ISO 27001 Control 5.23 cloud services requires clear governance, vendor review, configuration security, and ongoing monitoring. Use this audit-ready script and evidence checklist to prepare clean, defensible proof.
ISO/IEC 27002:2022 • Control 5.23 • Internal Audit–Ready
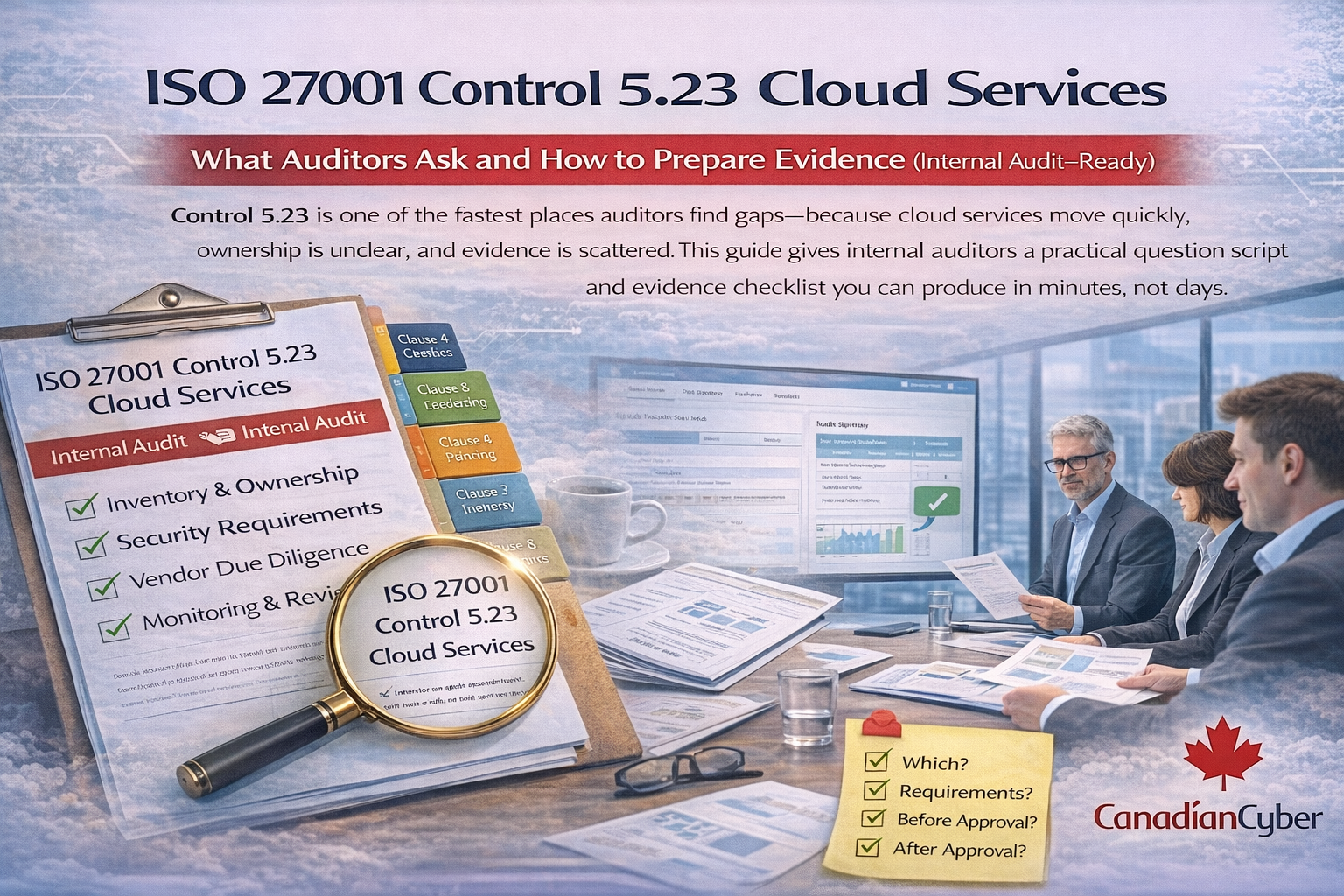
Control 5.23 is one of the fastest places auditors find gaps because cloud services move quickly, ownership is unclear, and evidence is scattered.
This guide gives internal auditors a practical question script and an evidence checklist you can produce in minutes, not days.
ISO/IEC 27002:2022 Control 5.23 (Information security for use of cloud services) expects the organization to define, implement, and monitor information security requirements when using cloud services.
Internal audits often surface the same issues:
Auditors are looking for proof that you can answer these four questions:
If you prepare only one thing, prepare this 5.23 evidence pack. It makes internal audits smooth and repeatable.