ISO 27001 • Scope Errors • Certification Readiness
Common Mistakes: ISO 27001 Scope Errors That Delay Certification and Increase Cost
A weak ISO 27001 scope creates confusion about what the ISMS protects, which controls apply, what evidence is needed, and what the auditor will test.
Quick Snapshot
| Scope Mistake | Why It Delays Certification |
|---|---|
| Too Broad | Creates too much evidence, audit testing, internal audit work, and remediation. |
| Too Narrow | Misses systems, vendors, tools, or teams that affect in-scope information. |
| Too Vague | Leaves control owners and auditors unclear about what is actually covered. |
| Misaligned | Creates mismatch between the scope, risk assessment, SoA, evidence, and audit testing. |
Introduction
ISO 27001 certification does not usually get delayed because teams refuse to work hard.
It gets delayed because the ISMS scope was unclear from the beginning.
- The organization starts writing policies.
- Risk assessments begin.
- Controls are mapped.
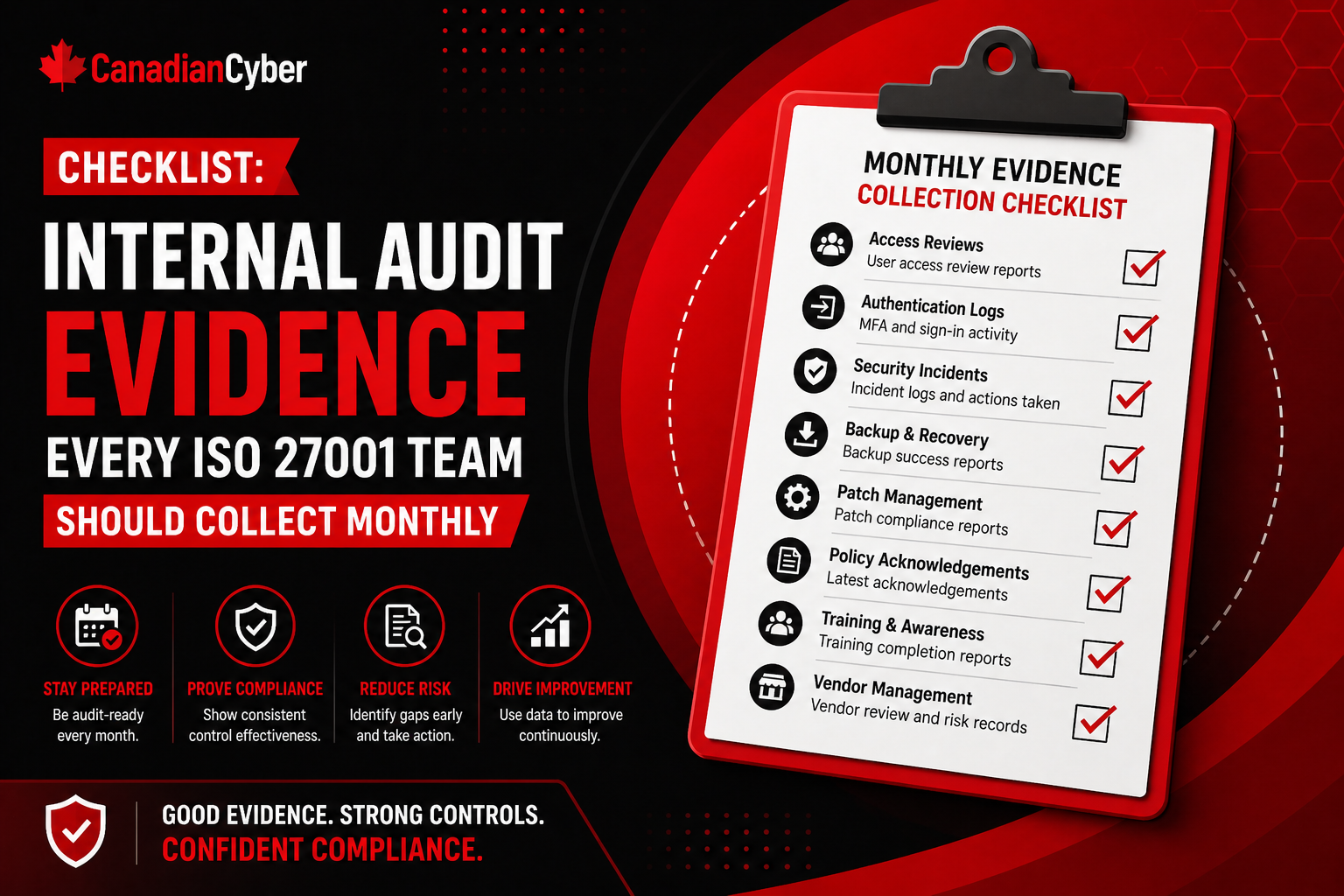
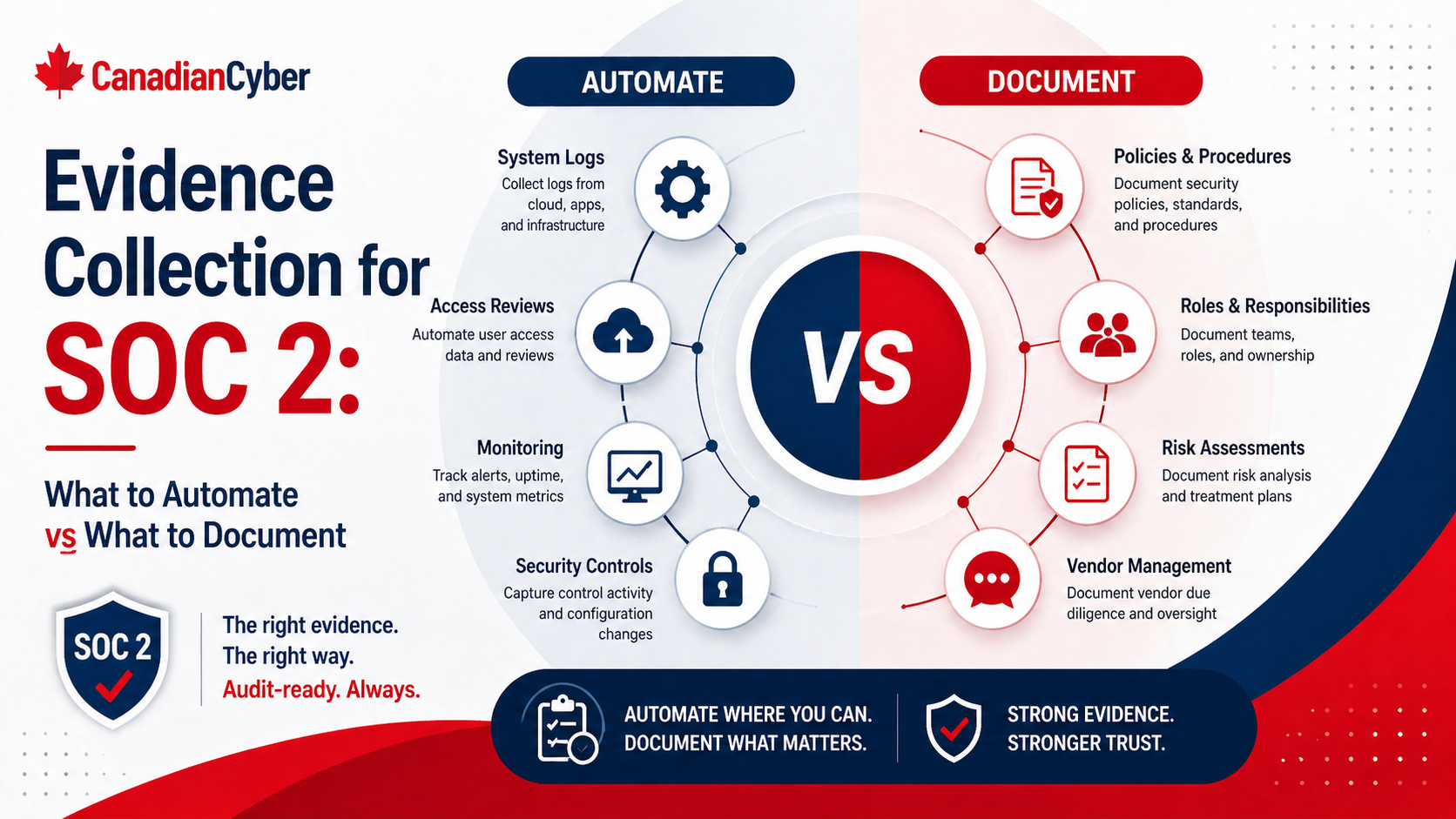
- Evidence is collected.
- Internal audit is scheduled.
Then someone asks a basic question: what exactly is in scope?
That question should have been answered early. When it is not, the whole project becomes slower, more expensive, and harder to audit.
