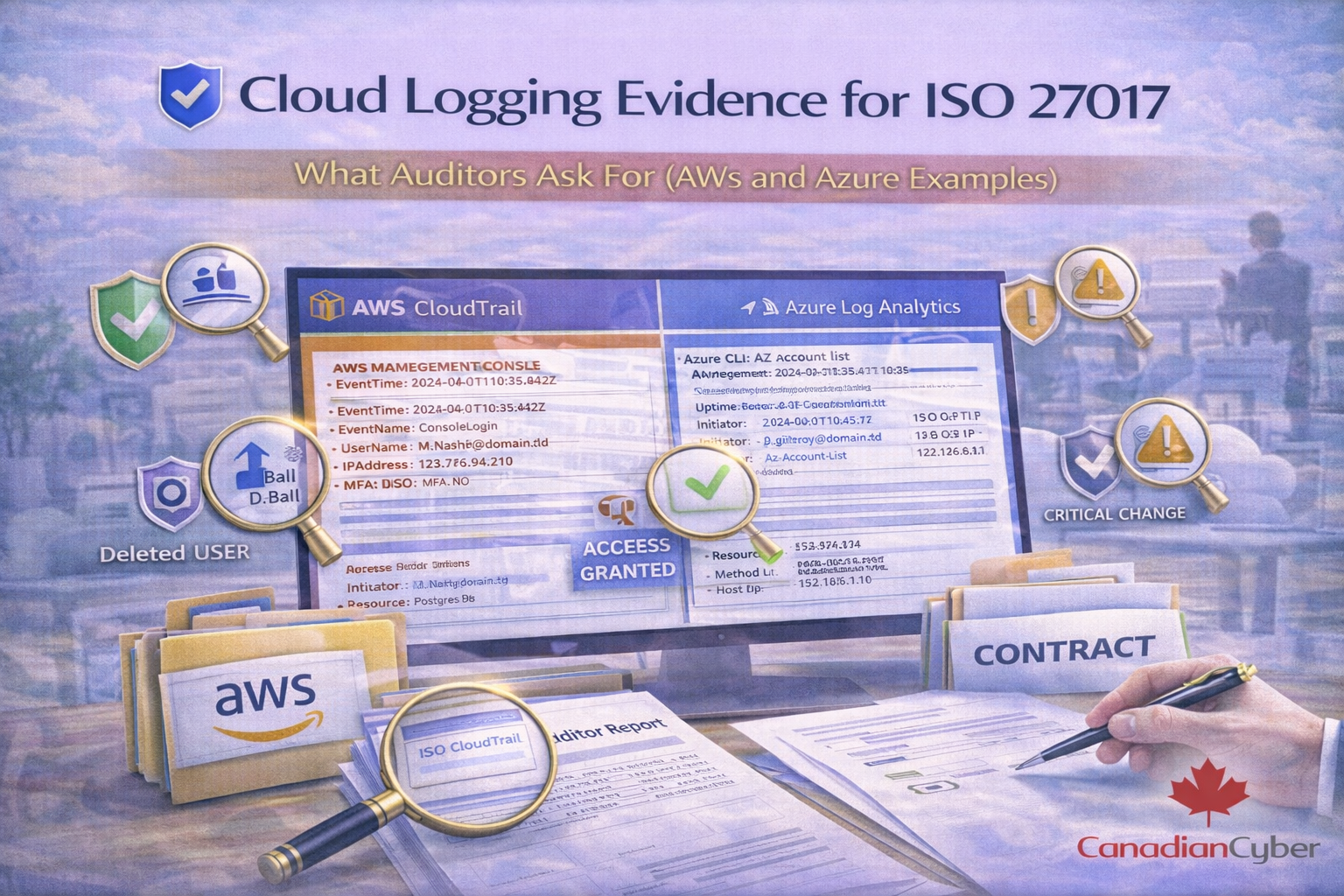
A practical guide to ISO 27017 cloud logging evidence using AWS and Azure examples. Learn what auditors actually ask for—logging coverage, integrity protection, monitoring alerts, and retention—and how to package cloud logging proof in an audit-ready evidence pack.
ISO 27017 doesn’t just want “we have logging.” It wants proof that cloud logging is enabled, protected, reviewed, and acted on matching your shared-responsibility model.
This guide shows exactly what auditors ask for, what evidence to collect, and how to package it cleanly in SharePoint using practical AWS and Azure examples.
ISO 27017 adds cloud-specific expectations around shared responsibility, administrative activity tracking, account/subscription governance, and continuous monitoring.
So “we have logs” is not enough. Auditors want evidence that logging is a working control.
If you prepare only one thing, prepare this cloud logging evidence pack.
These are the AWS log sources auditors ask about most, with evidence ideas that stand up in audits.
Use a consistent folder structure and tag each file with metadata (control ID, period, system, owner, approval).