A practical guide to OSFI B-13 cyber risk controls that any Canadian company can adopt. Learn how vCISOs borrow governance, resilience, and cybersecurity practices from B-13 to build stronger security programs.
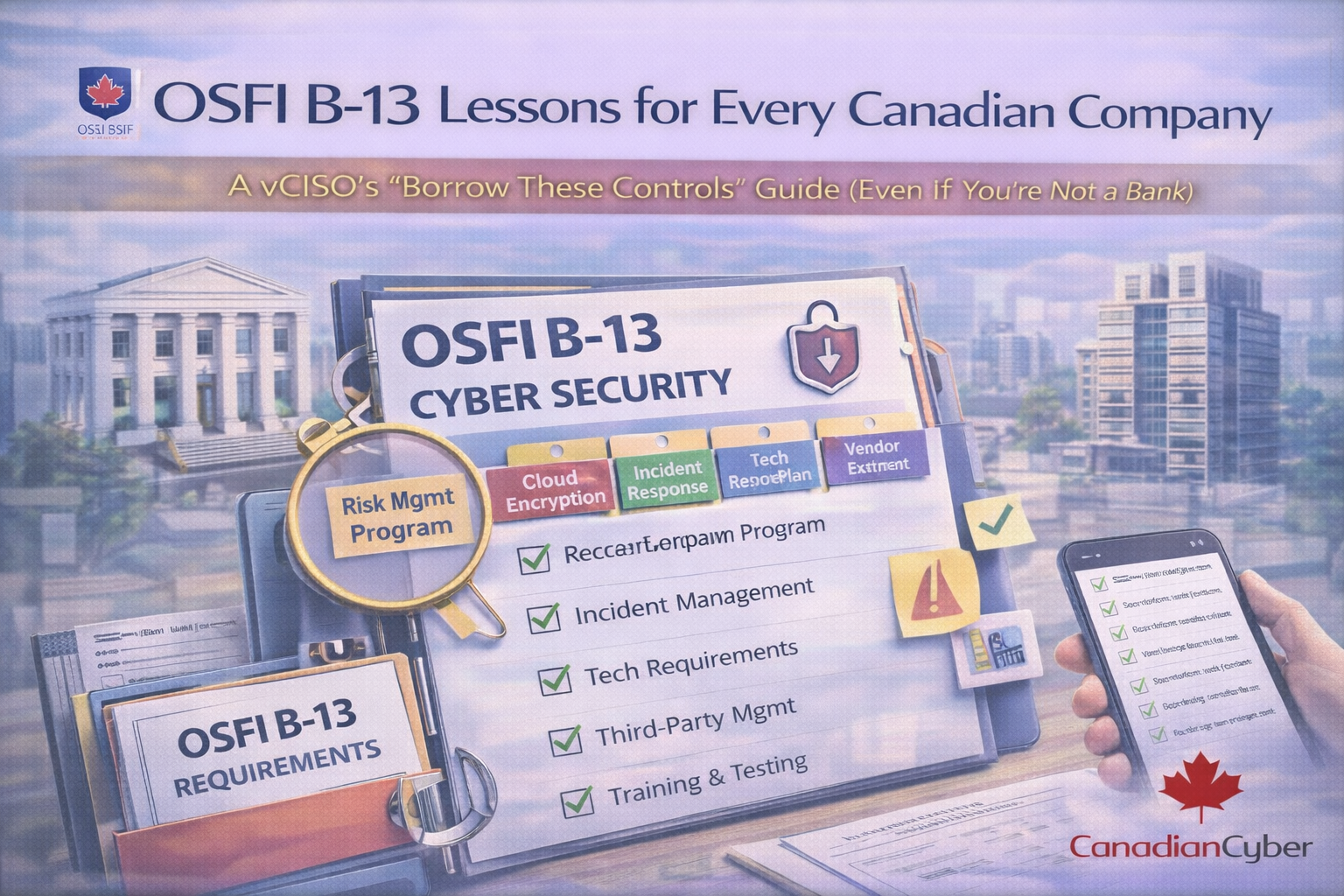
OSFI B-13 • Borrow These Controls • Board-Ready Governance
OSFI’s Guideline B-13 (Technology and Cyber Risk Management) was written for federally regulated financial institutions.
But the controls are one of the clearest “what good looks like” playbooks in Canada for technology and cyber risk governance.
This guide shows the B-13 controls worth copying into any company’s security program—without turning your team into a compliance factory.
Even if OSFI doesn’t regulate you, your stakeholders increasingly expect the same outcomes B-13 pushes:
clear accountability, resilient operations, and repeatable security controls that can be evidenced.
Start with the controls that create clarity and proof fast. This table is board-friendly.
Borrow it like this: assign one accountable executive sponsor, document the RACI, and record decisions in minutes.
Borrow it like this: write a one-page annual strategy (top risks, top initiatives, KPIs) and update quarterly.
Borrow it like this: define a simple risk taxonomy, set risk appetite statements, and enforce expiry dates on risk acceptance.
Borrow it like this: hold a quarterly tech and cyber risk review with leadership. Bring top risks, incidents, control health, vendor risk, and actions.
Borrow it like this: standardize change management, patch SLAs by severity, and configuration baselines (M365/cloud/endpoints/servers).
Borrow it like this: define RTO/RPO for critical services, test restores on a schedule, and record improvements.
Borrow it like this: list your top business-critical processes and document what systems and vendors each depends on.
Borrow it like this: no exceptions in email. Every exception needs a reason, compensating controls, owner, expiry date, and approval.
Borrow it like this: enforce MFA for everyone, apply stronger admin controls, monitor break-glass accounts, and review privileged access quarterly.
Borrow it like this: decide what you monitor, set a review cadence, and track alert-to-ticket-to-resolution.
Borrow it like this: keep the playbook short, define escalation, and run at least one tabletop exercise each year.
Borrow it like this: tier vendors, review critical vendors at least annually, and track exceptions and renewal-driven reviews.
B-13 is commonly read alongside related OSFI guidance like B-10 and E-21 because these risks intersect.
If you want high impact with minimal overhead, start here.
OSFI B-13 is a financial regulator guideline, but its structure is universally useful: governance, resilience, and cyber security backed by evidence.