Case Study • Manufacturing ISMS • ISO 27001
Case Study: How a Manufacturing Firm Built an ISMS Without Slowing Operations
A practical ISMS can protect production systems, engineering files, vendors, and customer trust without creating unnecessary delays on the floor.
Quick Snapshot
| ISMS Focus Area | Manufacturing Priority |
|---|---|
| Operations | Protect production schedules, ERP systems, quality records, and uptime |
| Customer Files | Secure CAD files, customer specifications, drawings, and engineering records |
| Vendors | Manage supplier portals, remote support, managed IT, ERP support, and maintenance access |
| Evidence | Use SharePoint to organize policies, risks, vendors, incidents, audits, and corrective actions |
Introduction
Manufacturing firms cannot afford security programs that slow the floor down.
- Production schedules matter.
- Machine uptime matters.
- Shipping deadlines matter.
- Supplier coordination matters.
- Quality checks matter.
- Customer commitments matter.
The firm succeeded because it designed the ISMS to support operations, not sit on top of them like bureaucracy.
This case study shows how a fictional manufacturing firm built a practical ISMS around real operations, focusing on risk, access, vendors, incidents, and evidence without disrupting production.
Need an ISMS That Does Not Slow Operations?
Canadian Cyber helps manufacturing firms build practical ISO 27001 and ISMS programs around real production workflows.
The Company
Let’s call the company NorthLine Manufacturing.
NorthLine produced precision components for industrial clients.
The company used:
- ERP systems
- production planning software
- supplier portals
- CAD files
- quality records
- customer specifications
- shop-floor devices
- cloud file sharing
- remote vendor support
- managed IT services
The leadership team wanted stronger security because customers were asking more questions about data protection, supplier risk, and business continuity. They also wanted to prepare for ISO 27001.
The Challenge
NorthLine had several common gaps:
- policies were outdated
- access reviews were informal
- vendor records were scattered
- incident response was not documented well
- backups were configured, but restore evidence was weak
- sensitive engineering files were shared inconsistently
- corrective actions were tracked through emails and spreadsheets
The company needed structure, but not complexity.
Step 1: Define a Practical ISMS Scope
The team kept the ISMS scope focused on systems and processes that mattered most.
In scope:
- ERP and production planning systems
- customer specifications and engineering files
- supplier and vendor access
- quality and compliance records
- cloud storage
- IT infrastructure supporting production
- backup and recovery processes
- employees and vendors with access to sensitive systems
This avoided dragging every minor tool into the first phase.
Not Sure What Your Manufacturing ISMS Should Cover?
We help define scope around production systems, customer files, vendors, ERP, backups, and operational continuity.
Step 2: Map Operational Risks
The team created a practical risk register focused on real manufacturing concerns.
| Risk | Why It Mattered |
|---|---|
| ERP outage | Could delay production and shipping |
| Unauthorized access to CAD files | Could expose customer designs |
| Vendor remote access misuse | Could affect systems or production uptime |
| Backup restore failure | Could delay recovery after outage |
| Supplier portal compromise | Could expose purchasing or delivery data |
| Ransomware on office systems | Could disrupt operations and customer service |
This helped employees see the ISMS as business protection, not paperwork.
Step 3: Build Controls Around Existing Workflows
Instead of creating brand-new processes everywhere, the team improved what already existed.
| Existing Workflow | ISMS Improvement |
|---|---|
| Onboarding tickets | Access approvals were added |
| Procurement workflow | Vendor reviews were added |
| IT support workflow | Incident reporting was added |
| Monthly IT checks | Backup testing was added |
| SharePoint document storage | Policy reviews were tracked |
| Email and spreadsheets | Corrective actions moved into a simple tracker |
This reduced resistance because teams did not have to learn a completely separate compliance system.
Step 4: Protect Engineering and Customer Files
Customer drawings, CAD files, and specifications were treated as high-value information assets.
The firm improved controls by:
- restricting file access by role
- removing outdated shared links
- using approved cloud storage
- limiting downloads where possible
- reviewing external sharing
- training teams on handling customer files
This was one of the biggest trust improvements for customers.
