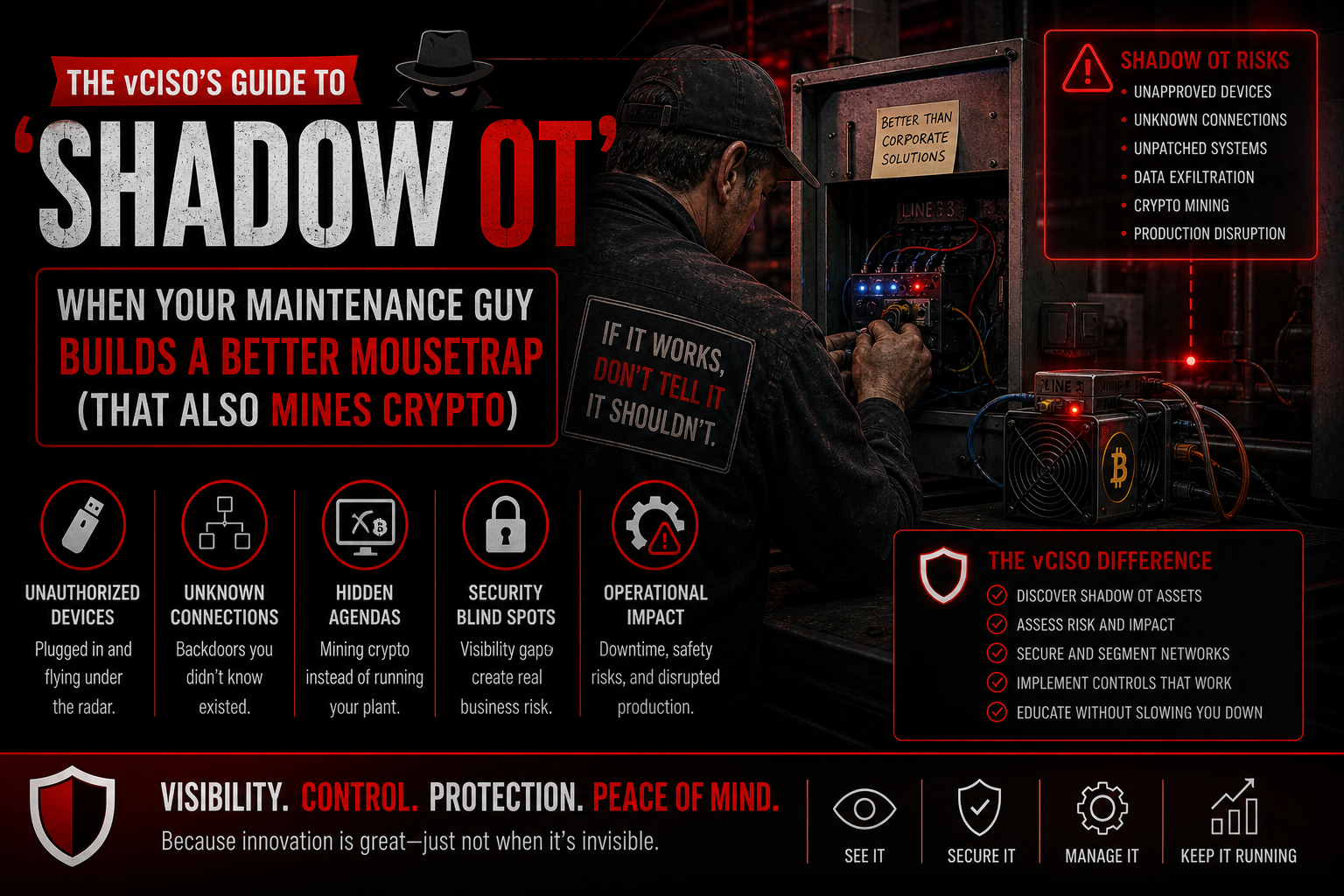
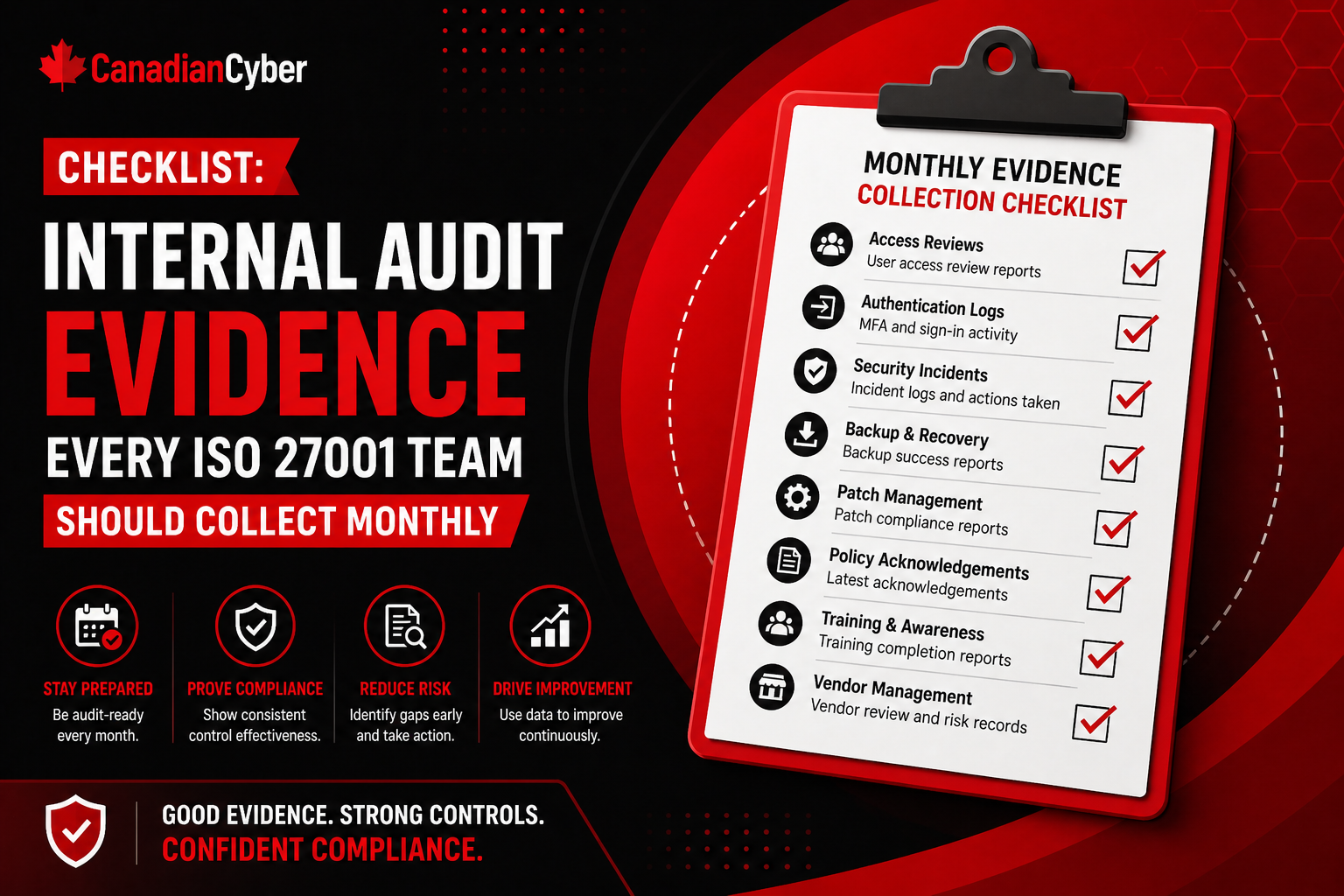
Manufacturing Cybersecurity • Ransomware Readiness • vCISO
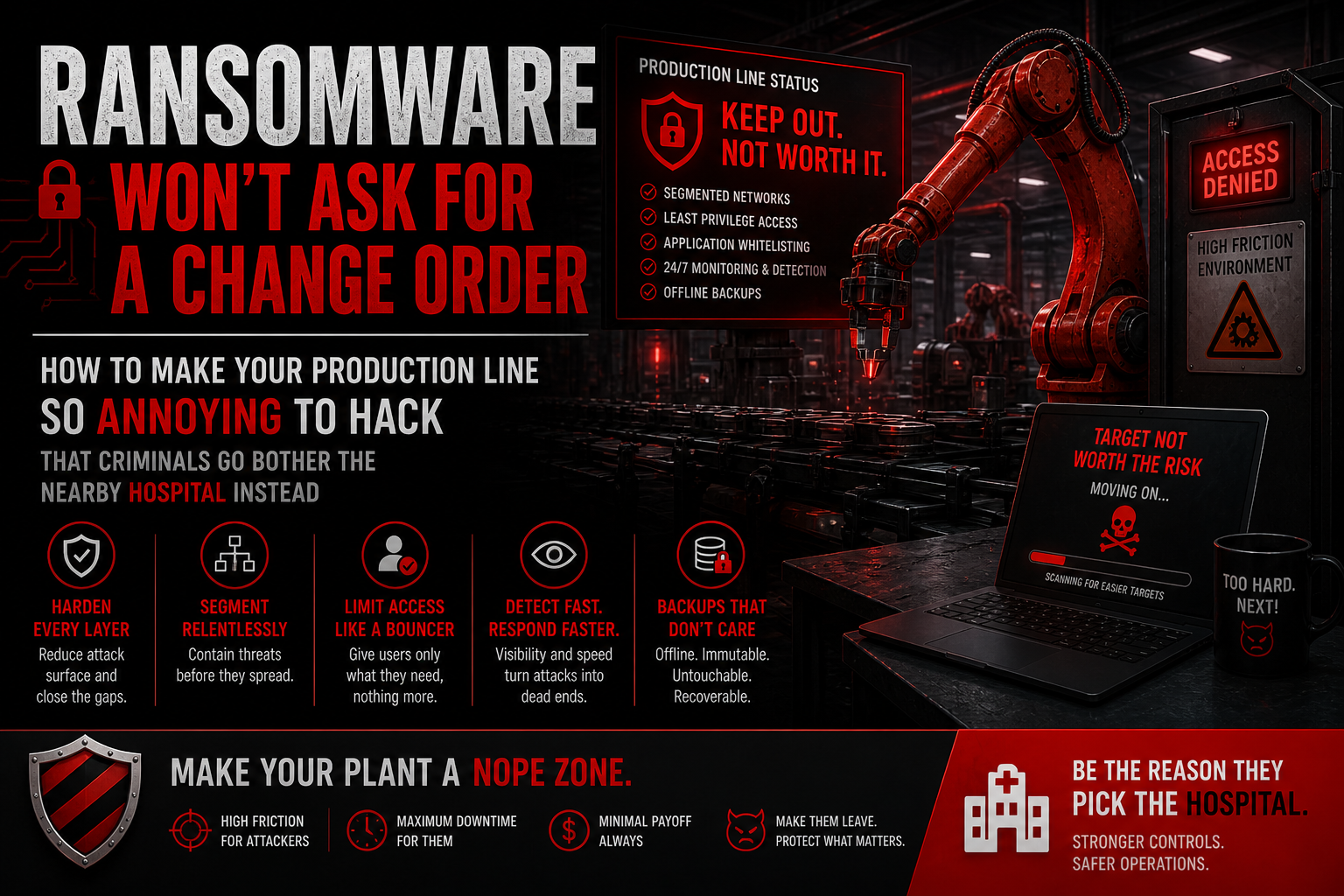
Ransomware Won’t Ask for a Change Order: How to Make Your Production Line So Annoying to Hack That Criminals Move On
Manufacturers do not need perfect security. They need controlled, segmented, monitored, and recoverable environments that make ransomware operators work too hard for too little reward.
Quick Snapshot
| Ransomware Defense Area | Manufacturing Priority |
|---|---|
| Segmentation | Stop one compromised laptop from reaching production systems, ERP, backups, and OT devices. |
| Remote Access | Control vendor access with MFA, named accounts, approval, time limits, logging, and review. |
| Backups | Protect backups with restricted admin access, immutability, monitoring, and restore testing. |
| Response | Practice ransomware scenarios before systems are down and decisions are urgent. |
Introduction
Ransomware does not care about your production schedule.
- It will not ask for a change order.
- It will not wait for maintenance weekend.
- It will not respect shipping deadlines.
- It will not pause because the line is running at capacity.
Your goal is not to become impossible to hack. Your goal is to make ransomware operators work so hard, move so slowly, and gain so little that your factory is not worth the effort.
If attackers get into a manufacturing environment, they are looking for leverage. Few things create leverage faster than a stopped production line.
Why Manufacturing Is a Ransomware Target
Manufacturers are attractive because downtime is expensive.
Attackers know that if they disrupt:
- production systems
- ERP
- scheduling
- shipping
- quality records
- engineering files
- vendor access
- backups
- plant-floor operations
the business feels pressure quickly. That pressure is exactly what ransomware groups want.
Attackers do not need to understand every machine on the floor. They just need enough access to create chaos.
The Production Line Problem
Factories often have a messy mix of old and new systems.
| Factory Environment Reality | Why It Creates Ransomware Risk |
|---|---|
| Old machines | May be hard to patch or monitor. |
| New IoT devices | May be connected before security review. |
| Vendor portals | Can become unmanaged remote access paths. |
| Flat networks | Let attackers move quickly. |
| Shared accounts | Make abuse harder to trace. |
| Office systems connected to operations | Allow IT-side compromise to affect production. |
A ransomware attack might start with a phishing email in the office and end with production systems unavailable. That is why factory cybersecurity cannot stay limited to IT.
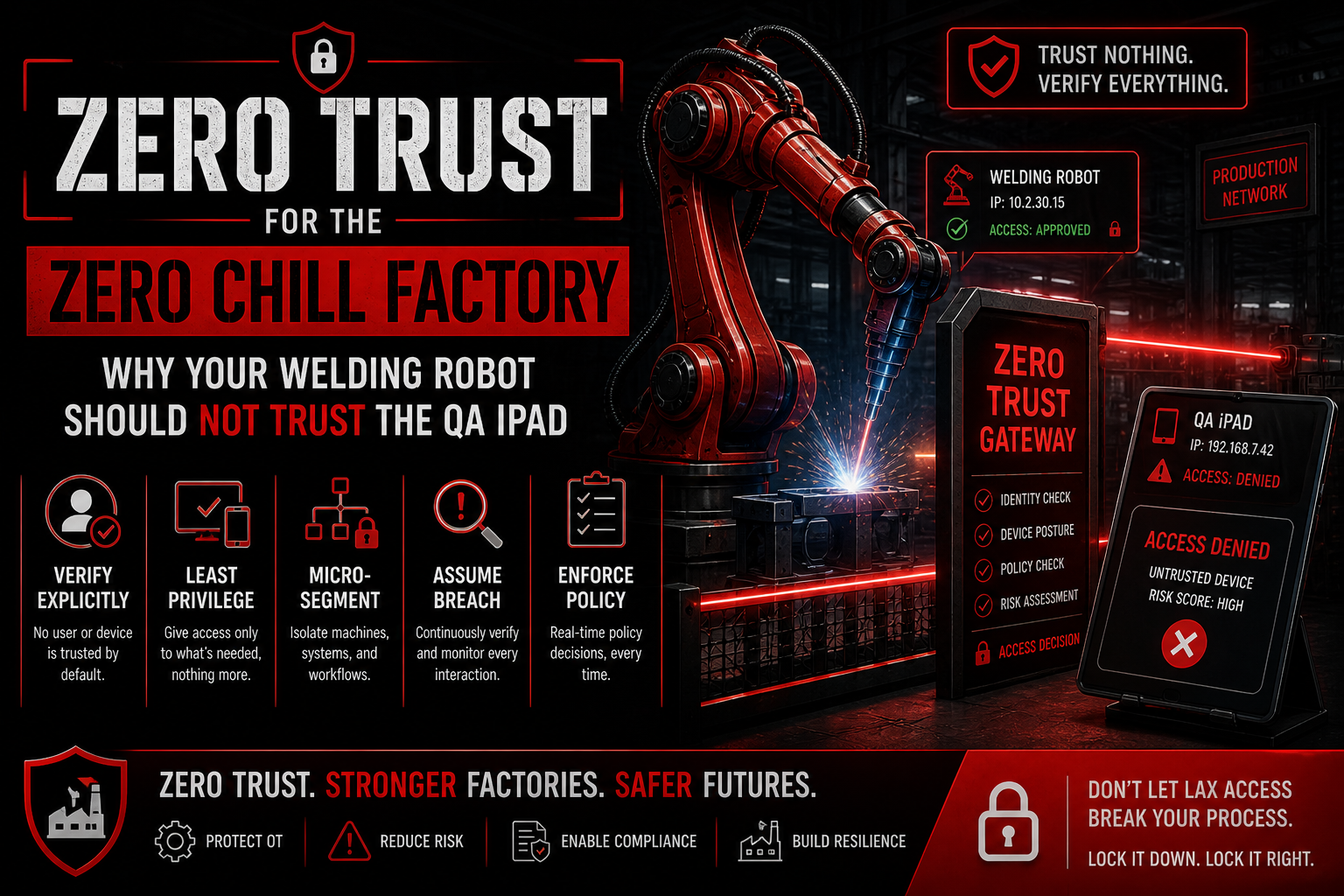
1. Segment the Network Before Attackers Do It for You
A flat network is a gift to ransomware.
If one compromised laptop can reach file shares, ERP, engineering systems, and plant-floor devices, attackers can move quickly.
Segment:
- corporate IT
- production OT
- guest Wi-Fi
- vendor access
- engineering workstations
- backup systems
- quality systems
- critical servers
A compromised office laptop should not have a free road to the production line.
2. Lock Down Remote Access
Ransomware loves remote access, especially when it is shared, always on, poorly logged, missing MFA, used by vendors, or forgotten after installation.
Manufacturers should require:
- MFA for remote access
- named accounts
- time-limited vendor access
- approval before remote sessions
- session logging
- regular review of active accounts
- removal of unused access
Vendor access should be treated like a controlled doorway, not a permanently open side entrance.
3. Protect Backups Like They Are the Last Copy of the Factory
Ransomware often tries to destroy or encrypt backups first.
So backups need stronger protection.
Focus on:
- offline or immutable backups
- restricted backup admin access
- separate credentials
- regular restore testing
- backup monitoring
- documented recovery priorities
A backup is only useful if you can restore it.
Manufacturers should test recovery for critical systems before a crisis, not during one.
When Was Your Last Real Restore Test?
We help manufacturers review backup protection, recovery priorities, restore testing, backup admin access, and ransomware recovery evidence.
4. Remove Easy Admin Paths
Attackers love excessive privileges.
Review:
- domain admins
- local admins
- cloud admins
- ERP admins
- vendor admins
- shared service accounts
- old contractor accounts
Reduce standing access wherever possible. Use least privilege. Make admin access harder to steal, harder to abuse, and easier to trace.
5. Patch What You Can, Isolate What You Cannot
Manufacturing environments often include systems that cannot be patched easily.
That is reality. But “cannot patch” should not mean “ignore forever.”
For legacy systems:
- isolate them
- restrict access
- monitor traffic
- remove internet exposure
- document compensating controls
- plan replacement where needed
If a system is too fragile to patch, it is too fragile to leave exposed.
6. Train People for Factory-Relevant Attacks
Generic security training is not enough.
Manufacturing staff should recognize risks like:
- fake vendor emails
- malicious invoices
- remote support scams
- suspicious USB devices
- fake maintenance requests
- phishing targeting supervisors
- unusual system prompts
- unexpected production alerts
Training should match how the factory actually works.
7. Monitor the Weird Stuff
Ransomware often creates warning signs before full impact.
Watch for:
- unusual login times
- failed admin logins
- new remote access tools
- large file transfers
- strange traffic between IT and OT
- disabled security tools
- backup deletion attempts
- new unknown devices
- unusual vendor account activity
You do not need perfect visibility on day one. But you need enough visibility to notice when something is wrong.
8. Practice the Bad Day
A ransomware plan that has never been tested is mostly hope.
Run a tabletop exercise with:
- IT
- OT
- operations
- maintenance
- legal
- communications
- leadership
- vendors where appropriate
Test scenarios like:
- ransomware on office systems
- ERP unavailable
- production scheduling down
- vendor remote access compromise
- backup restore failure
- plant network isolation decision
The key question is: can the business keep making decisions when systems are down and facts are incomplete?
What Manufacturers Usually Get Wrong
- Assuming OT is isolated when it is not: Verify the network, do not guess.
- Allowing vendors too much access: Remote access needs strict control.
- Not testing restores: Backup confidence must be proven.
- Relying on shared admin accounts: Shared accounts weaken accountability.
- Ignoring old machines: Legacy systems need isolation and compensating controls.
- Treating ransomware as only an IT issue: Operations must be involved.
- Leaving recovery plans on systems that may be encrypted: Keep response materials accessible during an outage.
- Failing to involve leadership before the crisis.
Make Your Factory Annoying to Hack
Canadian Cyber helps manufacturers make ransomware attacks slower, harder, less profitable, and easier to recover from.
Canadian Cyber’s Take
At Canadian Cyber, we often see manufacturers with strong operational discipline but weak ransomware resilience.
The factory knows how to manage quality, safety, uptime, and maintenance. Cybersecurity needs the same operational mindset.
That means:
- clear ownership
- controlled access
- tested recovery
- segmented systems
- vendor discipline
- practical incident drills
- evidence that controls actually work
Ransomware will always look for the easiest path. Your job is to make that path painful.
Takeaway
Ransomware will not ask for a change order.
It will hit when it can, move where it is allowed, and pressure the business where downtime hurts most.
Manufacturers can reduce that risk by making the environment harder to attack:
- segment the network
- control remote access
- protect and test backups
- reduce admin privileges
- isolate legacy systems
- train staff on real factory threats
- monitor suspicious behavior
- practice ransomware response
The best ransomware defense is not one magic tool. It is making your production environment so controlled, segmented, monitored, and recoverable that attackers decide it is not worth the trouble.
How Canadian Cyber Can Help
At Canadian Cyber, we help manufacturers improve ransomware resilience without slowing production.
- ransomware readiness assessments
- OT and IoT security reviews
- network segmentation planning
- vendor remote access governance
- backup and recovery testing
- incident response tabletop exercises
- vCISO support for manufacturing security
Stay Connected With Canadian Cyber
Follow Canadian Cyber for practical guidance on ransomware readiness, manufacturing cybersecurity, OT security, vendor access, backup recovery, and vCISO support.