Manufacturing Cybersecurity • Shadow OT • vCISO
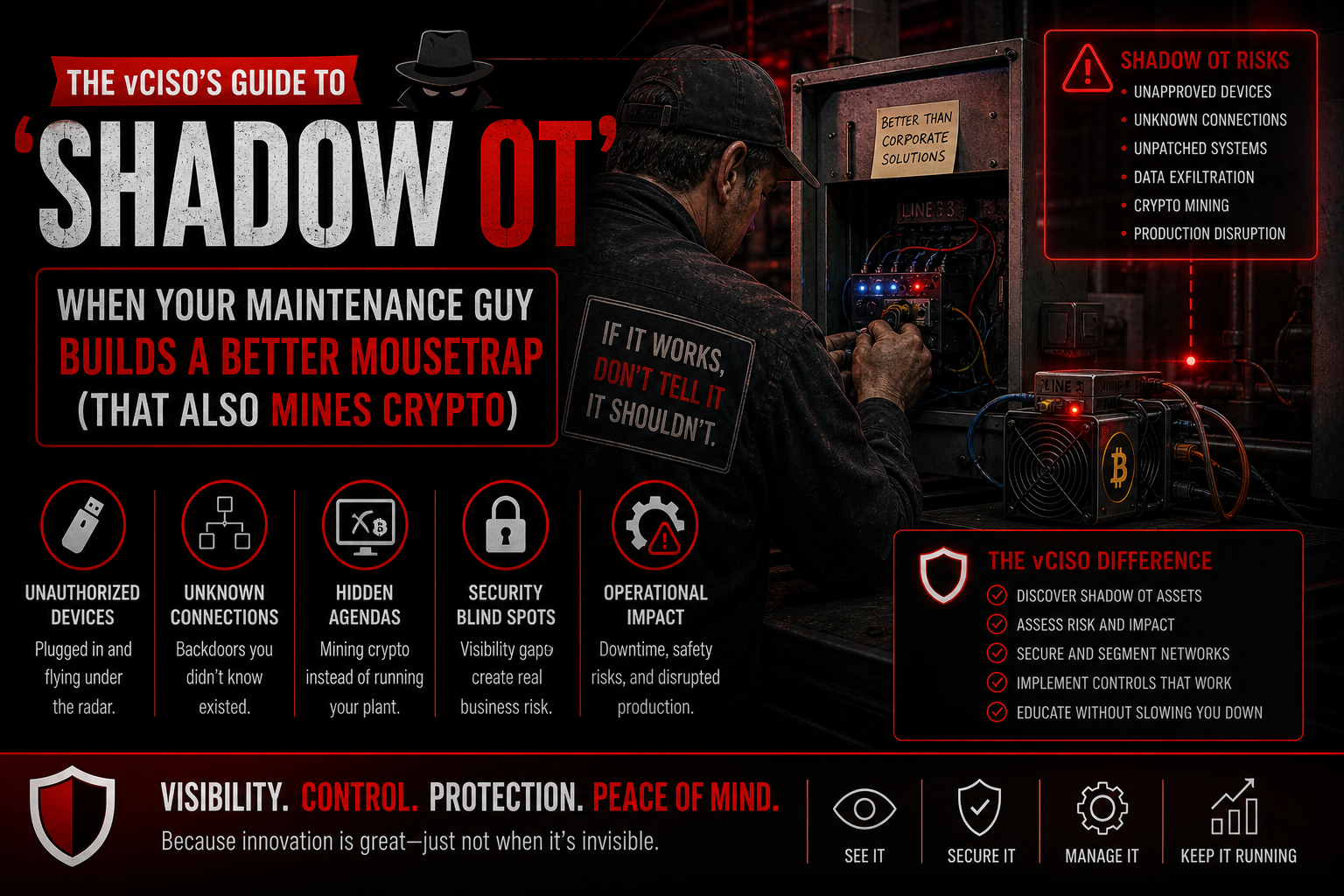
The vCISO’s Guide to Shadow OT: When Your Maintenance Guy Builds a Better Mousetrap That Also Mines Crypto
Shadow OT often starts with helpful operational creativity, but unmanaged devices, scripts, dashboards, and remote tools can quietly become serious cyber and production risks.
