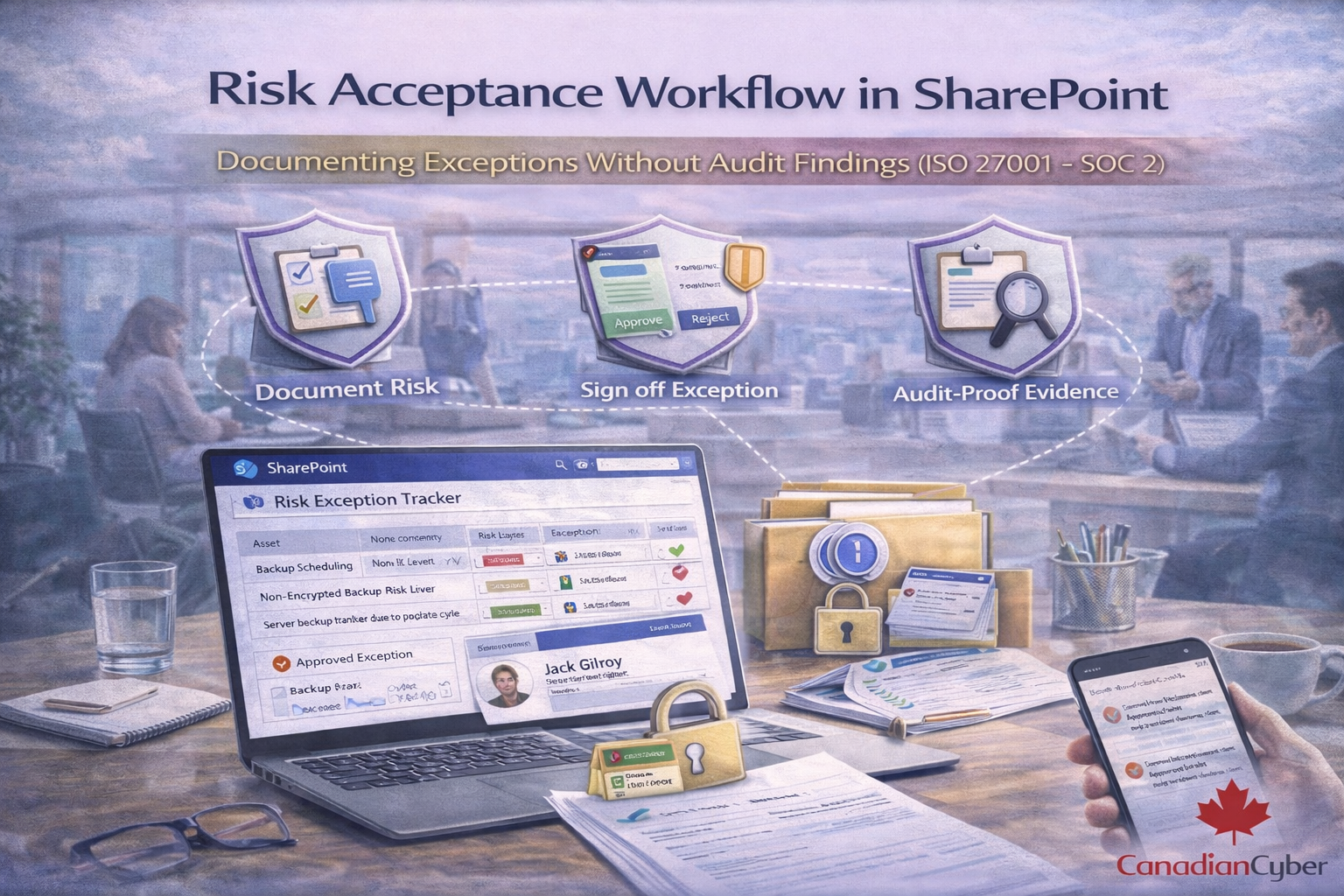
A practical SharePoint workflow to document risk acceptance the way auditors expect: clear rationale, compensating controls, approval authority, expiry dates, reminders, and closure evidence.
Risk acceptance is allowed in ISO 27001 and expected in SOC 2 but only if it’s disciplined.
Most audit findings happen when risk acceptance is informal: a Teams message, a spreadsheet line, or “we’ll fix it later.”
This guide shows a practical SharePoint workflow that creates clean evidence: rationale, approvals, expiry dates, and follow-up so exceptions don’t turn into nonconformities.
Auditors don’t fail you for accepting risk. They fail you for accepting risk without control.
Risk acceptance means: “We understand the risk, we’re choosing not to fully mitigate it right now, and we accept the consequences under defined conditions.”
Your SharePoint workflow needs two things: structured records (a list) and controlled evidence (a library with links).
Use this in your approval comment or approval page. It’s short, clear, and defensible.