Enterprise deals stall when SaaS vendors can't answer security questionnaires confidently. This checklist breaks down the 15 areas enterprise buyers and auditors assess before signing from identity management and encryption to AI data transparency and security governance so your team can prepare before the questionnaire ever arrives.
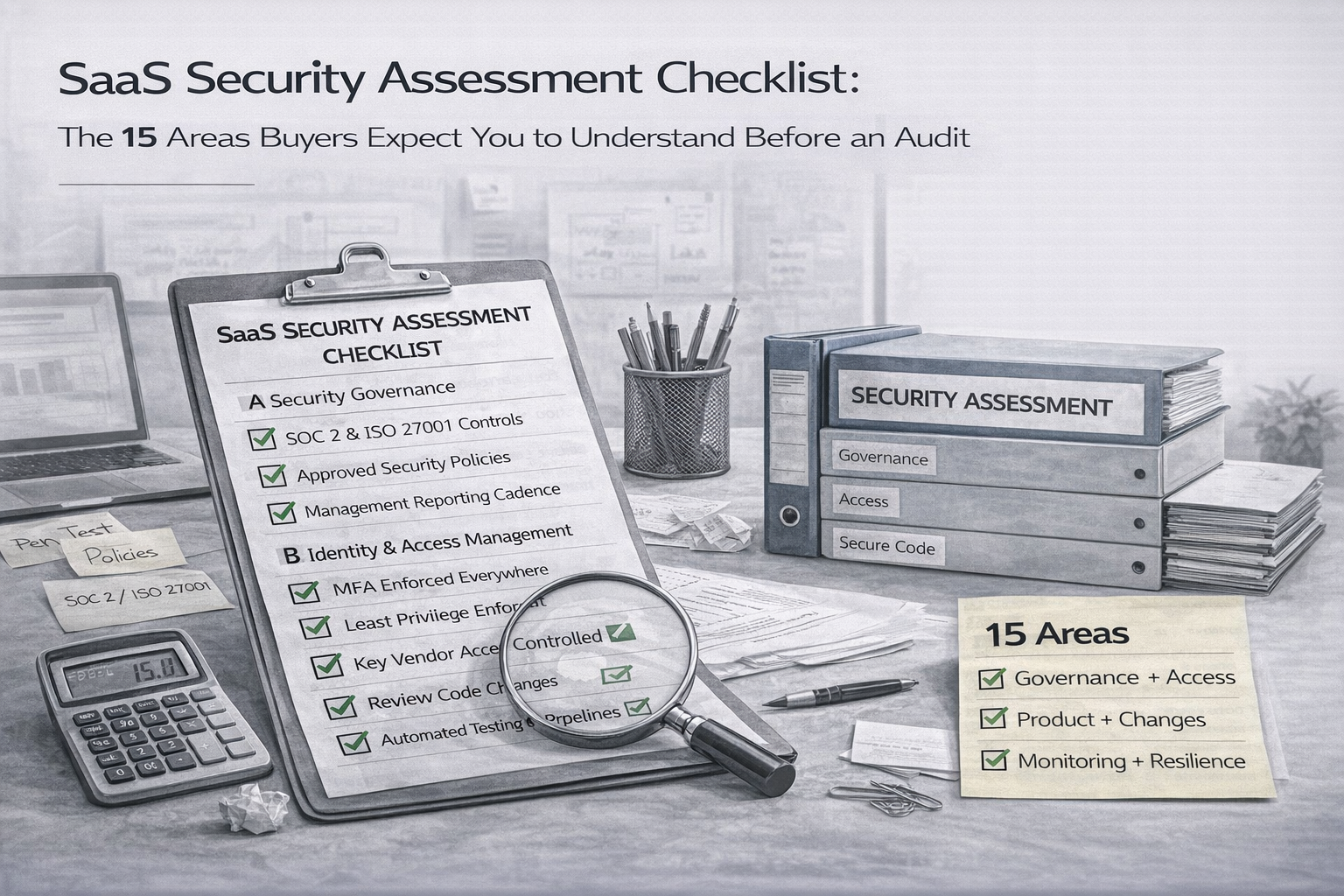
This guide breaks down the 15 security areas enterprise buyers and their security teams will assess before signing a contract. For each area, we explain what buyers are looking for, what auditors verify under SOC 2 and ISO 27001, and what your responses must demonstrate.
The bar is higher than it was even two years ago. Four shifts explain why.
Canadian Cyber assesses SaaS security programmes against the 15 areas enterprise buyers check — and delivers a clear remediation roadmap before your next enterprise sales cycle.
The organizations that move through enterprise security reviews fastest do the preparation before the questionnaire arrives. Here is what that looks like in practice.
The SaaS security assessment has become one of the most important filters in enterprise procurement. Buyers are not running these assessments to create paperwork. They are running them because they have accountability to their own boards, customers, and regulators for the vendors they choose.
The SaaS vendors who understand this shift treat their security programme as a commercial asset. A strong, documented, independently verified security posture means shorter sales cycles, fewer stalled deals, and the ability to walk into any enterprise RFP with confidence rather than scrambling to prepare answers the week before a review deadline.
The 15 areas in this checklist are not theoretical. They are the questions enterprise buyers in Canada and internationally are asking your team right now or will be asking in the next procurement cycle.