Quick Snapshot
| Shadow OT Area | Why It Matters |
|---|---|
| Unknown Devices | Unmanaged controllers, tablets, sensors, and industrial PCs can create hidden access paths. |
| Remote Access | Vendor tools, tunnels, and personal remote apps can become invisible security risks. |
| Network Segmentation | Flat networks let small workarounds become large production-wide problems. |
| vCISO Guidance | A vCISO helps balance operational creativity with visibility, governance, and risk control. |
Introduction
Every factory has one.
The brilliant maintenance person who can fix anything:
- A sensor fails? They build a workaround.
- A dashboard is missing? They connect a spare device.
- A machine needs monitoring? They add a small controller.
- A vendor tool is too slow? They create a shortcut.
Operations improves. Nobody files a ticket. And six months later, IT discovers a mystery device connected to the production network.
That device is monitoring machine uptime, sending data to a personal cloud account, and somehow mining crypto after hours.
Welcome to Shadow OT.
Have Mystery Devices on Your Factory Network?
Canadian Cyber helps manufacturers identify Shadow OT, review unmanaged devices, control remote access, and build practical governance without slowing operations.
What Is Shadow OT?
Shadow OT is what happens when operational technology is added, modified, connected, or automated outside formal IT and security governance.
It usually starts with good intentions.
The problem is not creativity. The problem is unmanaged connectivity.
Unmanaged OT workarounds can quietly become serious cyber, safety, uptime, and compliance risks.
Why Shadow OT Happens
Shadow OT does not usually begin as rebellion. It begins with pressure.
Manufacturing teams need to keep production moving. Maintenance teams need fast fixes. Operators need better visibility. Vendors need remote access. Engineering needs data. IT is busy. Security approval feels slow.
So people improvise.
| Shadow OT Example | Why It Appears |
|---|---|
| Unmanaged Raspberry Pi devices | Quick monitoring or automation workaround. |
| Spare industrial PCs | Temporary support for production visibility. |
| Unofficial Wi-Fi bridges | Connectivity added where network access is limited. |
| Personal cloud dashboards | Fast reporting without formal tooling. |
| Vendor remote tools installed informally | Troubleshooting pressure and urgent support needs. |
| Legacy devices connected “temporarily” | Temporary fixes become permanent. |
Why Shadow OT Is Risky
Shadow OT creates risk because nobody fully knows what is connected, what it does, and how exposed it is.
Common unknowns include:
- what the device does
- who owns it
- what network it uses
- what data it collects
- who can access it
- whether it is patched
- whether default credentials remain
- whether it connects to the internet
- whether it affects production systems
Blind spots are where incidents begin.
A Common Scenario
A maintenance technician notices that one packaging machine has recurring downtime.
To help, they install a small device that collects vibration and uptime data. It works. The team loves it.
But the device is:
- not in the asset inventory
- connected to the production network
- using default credentials
- sending data to an external dashboard
- accessible through an old vendor account
- never patched
- not monitored by IT
Later, strange network traffic appears. The device has been compromised.
Now the company has to answer:
- What data left the environment?
- Could the attacker reach production systems?
- Did this affect quality records?
- Who approved the device?
- Why was it not monitored?
- How many other devices like this exist?
Need to Find Shadow OT Before It Finds You?
We help manufacturers identify unknown devices, unofficial dashboards, unmanaged controllers, remote tools, and temporary workarounds that became permanent.
What a vCISO Should Do First
A vCISO should not walk into the factory and declare war on every workaround. That will fail.
Instead, the first move is to understand why Shadow OT exists.
Ask:
- What problem was the workaround solving?
- Was the official process too slow?
- Did operations lack approved tools?
- Did IT lack visibility?
- Was there no safe way to request quick innovation?
The goal is not to punish the maintenance team. The goal is to make useful operational improvements safe, visible, and controlled.
