SharePoint ISMS • Evidence Naming • Audit Readiness • ISO 27001 • Evidence Vault
Checklist: SharePoint Evidence Naming Rules Auditors Appreciate
Good evidence naming makes audits faster. Bad evidence naming creates confusion, rework, and follow-up questions.
Quick Snapshot
| Evidence Naming Area | What Auditors Appreciate |
|---|---|
| Control Reference | File names show which ISO, SOC 2, or internal control they support. |
| Date or Period | Names show the month, quarter, year, or review period covered. |
| Evidence Type | Names explain whether the file is a review, report, approval, screenshot, export, or test record. |
| System or Process | Names identify the platform, process, vendor, or control area. |
| Outcome | Auditors can understand the evidence without asking your team to explain every file. |
Introduction
Audit evidence should be easy to find.
It should also be easy to understand.
That sounds simple. But many organizations lose time during ISO 27001, SOC 2, internal audits, customer security reviews, and management reviews because their evidence is poorly named.
Files often get saved as:
- Screenshot 1
- Audit evidence
- Access review final
- Backup test latest
- Vendor SOC2
- Final final
These names may make sense to the person who uploaded them. They do not help an auditor. In a SharePoint ISMS, evidence naming is part of audit readiness.
Why Evidence Naming Matters During Audits
Auditors do not only review the file.
They also review the story around the file.
They want to know:
- What control does this support?
- What period does it cover?
- Which system does it relate to?
- Is this the current version?
- Is it from the right audit period?
- Can it be traced to a risk, policy, control, or review?
Good naming answers some of these questions before the file is even opened. Bad naming creates friction.
| Poor Naming Problem | Audit Impact |
|---|---|
| No date in file name | Auditor cannot tell whether evidence is current. |
| No control reference | Evidence cannot be traced easily. |
| No system name | Reviewer does not know what platform the file supports. |
| Duplicate “final” files | Version control becomes unclear. |
| No period covered | Evidence may not match the audit window. |
A person outside your team should understand the file name without opening the file.
The Core Evidence Naming Formula
Use a consistent naming formula.
It does not need to be complicated. The goal is to make every file understandable.
Recommended naming formula:
ControlArea-System-EvidenceType-Period-Version
| Example | What It Tells the Auditor |
|---|---|
| AccessControl-EntraID-AccessReview-2026-Q1-v1.pdf | The evidence supports access control, relates to Entra ID, is an access review, covers Q1 2026, and is version 1. |
| A5.18-AccessControl-EntraID-PrivilegedAccessReview-2026-Q1.pdf | The evidence maps directly to ISO 27001 Annex A control A.5.18. |
Rule 1: Include the Control Area
Every evidence file should show the control area it supports.
This helps auditors connect the evidence to the audit request quickly.
| Control Area | Example File Name |
|---|---|
| Access Control | AccessControl-EntraID-AccessReview-2026-Q1.pdf |
| Vendor Management | VendorManagement-CriticalVendors-Review-2026-Q1.xlsx |
| Incident Response | IncidentResponse-TabletopExercise-2026-Q2.docx |
| Backup and Recovery | BackupRecovery-ProductionDB-RestoreTest-2026-03.pdf |
| Logging and Monitoring | LoggingMonitoring-SIEM-LogReview-2026-04.pdf |
Rule 2: Include the System, Platform, or Process
Evidence should identify what it relates to.
For cloud and SaaS environments, this is very important.
| Weak Name | Better Name |
|---|---|
| AccessReview-Q1.pdf | AccessControl-EntraID-AccessReview-2026-Q1.pdf |
| BackupTest.pdf | BackupRecovery-AWSRDS-RestoreTest-2026-03.pdf |
| VendorReview.pdf | VendorManagement-Zendesk-SecurityReview-2026-Q1.pdf |
| Logs.pdf | LoggingMonitoring-CloudTrail-LogReview-2026-04.pdf |
Do not make auditors guess which system the evidence belongs to. Put the system name in the file name.
Rule 3: Include the Evidence Type
A file name should explain what kind of evidence it is.
