ISO 27001 • SaaS Startups • Enterprise Sales
DIY Guide: ISO 27001 Implementation for SaaS Startups Preparing for Enterprise Sales
ISO 27001 helps SaaS startups turn security from scattered documents into a structured, evidence-backed program that enterprise buyers can trust.
Quick Snapshot
| ISO 27001 Area | Startup Priority |
|---|---|
| Scope | Define the SaaS product, production cloud, customer data, support tools, employees, and key vendors in scope. |
| Risk | Build a practical risk register around access, cloud, vendors, incidents, backups, and secure development. |
| Evidence | Organize proof early so enterprise security reviews do not become last-minute scrambles. |
| Outcome | A buyer-friendly ISMS that shows security is managed, reviewed, and continuously improved. |
Introduction
Enterprise sales changes everything for a SaaS startup.
The product may be strong. The demo may go well. The buyer may be interested.
Then procurement asks for proof:
- Security questionnaires arrive.
- Vendor risk teams ask about access control.
- Legal asks about data handling.
- IT asks about cloud security.
- Leadership asks whether ISO 27001 is on the roadmap.
ISO 27001 helps SaaS startups prove to enterprise buyers that security is not improvised. It is managed.
It gives your startup a structured way to manage information security, risk, controls, evidence, and continual improvement without waiting for enterprise sales pressure to become urgent.
Preparing for Enterprise Security Reviews?
Canadian Cyber helps SaaS startups build practical ISO 27001 roadmaps that support enterprise sales without overwhelming small teams.
Why ISO 27001 Matters for Enterprise Sales
Enterprise buyers want confidence before they trust your platform with their data.
They often ask:
- Do you have an ISMS?
- How do you manage risk?
- Who has access to production?
- How do you review vendors?
- How do you handle incidents?
- Are policies approved and reviewed?
- Do you test backups?
- Can you prove controls are operating?
ISO 27001 helps answer these questions with a real management system instead of scattered documents. For startups, that can reduce sales friction and make security reviews easier to pass.
Step 1: Define the ISMS Scope
Start by deciding what ISO 27001 will cover.
For most SaaS startups, the scope usually includes:
- the SaaS product
- production cloud infrastructure
- customer data stores
- identity provider
- source code and CI/CD pipeline
- support tools
- monitoring and logging systems
- employees who build, support, or operate the platform
- key vendors that affect the service
Avoid vague scope language like “our company security program.” Use a clear scope that matches what enterprise buyers care about.
Not Sure What Should Be in Scope?
We help SaaS teams define ISO 27001 scope around the product, cloud environment, customer data, support workflows, vendors, and enterprise buyer expectations.
Step 2: Identify Assets and Data Flows
List the systems and data your SaaS platform depends on.
| Asset Area | Examples |
|---|---|
| Cloud and Data | cloud accounts, databases, object storage, backup systems |
| Application Layer | APIs, customer portals, admin dashboards |
| Development | GitHub or GitLab, CI/CD tools, ticketing systems |
| Operations | support systems, endpoint devices, vendor platforms, monitoring tools |
Then map where customer data goes. This helps you understand what needs protection and what should be included in the risk assessment.
Step 3: Build a Risk Register
ISO 27001 is risk-based. Start with practical SaaS risks.
- unauthorized production access
- cloud misconfiguration
- customer data leakage
- weak vendor controls
- insecure code changes
- backup failure
- phishing or account compromise
- support access misuse
- incident response delays
For each risk, track:
- risk owner
- likelihood and impact
- existing controls
- residual risk
- treatment decision
- treatment action and due date
A simple SharePoint List or spreadsheet can work at the beginning, but make sure it is reviewed and maintained.
Step 4: Create the Core Policies
You do not need 40 policies to begin. Start with the essentials.
- Information Security Policy
- Access Control Policy
- Risk Management Procedure
- Incident Response Plan
- Vendor Management Policy
- Change Management Policy
- Acceptable Use Policy
- Data Classification and Handling Policy
- Backup and Recovery Procedure
- Secure Development Policy
The policies should match how your team actually works. A policy that sounds mature but does not reflect reality will create audit problems later.
Step 5: Strengthen Access Control
Enterprise buyers care deeply about access.
Focus on:
- MFA for all critical systems
- SSO where practical
- least privilege
- production access restrictions
- privileged access reviews
- clear onboarding and offboarding
- removal of stale accounts
- contractor access controls
- support access logging
| Good Evidence | Why It Helps | |
|---|---|---|
| MFA reports | Shows identity controls are enforced | |
| Access review records | Shows access is periodically checked | |
| Offboarding tickets | Shows access is removed when people leave | |
| Admin role exports | Shows privileged access is controlled |
Need Access Controls Buyers Will Trust?
We help SaaS startups improve MFA, privileged access reviews, offboarding evidence, admin role exports, and support access controls.
Step 6: Formalize Change Management
SaaS startups move fast, but enterprise buyers still expect controlled changes.
Your change process should include:
- pull request reviews
- branch protection
- deployment records
- testing before release
- approval for high-risk changes
- emergency change documentation
- rollback planning
For startups, this does not need to be heavy. But it must be consistent and evidenced.
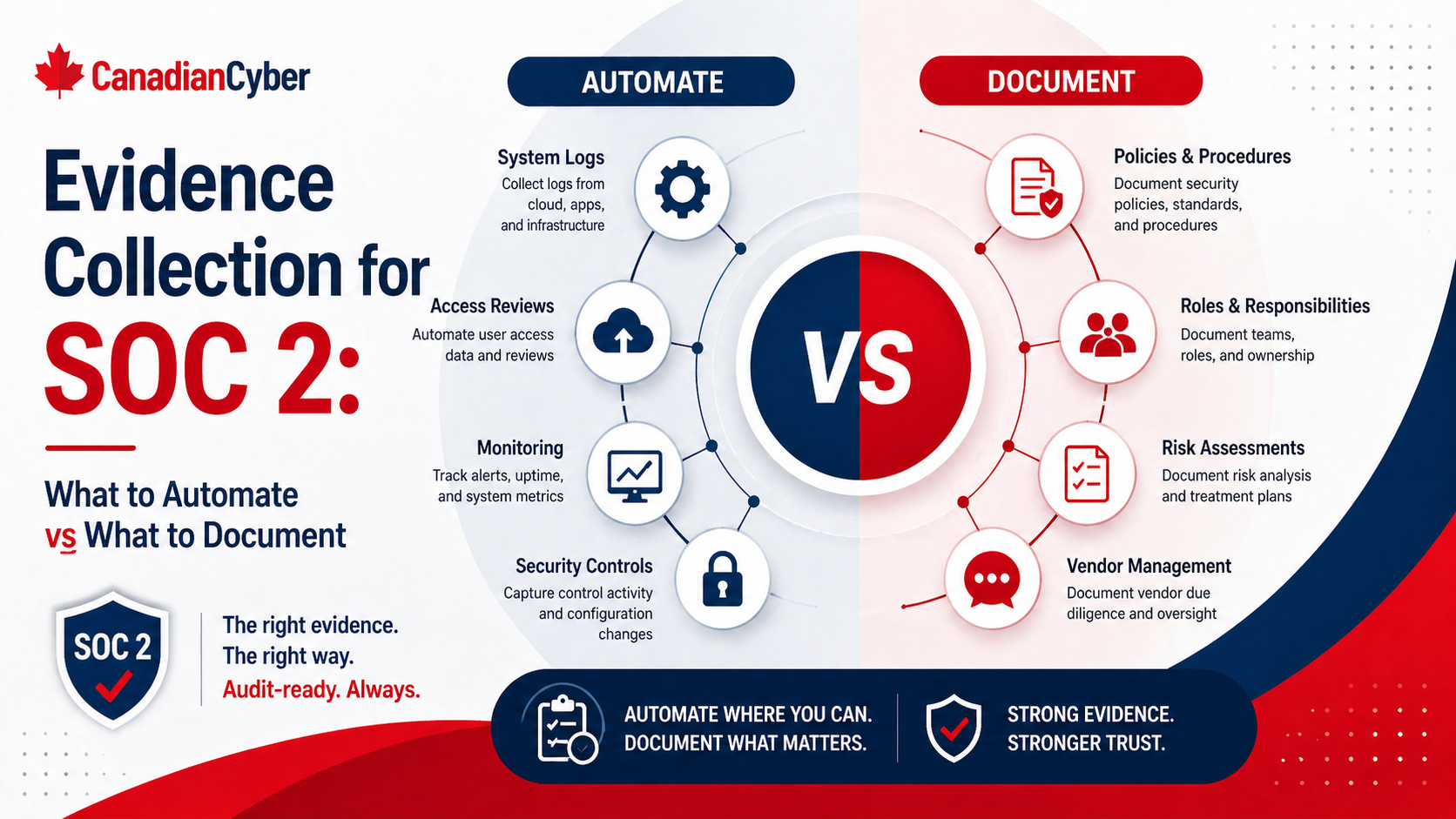
Step 7: Review Vendors
Create a vendor register and prioritize vendors that affect customer data, cloud hosting, identity, support, monitoring, payments, backups, and development workflows.
| Vendor Register Field | Purpose |
|---|---|
| Vendor name and service provided | Identifies the dependency |
| Data handled | Shows sensitivity and review depth |
| Criticality | Helps prioritize vendor reviews |
| Security evidence reviewed | Shows supplier risk was assessed |
| Next review date | Keeps vendor oversight active |
Enterprise buyers will ask about third-party risk. Be ready.
Step 8: Prepare Incident Response
Create a practical incident response plan.
It should define:
- incident types
- severity levels
- response roles
- escalation paths
- evidence preservation
- customer notification process
- decision logging
- post-incident review
- corrective action follow-up
Then run a tabletop exercise. A simple scenario like a compromised admin account or exposed customer file is enough to test whether the process works.
Need an Incident Plan That Actually Works?
Canadian Cyber helps SaaS teams build incident response plans, tabletop exercises, decision logs, customer notification workflows, and corrective action records.
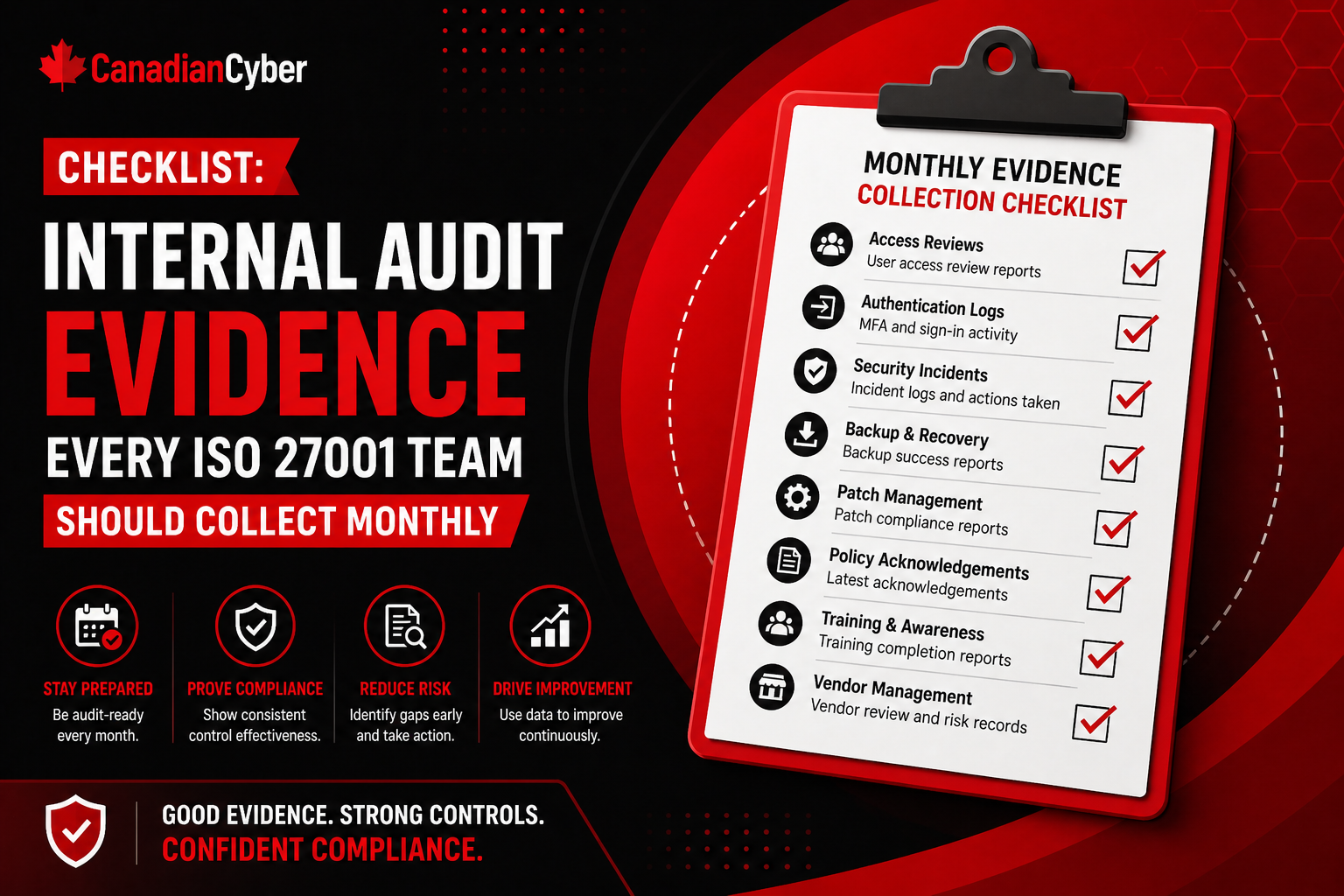
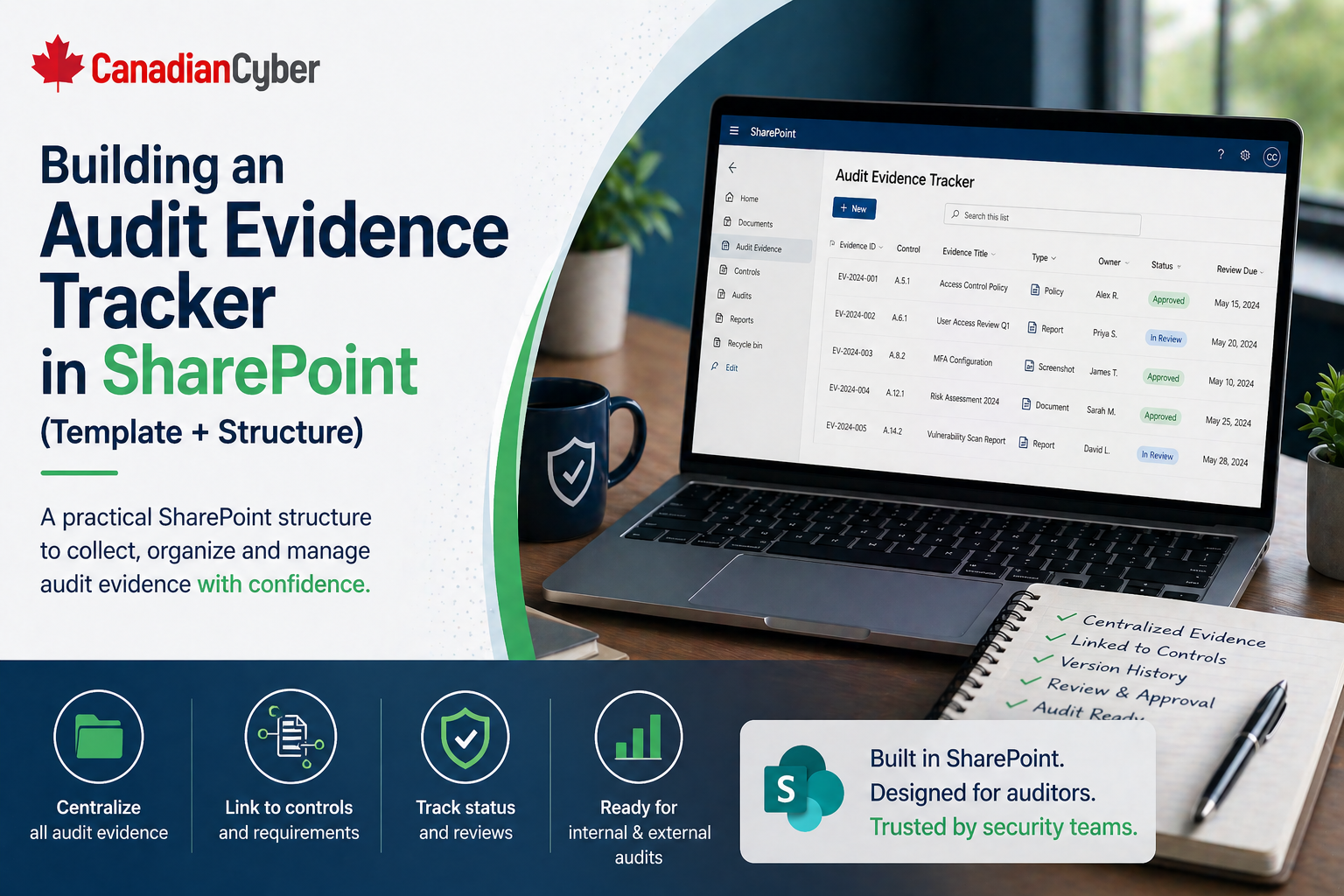
Step 9: Organize Evidence Early
Do not wait until audit week.