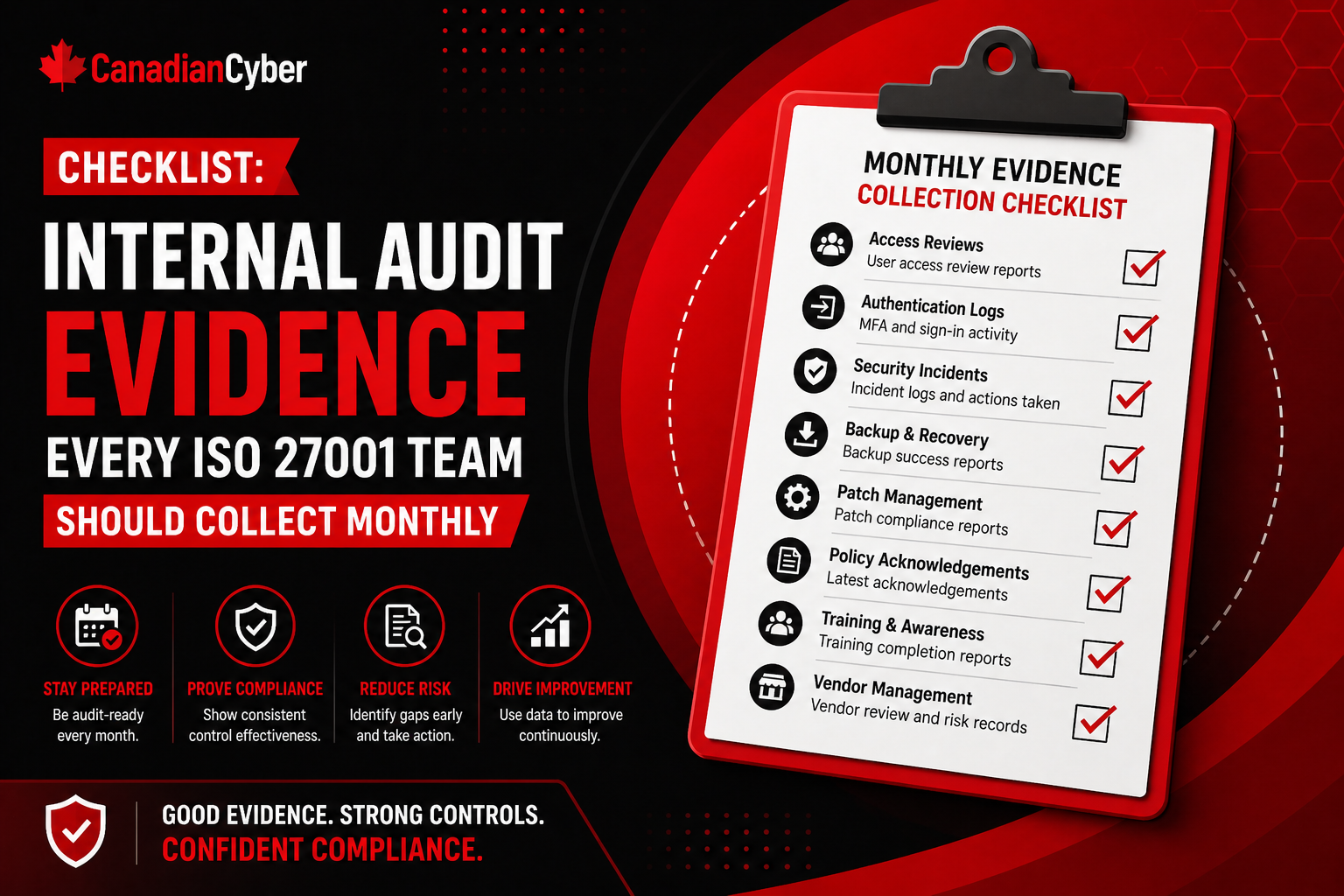
1. Build a Shadow OT Discovery Process
Start with visibility.
Create a lightweight discovery process for:
- unknown devices
- unmanaged controllers
- unofficial monitoring tools
- remote access utilities
- shop-floor tablets
- scripts and automation
- cloud dashboards
- vendor-connected equipment
Use network scans, interviews, walkthroughs, and maintenance records. The first inventory will not be perfect. That is fine. The goal is to start finding what nobody officially owns.