Are Customer Drawings and CAD Files Properly Protected?
Canadian Cyber helps manufacturing firms review access, external sharing, cloud storage, and handling rules for sensitive engineering files.
Step 5: Strengthen Vendor and Remote Access
Manufacturing environments often depend on vendors for:
- machine support
- ERP support
- IT support
- cloud services
- maintenance systems
- software platforms
NorthLine created a vendor register and reviewed high-risk vendors first.
| Vendor Register Field | Purpose |
|---|---|
| Vendor owner | Shows accountability |
| Service provided | Clarifies dependency |
| Access level | Shows operational exposure |
| Data handled | Supports risk ranking |
| Criticality | Prioritizes reviews |
| Security evidence | Supports supplier assurance |
| Next review date | Keeps oversight current |
Remote access was tightened with MFA, approval rules, and logging where available.
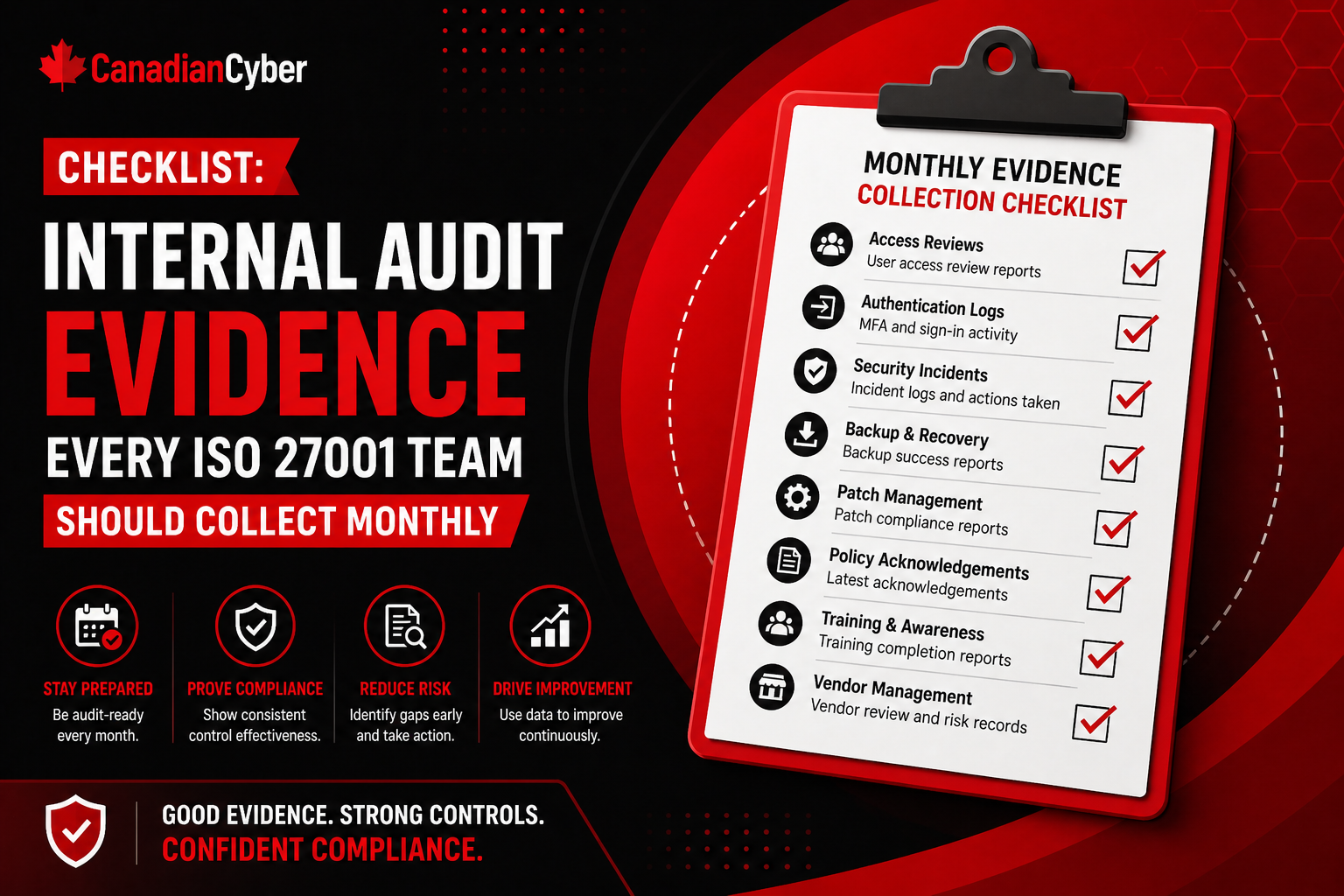
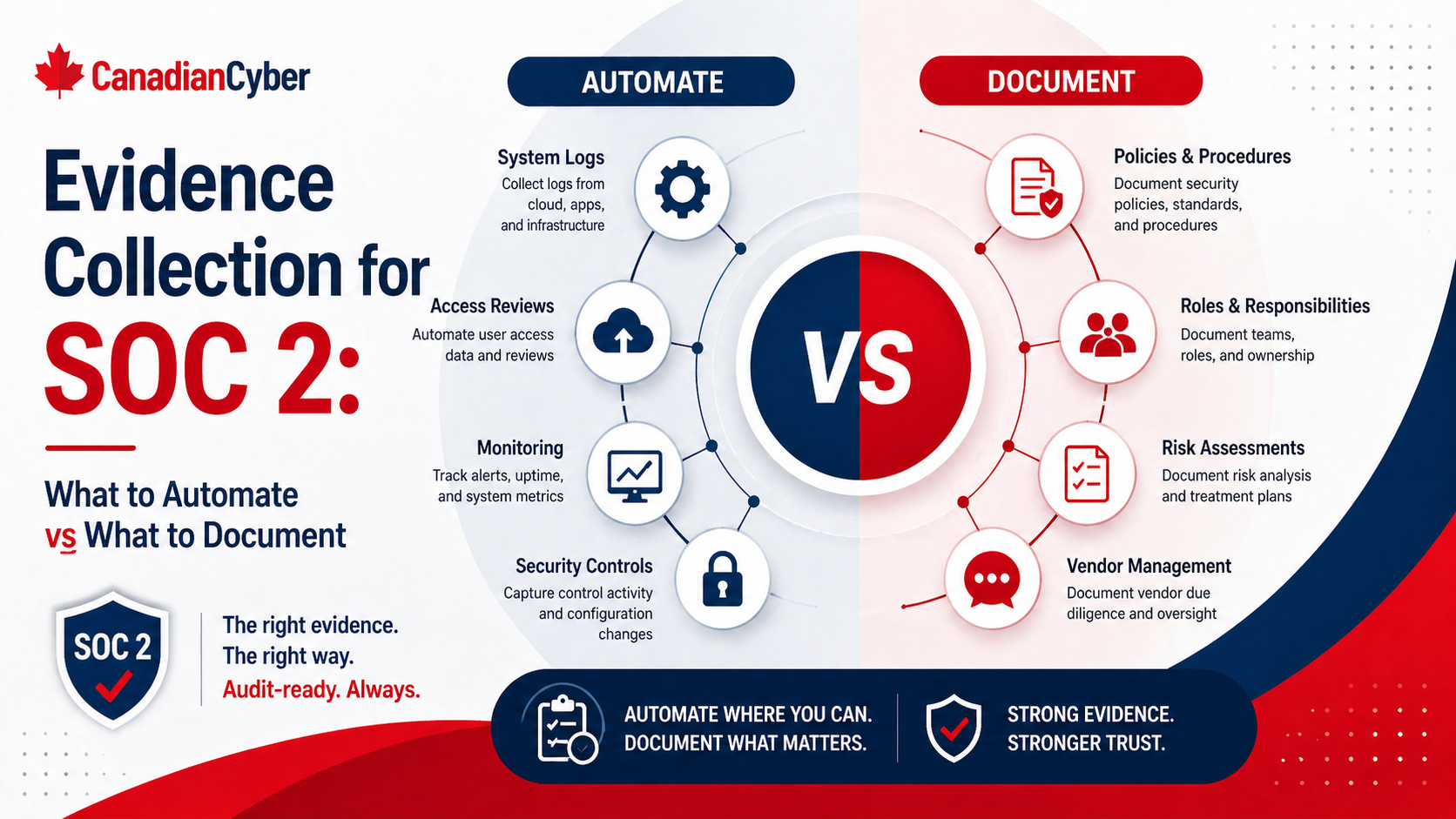
Step 6: Create Evidence Without Extra Burden
The team used SharePoint as the ISMS workspace.
It included:
- policy library
- risk register
- vendor tracker
- corrective action tracker
- evidence library
- incident records
- internal audit folder
- management review section
Evidence was collected from normal operations, such as:
- access review exports
- backup test records
- vendor review notes
- incident tickets
- policy approvals
- training completion reports
- corrective action closure proof
The goal was to reuse operational records instead of creating duplicate paperwork.
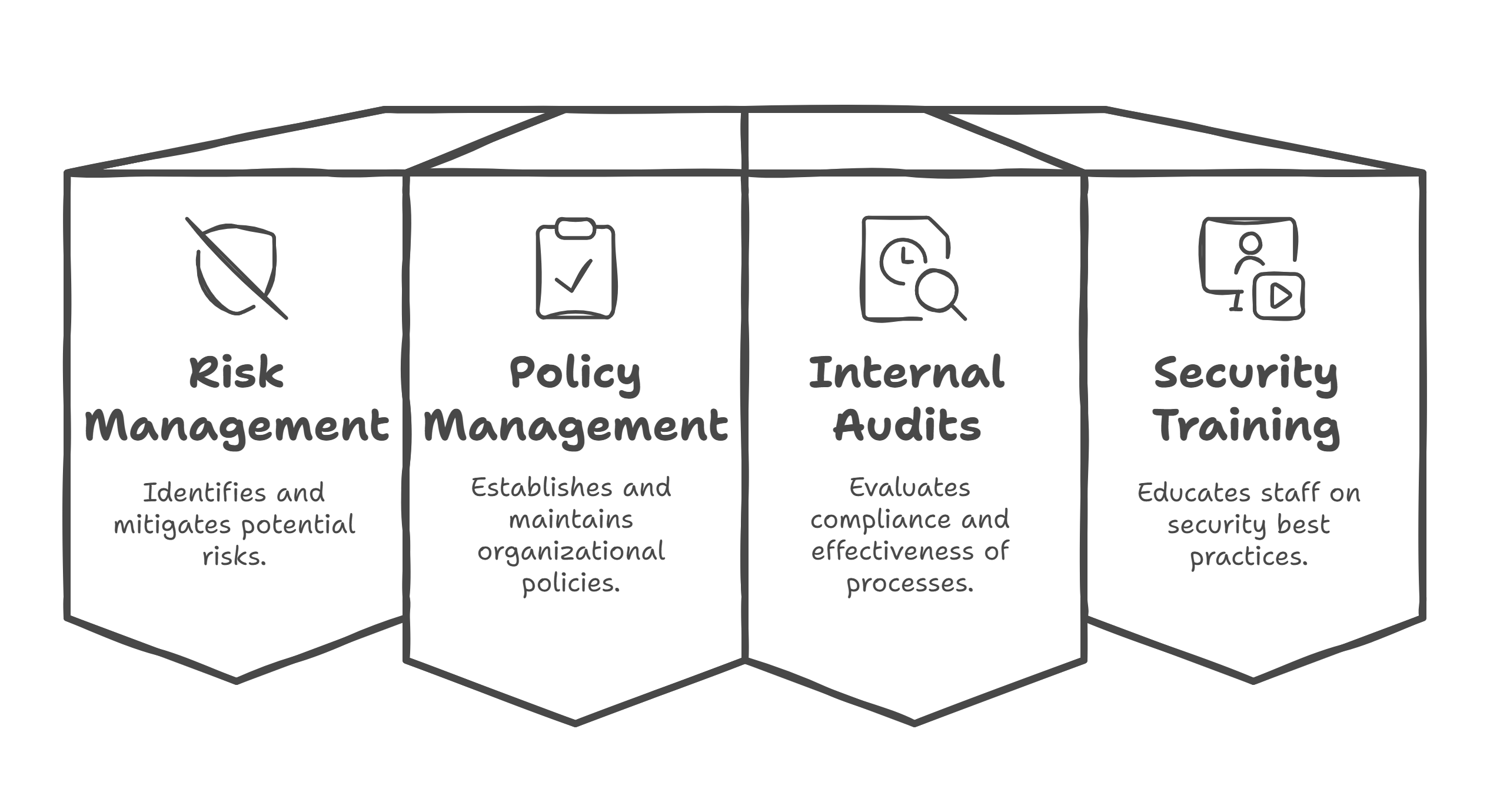
Step 7: Run a Focused Internal Audit
The internal audit tested the highest-risk areas:
- access to ERP and file storage
- vendor remote access
- backup and recovery evidence
- incident response records
- handling of customer engineering files
- corrective action tracking
The audit found a few gaps, including incomplete vendor evidence and inconsistent access review notes. Those findings were turned into corrective actions with owners and due dates.
Need a Focused Manufacturing Internal Audit?
We help test the controls that matter most: ERP access, vendor remote access, backups, customer files, incidents, and corrective actions.
The Results
NorthLine built an ISMS without slowing operations because the program was practical.
The company achieved:
- clearer ownership
- stronger access control
- better vendor oversight
- improved protection of customer files
- stronger backup evidence
- more consistent incident documentation
- better audit readiness
- less last-minute evidence chasing
Most importantly, production teams did not feel like the ISMS was blocking their work.
What Made It Work
- The ISMS was tied to operational risk: The team focused on uptime, customer files, vendors, and recovery.
- Controls fit existing workflows: The company avoided unnecessary new bureaucracy.
- SharePoint kept evidence organized: Evidence was easy to find and review.
- Vendors were prioritized by risk: Not every supplier needed the same review depth.
