A practical SharePoint on-prem security checklist for 2026. Learn how vCISOs approach patching, hardening, logging, and admin controls to secure SharePoint Server farms before end of support.
If you still run SharePoint Server on-prem, 2026 is not business as usual. It’s a risk cliff.
The question isn’t “Should we patch?” It’s: Do we have a patch and hardening plan that’s provable, repeatable, and fast enough for today’s threat pace?
If you’re on SharePoint 2016/2019, you’re approaching a hard deadline where security updates stop.
If you’re on SharePoint Subscription Edition, you’re supported, but you still need current servicing and hardening to avoid “known exploited” style incidents.
Either way, running internet-facing SharePoint on-prem without tight patching and hardening is an easy way to inherit ransomware risk.
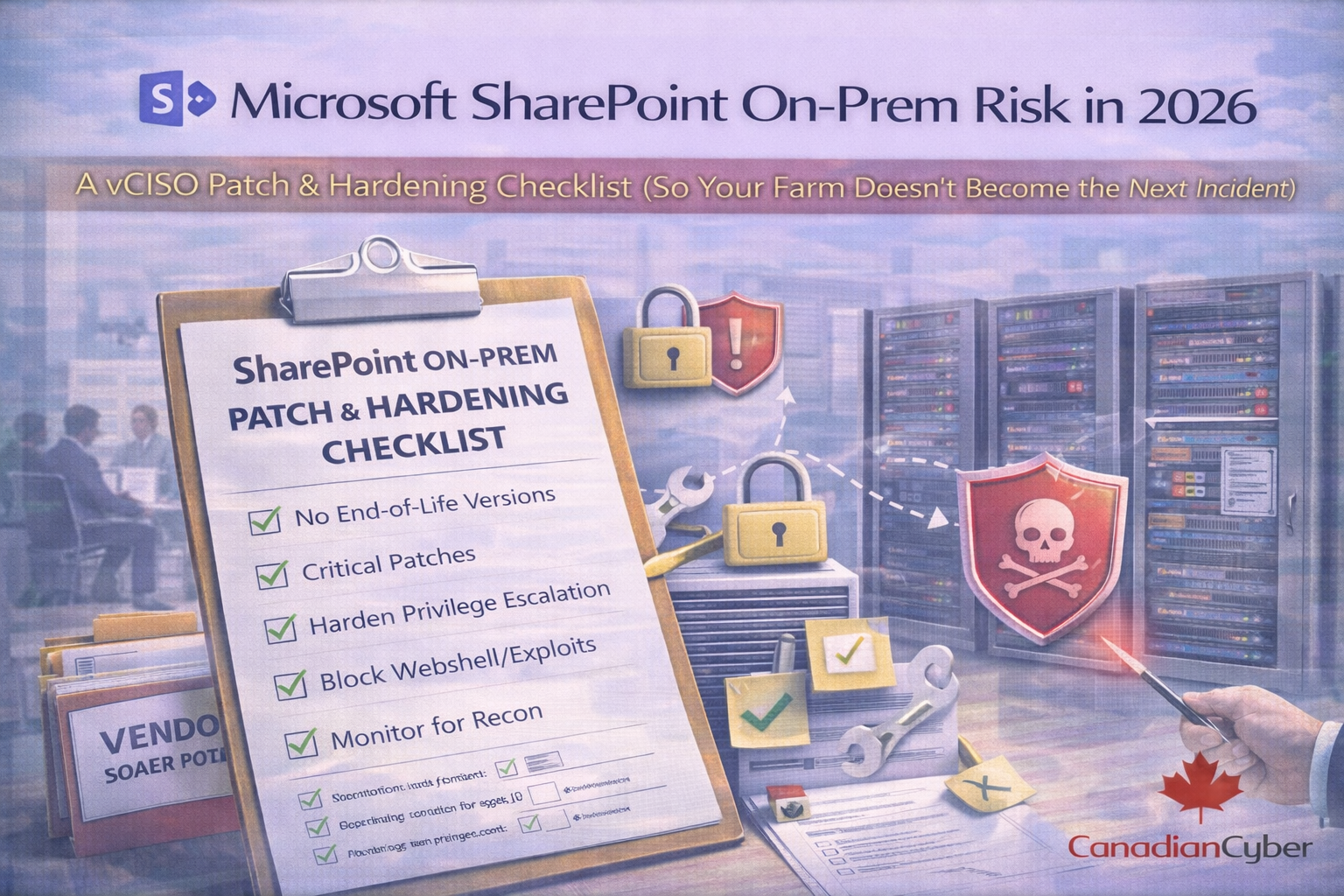
This is the checklist we use to get SharePoint farms audit-ready and incident-resistant.
If you’re on SharePoint 2016 or 2019, you need an executive decision path now because after July 14, 2026 you lose security updates.