2. Create an OT Asset Register
Every connected OT or shop-floor device should have a record.
| Field | Why It Matters |
|---|---|
| Device name | Identifies the asset. |
| Location | Shows where it operates. |
| Owner | Creates accountability. |
| Purpose | Explains why it exists. |
| Network | Shows exposure. |
| Vendor | Identifies support dependency. |
| Internet access | Shows external risk. |
| Remote access | Shows access risk. |
| Criticality | Helps prioritize. |
| Patch status | Supports maintenance planning. |
This turns mystery devices into managed assets.
Need an OT Asset Register?
Canadian Cyber helps manufacturers build practical OT and IoT asset registers with owners, vendors, network exposure, remote access, criticality, and patch status.
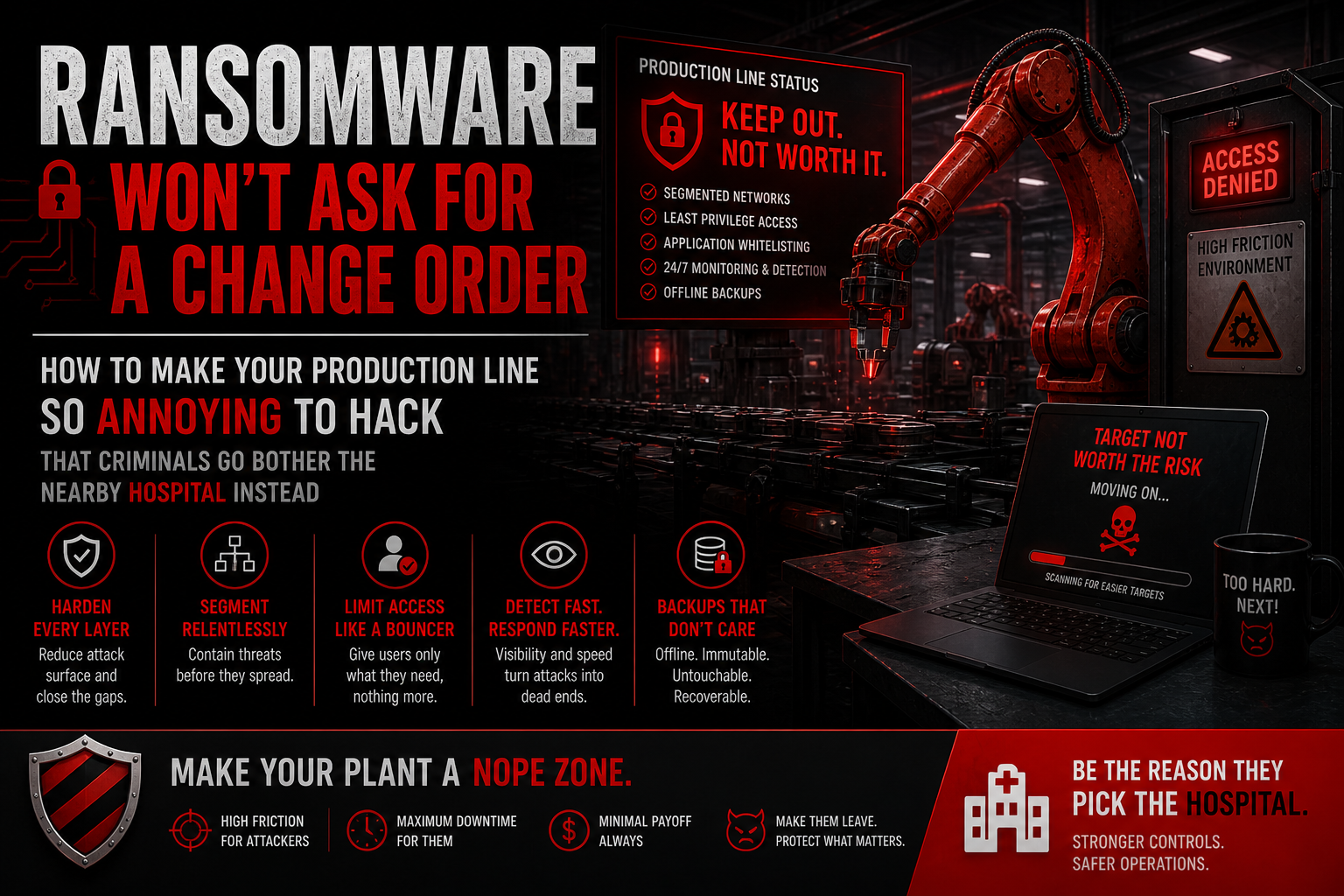
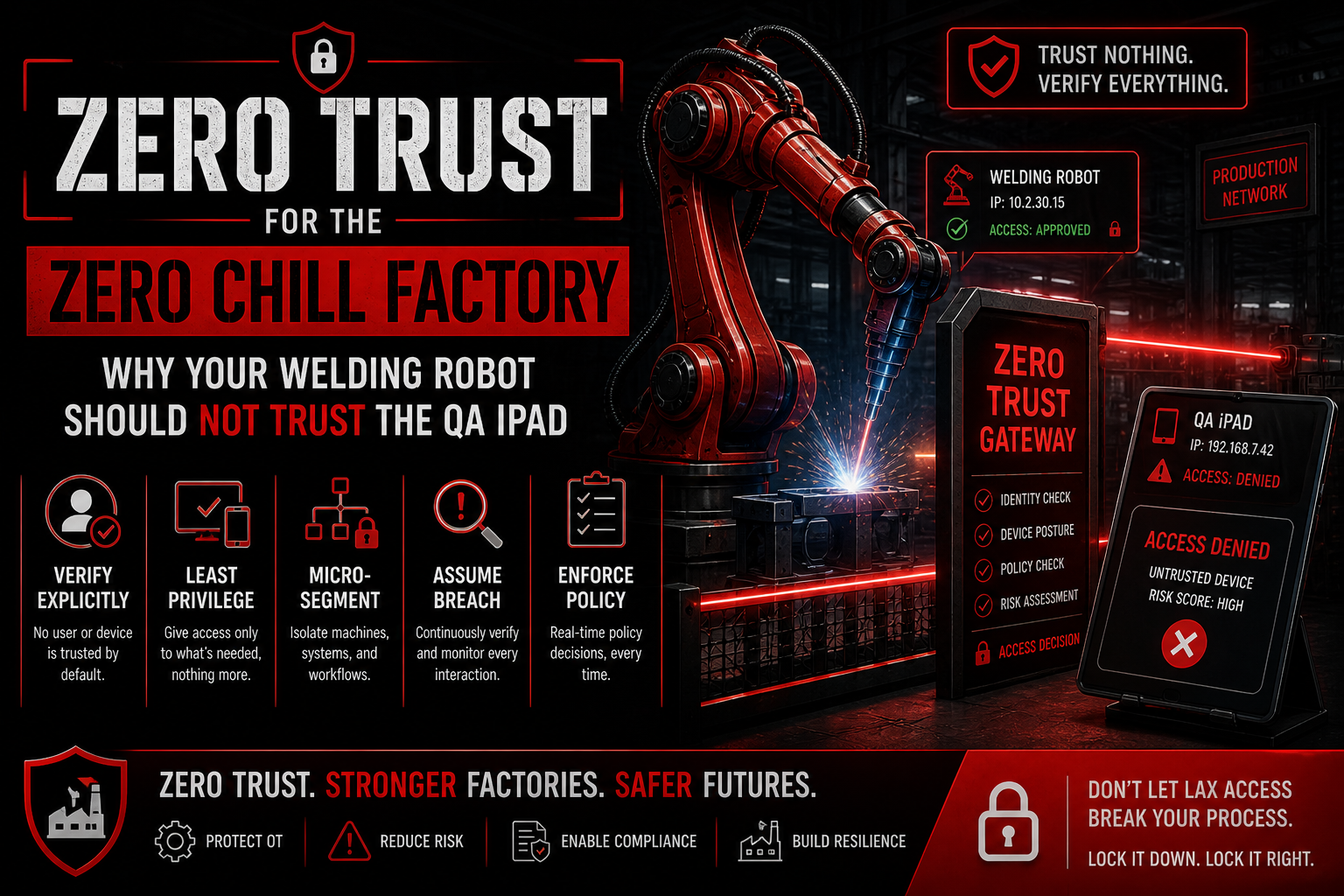
3. Segment the Network
Shadow OT becomes much more dangerous on a flat network.
