ISO 27001 • Internal Audit • Monthly Evidence
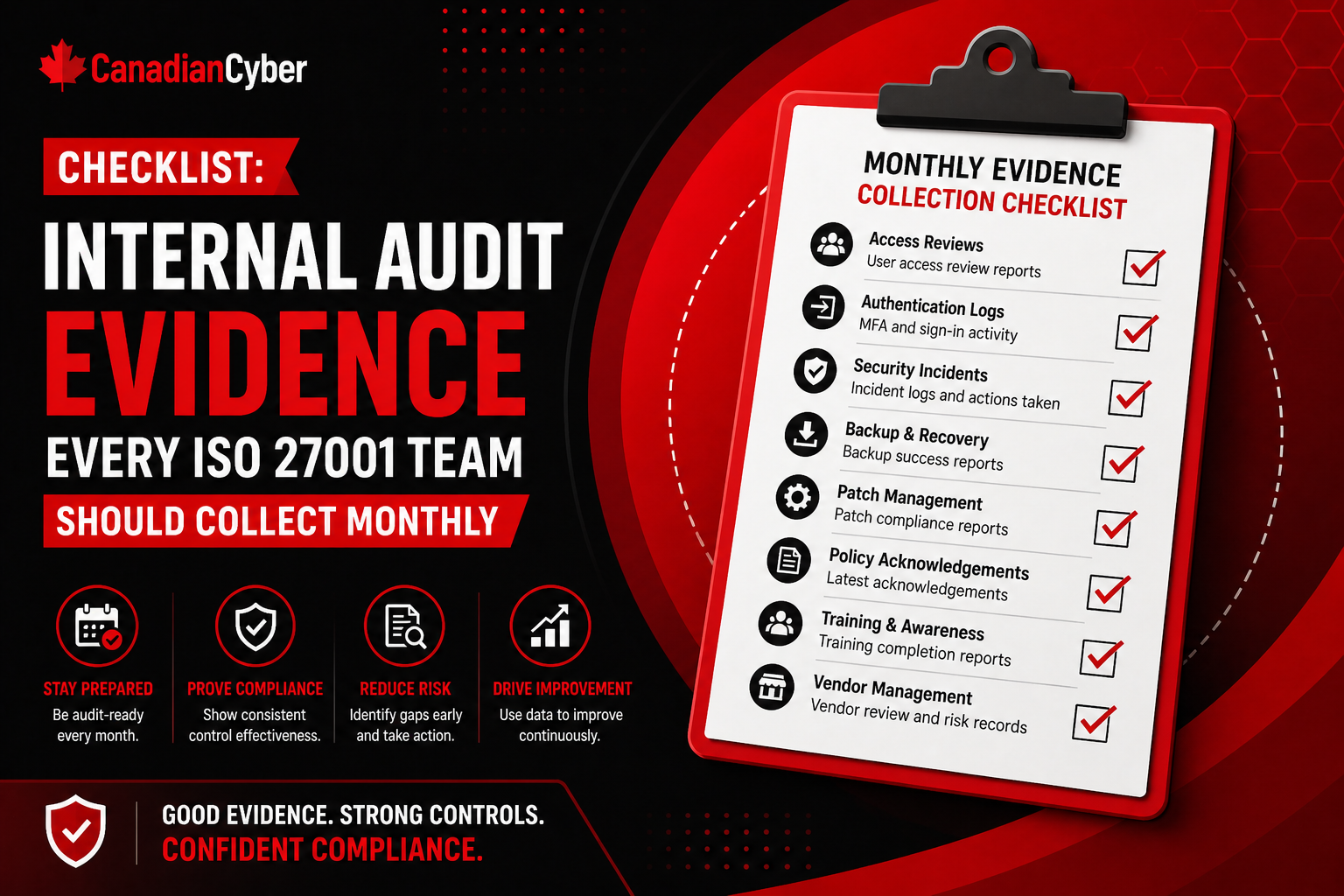
Checklist: Internal Audit Evidence Every ISO 27001 Team Should Collect Monthly
Monthly evidence collection helps ISO 27001 teams stay audit-ready all year instead of rebuilding the ISMS before every audit.
Quick Snapshot
| Evidence Area | What to Collect Monthly |
|---|---|
| Access Control | User access changes, privileged access changes, offboarding proof, and exceptions |
| Risks & Actions | New risks, updated risks, overdue treatment actions, corrective action progress, and closure proof |
| Operations | Incidents, vulnerabilities, backups, changes, monitoring alerts, and asset updates |
| Governance | Vendor reviews, awareness records, policy reviews, management inputs, and internal audit readiness |
Introduction
ISO 27001 audit readiness should not happen once a year.
If your team waits until the internal audit or certification audit to collect evidence, the process quickly becomes stressful.
- People start searching folders.
- Screenshots are taken last minute.
- Control owners forget what happened.
- Access reviews are hard to prove.
- Vendor records are incomplete.
- Corrective actions are missing closure evidence.
Monthly evidence collection helps ISO 27001 teams stay audit-ready all year instead of rebuilding the ISMS before every audit.
Still Collecting Evidence Only Before Audits?
Canadian Cyber helps ISO 27001 teams build monthly evidence workflows, SharePoint trackers, and clear control owner routines.
Why Monthly Evidence Collection Works
Monthly evidence collection helps teams:
- keep records current
- catch missing controls early
- reduce audit preparation time
- prove controls are operating
- support internal audits
- prepare management review inputs
- track corrective actions faster
It also makes control owners more accountable because evidence becomes part of the operating rhythm.
The Monthly ISO 27001 Evidence Checklist
| Evidence Area | What to Collect Monthly |
|---|---|
| Access Control | User access changes, privileged access changes, offboarding proof |
| Risk Register | New risks, updated risks, overdue treatment actions |
| Corrective Actions | Open actions, overdue items, closure evidence |
| Incidents | Incidents, near misses, response records, lessons learned |
| Vulnerabilities | Scan results, remediation status, accepted risks |
| Backups | Backup success reports, restore test evidence if performed |
| Change Management | Approved changes, deployment records, emergency changes |
| Vendor Management | New vendors, reassessments due, vendor issues |
| Security Awareness | New hire training, overdue training, phishing results |
| Policies | Policies due for review, approvals, version changes |
| Logging and Monitoring | Alert summaries, investigation tickets, monitoring exceptions |
| Asset Inventory | New assets, retired assets, ownership changes |
1. Access Control Evidence
Collect:
- new user access approvals
- terminated user removal proof
- privileged access changes
- admin role exports
- access exceptions
- quarterly access review progress
Access control is one of the most commonly tested ISO 27001 areas. Monthly evidence helps prove that access is not being managed casually.
2. Risk Register Evidence
Collect:
- newly identified risks
- updated residual risk ratings
- treatment progress
- overdue treatment actions
- accepted risk approvals
- risks triggered by incidents or changes
ISO 27001 is risk-based. Your risk register should show movement, not sit untouched between audits.
Need a Monthly Risk Review Rhythm?
Canadian Cyber helps teams set up risk registers, review schedules, treatment tracking, and SharePoint views for overdue actions.
3. Corrective Action Evidence
Collect:
- open corrective actions
- overdue actions
- completed actions
- evidence of closure
- verification notes
- root cause updates
Auditors want to see that findings are not only recorded but fixed and verified.
4. Incident and Near-Miss Evidence
Collect:
- incident records
- near-miss reports
- severity classifications
- response timelines
- closure summaries
- lessons learned
- linked corrective actions
Even small events can show whether your incident process is working.
5. Vulnerability and Patch Evidence
Collect:
- vulnerability scan summaries
- high-risk findings
- remediation tickets
- patch compliance reports
- accepted vulnerability risks
- overdue remediation items
Monthly review helps prevent unresolved vulnerabilities from becoming repeat audit findings.
6. Backup and Recovery Evidence
Collect:
- backup job success reports
- backup failure tickets
- remediation for failed backups
- restore test evidence if completed
- backup configuration changes
Backups prove resilience only when they are monitored and tested.
7. Change Management Evidence
Collect:
- approved production changes
- pull request reviews
- deployment records
- emergency change records
- rollback notes where relevant
- failed change follow-up
Change evidence shows that production systems are not modified informally.
Want Cleaner Monthly Evidence Collection?
We help ISO 27001 teams collect evidence for access, risks, corrective actions, incidents, vulnerabilities, backups, changes, vendors, policies, and monitoring.
8. Vendor Management Evidence
Collect:
- new vendor approvals
- vendor risk ratings
- completed reassessments
- security reports received
- vendor incidents or issues
- upcoming vendor reviews
Third-party risk changes throughout the year. Monthly tracking prevents vendor reviews from becoming last-minute audit work.
9. Security Awareness Evidence
Collect:
- new-hire training completion
- overdue training reminders
- phishing simulation results
- targeted retraining evidence
- monthly awareness communications
Awareness evidence should show ongoing reinforcement, not only annual completion.
10. Policy and Document Control Evidence
Collect:
- policies due for review
- policies approved during the month
- version updates
- archived documents
- owner changes
- review reminders sent
Policies must stay current and controlled. Monthly tracking prevents stale documents.
11. Logging and Monitoring Evidence
Collect:
- alert summaries
- investigation tickets
- monitoring exceptions
- high-risk event reviews
- log retention checks
- unresolved alert follow-up
Logging is stronger when someone can prove alerts are reviewed and acted on.
12. Asset Inventory Evidence
Collect:
- new laptops
- retired devices
- new SaaS tools
- cloud resources added
- ownership changes
- unsupported assets identified
Asset visibility supports access, risk, vulnerability, vendor, and incident management.
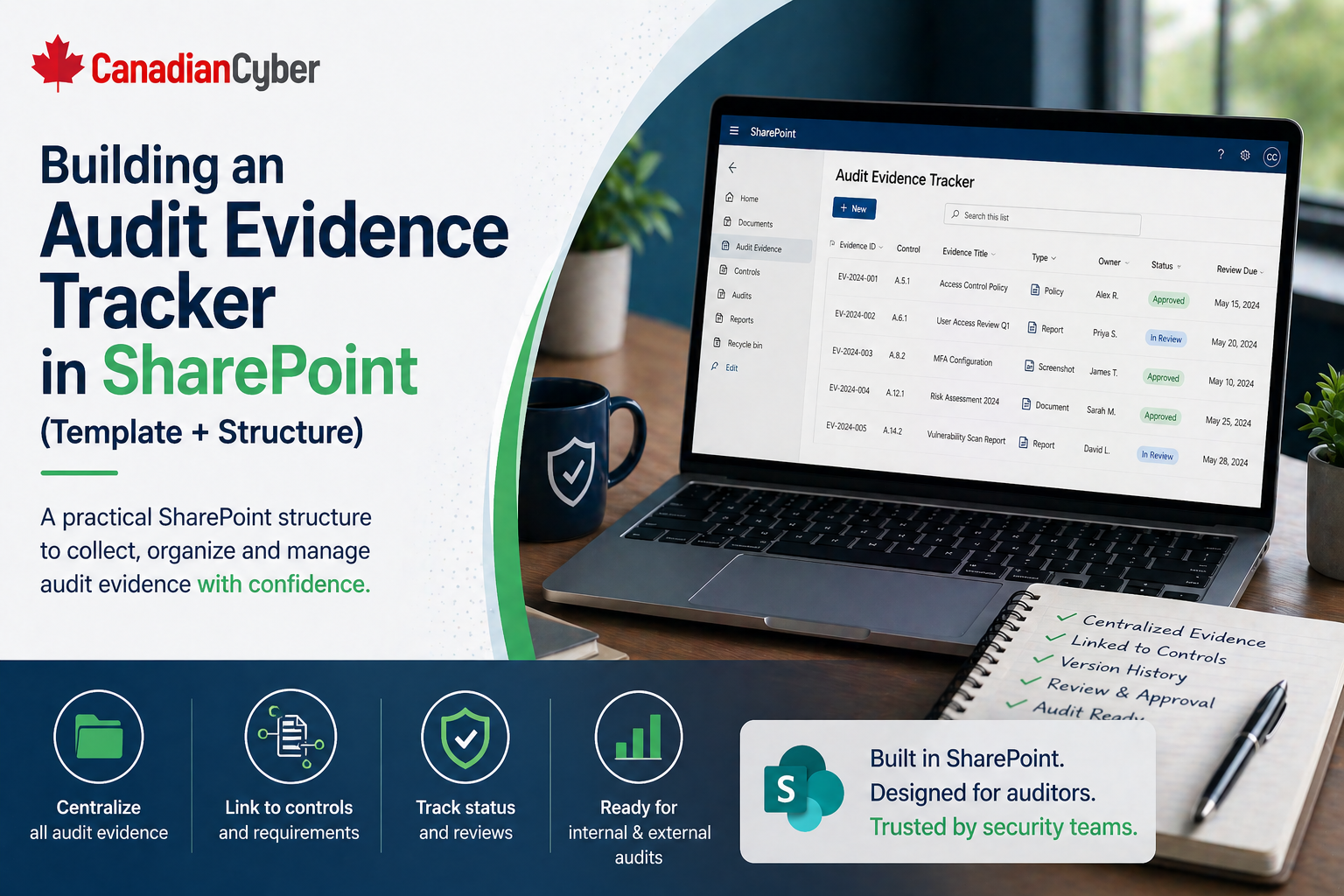
Monthly SharePoint Tracker Structure
| Field | Purpose |
|---|---|
| Evidence ID | Unique record |
| Month | Evidence period |
| Control Area | Access, risk, vendor, incident, and more |
| Evidence Owner | Responsible person |
| Evidence Type | Report, screenshot, ticket, or minutes |
| Evidence Link | File or record location |
| Review Status | Submitted, reviewed, accepted, or needs update |
| Gap Found | Yes or no |
| Corrective Action Link | Remediation item |
Need a SharePoint Evidence Tracker?
Canadian Cyber can help design a monthly evidence tracker with owners, review status, control areas, evidence links, gaps, and corrective action tracking.
Common Mistakes to Avoid
- Collecting screenshots without context: Every evidence item should show what it proves.
- Waiting until quarter-end: Monthly collection reduces audit pressure.
- Forgetting ownership: Every evidence area needs an owner.
- Not reviewing submitted evidence: Collected evidence is not automatically good evidence.
- Ignoring small gaps: Small monthly gaps often become major audit issues later.
Canadian Cyber’s Take
At Canadian Cyber, we often see ISO 27001 teams lose time because evidence collection is treated as an audit event instead of a monthly habit.
The strongest ISMS programs collect small amounts of evidence consistently. That creates:
- cleaner audits
- faster internal reviews
- stronger management reporting
- better corrective action follow-up
- less last-minute stress
Monthly evidence collection is one of the simplest ways to make ISO 27001 easier to maintain.
Takeaway
ISO 27001 audit readiness is easier when evidence is collected monthly.
Your team should regularly collect evidence for:
- access control
- risks
- corrective actions
- incidents
- vulnerabilities
- backups
- changes
- vendors
- awareness
- policies
- monitoring
- assets
Audit readiness is not built in the final week. It is built through small, consistent evidence habits every month.
How Canadian Cyber Can Help
At Canadian Cyber, we help ISO 27001 teams build practical monthly evidence collection workflows using SharePoint, templates, and clear control ownership.
- ISO 27001 evidence tracker setup
- monthly evidence checklist design
- SharePoint evidence libraries
- internal audit preparation
- corrective action tracking
- management review reporting
- vCISO guidance for continuous ISMS operations
Stay Connected With Canadian Cyber
Follow Canadian Cyber for practical guidance on ISO 27001, evidence management, internal audits, SharePoint tracking, vCISO support, and audit readiness.