Avoid the most expensive ISO 27001 implementation mistakes in SaaS. Learn how to control scope, structure evidence, and pass audits without overspending.
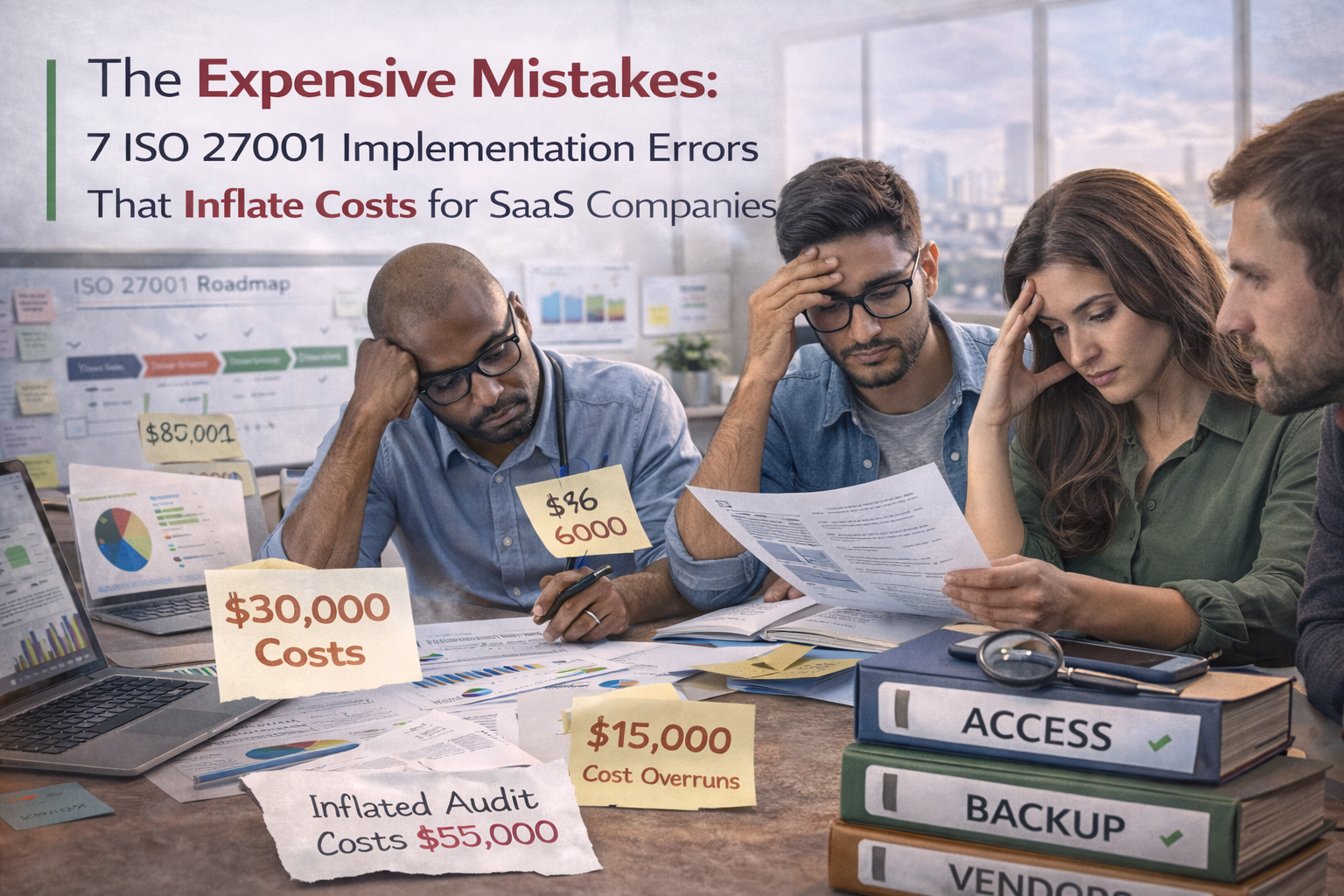
Timelines slip, consulting bills grow, teams burn out, and audits become recurring fire drills. Usually that is not because ISO 27001 is too hard. It is because the implementation model is bloated, reactive, and poorly structured.
Here are the seven most expensive ISO 27001 implementation errors we see in SaaS environments, plus the fixes that keep scope tight, evidence clean, and certification achievable.
The cost problem usually does not start at the certification audit. It starts much earlier, when the ISMS is built around too much scope, too much documentation, weak evidence discipline, and no clear operating rhythm.
Each one adds time, rework, and avoidable audit pain. Together, they create a very expensive compliance program.
This is the number one cost multiplier. SaaS teams often scope every product, every cloud account, every internal tool, corporate IT, and sometimes even customer environments. That turns one audit program into five at once.
Some teams begin by writing a big policy set. They end up with beautiful documentation and weak evidence. Auditors are rarely impressed by that combination.
| What this causes | Practical fix |
|---|---|
| Paper compliance that auditors challenge | Start with operational proof first |
| Months spent writing instead of operating | Capture admin access reviews, change samples, logging reviews, restore tests, and vendor decisions before polishing policy language |
| Last-minute evidence scrambling | Write policies that match what already operates |
Without an evidence structure, everything becomes screenshots, exports named final_v3, and scattered artifacts in chats and inboxes. That is where audit time disappears.
Inside each pack, include a short summary that explains what was tested, what period it covers, the result, and links to supporting artifacts. That is what makes evidence usable.
SaaS teams always have real constraints: legacy services, patch delays, vendor gaps, logging limitations, and temporary admin access. The expensive part is not having them. The expensive part is failing to govern them.
Most SaaS incidents now involve third parties somewhere in the chain. But many teams still treat vendor risk like document collection. They gather SOC reports and call it done.
Backups and incident response plans are common. Proof of testing is not. That gap is expensive because it creates findings that are very hard to argue with.
| Test type | Lean minimum cadence |
|---|---|
| Restore test | Quarterly for Tier 1 systems, or at least semi-annually |
| Disaster recovery tabletop | One to two per year minimum |
| Incident tabletop | At least one per year, more if the company is growing fast |
The hidden cost killer is open loops. Findings get logged but never truly closed. Or they get marked closed without proof. Then the same issue returns in the next review.
Each item should have an owner, a due date, an exact closure artifact, and a re-sampling plan for the next quarter.
If you want to keep ISO 27001 costs under control, build the program in a practical sequence instead of trying to mature everything at once.
That is how SaaS teams create an ISMS that runs continuously without seasonal panic.
The most expensive ISO 27001 programs are not usually the most ambitious. They are the least disciplined. They try to include too much, prove too little, and fix too slowly.
When scope is right-sized, evidence is curated, exceptions expire, and corrective actions are verified, ISO becomes much cheaper to run and much easier to trust.