-Minute ISO Readiness Call
Explore the ISMS SharePoint Platform
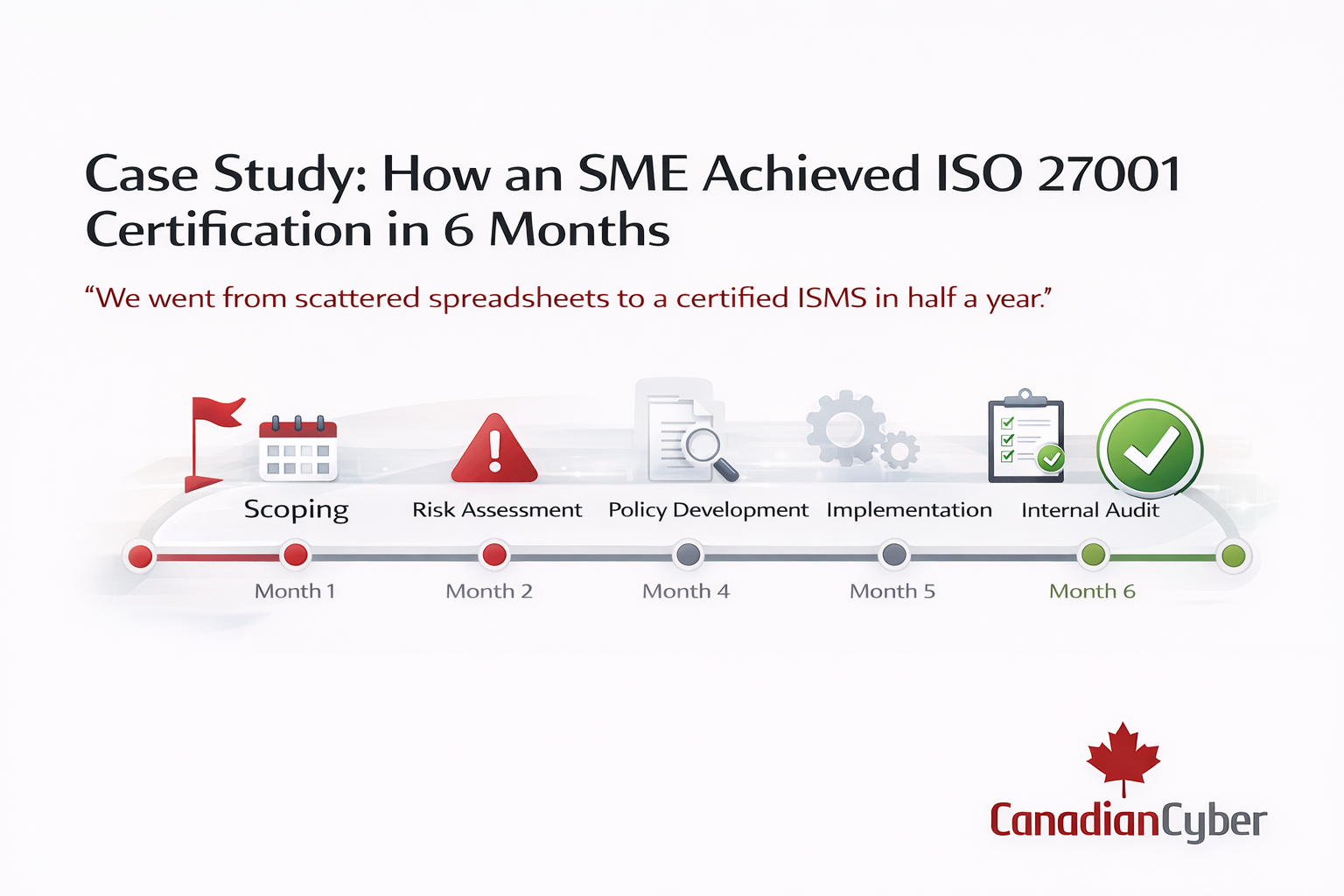
The 6-Month Timeline
| Month | Focus | Key Wins |
|---|---|---|
| Month 1 | Foundation | Scope, risk assessment, 12 policies, SoA drafted |
| Month 2 | Implementation | MFA, change mgmt, vendor risk, IR plan tested |
| Month 3 | Embedding | Training, asset inventory, logging & monitoring |
| Month 4 | Evidence & docs | Policy approvals, evidence folders, treatments |
| Month 5 | Internal audit | Independent audit, fixes done fast |
| Month 6 | Certification | Stage 1 + Stage 2 passed, certificate issued |
The Results
Before: Security questionnaires took 3–5 days, enterprise deals stalled, access reviews were inconsistent.
After: Questionnaires answered in <24 hours, the enterprise deal closed, ownership became clear, policy review hit 100%.
First deal post-certification: $450K ARR
Payback period: under 3 months
What Actually Made It Work
• Scoped aggressively
• Used templates (no “write from scratch” trap)
• Automated recurring tasks
• Assigned accountability early
• Used internal audit strategically not as a formality
ISO 27001 became a system not a checklist.
How Canadian Cyber Helps You Do This Faster
Everything they built manually can be deployed faster with the right foundation.
• 50+ ISO-aligned policy templates
• Pre-mapped Annex A controls + SoA structure
• Risk register with scoring logic
• Evidence folders with approval workflows and audit trails
• Reminders, tasks, and ownership tracking
Then we layer vCISO oversight, internal audits, and certification readiness support so you build a repeatable compliance engine, not a one-time project.
Ready to Turn ISO 27001 into a Growth Advantage?
In 15 minutes, we’ll tell you how close you are, what scope makes sense, and how fast you can get audit-ready.
Stay Connected With Canadian Cyber
Follow Canadian Cyber for ISO 27001 insights, audit readiness strategies, and compliance automation updates: