Most SharePoint ISMS setups fail audits due to poor structure. Learn how to build an audit-ready ISMS with proper evidence, ownership, and traceability.
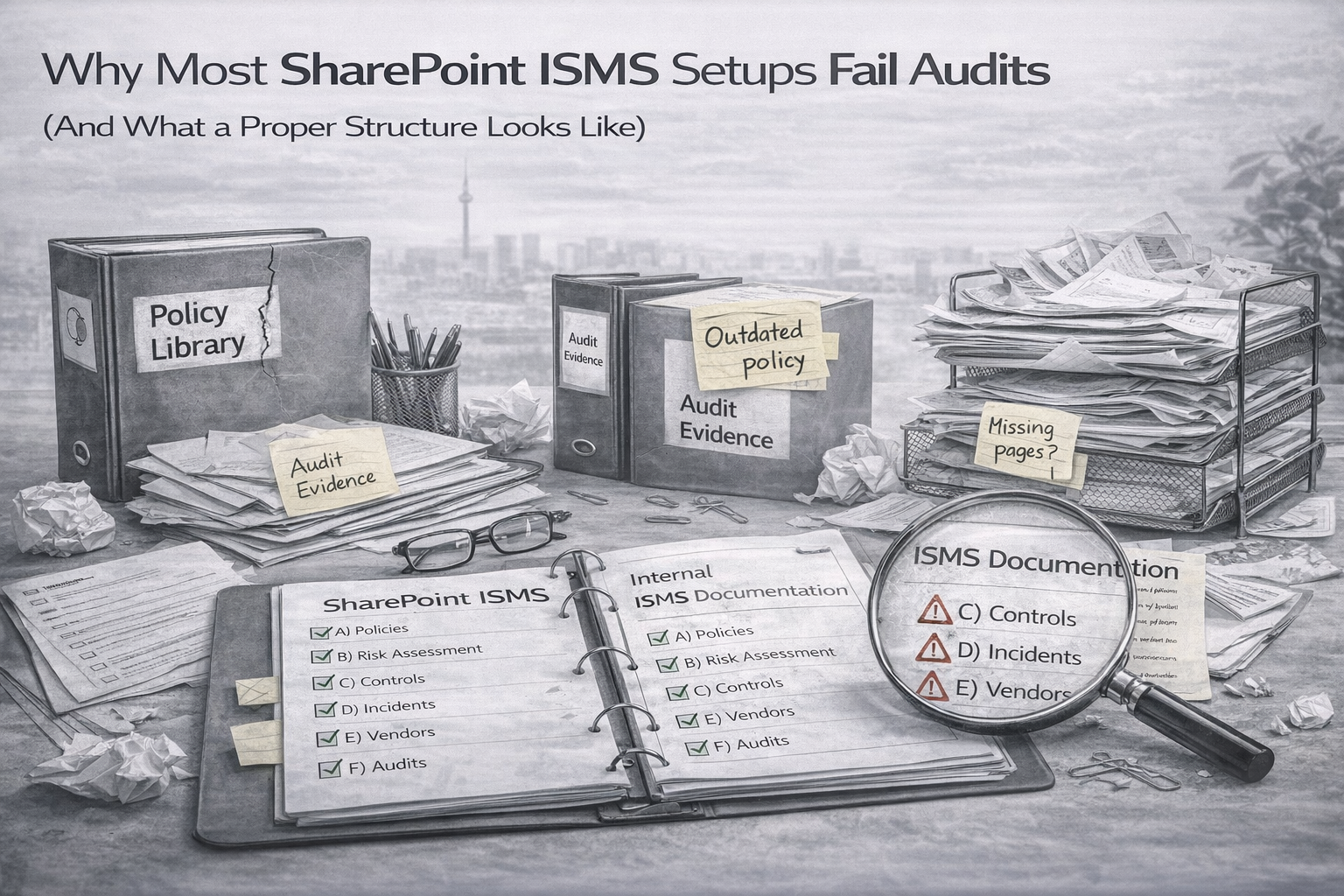
Auditors usually do not fail teams because policies are stored in SharePoint. They fail teams because SharePoint cannot quickly show who owns the control, how often it runs, where the latest approved evidence lives, what exceptions are active, and whether findings actually close with proof.
This guide breaks down the most common failure patterns and shows what an audit-ready SharePoint ISMS structure should look like for ISO 27001 and SOC 2.
Auditors are not judging whether SharePoint looks tidy. They are judging whether your ISMS is defined, operating, provable, and improving.
One of the most common audit moments is simple. The team shows a policy PDF, and the auditor immediately asks for the last real evidence sample behind it. If the policy is not tied to operating proof, the document becomes shelfware.
When evidence is saved as “final_v7,” “audit stuff,” random screenshots, or exports with no date or context, teams lose hours and auditors keep asking for more.
Uploading evidence is not the same as reviewing it. Auditors want proof that someone accountable checked the evidence, matched it to the control, and approved it on time.
SharePoint fails when everything is treated as a file. Risks, exceptions, corrective actions, and reviews are not just documents. They are records that need filtering, grouping, expiry tracking, and dashboards.
Unpatched systems, logging gaps, vendor assurance gaps, and temporary admin access all become audit findings when they are not tracked with compensating controls, approvals, expiry dates, and closure plans.
Without a curated auditor view, teams either overshare internal detail or scramble to assemble a temporary portal during the audit. Both create stress and inconsistency.
Auditors usually test a chain: control, evidence, outcome, frequency, and owner. If SharePoint cannot show that chain, they keep pulling threads until they find the break.
Many teams store internal audit reports but do not manage the chain from finding to action to closure proof to verification. That is how repeat findings survive year after year.
You do not need dozens of libraries. You need a clean operating structure with a few core libraries for documents and a few core lists for records.
| Library | What belongs there | Design notes |
|---|---|---|
| Policies and Procedures | Approved policies, procedures, and runbooks | Versioning on, approvals on, retired items archived |
| Evidence Packs | Quarterly evidence grouped by control area | Use 2026-Q1, 2026-Q2 and category folders inside each quarter |
| Auditor View | Curated, approved-only content for sampling | Read-only, minimal exposure, built for speed |
A good SharePoint ISMS should let you answer these in about two minutes.
If any of those turn into a scavenger hunt, your structure is still doing too much hiding and not enough proving.
After one month of focused cleanup, most SharePoint ISMS setups become much easier to audit and much easier to run.
SharePoint does not fail audits because it is the wrong platform. It fails audits when it is asked to hold an ISMS without the structure that makes ownership, cadence, approvals, evidence, and improvement obvious.
Once you separate records from documents, make traceability visible, and create a real auditor view, SharePoint becomes much easier to trust and much faster to audit.