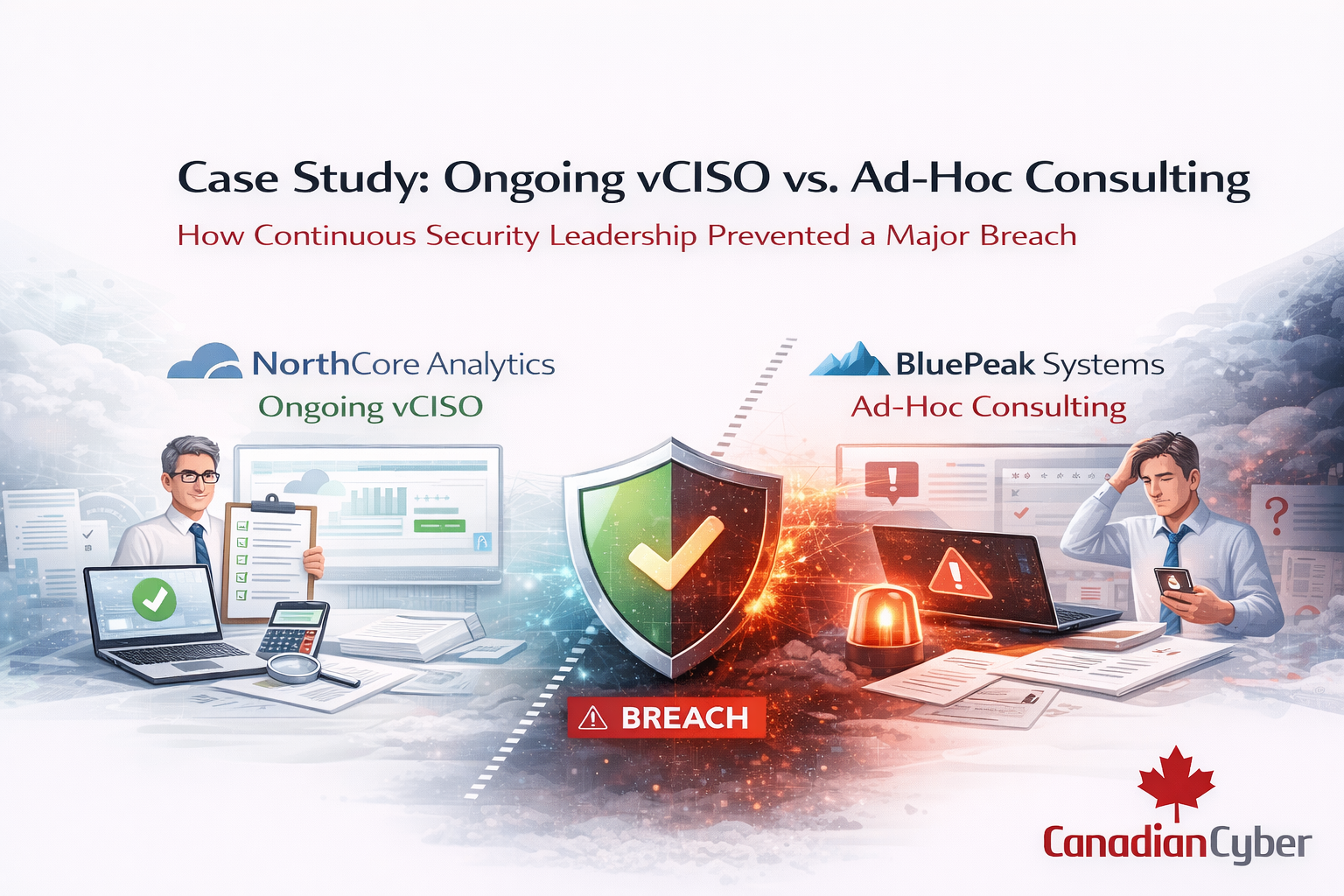
Case Study: Ongoing vCISO vs. Ad-Hoc Consulting
How Continuous Security Leadership Prevented a Major Breach
There were two companies.
Both were Canadian. Both were growing SaaS providers. Both handled sensitive customer data. Both believed they were “secure enough.”
But only one avoided a breach.
This is the story of what made the difference.
Meet the Two Companies
NorthCore Analytics – 65 employees, B2B SaaS
BluePeak Systems – 70 employees, similar product, similar growth
On paper, they looked identical.
• AWS + Microsoft 365
• MFA enabled
• Documented policies
• Basic vulnerability scanning
• Enterprise clients requesting SOC 2
But their approach to security leadership was very different.
The Key Difference
BluePeak Systems
• Annual penetration testing
• Reactive gap assessments
• Support only before audits
Security was reactive.
NorthCore Analytics
• Monthly risk reviews
• Quarterly access oversight
• Continuous cloud governance checks
• Executive reporting cadence
Security was continuous.
The Turning Point
During a routine cloud configuration review, NorthCore’s vCISO noticed something unusual.
• Misconfigured API endpoint
• Logging disabled
• No IP restrictions
• Connected to a production-adjacent database replica
It wasn’t exploited yet. But it was visible. And searchable.
Continuous oversight caught what a one-time review would have missed.
What Happened Next
• Endpoint closed
• Logging enabled
• Access tightened
• Checklist updated
• Automated alert implemented
No headlines. No emergency board calls. Just risk removed before crisis.
Meanwhile at BluePeak
Three months later, BluePeak discovered a publicly exposed storage bucket flagged by an external security researcher.
• Client notifications
• Legal review
• Emergency remediation
• Insurance engagement
• Lost enterprise deal
Total impact: six-figure response cost and delayed SOC 2 readiness.
Ad-Hoc Consulting vs Continuous vCISO
| Ad-Hoc Consulting | Continuous vCISO |
|---|---|
| Project-based | Ongoing oversight |
| Reactive | Proactive |
| Gap-focused | Governance-focused |
| Event-triggered | Scheduled cadence |
Ad-hoc consulting solves isolated issues.
A vCISO builds a living security system.
The Financial Reality
Prevention is cheaper than remediation every time.
Book a 15-minute vCISO strategy session and uncover hidden risk before it becomes visible to attackers.
Final Question
Security leadership doesn’t have to be full-time.
But it must be continuous.
Stay Connected With Canadian Cyber
Follow us for vCISO insights, ISO 27001 strategies, and compliance best practices: