SOC 2 • Continuous Controls Monitoring • CCM • SaaS Compliance • Audit Readiness
Continuous Controls Monitoring Is Eating the SOC 2 Type II Calendar
Waiting 12 months to find a control failure is like checking your smoke alarm once a year while the house burns. Continuous Controls Monitoring helps SaaS teams find issues earlier, keep evidence current, and avoid audit-season panic.
Quick Snapshot
| CCM Area | Why It Matters |
|---|---|
| Traditional SOC 2 | Evidence is often collected in batches before or during the audit period. |
| Continuous Controls Monitoring | Controls are checked more often through automated signals, integrations, and alerts. |
| Main Benefit | Control failures are found earlier, not months later. |
| Common Tools | Vanta, Drata, Secureframe, Sprinto, Thoropass, Hyperproof, and custom cloud workflows. |
| Business Outcome | Faster reviews, fewer surprises, better buyer confidence, and cleaner Type II preparation. |
Introduction
SOC 2 Type II used to feel like a calendar event.
The old rhythm looked like this:
- pick an audit period
- collect evidence
- chase owners
- fix gaps
- answer auditor questions
- wait for the report
- start again next year
That model is breaking.
Modern SaaS teams move too quickly for annual evidence scrambles. Cloud environments change daily. Employees join and leave. Vendors change. Access changes. Code ships constantly. Alerts fire. Tickets close. Policies update. Infrastructure moves.
If a control fails in February, finding out during the audit in November is too late.
Continuous Controls Monitoring helps teams monitor control health throughout the year, so SOC 2 stops feeling like a once-a-year fire drill.
Want SOC 2 Evidence That Stays Ready?
Canadian Cyber helps SaaS teams build continuous evidence workflows, control monitoring processes, SharePoint evidence workspaces, and vCISO-led SOC 2 readiness programs.
Build My SOC 2 Evidence System
Explore SharePoint Evidence Workspaces
What Continuous Controls Monitoring Actually Means
Continuous Controls Monitoring, or CCM, is the practice of checking whether key controls are operating on an ongoing basis.
It does not mean every control is checked every second.
It means the company has a repeatable way to monitor control status, evidence freshness, exceptions, and failures across the audit period.
| Traditional SOC 2 Evidence | CCM Approach |
|---|---|
| Collected close to audit time. | Collected throughout the year. |
| Manual screenshots. | Automated integrations where possible. |
| Evidence stored in random folders. | Evidence mapped to controls. |
| Control failures found late. | Control failures flagged earlier. |
| Audit prep is stressful. | Audit readiness becomes routine. |
Practical rule: CCM is not just a tool. It is a control operating model.
Why Annual SOC 2 Evidence Collection Is Breaking
Annual evidence collection worked better when systems changed slowly.
That is not how SaaS works anymore.
SaaS environments change constantly:
- new employees join
- users leave
- developers deploy code
- vendors are added
- cloud roles change
- support tools expand
- APIs are updated
- infrastructure scales
A control that worked in January may fail in March. If no one checks until audit time, the damage is already done.
| Audit Surprise | Why It Happens |
|---|---|
| Access review missing for one system. | System was added but not included in review scope. |
| Vendor review overdue. | Vendor register was not maintained. |
| MFA exception undocumented. | Exception was allowed but never approved. |
| Backup restore test incomplete. | Backups ran, but recovery was not tested. |
| Policy review missed. | Owner changed and review date passed. |
Why CCM Is Trending Now
CCM is growing because SaaS teams need faster, cleaner assurance.
Enterprise buyers expect SOC 2. Investors expect security maturity. Procurement teams expect fresh evidence. Cyber insurance forms ask detailed control questions. Boards want risk visibility.
| Driver | What It Means |
|---|---|
| Faster SaaS release cycles | Controls must keep up with product and cloud changes. |
| More enterprise security reviews | Evidence needs to be ready before buyers ask. |
| SOC 2 is table stakes | The edge is speed, clarity, and trust. |
| Tool integrations are mature | GRC platforms can connect to cloud, HR, ticketing, and identity systems. |
| Manual audit prep is expensive. | Teams want fewer last-minute evidence hunts. |
The tool choice matters less than the operating model. A tool can monitor signals. Your team still has to own the control.