Is Your ISO 27001 Scope Unclear?
Canadian Cyber helps organizations define practical, audit-ready ISO 27001 scopes before costly rework begins.
Why Scope Matters So Much
The ISMS scope defines the boundary of your ISO 27001 implementation.
It tells everyone:
- which products, services, teams, systems, and locations are covered
- which information assets must be protected
- which vendors and processes matter
- which controls apply
- what evidence must be collected
- what is excluded and why
If the scope is wrong, the rest of the ISMS is built on shaky ground. A clear scope makes implementation easier. A vague scope creates rework.
Mistake 1: Writing a Scope That Is Too Broad
Many organizations think broader scope looks more mature.
So they include:
- every department
- every system
- every vendor
- every office
- every cloud service
- every internal process
This sounds impressive, but it can quickly make certification harder.
| Broad Scope Impact | Result |
|---|---|
| More evidence volume | More time spent collecting proof |
| More control testing | Longer audit preparation |
| More internal audit work | Higher internal effort |
| More remediation | More delays and consultant cost |
Better approach: start with the business service, product, or operational area that matters most.
Better scope: The ISMS covers the cloud-hosted SaaS platform, production infrastructure, customer data processing, support operations, and the teams and vendors that operate or support the service.
Weak scope: The ISMS covers all company operations.
Mistake 2: Writing a Scope That Is Too Narrow
The opposite problem also happens. Organizations try to keep the scope small, but accidentally exclude systems that clearly affect the security of in-scope information.
Examples include:
- support tools that contain customer data
- identity provider used for production access
- CI/CD pipeline that deploys the product
- logging platform with sensitive records
- backup systems
- endpoint devices used by administrators
- vendors that process in-scope data
Is Your Scope Too Broad or Too Narrow?
We help teams identify missing systems, vendors, workflows, and dependencies before the auditor does.
Mistake 3: Using Vague Scope Language
Vague scope language creates confusion.
| Vague Phrase | Why It Is Weak |
|---|---|
| Information security activities | Does not define systems, teams, or data |
| Company data | Too broad and unclear |
| Cloud systems | Does not identify environments or dependencies |
| Business operations | Does not explain what the auditor should test |
Better scope language should include:
- business service
- locations
- systems
- data types
- teams
- cloud environments
- support processes
Specific wording helps control owners know what evidence to provide and helps auditors understand what is covered.
Mistake 4: Forgetting Support and Customer Success Tools
Support tools are often missed, but they may contain sensitive customer information.
- customer screenshots
- support tickets
- account data
- error logs
- attachments
- export files
- access to admin dashboards
Auditors may ask:
- Can support access customer information?
- Are support actions logged?
- Are support users reviewed?
- Are support attachments controlled?
- Are tickets retained properly?
Mistake 5: Ignoring Vendors and Subprocessors
Many organizations define scope around internal systems only. Then they forget that vendors may handle critical parts of the service.
Examples include:
- cloud hosting provider
- identity provider
- ticketing platform
- monitoring tool
- managed IT provider
- payment processor
- backup provider
- AI or analytics provider
Create a vendor register early and track:
| Vendor Field | Why It Matters |
|---|---|
| Vendor name | Identifies the dependency |
| Service provided | Clarifies business use |
| Data handled | Shows sensitivity |
| Criticality | Supports risk-based review |
| Security evidence reviewed | Shows supplier assurance |
| Next review date | Keeps vendor oversight current |
Missing Vendors From Your ISO 27001 Scope?
Canadian Cyber helps map vendors, subprocessors, cloud services, support platforms, and critical dependencies before audit evidence gaps appear.
Mistake 6: Leaving Out Cloud Infrastructure Dependencies
For SaaS and cloud-based companies, cloud scope errors are common.
Teams include the application, but forget supporting cloud components such as:
- storage buckets
- databases
- secrets managers
- cloud IAM
- logging services
- backup snapshots
- monitoring services
- network configuration
- container registries
- deployment infrastructure
Create a cloud architecture and data flow diagram before finalizing scope. This helps identify hidden dependencies and avoids rework later.
Mistake 7: Treating Development and CI/CD as Out of Scope
Some teams assume development tools are outside the ISMS because they do not store production customer data. That can be a mistake.
Source control and CI/CD can affect production security because they control:
- code changes
- infrastructure changes
- secrets
- deployment approval
- access to production pipelines
- release integrity
At minimum, review:
- source code access
- branch protection
- pull request review
- deployment permissions
- secret handling
- emergency changes
Mistake 8: Not Defining Exclusions Clearly
Exclusions are acceptable when justified. The problem is when exclusions are vague or undocumented.
