Manufacturing Cybersecurity • IoT Security • vCISO
The Great Sausage Hack: Why Your Factory’s IoT Smoker Is Crying for Help
Connected factory equipment can create real cyber, operational, and compliance risk when IoT devices, vendor access, and production networks are not properly governed.
Quick Snapshot
| Factory Risk Area | Why It Matters |
|---|---|
| IoT Devices | Connected smokers, sensors, dashboards, and production equipment can become unmanaged entry points. |
| Vendor Access | Remote support accounts can create hidden risk if they are shared, unmanaged, or always active. |
| Production Continuity | Device failures or tampering can affect uptime, quality records, food safety, and customer deliveries. |
| vCISO Support | A vCISO helps bring structure to IoT, OT, vendor access, segmentation, monitoring, and incident readiness. |
Introduction
It starts with one innocent machine.
- An IoT smoker in the production area.
- Connected for temperature monitoring.
- Integrated with maintenance alerts.
- Accessible through a vendor portal.
- Forgotten by everyone except operations.
Your IoT smoker may not look like a cybersecurity risk, but if it is connected, unmanaged, and vendor-accessible, it can become a very real threat to production.
Your factory is no longer just machines, people, and production schedules. It is sensors, cloud dashboards, remote support tools, vendor accounts, IoT devices, wireless networks, ERP integrations, maintenance apps, and connected equipment that nobody remembers adding to the asset inventory.
Is Connected Equipment Creating Hidden Risk?
Canadian Cyber helps manufacturers identify IoT, OT, vendor access, and production network risks before they become operational disruptions.
Why This Is Not as Funny as It Sounds
The idea of a hacked sausage smoker sounds ridiculous.
Until you think about what connected factory equipment can affect:
- production quality
- food safety
- uptime
- maintenance schedules
- temperature records
- compliance evidence
- vendor access paths
- operational continuity
The sausage smoker is funny. The risk is not.
If connected equipment fails, production may stop. If temperature logs are unreliable, quality evidence may be questioned. If remote access is abused, attackers may move deeper into the environment. If production data is altered, trust suffers.
A Common Scenario
Picture this: a food manufacturer uses connected equipment across the facility.
The environment includes:
- IoT smokers
- refrigeration sensors
- packaging equipment
- production dashboards
- ERP systems
- vendor remote access
- quality monitoring tools
- maintenance tablets
- Wi-Fi networks
- cloud reporting portals
Everything was added for good reasons: better visibility, faster maintenance, less downtime, and improved quality control.
But nobody owns the full security picture.
Then a connected smoker starts behaving oddly. Now the questions begin:
- Who owns this device?
- Is it patched?
- Which network is it on?
- Does the vendor still have remote access?
- Are default credentials still active?
- Is it logging properly?
- Could it reach other systems?
- Is production evidence still reliable?
Why IoT Devices Become Factory Weak Points
Industrial IoT devices often become risky because they sit between two worlds.
They are operational enough that production depends on them. But they are connected enough that cybersecurity matters.
| Common Weakness | Why It Creates Risk |
|---|---|
| Default passwords | Attackers or unauthorized users may gain easy access. |
| Outdated firmware | Known vulnerabilities may remain exposed. |
| Weak vendor access controls | Remote access can become an unmanaged pathway into production. |
| Poor network segmentation | One compromised device may reach systems it should never touch. |
| No asset ownership | Nobody is accountable for updates, access, or monitoring. |
| Limited logging | Suspicious activity may not be detected quickly. |
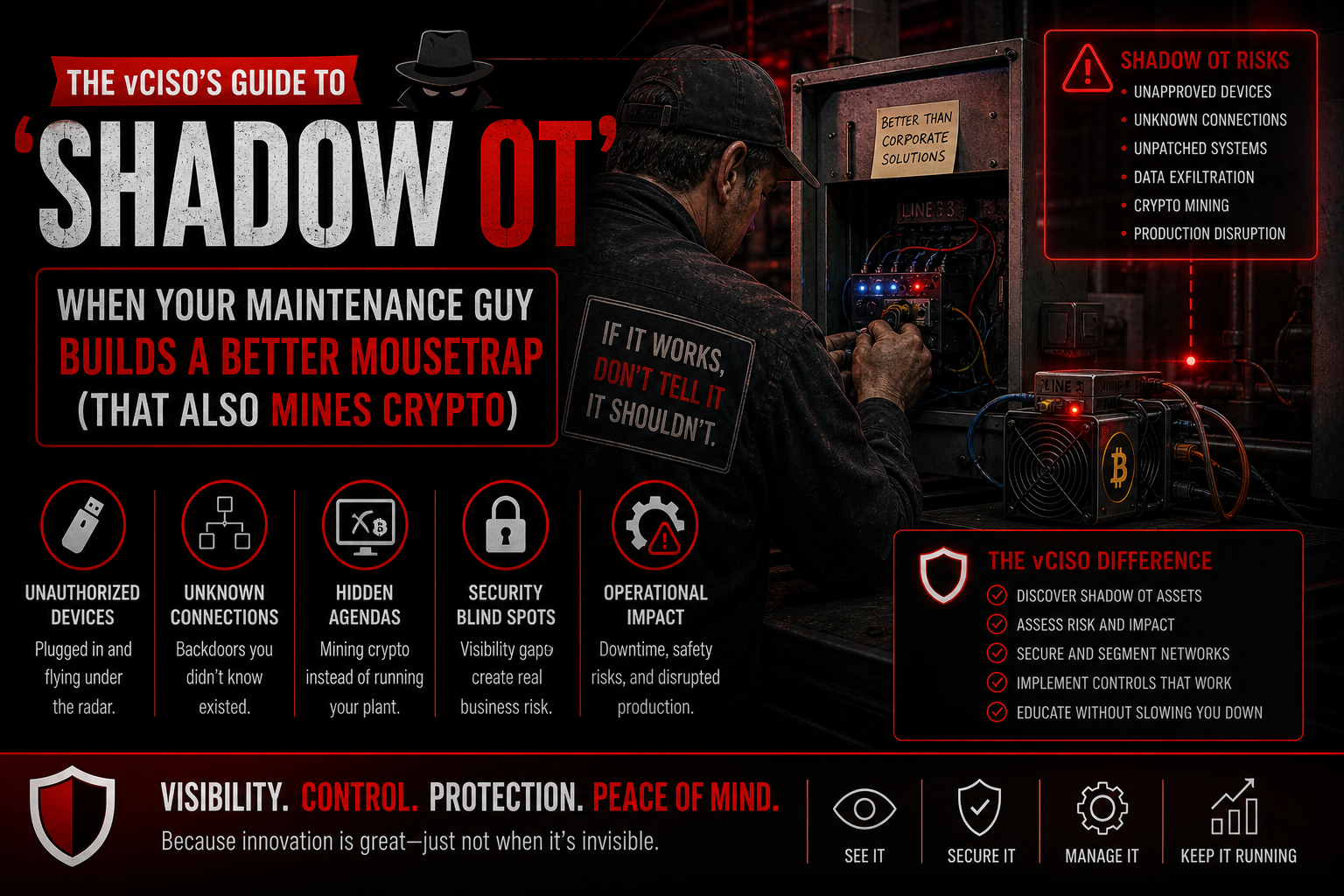
Where the vCISO Comes In
A vCISO helps connect the dots.
Not by telling production teams to stop using connected equipment. And not by creating paperwork that slows the line.
A good vCISO helps the business ask:
- What connected equipment do we have?
- Which systems are production-critical?
- Which vendors can access them?
- What networks are they on?
- What happens if they fail?
- Which devices need stronger controls first?
- How do we reduce risk without disrupting operations?
Need Security Leadership for Connected Operations?
Canadian Cyber provides vCISO support for manufacturers that need practical oversight of IoT, OT, vendors, production systems, and cyber maturity.
1. Build an IoT and OT Asset Inventory
The first step is visibility.
You cannot secure the smoker if nobody knows it exists.
| Inventory Field | Why It Matters |
|---|---|
| Device name | Identifies the asset |
| Location | Shows where it operates |
| Owner | Assigns accountability |
| Vendor | Shows support dependency |
| Network | Shows exposure |
| Remote access | Identifies access risk |
| Criticality | Helps prioritize |
| Firmware status | Supports patch planning |
The goal is not perfection on day one. The goal is to stop managing connected equipment from memory.
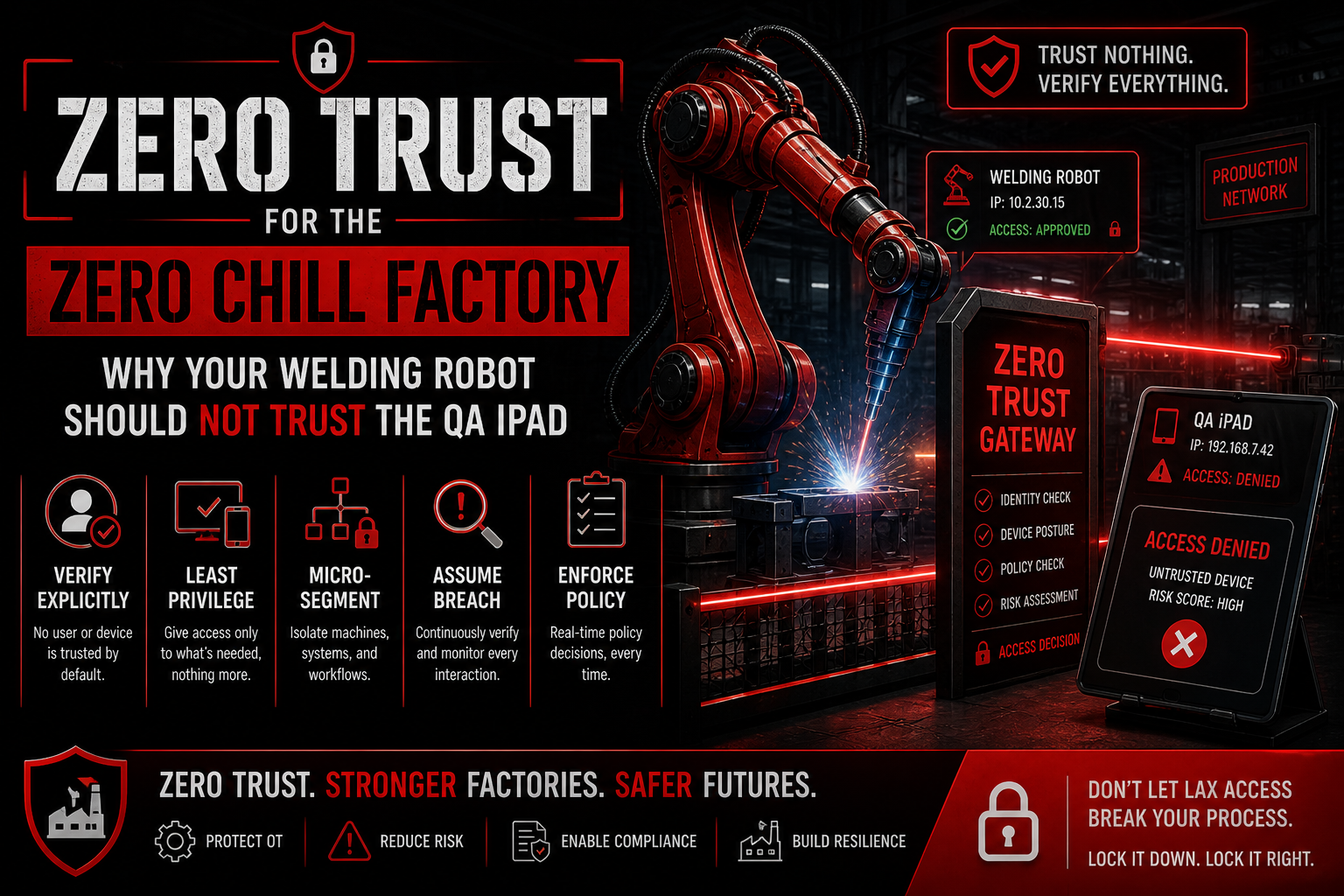
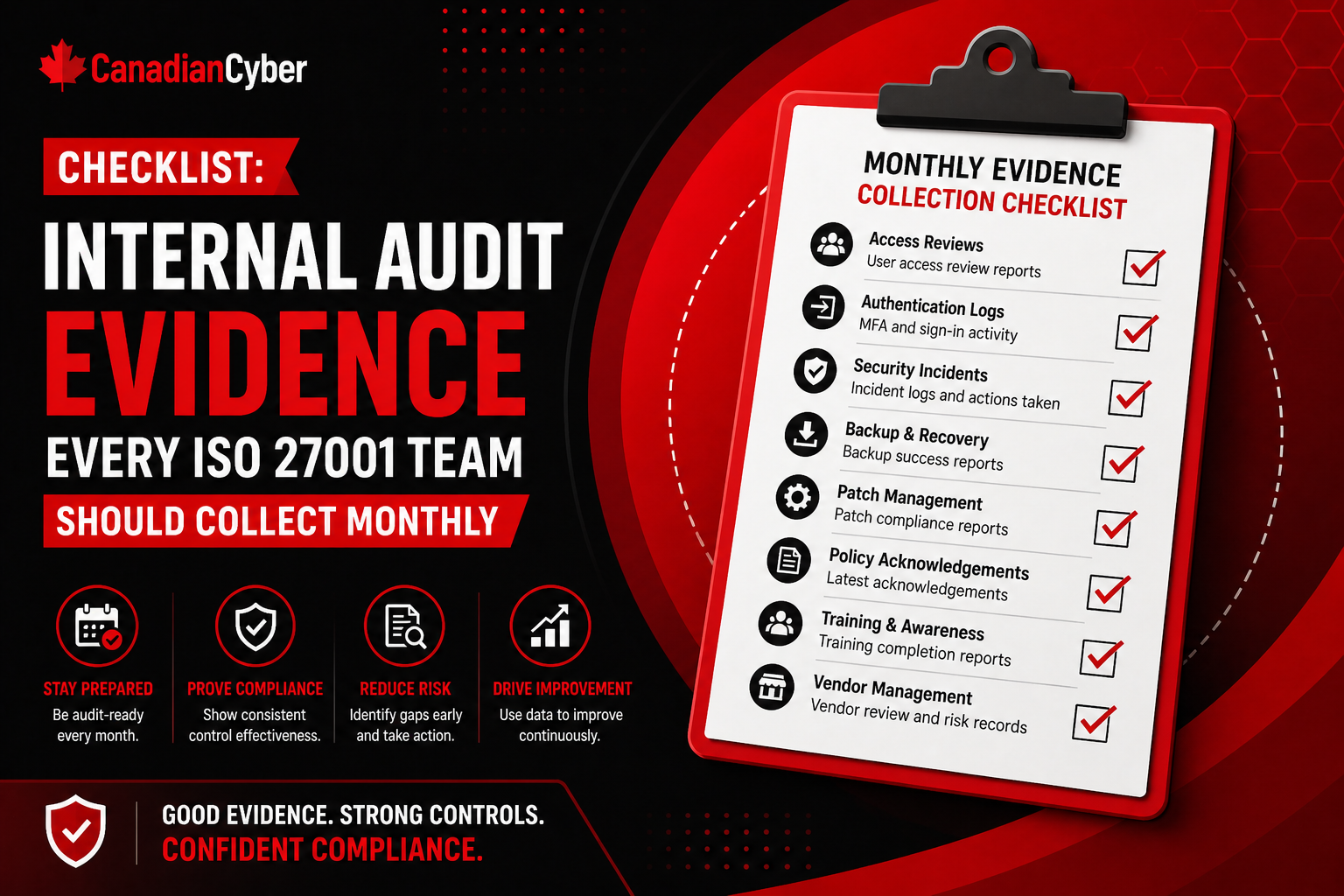
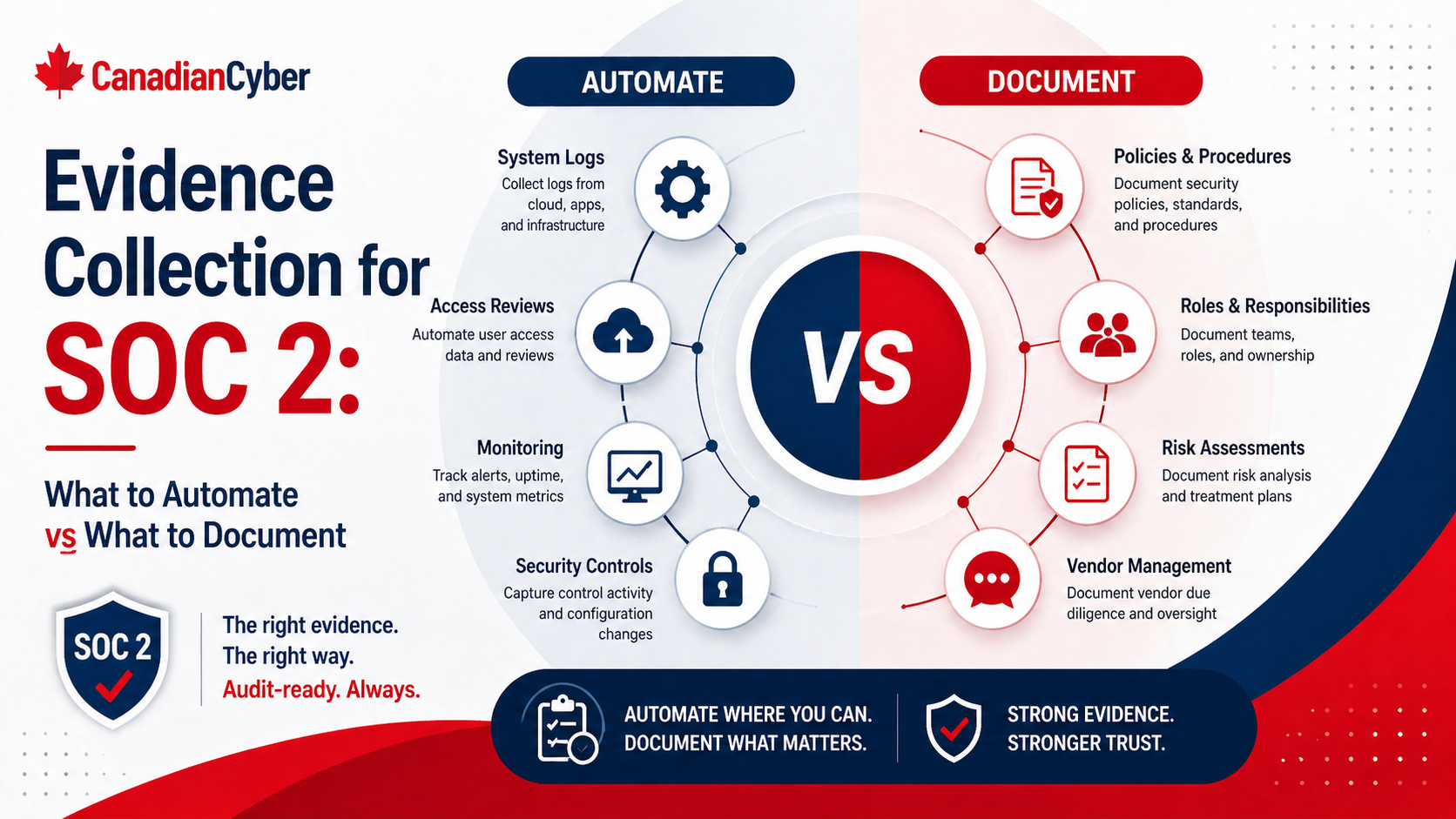
2. Review Vendor Remote Access
Many factory IoT risks come from vendor access.
Vendors may need access for maintenance, diagnostics, updates, and support. That is normal. But vendor access should not be uncontrolled.
A vCISO helps define rules such as:
- named vendor accounts only
- MFA where possible
- time-bound access
- approval before remote sessions
- logging of vendor activity
- removal of inactive vendor accounts
- regular review of vendor access
This protects operations without blocking legitimate support.
3. Segment the Factory Network
Your IoT smoker should not have the same network freedom as finance systems, HR files, or domain admin tools.
Network segmentation helps limit damage if one device is compromised.
A better model separates:
- guest Wi-Fi
- corporate systems
- production equipment
- vendor remote access
- critical servers
- monitoring tools
Segmentation does not need to be perfect immediately. But the most critical devices should not sit on a flat network with everything else.
Is Your Factory Network Too Flat?
We help manufacturers plan practical segmentation that separates production equipment, vendor access, corporate systems, and critical services.
4. Patch and Configure Devices Properly
Many IoT devices are installed once and forgotten. That creates long-term risk.
A vCISO helps create a practical process for:
- firmware review
- vendor security updates
- password changes
- default account removal
- configuration baselines
- patch testing before production deployment
- maintenance windows
For manufacturing, patching must be planned carefully. Security should support uptime, not surprise operations with risky changes.
5. Monitor What Matters
Not every IoT device will produce perfect security logs.
But production-critical connected systems should still have some monitoring strategy.
This may include:
- network activity monitoring
- remote access logs
- vendor login records
- device health alerts
- configuration change records
- production anomaly reporting
The goal is to notice strange behavior before it becomes a production crisis.
6. Plan for Production Disruption
If the IoT smoker fails, what happens?
A vCISO helps operations and leadership plan for scenarios like:
- device outage
- vendor portal compromise
- ransomware affecting production systems
- loss of temperature records
- suspicious remote access
- network isolation of production equipment
- recovery from backup or manual process
This turns cybersecurity into operational resilience.
What Manufacturers Usually Get Wrong
- Treating IoT devices as “operations only”: If a device is connected, cybersecurity matters.
- Assuming vendors handle security: Vendor support does not replace internal oversight.
- Leaving default credentials in place: Default accounts create avoidable exposure.
- Failing to inventory connected equipment: You cannot protect what you do not know exists.
- Using flat production networks: Segmentation helps contain problems.
- Ignoring remote access logs: Vendor activity should be visible and reviewed.
- Waiting until disruption happens to assign ownership.
Don’t Wait for the Great Sausage Hack
Canadian Cyber helps manufacturers build practical roadmaps for IoT visibility, vendor access, segmentation, monitoring, and incident response.
Canadian Cyber’s Take
At Canadian Cyber, we often see manufacturers with strong operational discipline but weaker visibility into connected equipment risk.
The issue is not that teams are careless. It is that IoT and OT environments often grow quietly.
A sensor here. A vendor portal there. A connected smoker. A remote maintenance account. A cloud dashboard.
Before long, the factory has a cyber risk surface nobody fully owns.
A vCISO helps bring structure to that environment by focusing on asset visibility, access control, vendor risk, network segmentation, monitoring, and incident readiness. That is how you protect production without turning security into a bottleneck.
Takeaway
The hacked sausage smoker may sound funny.
But connected factory equipment can create real cyber, operational, and compliance risk.
Manufacturers should treat IoT and OT security as part of business resilience, especially when devices affect:
- production uptime
- quality records
- vendor access
- food safety
- operational continuity
- customer delivery commitments
National Sausage Day should be remembered for great sausage, not for the day your IoT smoker became the weakest link.
How Canadian Cyber Can Help
At Canadian Cyber, we help manufacturers secure connected operations without slowing production.
- vCISO services for manufacturing
- IoT and OT asset reviews
- vendor remote access governance
- network segmentation planning
- incident response and tabletop exercises
- SharePoint-based risk and evidence tracking
- ISO 27001 and cyber maturity readiness
Stay Connected With Canadian Cyber
Follow Canadian Cyber for practical guidance on manufacturing cybersecurity, IoT risk, OT security, vCISO support, vendor access, and cyber maturity.