- Leadership stayed involved: Management review helped keep security aligned with business needs.
Lessons for Other Manufacturing Firms
Manufacturing companies should avoid treating an ISMS like an office-only compliance project.
A useful ISMS should protect:
- production systems
- engineering files
- supplier workflows
- customer data
- vendor access
- recovery capability
- operational continuity
The best approach is to build controls around how the business already works.
Canadian Cyber’s Take
At Canadian Cyber, we often see manufacturing firms worry that ISO 27001 or ISMS work will slow down operations.
That usually happens when the program is designed too generically.
A strong manufacturing ISMS should be practical, risk-based, and operationally aware. It should help protect uptime, customer trust, supplier relationships, and sensitive production information without turning every task into paperwork.
Takeaway
A manufacturing firm can build an ISMS without slowing operations when the program is designed around real business workflows.
The key is to focus on:
- practical scope
- operational risk
- access control
- vendor oversight
- customer file protection
- backup and recovery
- simple evidence collection
- corrective action follow-up
An ISMS should not make manufacturing slower. It should make the business more resilient, trusted, and easier to defend during customer or audit reviews.
How Canadian Cyber Can Help
At Canadian Cyber, we help manufacturing firms build practical ISMS programs that support security and compliance without disrupting operations.
- ISO 27001 and ISMS implementation
- manufacturing risk assessments
- SharePoint ISMS setup
- vendor and remote access reviews
- backup and incident readiness
- customer data and engineering file protection
- internal audit and corrective action tracking
- vCISO guidance for operational security
Stay Connected With Canadian Cyber
Follow Canadian Cyber for practical guidance on ISO 27001, manufacturing security, ISMS implementation, operational resilience, and vCISO support.