What CCM Can Monitor Well
Some controls are easier to monitor than others.
CCM works best when the control has a clear system signal, evidence source, or recurring workflow.
| Control Area | What Can Be Monitored |
|---|---|
| MFA | Whether users have MFA enabled. |
| Device Security | Encryption, screen lock, antivirus, and endpoint agent status. |
| Access Control | User access, admin roles, and review completion. |
| Vulnerability Management | Open findings, severity, and SLA status. |
| Change Management | Pull requests, approvals, and deployment records. |
| Policy Reviews | Review dates, approval status, and overdue policies. |
What Still Needs Human Review
CCM can flag status. It cannot replace judgment. Human review still matters for:
- risk acceptance
- policy approval
- vendor approval decisions
- incident severity decisions
- customer notification decisions
- exception approval
- management review
Automate the signal. Keep humans responsible for the decision.
The Big Shift: From Evidence Collection to Control Health
Traditional audit prep asks, “Do we have evidence?”
CCM asks a better question:
“Is the control healthy right now?”
That is stronger because it tells leadership whether the control is actually operating.
| Control | Status | Issue | Owner |
|---|---|---|---|
| MFA Enforcement | Green | No gaps | IT |
| Access Reviews | Amber | GitHub review due in 7 days | Engineering |
| Vendor Reviews | Red | Two critical vendors overdue | Operations |
| Backup Recovery | Amber | Restore test pending | IT |
How CCM Changes the SOC 2 Type II Calendar
SOC 2 Type II still has an audit period.
But CCM changes what happens during that period. Instead of waiting until the audit is close, the team monitors evidence and control health throughout the year.
| Old SOC 2 Calendar | CCM-Driven SOC 2 Calendar |
|---|---|
| Audit period starts. | Audit period starts with control owners and evidence sources defined. |
| Controls operate, but evidence collection is inconsistent. | Control health is reviewed monthly or quarterly. |
| Team starts evidence cleanup late. | Tool integrations flag missing evidence and failures throughout the year. |
| Gaps are found close to audit time. | Issues are corrected early. |
| Audit creates surprises. | Evidence is already organized before audit. |
CCM does not remove the SOC 2 calendar. It stops the calendar from controlling you.
The Smoke Alarm Problem
Waiting 12 months to find a control failure is like checking your smoke alarm once a year while the house burns.
A policy can exist. A tool can be installed. A process can be documented. A control can pass once. But if it fails quietly for months, the business is still exposed.
| Control Failure | Late Discovery Problem |
|---|---|
| MFA disabled for a small group. | Account takeover exposure continues. |
| Critical vendor review missed. | Third-party risk is not accepted or controlled. |
| Backup restore test skipped. | Recovery ability is assumed, not proven. |
| Access review not completed. | Former users may retain access. |
| Vulnerability SLA missed. | Known exposure remains open. |
CCM catches smoke earlier. That is the point.
The CCM Evidence Pack
CCM should produce evidence that is useful for auditors and leadership.
Not just dashboard screenshots.
| Evidence Item | What It Shows |
|---|---|
| Control Inventory | Which controls are monitored. |
| Evidence Source Map | Which system provides evidence. |
| Owner List | Who owns each control. |
| Monitoring Frequency | How often the control is checked. |
| Exception Register | Open exceptions and approvals. |
| Remediation Tickets | Actions taken to fix gaps. |
Example Evidence Source Map
| Control | Evidence Source | Owner | Frequency |
|---|---|---|---|
| MFA enabled | Entra ID / Okta | IT | Continuous / monthly review |
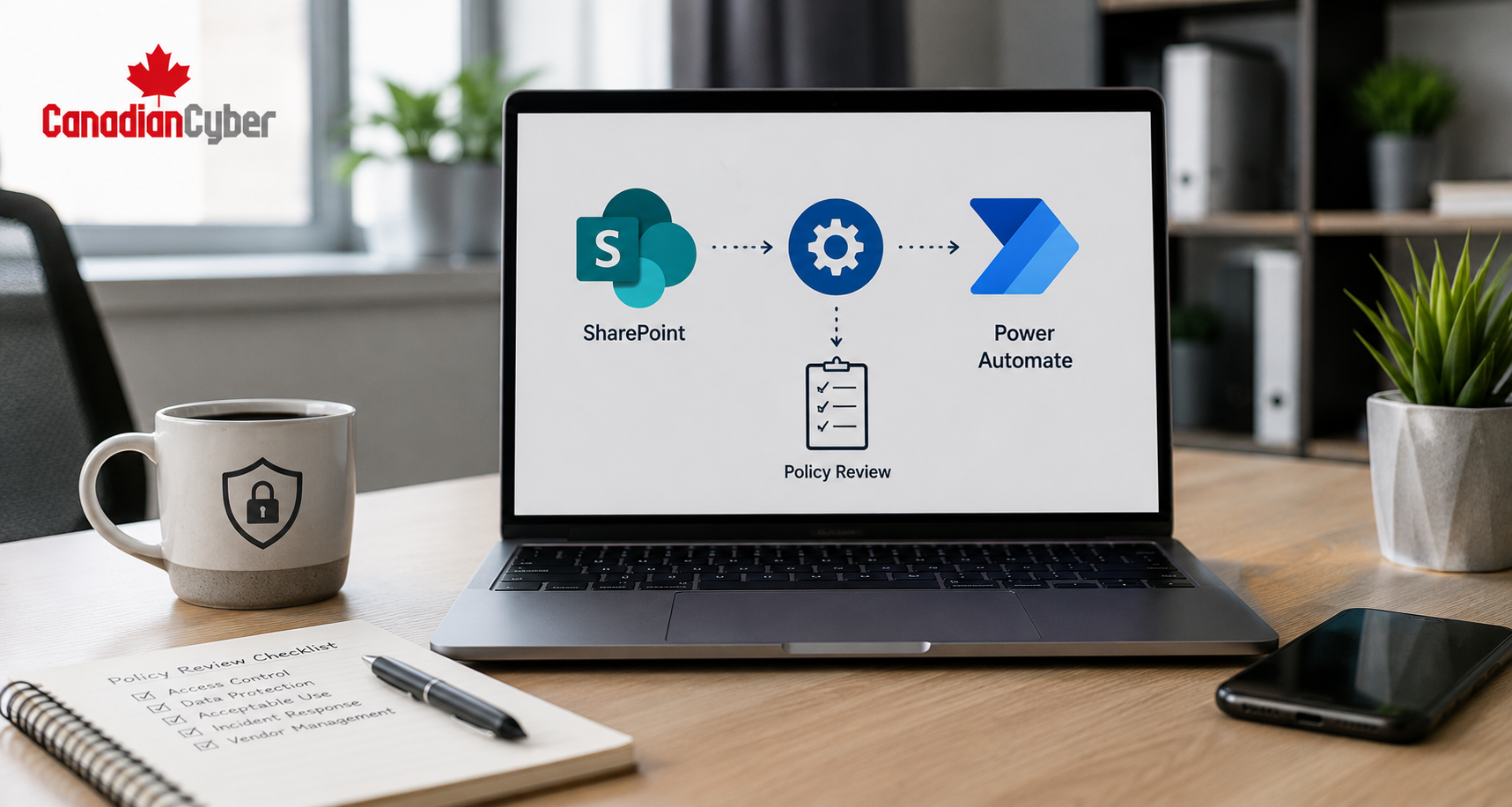
| Access review | SharePoint tracker / GRC tool | System owners | Quarterly |
| Vendor review | Vendor register | Operations | Annual / quarterly check |
| Change approval | GitHub / Jira | Engineering | Continuous |
Where Vanta, Drata, and Secureframe Fit
Tools like Vanta, Drata, and Secureframe can be very useful.
They can connect to systems, monitor control status, track evidence, remind owners, centralize audit requests, and show gaps.
| Platform Capability | Value |
|---|---|
| Integrations | Pull evidence from cloud, HR, identity, code, and ticketing tools. |
| Automated checks | Flag control failures faster. |
| Evidence mapping | Connect proof to control requirements. |
| Task reminders | Push owners to complete work. |
| Readiness dashboards | Show status before audit. |
What These Platforms Do Not Solve Alone
- unclear SOC 2 scope
- weak risk management
- bad policies
- no owner accountability
- poor vendor decisions
- untested incident response
- missing management review
- unrealistic control commitments
A CCM tool is not the compliance program. It is the monitoring layer.
How to Start CCM Without Overbuilding
You do not need to monitor every control on day one.
Start with the controls that fail most often and matter most to buyers.
| Phase | Focus Area |
|---|---|
| Phase 1 | MFA, access reviews, offboarding, vendor reviews, vulnerability management, training, backup restore testing, and policy reviews. |
| Phase 2 | Cloud configuration checks, GitHub branch protection, deployment approval evidence, logging reviews, container scanning, and secret scanning. |
| Phase 3 | Executive reporting for control health, overdue evidence, open exceptions, audit readiness, high-risk gaps, and remediation progress. |
Start with controls that are easy to monitor and painful to fail.
CCM Checklist for SOC 2 Teams
Use this checklist to assess your current readiness.
| Question | Yes / No |
|---|---|
| Do we have a complete SOC 2 control inventory? | |
| Does each control have an owner? | |
| Do we know which controls can be monitored automatically? | |
| Do we know which controls need manual review? | |
| Are evidence sources mapped to controls? | |
| Are control failures flagged before audit time? | |
| Are exceptions documented and approved? | |
| Are remediation tickets linked to failed controls? | |
| Is evidence stored in a way auditors can review? |
Common Mistakes to Avoid
- Mistake 1: Thinking CCM means “set it and forget it.” Monitoring is not ownership. Someone must review alerts, approve exceptions, and close gaps.
- Mistake 2: Monitoring too much too soon. Start with key controls. Expand once the process works.
- Mistake 3: Trusting green dashboards without sampling. Automated checks can miss context. Review samples and exceptions.
- Mistake 4: Ignoring manual controls. Management review, risk acceptance, incident decisions, and vendor approvals need people.
- Mistake 5: Not linking failed checks to remediation. A failed control should create an action.
- Mistake 6: Using CCM only for the auditor. CCM should help operations, leadership, sales, and risk management too.
- Mistake 7: Letting evidence live only inside the tool. Keep exportable evidence and summaries.
What Good Looks Like
A strong CCM-backed SOC 2 program has:
- control owners
- evidence source mapping
- automated checks where possible
- manual review where needed
- exception tracking
- remediation tickets
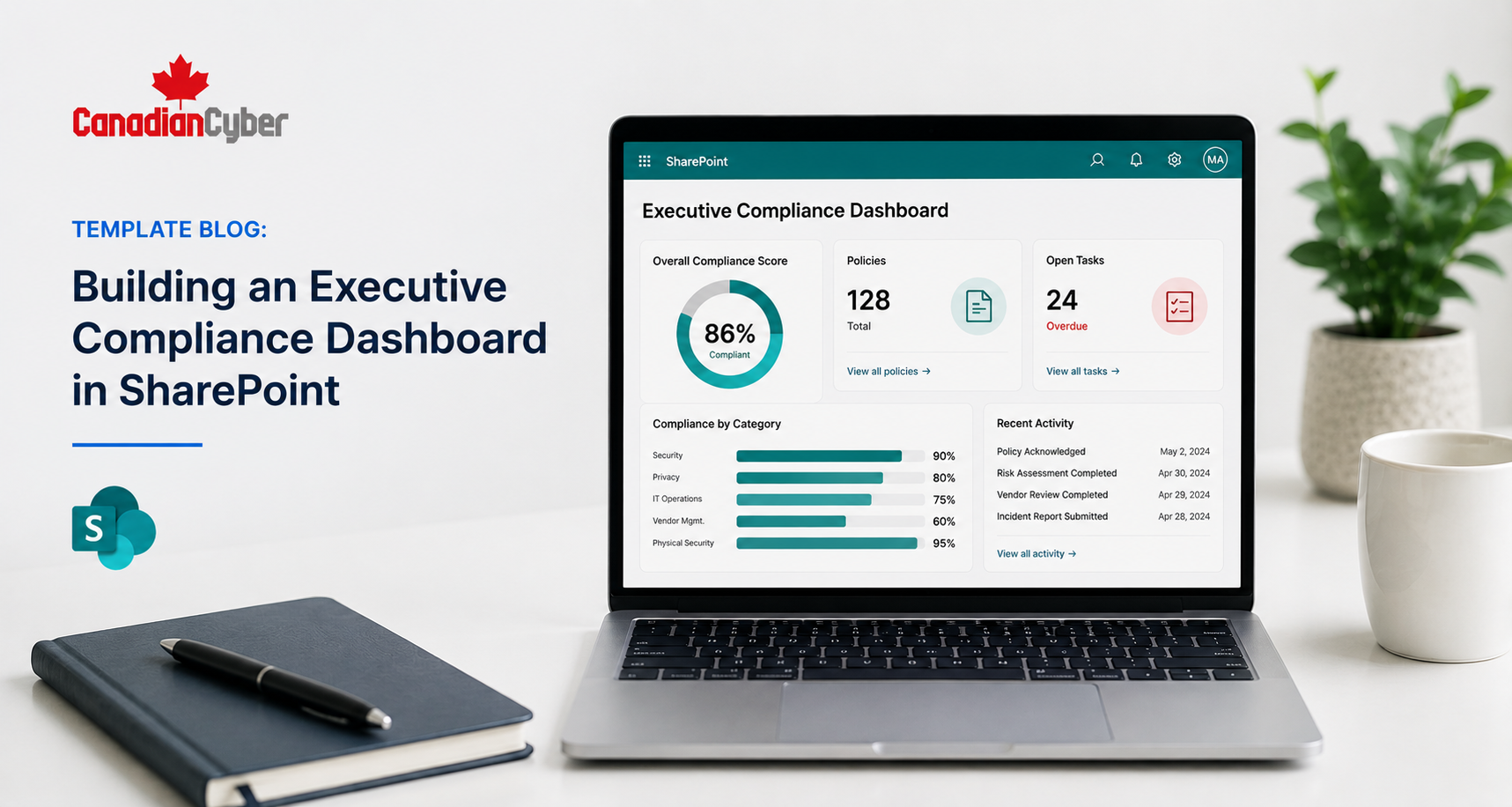
- control health dashboard
- quarterly reviews
- audit-ready evidence packs
- leadership reporting
- fresh trust materials for buyers
The team does not wait until audit time to find issues. It finds them during the year.
Canadian Cyber’s Take
At Canadian Cyber, we often see SaaS teams buy a compliance automation platform and assume SOC 2 will run itself.
It will not.
Tools like Vanta, Drata, and Secureframe are useful. But the real value comes when the company defines ownership, evidence sources, review cadence, exception handling, and remediation workflows.
Continuous Controls Monitoring is not about replacing auditors.
It is about reducing surprises. It helps teams catch control failures while there is still time to fix them. It also helps sales and customer success because trust evidence stays current throughout the year.
The best SOC 2 programs are no longer audit-season programs. They are operating systems.
Takeaway
Annual SOC 2 evidence scrambles are losing ground.
Continuous Controls Monitoring is becoming the new standard for cloud-native SaaS teams.
The reason is simple.
A control failure found early is manageable. A control failure found at audit time is expensive.
Start by doing the basics well:
- map your controls
- assign owners
- connect evidence sources
- monitor high-value controls first
- track exceptions
- link failures to remediation
- review control health regularly
- keep evidence audit-ready throughout the year
Your SOC 2 Type II calendar still matters. But CCM makes sure it does not become a surprise machine.
How Canadian Cyber Can Help
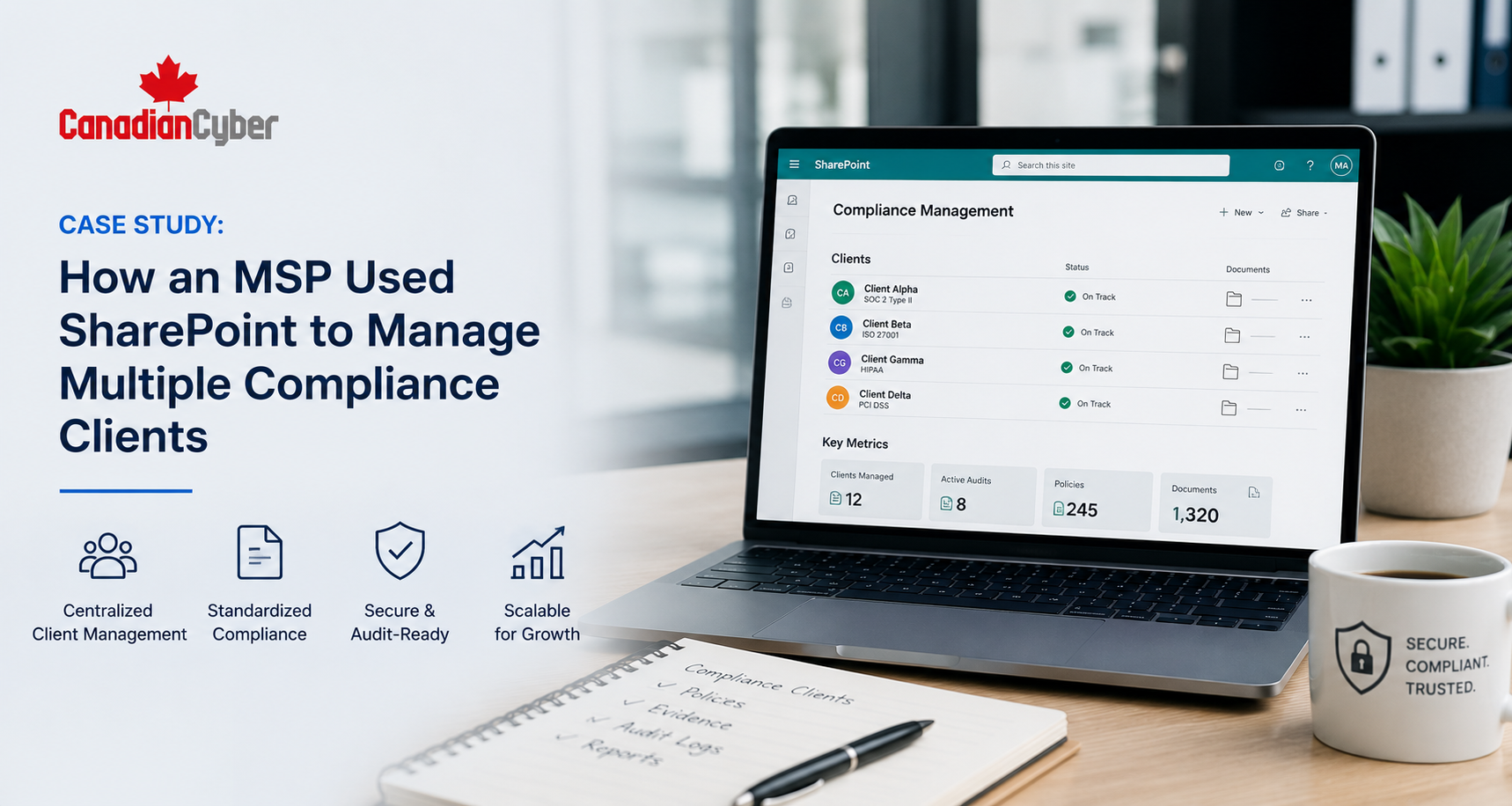
Canadian Cyber helps SaaS companies move from SOC 2 audit scramble to continuous control readiness.
- SOC 2 readiness reviews
- Continuous Controls Monitoring design
- Vanta, Drata, and Secureframe implementation support
- control inventory development
- evidence source mapping
- SharePoint evidence workspaces
- control health dashboards
- access review workflows
- vendor review tracking
- policy review reminders
- exception registers
- remediation tracking
- vCISO support for SOC 2 governance
Stay Connected With Canadian Cyber
Follow Canadian Cyber for practical guidance on SOC 2, CCM, SharePoint ISMS, SaaS compliance, audit readiness, ISO 27001, and vCISO support.