If an unmanaged device can reach production servers, file shares, ERP systems, or cloud admin tools, the blast radius is too large.
Segment:
- corporate IT
- production OT
- guest Wi-Fi
- vendor access
- engineering workstations
- IoT sensors
- quality systems
- maintenance devices
The maintenance dashboard may need machine data. It does not need access to payroll.
4. Control Remote Access
Many Shadow OT risks involve remote access.
Sometimes it is a vendor tool. Sometimes it is a personal remote desktop app. Sometimes it is an open tunnel nobody remembers creating.
A vCISO should help define rules:
- approved remote access tools only
- MFA where possible
- named accounts only
- no shared vendor accounts
- time-bound access
- logging of sessions
- periodic review
- immediate removal when no longer needed
Remote access should never be invisible.
5. Create a Safe Path for Innovation
This is the most important cultural point.
If the official process is too slow, Shadow OT will come back.
Give operations a safe way to propose improvements, such as:
- quick review form for new shop-floor devices
- approved device standards
- pre-approved network zones
- fast-track security review for low-risk pilots
- vendor access checklist
- temporary exception process
- expiry dates for experimental setups
6. Watch for Strange Behavior
Shadow OT detection should include monitoring for unusual activity.
Watch for:
- unknown devices
- unusual outbound traffic
- unexpected internet connections
- crypto-mining indicators
- unauthorized remote access tools
- odd communication between IT and OT networks
- new devices appearing outside approved windows
- suspicious traffic from production equipment
The earlier you detect abnormal behavior, the easier it is to contain.
What Manufacturers Usually Get Wrong
- Ignoring unknown devices because production is working: Functioning equipment can still be risky.
- Blaming maintenance instead of fixing the approval process: Shadow OT often points to a process gap.
- Allowing flat networks: Flat networks increase blast radius.
- Trusting vendor tools too much: Vendor access still needs governance.
- Skipping OT asset inventory: Unknown assets cannot be properly protected.
- Leaving temporary devices permanent: Temporary fixes need expiry dates.
- Treating crypto-mining as an IT issue only: It may indicate broader OT exposure.
- Excluding OT from incident response planning.
Turn Shadow OT Into Managed OT
Canadian Cyber helps manufacturers discover unmanaged devices, assess Shadow OT risks, plan segmentation, govern vendor access, and track remediation actions.
Canadian Cyber’s Take
At Canadian Cyber, we often see Shadow OT appear because operational teams are trying to solve real problems quickly.
That creativity is valuable. But connected devices need governance.
A practical vCISO approach should balance:
- operational speed
- production uptime
- device visibility
- network segmentation
- vendor control
- remote access governance
- incident readiness
The goal is not to stop better mousetraps. The goal is to make sure the mousetrap does not become a backdoor, a data leak, or a crypto miner.
Takeaway
Shadow OT is not just an inventory problem. It is a governance problem.
Manufacturers need to know:
- what is connected
- who owns it
- why it exists
- what it can access
- who can reach it remotely
- whether it is behaving normally
Your maintenance team should be able to improve the factory. They just should not accidentally build the next unmanaged attack path.
How Canadian Cyber Can Help
At Canadian Cyber, we help manufacturers identify and control Shadow OT before it becomes a production or security incident.
- vCISO services for manufacturing
- OT and IoT asset discovery
- vendor remote access governance
- network segmentation planning
- Shadow OT risk reviews
- incident response tabletop exercises
- SharePoint-based risk and action tracking
Stay Connected With Canadian Cyber
Follow Canadian Cyber for practical guidance on Shadow OT, manufacturing cybersecurity, IoT risk, OT security, vendor access, and vCISO support.