Different evidence types prove different things.
| Evidence Type | What It Shows |
|---|---|
| AccessReview | Access was reviewed. |
| ApprovalRecord | Approval was completed. |
| Screenshot | Configuration or setting proof. |
| RestoreTest | Recovery capability was tested. |
| TabletopRecord | An incident exercise was performed. |
Rule 4: Include the Period Covered
This is one of the most important naming rules.
Auditors often test a specific period. If your evidence does not show the period covered, the auditor may ask follow-up questions.
| Format | Use Case |
|---|---|
| 2026-Q1 | Quarterly evidence. |
| 2026-03 | Monthly evidence. |
| 2026-H1 | First half of the year. |
| 2026-Annual | Annual review. |
| 2026-03-15 | Specific event or approval date. |
If the evidence proves a control operated during a specific time, include that time in the file name.
Rule 5: Use Control References Where Helpful
Control references improve traceability.
They are especially useful in mature SharePoint ISMS environments where evidence maps directly to ISO 27001, SOC 2, or internal controls.
| Framework | Example File Name |
|---|---|
| ISO 27001 Annex A | A5.18-AccessControl-EntraID-AccessReview-2026-Q1.pdf |
| ISO 27001 Clause | Clause9.3-ManagementReview-Minutes-2026-Q2.docx |
| SOC 2 | CC6.1-AccessControl-MFAEvidence-2026-Q1.pdf |
| Internal Control ID | CTRL-AC-04-PrivilegedAccessReview-2026-Q1.pdf |
Rules That Keep Naming Clean
Good naming is not only about what to include.
It is also about what to avoid.
| Rule | Practical Guidance |
|---|---|
| Avoid “final,” “latest,” and “updated” | Use dates, versions, and approval status instead. |
| Keep names short but complete | Include control area, system, evidence type, period, and version where needed. |
| Use consistent separators | Hyphens are usually easiest for sorting, scanning, and automation. |
| Use clear abbreviations only | Avoid internal nicknames, unexplained shortcuts, and project code names. |
Use dates and version numbers instead of vague words. “Final” is not a control.
Rule 10: Name Screenshots Properly
Screenshots are common audit evidence.
They are also often poorly named. A screenshot should include the control area, system, setting shown, and date captured.
| Weak Name | Better Name |
|---|---|
| Screenshot.png | AccessControl-EntraID-MFAEnforcement-Screenshot-2026-04-10.png |
| image1.png | LoggingMonitoring-Sentinel-RetentionSetting-Screenshot-2026-04-10.png |
| backup.png | BackupRecovery-AWSBackupPolicy-Screenshot-2026-04-10.png |
A screenshot without context is weak evidence. A named screenshot with control context is much stronger.
Rule 11: Name Reviews, Approvals, and Decisions Clearly
Reviews and approvals are often tested during audits.
If the evidence shows a decision, name the decision clearly.
| Evidence | Good File Name |
|---|---|
| Policy approval | PolicyReview-AccessControlPolicy-ApprovalRecord-2026-03-12.pdf |
| Risk acceptance | RiskManagement-RiskAcceptance-RISK-014-2026-Q1.pdf |
| Vendor approval | VendorManagement-Zendesk-ApprovalDecision-2026-Q1.pdf |
| Access review sign-off | AccessControl-EntraID-AccessReviewSignoff-2026-Q1.pdf |
Rule 12: Name Corrective Action Evidence by Finding ID
Corrective action evidence should connect to the finding it closes.
This helps internal audit, external audit, and management review.
| Finding ID | Good Evidence Names |
|---|---|
| IA-2026-004 | CAPA-IA-2026-004-GuestAccessReview-2026-Q2.pdf |
| IA-2026-004 | CAPA-IA-2026-004-GuestRemovalEvidence-2026-Q2.xlsx |
| IA-2026-004 | CAPA-IA-2026-004-ClosureSignoff-2026-05-10.pdf |
Auditors can trace finding → corrective action → evidence → closure. That is clean audit logic.
Naming Examples Auditors Commonly Ask For
Some evidence categories are requested often.
