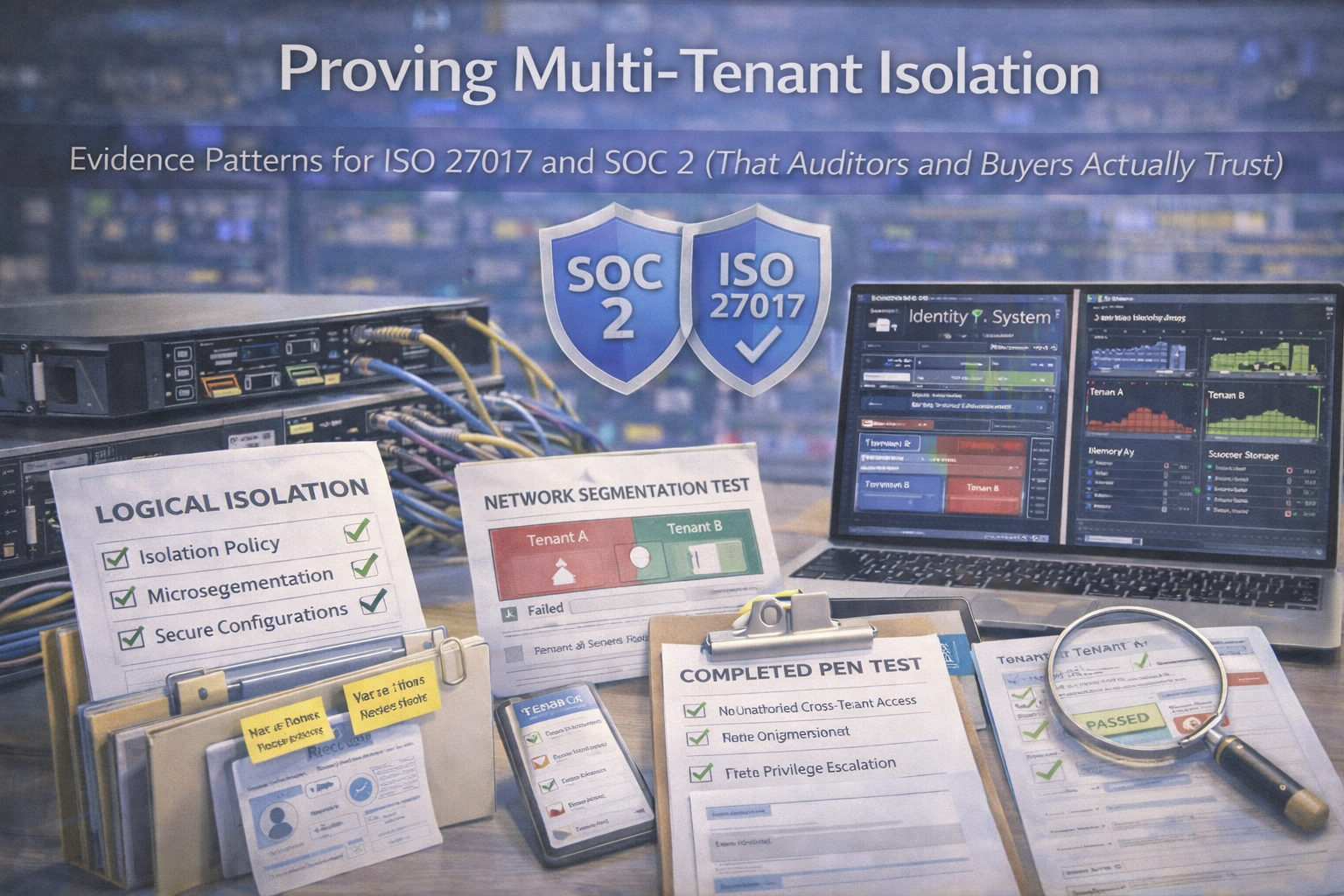
A practical guide explaining how SaaS companies prove multi-tenant isolation using architecture, authorization controls, testing, monitoring, and audit-ready evidence.
Multi-tenant isolation is one of those topics where everyone believes it’s true until an auditor or enterprise buyer asks:
“How do you prove one customer can’t see another customer’s data?”
Buyers and auditors focus on isolation because the failure mode is catastrophic: cross-customer exposure, regulatory notifications, breach reporting, and contract fallout. Unlike many controls, isolation isn’t proven by policy alone.
It’s proven by architecture + code + configuration + tests + logs + operating evidence.
Auditors want samples. Give them a clean, repeatable path that answers most questions without chaos.