For every exclusion, document:
- what is excluded
- why it is excluded
- whether it has any interface with in-scope systems
- why the exclusion does not create unmanaged risk
Mistake 9: Scope Does Not Match the Risk Assessment
The risk assessment should reflect the scope.
If the ISMS scope covers a SaaS platform, the risk register should include risks around:
- production access
- cloud misconfiguration
- customer data exposure
- vendor dependency
- incident response
- backups
- secure development
- support access
If the risk register focuses on generic office risks only, there is a mismatch. Auditors expect the risk assessment to reflect the real scoped environment.
Mistake 10: Scope Does Not Match the Statement of Applicability
The Statement of Applicability should be consistent with the ISMS scope and risk treatment.
Common issues include:
- controls marked not applicable without justification
- cloud-related controls ignored
- supplier controls underdeveloped
- access controls too generic
- secure development controls not aligned to SaaS scope
Need Scope, Risk, and SoA Alignment?
We help align your ISO 27001 scope, risk register, treatment plan, Statement of Applicability, and evidence plan into one audit-ready story.
Mistake 11: Ignoring Physical and Remote Work Boundaries
Even cloud-first companies need to think about people and devices.
If employees remotely administer in-scope systems, the ISMS may need to consider:
- laptops
- endpoint protection
- remote access
- MFA
- acceptable use
- home working expectations
- offboarding
- device encryption
Mistake 12: Not Validating Scope With the Certification Body Early
One of the most expensive mistakes is waiting too long to validate scope.
If the certification body or auditor challenges the scope late in the project, the organization may need to redo:
- risk assessment
- SoA
- evidence collection
- internal audit
- management review
- control testing
Discuss scope early with your certification body or advisor. Make sure the wording, boundaries, and exclusions are defensible before heavy implementation work begins.
How Scope Errors Increase Cost
Scope errors increase cost because they create rework.
| Cost Driver | What Happens |
|---|---|
| Late systems added to scope | More evidence collection and testing |
| Policies rewritten | More review and approval cycles |
| Risk register updated | Treatment plans may change |
| SoA revised | Control applicability must be rechecked |
| Internal audit expanded | More audit time and corrective actions |
| Certification delayed | More consulting and project cost |
A Better ISO 27001 Scope Checklist
Before finalizing scope, ask these questions:
| Question | Answer / Notes |
|---|---|
| What product, service, or business process is covered? | |
| Which locations are included? | |
| Which teams operate or support the scope? | |
| Which systems store or process in-scope information? | |
| Which cloud services support the environment? | |
| Which vendors materially affect the service? | |
| Which support tools can access customer or sensitive data? | |
| Which development and deployment tools affect production? | |
| Which data types are protected? | |
| What is excluded and why? |
Fix Scope Before It Delays Certification
Canadian Cyber helps organizations clarify ISO 27001 scope, exclusions, dependencies, vendors, risk alignment, and SoA consistency.
Canadian Cyber’s Take
At Canadian Cyber, we often see ISO 27001 projects struggle because the team starts building controls before the scope is truly clear.
That creates avoidable rework.
The strongest projects start with a practical scope workshop that maps:
- business services
- systems
- data
- teams
- vendors
- cloud dependencies
- support workflows
- exclusions
Once the scope is clear, the rest of the ISMS becomes easier to build and easier to audit.
Takeaway
ISO 27001 scope errors are one of the fastest ways to delay certification and increase cost.
The most common mistakes include:
- scope too broad
- scope too narrow
- vague wording
- missed support tools
- ignored vendors
- forgotten cloud dependencies
- excluded CI/CD
- unclear exclusions
- mismatch with risk assessment
- mismatch with SoA
ISO 27001 certification depends on more than having controls. It depends on knowing exactly what those controls are meant to protect.
How Canadian Cyber Can Help
At Canadian Cyber, we help organizations define ISO 27001 scopes that are practical, audit-ready, and aligned with real business operations.
- ISO 27001 scoping workshops
- ISMS boundary and exclusion review
- cloud and SaaS dependency mapping
- risk register and SoA alignment
- vendor and support workflow scoping
- internal audit preparation
- vCISO guidance for certification readiness
Stay Connected With Canadian Cyber
Follow Canadian Cyber for practical guidance on ISO 27001, ISMS scoping, audit readiness, risk management, and vCISO support.