Create an evidence workspace in SharePoint with sections for:
- policies
- risk register
- access reviews
- vendor reviews
- change management
- incidents
- backups
- training
- management review
- internal audit
- corrective actions
Use metadata where possible:
- owner
- control area
- period covered
- review date
- evidence status
Step 10: Complete Internal Audit and Management Review
Before certification, you need to test the ISMS.
| Activity | What It Should Cover |
|---|---|
| Internal Audit | scope, policies, risk register, access control, vendor management, incident response, change management, backup evidence, corrective actions |
| Management Review | risks, audit results, incidents, corrective actions, security objectives, vendor issues, resource needs, improvement priorities |
A Practical 90-Day Startup Roadmap
| Timeline | Focus |
|---|---|
| Days 1–15 | Scope, asset inventory, data flows |
| Days 16–30 | Risk register and policy foundation |
| Days 31–45 | Access control and vendor review cleanup |
| Days 46–60 | Change management, incident response, backup testing |
| Days 61–75 | Evidence organization and corrective actions |
| Days 76–90 | Internal audit, management review, readiness review |
This timeline is aggressive, but realistic if the team already has some security basics in place.
What SaaS Startups Usually Get Wrong
- Defining scope too vaguely: Buyers care about the actual service, systems, people, and vendors protecting their data.
- Writing policies before understanding workflows: Policies must match reality.
- Ignoring support access to customer data: Support workflows often create hidden exposure.
- Treating vendor review as optional: Enterprise buyers will ask about third-party risk.
- Skipping restore testing: Backup settings are not enough. Recovery must be proven.
- Leaving evidence scattered: Evidence chaos slows audits and sales reviews.
- Assigning control ownership too late: Every control needs an owner early.
Want ISO 27001 Without Startup Overload?
We help small SaaS teams focus on the ISO 27001 controls that matter most for enterprise sales, buyer trust, and audit readiness.
Canadian Cyber’s Take
At Canadian Cyber, we often see SaaS startups wait until an enterprise buyer asks for ISO 27001 before getting organized.
That creates pressure.
The strongest startups begin earlier by building a practical ISMS around:
- scope
- risk
- access
- vendors
- secure development
- incidents
- evidence
- leadership review
ISO 27001 does not need to slow a startup down. Done properly, it gives the company a cleaner way to prove trust and support larger sales.
Takeaway
ISO 27001 implementation for SaaS startups should be practical, focused, and tied to enterprise sales needs.
Start with:
- clear scope
- asset and data flow visibility
- risk register
- core policies
- access control
- vendor review
- change management
- incident response
- evidence organization
- internal audit and management review
Enterprise buyers are not only buying your product. They are trusting your company to protect their data.
How Canadian Cyber Can Help
At Canadian Cyber, we help SaaS startups build practical ISO 27001 programs that support enterprise sales without overwhelming small teams.
- ISO 27001 implementation planning
- ISMS scope and risk workshops
- policy and control development
- access and vendor review workflows
- SharePoint-based evidence organization
- internal audit and management review support
- vCISO guidance for SaaS security leadership
Stay Connected With Canadian Cyber
Follow Canadian Cyber for practical guidance on ISO 27001, SaaS security, enterprise sales readiness, vCISO support, and audit preparation.