Use clear names for these areas first.
| Evidence Area | Good File Name |
|---|---|
| Vendor register | VendorManagement-VendorRegister-2026-Q2.xlsx |
| Vendor SOC 2 review | VendorManagement-Datadog-SOC2Review-2026-Q1.pdf |
| Privileged access review | AccessControl-EntraID-PrivilegedAccessReview-2026-Q1.pdf |
| Restore test | BackupRecovery-ProductionDB-RestoreTest-2026-03-15.pdf |
| Log review | LoggingMonitoring-SIEM-LogReview-2026-04.pdf |
Do not just save vendor reports. Save review decisions. The file name should show that the vendor was actually assessed.
SharePoint Evidence Naming Checklist
Use this checklist before uploading evidence to your ISMS SharePoint site.
| Question | Yes / No |
|---|---|
| Does the file name include the control area? | |
| Does it identify the system, platform, vendor, or process? | |
| Does it describe the evidence type? | |
| Does it include the period or date covered? | |
| Does it avoid vague words like final, latest, or updated? | |
| Does it use consistent separators? | |
| Can an auditor understand the file without opening it? | |
| Can the evidence be traced to a control, risk, audit finding, or review? |
Recommended SharePoint Evidence Vault Structure
Evidence naming works best when the SharePoint structure also makes sense.
Use a clean evidence vault with metadata, views, and control mapping.
| Folder / Library | Evidence Examples |
|---|---|
| 01 Governance | Management review, policy approvals, leadership decisions. |
| 02 Risk Management | Risk register, risk reviews, risk acceptance. |
| 03 Access Control | User reviews, privileged access, offboarding. |
| 04 Vendor Management | Vendor reviews, SOC report reviews, approvals. |
| 10 Internal Audit | Audit plans, findings, CAPA closure evidence. |
Ready to Move Beyond Scattered Evidence Folders?
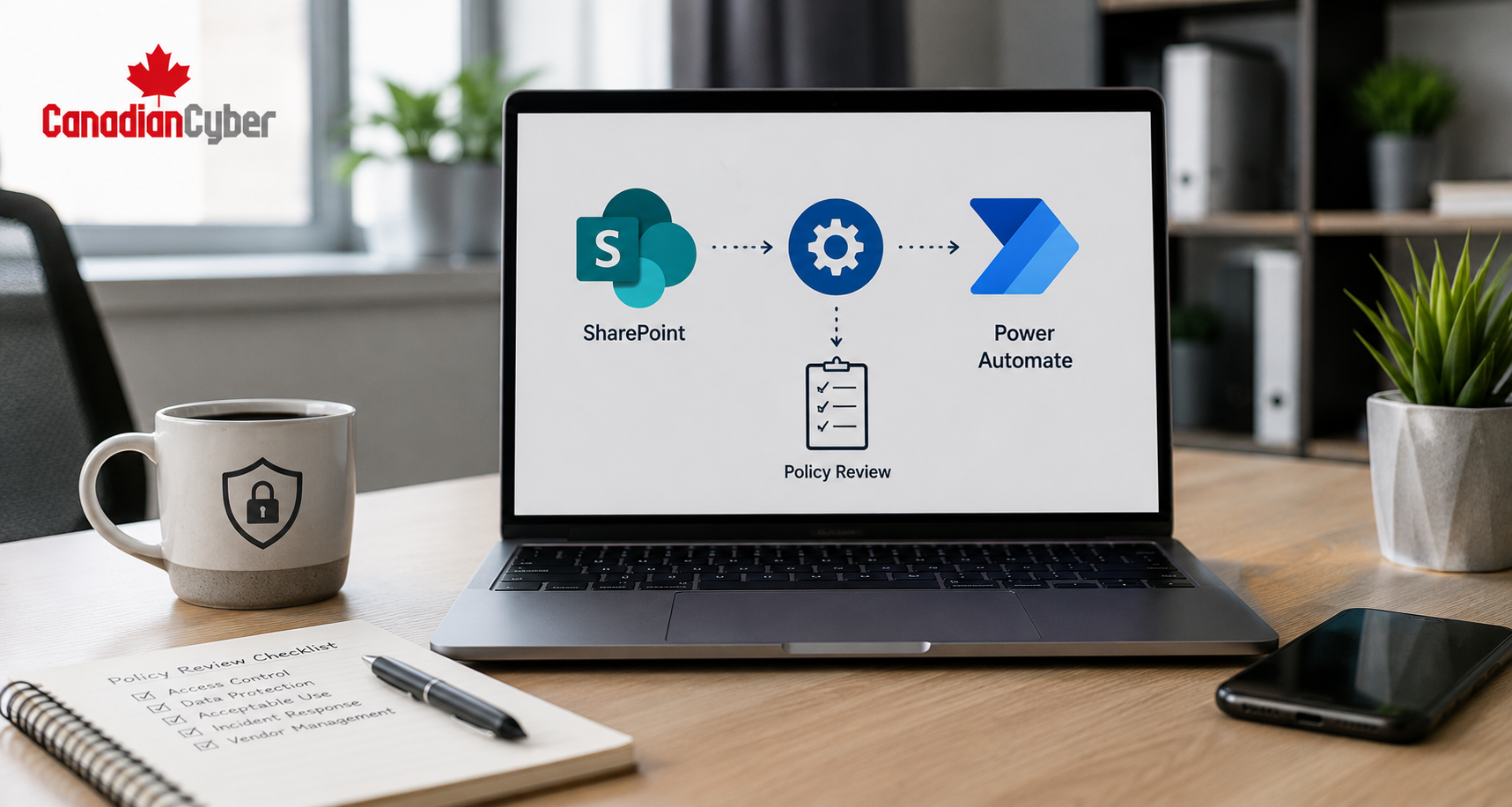
Canadian Cyber’s ISMS SharePoint solution helps organizations build structured evidence vaults with metadata, dashboards, review workflows, and audit-ready naming conventions.
Explore the SharePoint ISMS Evidence Vault
Talk to Canadian Cyber
Common Mistakes to Avoid
- Mistake 1: Letting everyone name files differently. Give control owners a naming standard.
- Mistake 2: Using “final” instead of version numbers. Use dates, versions, and approval status.
- Mistake 3: Forgetting the audit period. Evidence must match the review period.
- Mistake 4: Naming screenshots too vaguely. Screenshots need system, setting, and date.
- Mistake 5: Saving vendor reports without review evidence. Name and save the review decision.
- Mistake 6: Relying only on folder location. A file name should still make sense if downloaded or moved.
- Mistake 7: Making file names too long. Clear is good. Overloaded is not.
Example Naming Standard You Can Use
Here is a simple standard for your SharePoint ISMS.
Standard format:
ControlArea-SystemOrProcess-EvidenceType-Period-Version
| Evidence Type | Example Name |
|---|---|
| Access review | AccessControl-EntraID-AccessReview-2026-Q1-v1.pdf |
| Vendor review | VendorManagement-Zendesk-SecurityReview-2026-Q1-v1.pdf |
| Tabletop record | IncidentResponse-PhishingTabletop-TabletopRecord-2026-Q2-v1.pdf |
| Restore test | BackupRecovery-ProductionDB-RestoreTest-2026-03-15-v1.pdf |
| CAPA closure | CAPA-IA-2026-004-ClosureEvidence-2026-05-v1.pdf |
What Good Looks Like
A strong SharePoint evidence naming system has:
- consistent naming rules
- clear control areas
- system or process names
- evidence types
- dates or periods
- version clarity
- metadata alignment
- control mapping
- owner accountability
- easy search and filtering
When auditors ask for evidence, your team should not need to search through messy folders. They should know where it is and what it proves.
Canadian Cyber’s Take
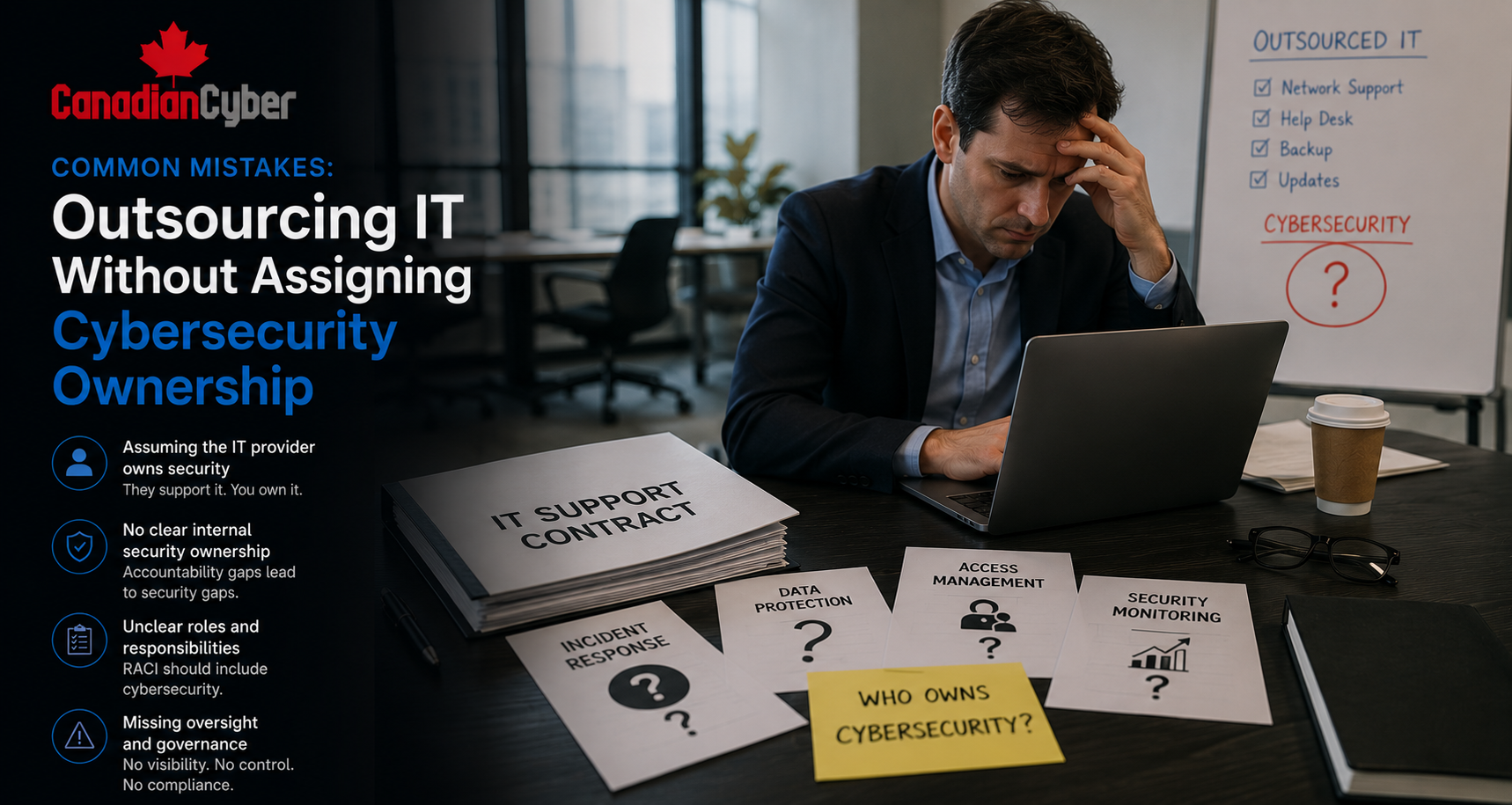
At Canadian Cyber, we often see organizations with the right evidence but poor evidence structure.
The control worked. The review happened. The approval was completed. The vendor was assessed. The restore test was run.
But the file name does not show it.
That creates avoidable audit stress. In a SharePoint ISMS, evidence naming is a small discipline with a big impact.
The best SharePoint ISMS builds combine naming rules, metadata, views, workflows, dashboards, and control mapping.
Takeaway
Evidence naming may seem minor.
It is not.
Good naming helps prove that your ISMS is organized, controlled, and audit-ready. Start with a simple formula:
- include the control area
- name the system or process
- describe the evidence type
- add the date or period
- use version numbers where needed
- avoid vague words
- store it in the right SharePoint evidence vault
Auditors appreciate evidence they can understand quickly. Your team will appreciate it too.
How Canadian Cyber Can Help
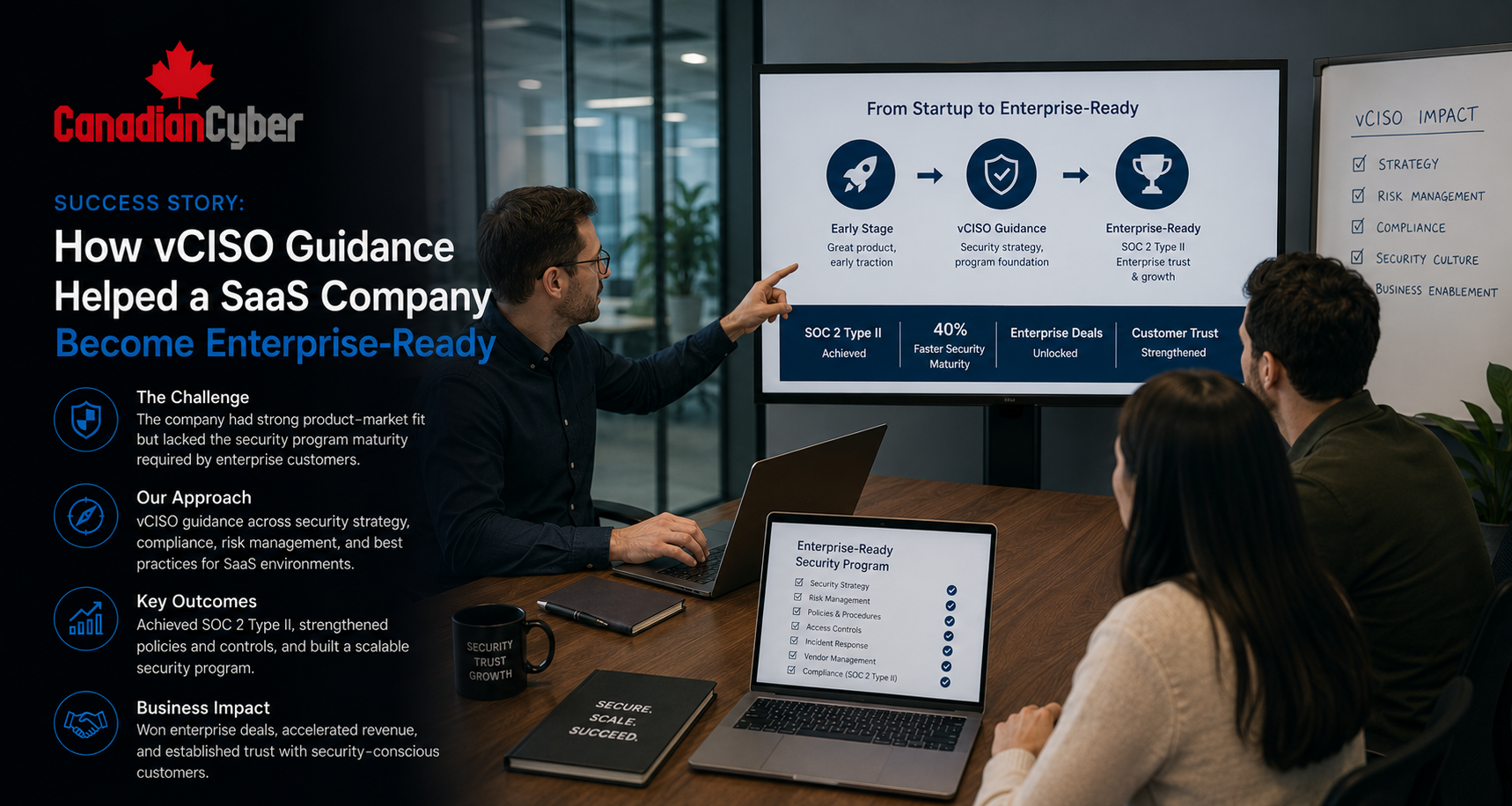
Canadian Cyber helps organizations build SharePoint ISMS evidence systems that are practical, searchable, and audit-ready.
- SharePoint ISMS evidence vault setup
- evidence naming standards
- metadata and view design
- ISO 27001 evidence mapping
- SOC 2 evidence organization
- policy review workflows
- risk register integration
- internal audit workspaces
- corrective action tracking
- vendor evidence libraries
- access review evidence packs
- vCISO support for audit readiness
Stay Connected With Canadian Cyber
Follow Canadian Cyber for practical guidance on SharePoint ISMS, evidence management, ISO 27001, SOC 2, audit readiness, and vCISO support.