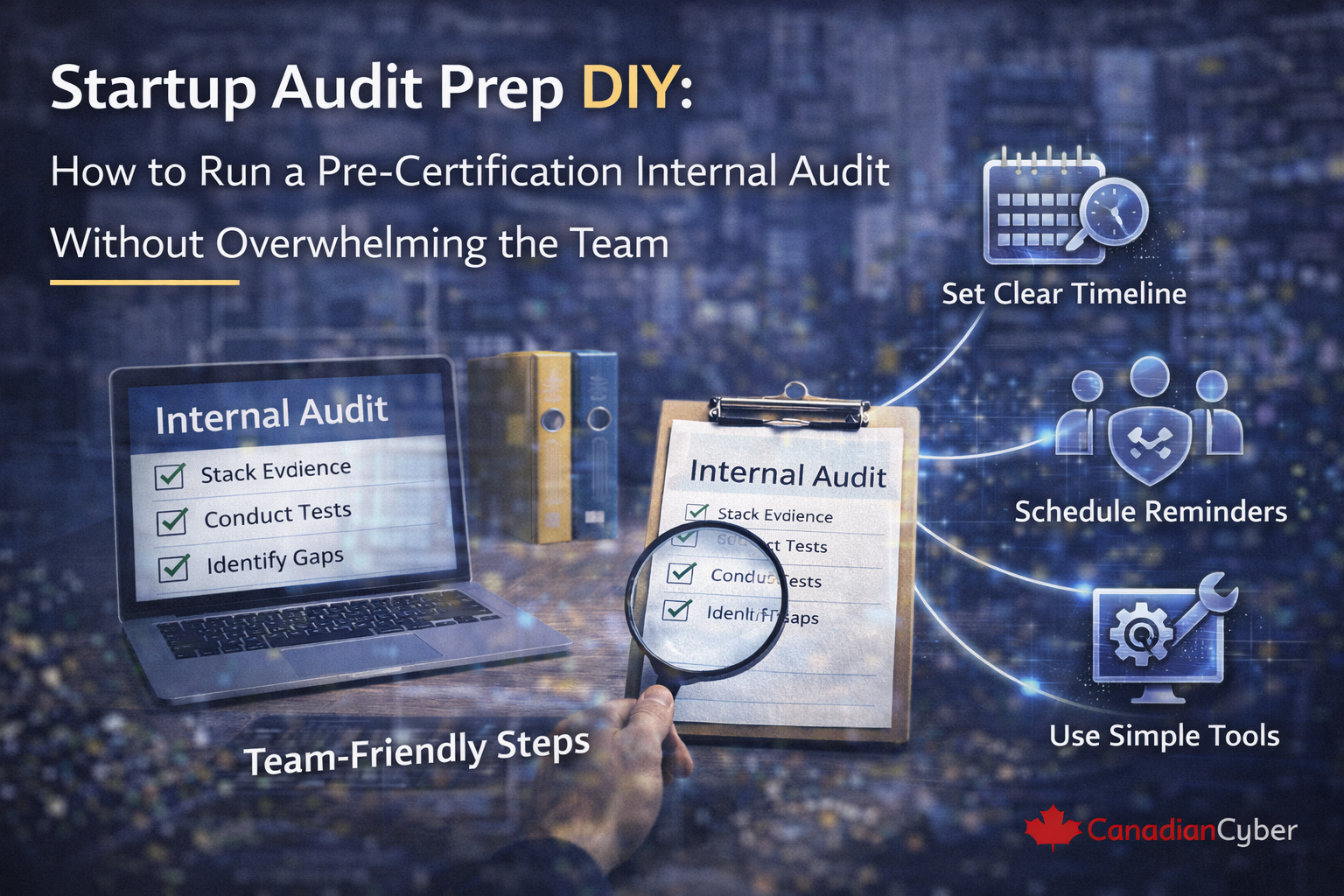
A practical guide to running a startup internal audit before ISO 27001 or SOC 2 certification, without overwhelming the team.
That is exactly why many teams delay it.
But if your startup is working toward ISO 27001, SOC 2, or broader security readiness, a pre-certification internal audit is one of the smartest things you can do before the external auditor arrives.
Not because it needs to be painful. And not because auditors expect perfection. It matters because it gives your team one controlled chance to answer a very useful question: if someone tested our program today, what would actually hold up and what would still fall apart?
For startups, that is the real goal. A good DIY pre-certification internal audit should reduce audit stress, not create more of it.
Most startups do not avoid internal audits because they do not care about compliance. They avoid them because they assume the audit will slow the team down, create extra bureaucracy, produce too many findings at once, distract from real work, and feel too formal for a growing company.
Those concerns are understandable. Startups are already juggling product releases, customer deadlines, hiring, security questionnaires, vendor onboarding, infrastructure changes, and certification prep work at the same time.
A pre-certification internal audit is not about pretending to be a regulator. It is about checking whether your security and compliance program is aligned to what you say you do, supported by evidence, operating consistently, understood by control owners, and ready enough that external audit does not become chaos.
That means the audit should help answer questions like these:
Imagine a startup that is a few months away from certification or attestation. The team has already done a lot of useful work. Policies are drafted. The risk register exists. MFA is in place. Vendor reviews have started. Onboarding and offboarding are more structured. Corrective action tracking exists in some form. Evidence folders are beginning to take shape.
On paper, progress looks good. But nobody has really tested the program as a system.
This is exactly where a lean internal audit becomes useful. It helps the startup find the gaps before the external auditor does.
You do not. A startup does not need a massive audit plan, heavy audit language, or a multi-week disruption to get value from internal audit work.
What it does need is a clear scope, practical control testing, focused evidence review, short interviews with the right owners, honest documentation of gaps, and manageable corrective actions.
A pre-certification internal audit should focus on the areas most likely to affect certification readiness. You do not need to review everything with the same depth. The goal is to test the areas that matter most.
| Audit Area | Why It Matters Before Certification |
|---|---|
| Access control | Often one of the first areas external auditors review |
| Vendor review | Frequently incomplete or inconsistent in startups |
| Incident handling | Easy to describe, harder to prove with records |
| Policy review and governance | Shows management discipline and control ownership |
| Evidence readiness | Makes or breaks external audit efficiency |
| Corrective action tracking | Shows whether issues are truly being resolved |
One of the fastest ways to overwhelm the team is to make the audit too broad. For a startup, the best first move is usually to define a practical scope around the systems and teams already in scope for certification, the most important operational controls, the evidence-heavy areas most likely to be tested later, and the highest-risk workflows.
In a startup, the internal audit is often run by a compliance lead, security lead, operations lead, consultant, vCISO, or a cross-functional person with enough independence to review fairly.
The key is not perfect formality. The key is objectivity. The person leading the audit should be able to ask practical questions, document findings clearly, and avoid grading their own work too generously.
You do not need a huge audit binder. A lean plan can be short and still useful.
| Section | Example |
|---|---|
| Objective | Assess pre-certification readiness of key ISMS or control areas |
| Scope | In-scope systems, policies, operational controls, and evidence |
| Focus Areas | Access, vendors, incidents, policies, evidence, corrective actions |
| Audit Methods | Evidence review, short interviews, walkthroughs, spot checks |
| Output | Findings, observations, corrective actions, readiness summary |
This is one of the most important rules. A startup internal audit should never stop at “Do we have a policy?” or “Did someone say this happens?”
Instead, test whether the control leaves a trail.
Startups do not need hour-long interviews for every area. Most internal audit conversations can be short if the questions are focused. A 20 to 30 minute discussion with a control owner is often enough to ask what they own, how the process works in practice, what evidence exists, what usually goes wrong, what still feels messy, and whether there are known gaps not yet fixed.
The audit should feel like a readiness review, not an interrogation.
Not every issue needs the same level of urgency. A helpful startup internal audit usually separates results into major readiness gaps, moderate weaknesses, and minor observations.
| Finding Type | What It Means | Example |
|---|---|---|
| Major readiness gap | Likely to create serious trouble in certification | No evidence for a key control, no ownership, no incident records |
| Moderate weakness | Control exists, but discipline is inconsistent | Evidence hard to find, policy dates behind, vendor reviews uneven |
| Minor observation | Cleanup item that matters but is unlikely to derail readiness | Naming issues, scattered screenshots, outdated tracker formatting |
One of the fastest ways to overwhelm the team is to document every possible issue with equal intensity. A better approach is to write findings that are clear, useful, and actionable, but do not create more open work than the team can realistically close before the next phase.
Combine related issues where appropriate. Focus on root problems, not every symptom. Avoid vague findings nobody knows how to fix.
The internal audit is only useful if the output leads to cleanup. A good post-audit action plan usually includes the finding, required action, owner, target date, evidence needed for closure, and a verification step.
| Finding | Action | Owner | Target Date |
|---|---|---|---|
| Access review evidence incomplete | Standardize review output and store latest completed review centrally | IT Lead | May 15 |
| Vendor reassessments inconsistent | Complete missing critical vendor reviews and define annual schedule | Operations Lead | May 22 |
| Incident records lack closure notes | Update incident template and complete closure summaries for recent events | Security Lead | May 12 |
A startup internal audit should end with more than a list of issues. It should also answer the higher-level question: are we close, or are we still structurally unready?
A simple readiness summary gives leadership a better picture than findings alone.
To keep the audit useful, avoid a few common mistakes.
| Checkpoint | Done? |
|---|---|
| Scope is defined and limited | ☐ |
| Audit lead is identified | ☐ |
| Key control owners are scheduled for short interviews | ☐ |
| Evidence review list is prepared | ☐ |
| Focus areas are prioritized | ☐ |
| Findings format is defined | ☐ |
| Corrective action tracker is ready | ☐ |
| Readiness summary will be produced | ☐ |
At Canadian Cyber, we often see startups delay internal audit work because they think it has to be heavy, formal, and disruptive. It does not.
The most effective pre-certification internal audits for startups are usually the ones that stay focused on a few things: real control operation, evidence readiness, ownership clarity, and manageable corrective action.
That approach gives the team a realistic picture without flooding them with work they cannot absorb. The goal is not to simulate a giant enterprise audit. It is to create enough honest pressure that the startup can fix the important issues before external review begins.
A startup does not need a massive internal audit to prepare for certification well. It needs a lean, honest, pre-certification review that checks whether key controls actually operate, whether evidence is ready, and whether the team can fix the remaining issues without burnout.
The most practical DIY internal audits usually work because they keep scope tight, focus on high-value controls, use short interviews, test real evidence, prioritize only the most important findings, and turn results into a manageable corrective action plan.
Because in the end, the purpose of a pre-certification internal audit is not to overwhelm the team. It is to make the external audit far less overwhelming.