Not legal advice.
Use this as an operational readiness guide alongside your legal and contract team.
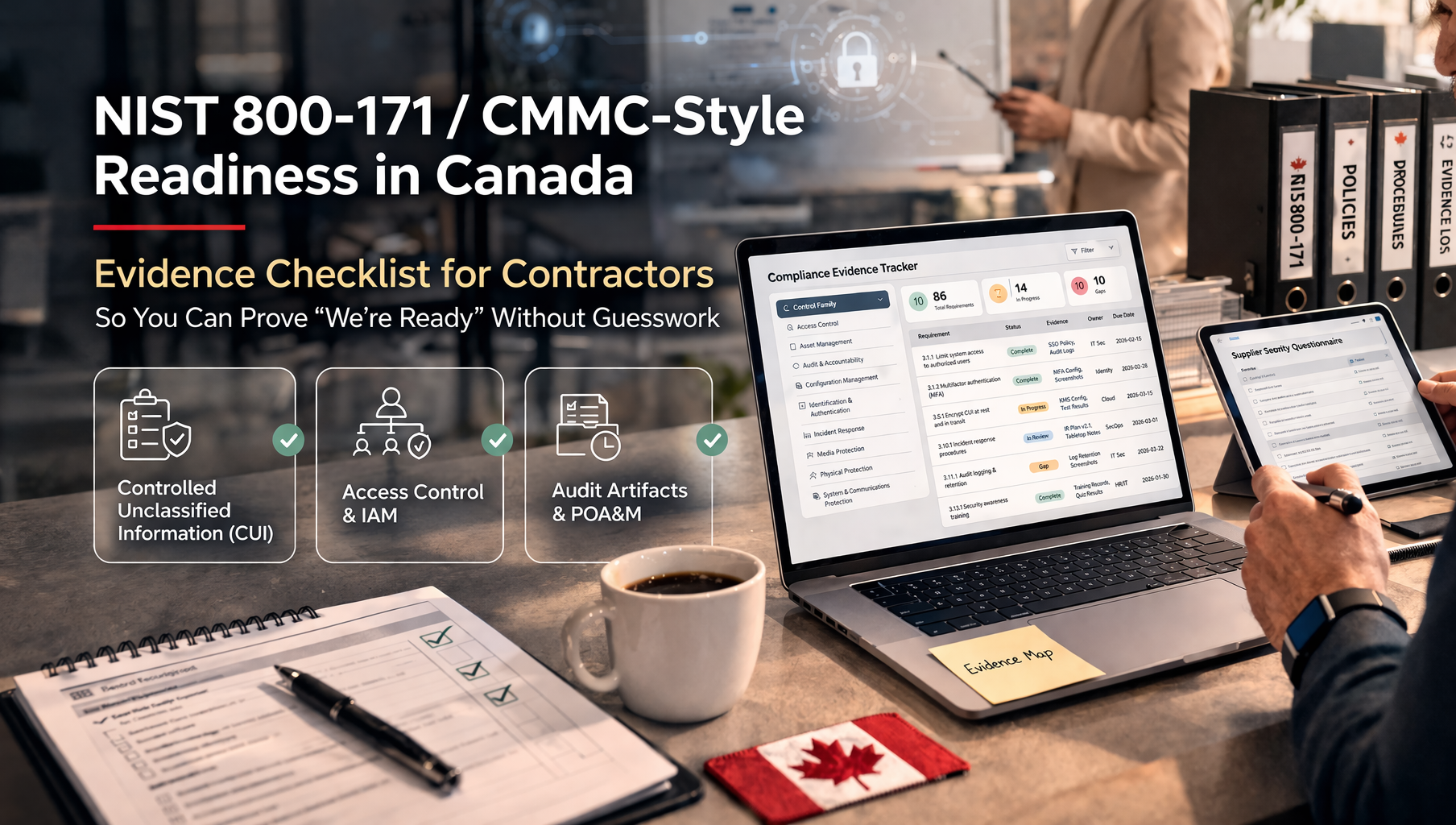
Why the goal is evidence readiness, not paper compliance
The versions and procurement mechanics matter, but what actually decides approvals is much simpler:
buyers trust what you can prove.
What teams often say
- We align to NIST.
- We follow secure practices.
- We take CMMC seriously.
What buyers actually approve
- Here’s how access is controlled.
- Here’s how we patch and verify.
- Here’s how we detect and respond.
- Here’s how we protect sensitive government or customer data.
Bottom line:
readiness becomes real the moment you can pull the evidence quickly, consistently, and without improvising.
Canada-specific context you should not ignore
Even when the commercial pressure starts with U.S. primes or defense-style requirements, Canadian contracting can introduce its own security expectations.
- Government of Canada contracting may trigger IT security requirements through the Contract Security Program when protected or classified information is handled electronically.
- Government environments often use structured control language and evidence expectations aligned to Canadian security control profiles.
- That means even if your driver is “NIST/CMMC-style,” Canadian buyers may still expect disciplined scope, control, and evidence language.
Translation:
your evidence model should be strong enough to satisfy both prime-contractor due diligence and Canadian public-sector style discipline.
The evidence checklist
Below is a practical “show me” checklist. If you can produce these artifacts cleanly, you are functionally much closer to NIST/CMMC-style readiness than most contractors.
1) Scope and data: prove what you’re protecting
- system boundary statement
- data handling statement for sensitive data types
- high-level data flow diagram
- asset inventory for endpoints, servers, cloud accounts, and key SaaS tools
Why it matters: without scope clarity, every assessment turns into endless expansion.
2) Identity and access: prove who can access what
This is one of the fastest sampling areas during assessments. Reviewers want to see least privilege, removal discipline, and real enforcement, not just account policies.
Evidence to have
- MFA enforcement proof
- privileged account list + quarterly review sign-off
- joiner / mover / leaver sample records
- RBAC model for key systems
- service account inventory, owners, and rotation approach
Auditor pattern
Expect reviewers to sample a handful of users and ask you to prove why they have access, whether it is appropriate, and whether stale access is removed on time.
3) Access control to environments: prove segmentation and boundaries
- network diagrams showing segmentation and remote access paths
- admin access path documentation such as VPN, jump box, restrictions, and logging
- firewall or security group review evidence
- cloud tenant guardrails and proof of enforcement
High-intent tip: if perfect segmentation does not exist yet, document compensating controls and a time-bound remediation path.
4) Configuration management: prove known-good baselines
- secure baseline standards for endpoints, servers, and cloud environments
- hardening evidence for a sample set of systems
- approved software list
- drift handling process
- links to related configuration change approvals
5) Patch and vulnerability governance: prove patched and verified
This is where many teams feel ready but cannot prove it. Reviewers want to see not just scanning and patching, but actual closure discipline.
| Evidence item |
What it proves |
| patch SLAs by severity |
you have defined response expectations |
| scan cadence + sample reports |
you actually identify issues on schedule |
| ticket trail from finding to remediation |
you can trace action and ownership |
| exception records with expiry |
you manage unavoidable gaps formally |
| verification proof such as rescan or version evidence |
you prove resolution, not just intention |
Common failure:
teams patch, but cannot prove verification. “Patched” is not the same thing as “resolved.”
6) Logging and monitoring: prove you can investigate
- logging standard that defines what is logged and what is intentionally excluded
- central log retention settings proof
- monthly or quarterly log review sign-offs
- 2–3 alert-to-ticket examples showing triage to closure
- privileged action logs for admin and security-relevant changes
Canadian procurement angle: auditability and retention discipline matter a lot in public-sector and regulated assessments.
7) Incident response: prove you’re ready, not hopeful
- IR plan with roles, escalation path, and customer notification approach
- tabletop exercise record from the last year
- evidence preservation steps
- post-incident review template with corrective action linkage
What primes want: not perfection—repeatability, clarity, and coordination.
8) Data protection: prove encryption and handling controls
Evidence to have
- encryption-in-transit statement
- encryption-at-rest settings proof
- key management model
- media and export controls
- approved secure file transfer methods
What reviewers are testing
Whether sensitive data is protected technically, whether keys are controlled, and whether data movement is restricted to approved, auditable channels.
9) Secure development and change management: prove authorized change
If you build or deploy software, this is not optional. Reviewers want traceability from request to approval to deployment to validation.
- PR review rules and branch protections
- CI/CD logs proving controlled deployment
- security review triggers for sensitive changes
- emergency change process with after-the-fact documentation
Auditor sampling: expect a few releases to be traced from request → approval → deploy → validation.
10) Vendor and supply chain: prove you’re not the weak link
- tiered vendor register
- annual review evidence for critical vendors
- contract clause checklist covering incident notice, deletion, and access controls
- subprocessor visibility for vendors touching sensitive client data
11) Training and personnel controls: prove people are part of the system
- security awareness completion records
- privileged or admin training evidence where applicable
- onboarding and offboarding checklists
- background screening policy where contractually required
12) Assessment artifacts: the readiness pack primes expect
Even when nobody names the documents explicitly, most reviewers want a pack that works like this:
System Security Plan style documentation
Your boundary, controls, and operating model.
Evidence index
A map of where proof lives.
POA&M style tracker
Open gaps, owners, due dates, and proof of closure.
This is how readiness becomes repeatable:
the pack lets you answer buyer questions without starting from zero every time.
The fastest way to implement this without bureaucracy
A practical vCISO approach is usually much simpler than teams expect:
- Build the evidence index first.
- Close the biggest deal-blocking gaps first: MFA, admin governance, logging review, patch verification.
- Create a monthly cadence for reviews and triage.
- Run micro-audits so the program stays continuously ready.
Next steps
If you’re a Canadian contractor and want to be CMMC-style ready without months of confusion, the fastest win is to make your evidence visible, structured, and current.
Final takeaway
NIST 800-171 / CMMC-style readiness for Canadian contractors is less about memorizing framework language and more about building an evidence-ready operating system. Buyers want proof that access is governed, changes are controlled, vulnerabilities are handled, incidents are managed, and sensitive data is protected consistently.
When you can produce that proof quickly with scope clarity, ownership, dates, and closure evidence you stop sounding “aspirational” and start sounding ready.
In one line
Contractors do not win trust by claiming alignment. They win trust by showing evidence on demand.
Follow Canadian Cyber
Practical cybersecurity + compliance guidance: