The failure patterns are consistent. They all come from the same root cause: exercises are designed to avoid discomfort rather than create it. Here is what that looks like in practice.
The scenario is too vague
“A threat actor has gained access to your network” tells executives nothing real. No specificity, no stakes, no urgency so no genuine decision-making happens.
The technical team carries all the weight
When the CTO is the only person speaking for 60 minutes, you have run an IT debrief with observers not a tabletop exercise.
Executives aren’t given their actual roles
In a real incident, the CFO decides on ransom under legal ambiguity. The CEO decides when to notify regulators. If they’re not practising those decisions, the exercise is theatre.
There’s no pressure
Real incidents don’t give you time to look things up. A good exercise uses time constraints, incomplete information, and evolving injects because that’s what reality delivers.
The debrief produces observations, not commitments
A list of “areas to improve” with no owners, no budgets, and no deadlines is not an output. It’s a way of feeling productive without being accountable.
What makes a tabletop exercise truly cross-functional
A cross-functional exercise isn’t just a bigger room with more people. It’s a deliberate design choice to stress-test the gaps between departments because that’s exactly where real incidents break down.
1. The right people in the room not just the security team
A real enterprise drill requires every function that would be activated in an actual incident. The moment the exercise is dominated by the security team, it has stopped being cross-functional.
C-Suite
CEO (or COO), CFO, CTO/CIO, CHRO
Legal & Compliance
General Counsel, Privacy Officer, Compliance lead
Communications
Internal and external communications leads
IT & Security
CISO, IR lead, IT operations
Finance
Ransom payment decisions, insurance coordination, incident costing
Third-Party Risk
Procurement or vendor management lead, where relevant
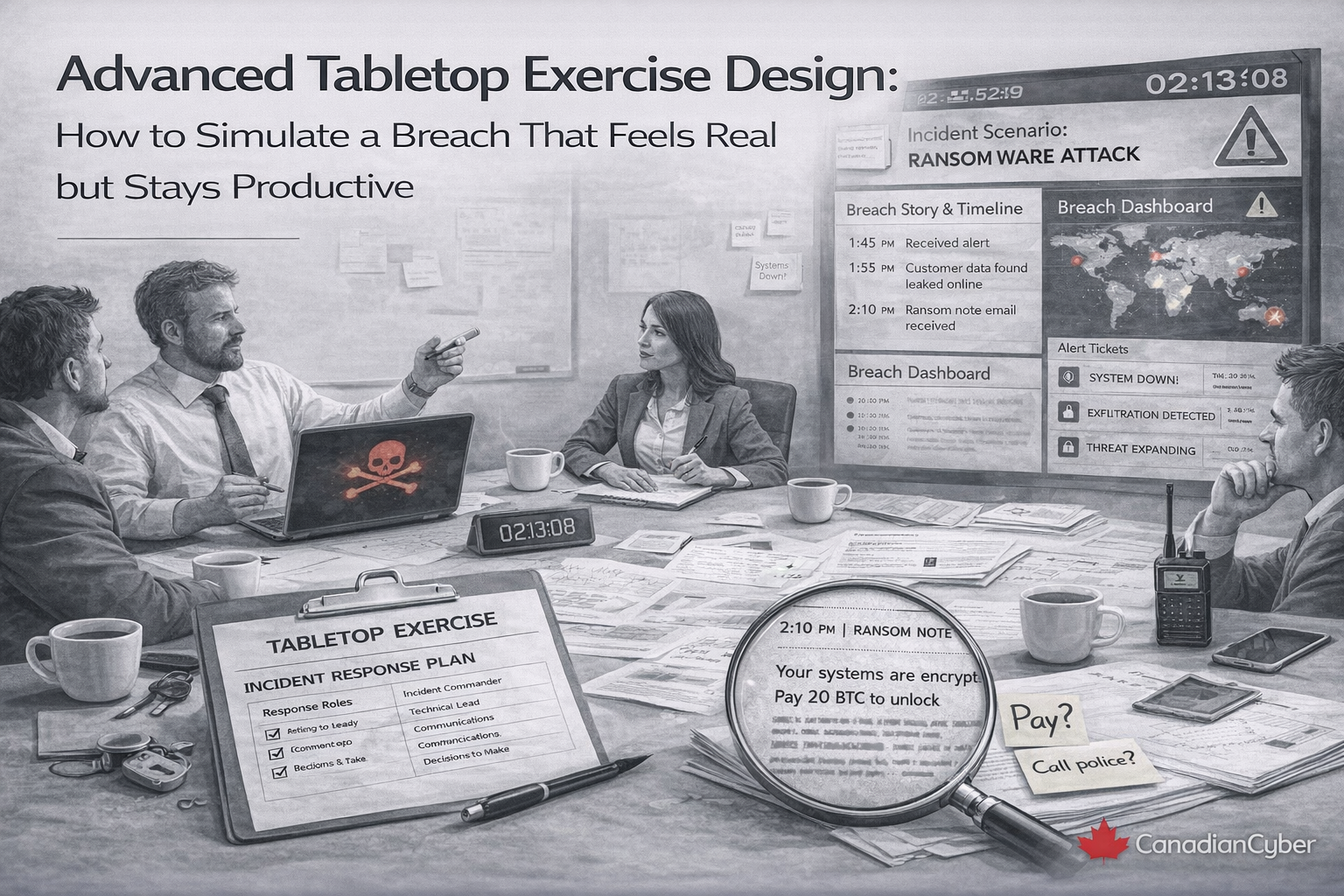
2. Scenario specificity that forces real decisions
The scenario must be specific enough that participants cannot stay abstract. Compare these two approaches:
Too vague
“A data breach has occurred.”
No decisions. No urgency. Executives disengage within minutes.
Specific and pressure-tested
“It is 7:43 AM on a Tuesday. Your EDR has flagged anomalous lateral movement across 14 servers. Your payroll processor just called — they can’t access your tenant. Your customer portal is slow. No confirmed exfiltration yet.”
Pro tip:
Brief the scenario design team separately from participants. Participants should experience the scenario cold — just like a real incident.
3. Injects that evolve the crisis in real time
Static exercises give all the information at once. Real incidents don’t work that way. A strong facilitator introduces new injects every 20–30 minutes escalating pressure and revealing new dimensions of the crisis.
Sample inject sequence — ransomware scenario:
T+0
Inject 1: EDR alert confirmed ransomware on three endpoints. Who makes the call to isolate systems?
T+20
Inject 2: A journalist contacts your comms team asking about “a major outage” — before scope is confirmed internally.
T+40
Inject 3: The threat actor posts on a dark web forum claiming 250,000 customer records exfiltrated.
T+60
Inject 4: Your cyber insurer advises the policy required notification within 4 hours of detection. You are at hour 5.
Pro tip:
Base injects on your sector’s real incident history. Canadian financial institutions face different threat patterns than healthcare providers. Tailor accordingly.
4. Role-based decision lanes
Each participant gets a role card. It outlines their specific responsibilities, the decisions they are authorized to make, and their escalation path. The facilitator routes injects to the right role not just the loudest voice in the room.
What role cards reveal
- Executives cannot passively observe when the inject lands in their lane, they must respond
- Decision authority gaps surface quickly executives often discover they own decisions they didn’t know they had
- IR plan mismatches become visible if the plan assumes authority that no one in the room recognizes, that’s a finding
How to design scenarios executives cannot tune out
Getting executives to engage is a design challenge, not an authority challenge. Here is what drives real participation at the leadership level.
Make impact concrete and financial
Executives speak the language of risk, revenue, and reputation. Quantify it: “$4–6M projected revenue loss if the portal is offline for 72 hours. PIPEDA notification deadline: 72 hours from confirmed breach.”
Give them decisions they cannot delegate
The most powerful moments happen when an executive realizes the ransom payment call, the regulator notification, or the public statement sits with them personally — not with IT. Design those moments intentionally.
Use an independent external facilitator
Executives engage differently with an external expert. An independent facilitator can challenge the CEO’s decision and push back on weak answers without internal politics getting in the way.
Brief on role, not scenario
Send a one-page role brief a week before the exercise. Tell participants what decisions they’ll be expected to make but keep the scenario confidential. Pressure stays intact.
Keep it under three hours
Executive calendars are real. A tight three-hour session with sharp facilitation outperforms a full-day drill where attention fades after lunch.
Is your organization ready for a real cyber crisis?
Canadian Cyber designs and facilitates enterprise tabletop exercises built for your sector, your threat landscape, and your regulatory environment — from scenario design through to post-exercise remediation planning.
The 5 scenarios that hit hardest in 2026
Not all scenarios are equal. These five consistently produce the most revealing decision moments for cross-functional enterprise teams.
| Scenario |
Core pressure |
Best for |
| Ransomware + data exfiltration |
System downtime, extortion, 48-hour ransom deadline, dark web leak site |
CFO and CEO engagement, cyber insurance coordination, crisis comms |
| Supply chain compromise |
Trusted vendor breached with 90-day access unknown scope of exposure |
Third-party risk, legal, procurement, operations |
| Insider threat |
Senior IT employee suspected of IP exfiltration during notice period employment law constraints apply |
HR, Legal, and IT Security coordination |
| Critical infrastructure outage |
Cyber-physical incident takes down a key operational system BCP never fully tested |
Business continuity, operations, executive decisions under financial pressure |
| Regulatory notification deadline |
Breach confirmed, scope unknown, PIPEDA 72-hour clock ticking, journalist at the door |
Legal, communications, executive decisions around regulatory risk |
Canadian regulatory context matters:
Your injects should reference PIPEDA’s breach notification requirements, the Office of the Privacy Commissioner, sector-specific regulators (OSFI, Health Canada), and the Canadian Centre for Cyber Security’s breach guidance. Generic exercises miss the nuance Canadian organizations need to practise.
What your organization should walk away with
A four-page summary report with no owners and no timelines is not a success. Here is what a genuinely useful post-exercise output looks like.
Immediate findings (within 48 hours)
A prioritized list of gaps in decision authority, communication protocols, IR plan accuracy, or technical response with a severity rating and a named owner for each.
Decision tree updates
If the exercise revealed that ransom payment, media statements, or regulator notification have no clear owner those gaps get documented and filled before the next drill.
Revised IR plan sections
Clauses contradicted by actual behaviour during the exercise get updated to reflect operational reality not aspirational intent.
Committed remediation items
At least three to five specific, budgeted, time-bound actions that will be completed before the next exercise. These are the proof that the drill changed something.
Scheduled follow-up exercise
The best outcome is a date on the calendar for the next drill — with a specific scope that targets the gaps just identified.
Present findings to the board, not just the executive team.
Boards are expected to demonstrate oversight of cyber risk. Seeing the findings and remediation commitments is exactly the governance evidence regulators and auditors want.
Best practices for drills that actually stick
To run exercises that produce lasting improvement — not a checked box — keep these principles in mind.
- Run at least two exercises per year. One technical, one executive. They are complementary not interchangeable.
- Separate the audiences by design. Mixing your SOC team and your CEO in the same exercise often produces the worst of both. Run them separately, then integrate in a unified command exercise.
- Record findings in real time. Assign a dedicated scribe to capture decisions made, decisions deferred, and gaps surfaced while they’re still fresh.
- Rotate the scenario type each year. An organization that runs ransomware exercises three years running will optimize for ransomware. Rotate to supply chain, insider, regulatory, and physical/cyber scenarios.
- Treat the debrief as the most important hour. The exercise surfaces gaps. The debrief turns them into commitments. Never let it be cut short for schedule reasons.
- Use Canadian-specific regulatory context. Generic exercises miss the nuance. Reference PIPEDA, OSFI, provincial privacy legislation, and the Canadian Centre for Cyber Security’s guidance.
The gap between the plan and the response is where breaches escalate
Your incident response plan describes what should happen. A cross-functional tabletop exercise reveals what actually would happen. The distance between those two things is often larger than anyone in the room expected.
The organizations that close that gap before an incident are the ones that contain breaches faster. They communicate more credibly. They recover more quickly. And they avoid the compounding damage that comes from fumbled decisions in the first 24 hours.
Running a tabletop exercise that executives take seriously isn’t about making security dramatic. It’s about making it genuinely relevant to the decisions they will be required to make. Give them a safe environment to make those decisions badly once so they don’t make them badly when it counts.
Ready to run a cross-functional cyber crisis drill your executives will actually remember?
Canadian Cyber designs and facilitates enterprise tabletop exercises for organizations across Canada — from scenario design through to post-exercise remediation planning. We build it to your sector, your threat landscape, and your regulatory environment.
Follow Canadian Cyber
Practical cybersecurity and compliance guidance: