SaaS Security • vCISO • Enterprise Readiness • Customer Trust • Security Governance
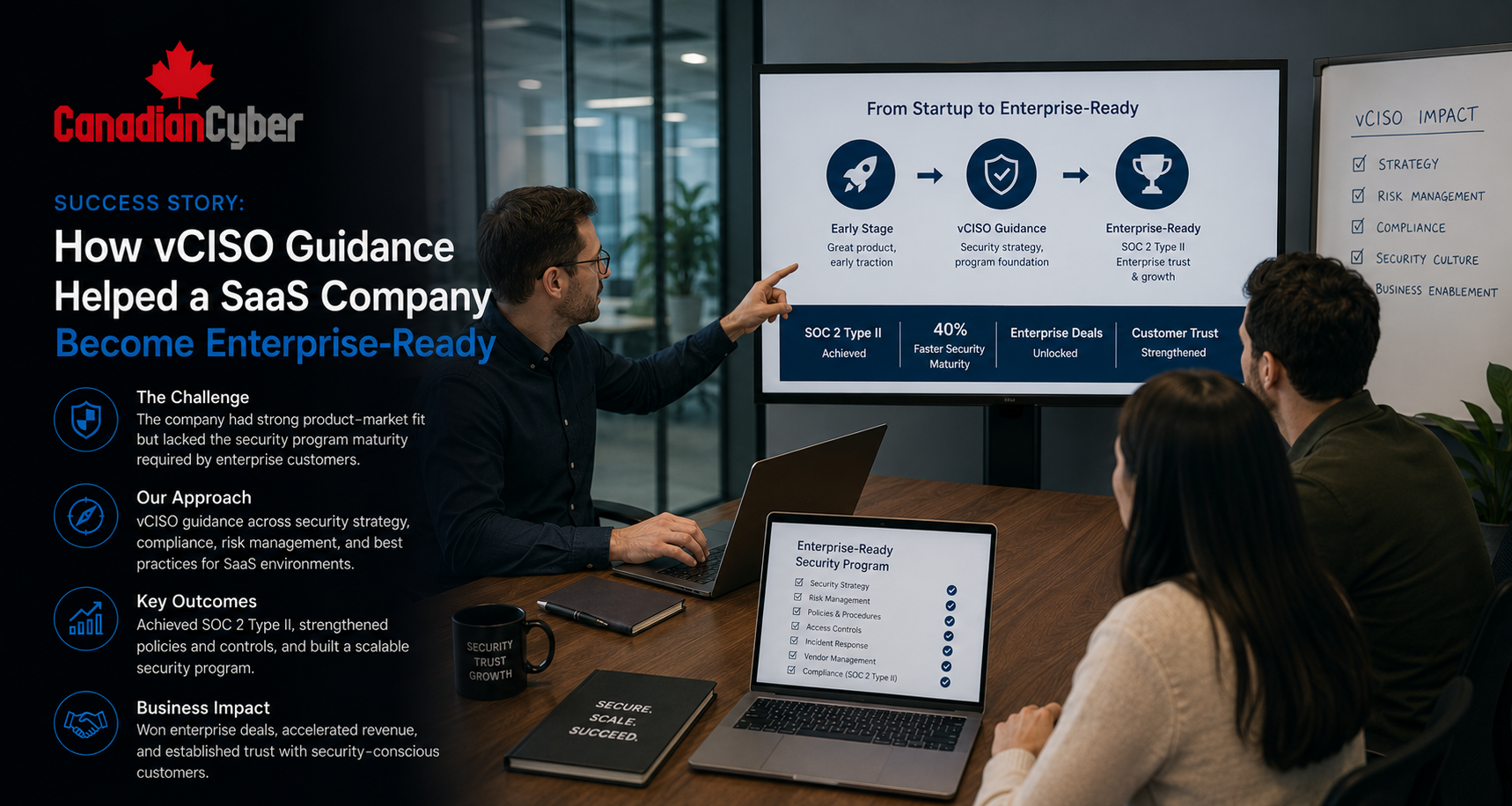
Success Story: How vCISO Guidance Helped a SaaS Company Become Enterprise-Ready
Enterprise buyers do not only ask whether your SaaS product works. They ask whether your company can protect customer data, prove controls, manage vendors, and respond to incidents with confidence.
Quick Snapshot
| Success Area | What Improved |
|---|---|
| Business Context | A growing SaaS company wanted to sell into larger enterprise accounts. |
| Main Challenge | Security questionnaires, vendor reviews, weak evidence, unclear ownership, and no executive cyber roadmap. |
| vCISO Focus | Risk register, access reviews, vendor governance, incident readiness, evidence packs, and customer trust materials. |
| Key Outcome | The company moved from reactive answers to an organized enterprise-readiness program. |
| Main Lesson | Enterprise readiness is about governance, evidence, leadership, and repeatable security operations. |
Introduction
Many SaaS companies reach the same turning point.
The product is strong. Customers like it. Revenue is growing. Larger prospects are interested.
Then enterprise due diligence begins.
A buyer may ask for:
- a long security questionnaire
- SOC 2 or ISO 27001 evidence
- sub-processor details
- SSO, MFA, logging, and encryption proof
- access review records
- incident response evidence
- clear cybersecurity ownership
This is where many SaaS teams feel the gap. They may have good technical controls, but enterprise buyers need more than good intentions. They need proof.
Trying to Become Enterprise-Ready?
Canadian Cyber helps SaaS companies prepare for enterprise security reviews, SOC 2, ISO 27001, customer due diligence, and board-level cyber reporting with practical vCISO guidance.
Meet the SaaS Company
Let’s call the company WorkFlowStack.
WorkFlowStack is a growing B2B SaaS company. It helps mid-market teams automate approvals, document workflows, and client onboarding.
The platform handles:
- customer account data
- workflow records
- uploaded documents
- user activity logs
- API integrations
- support tickets
- customer configuration data
At first, customers asked basic security questions. Then larger enterprise prospects entered the pipeline, and the questions became much deeper.
The product was enterprise-capable. The security program was not yet enterprise-ready.
The Starting Point
WorkFlowStack was not careless.
The company already had useful controls. But enterprise readiness exposed gaps in ownership, proof, and repeatability.
| Area | Existing Strength | Enterprise Gap |
|---|---|---|
| Authentication | MFA was available. | Review evidence was weak. |
| Cloud Hosting | Production ran in a major cloud provider. | Cloud evidence was scattered. |
| Backups | Automated backups were configured. | Restore testing proof was limited. |
| Policies | Some policies were drafted. | Approval and ownership were unclear. |
| Vendors | Critical vendors were known informally. | Vendor reviews were not formal. |
The problem was not the absence of security. The problem was the absence of a mature security operating model.
Why the SaaS Company Chose vCISO Guidance
WorkFlowStack considered hiring a full-time CISO.
But the company was not ready for that role yet. It needed structure, prioritization, and credibility fast.
A vCISO was the right fit.
| Business Need | vCISO Value |
|---|---|
| Enterprise buyer pressure. | Build customer-ready security evidence. |
| No full-time security leader. | Provide strategic leadership without permanent headcount. |
| Scattered security work. | Create a roadmap, owners, and governance cadence. |
| Customer questionnaires. | Standardize answers and proof. |
Workstream 1: Building the Enterprise Security Readiness Map
The first step was to understand what enterprise buyers were actually asking for.
The vCISO reviewed questionnaires, customer calls, sales objections, legal requests, and procurement comments. A pattern appeared quickly.
| Readiness Area | What Buyers Wanted |
|---|---|
| Governance | Security ownership, risk management, policies, and leadership review. |
| Access Control | MFA, SSO, privileged access, access reviews, and offboarding. |
| Cloud Security | Encryption, logging, backups, configuration, and monitoring. |
| Vendor Management | Sub-processors, vendor assurance, data processing, and risk reviews. |
| Incident Readiness | Incident response plan, escalation, tabletop evidence, and customer notification process. |
Need an Enterprise Readiness Map?
Canadian Cyber helps SaaS companies identify the security gaps that slow enterprise sales and turn them into a practical readiness roadmap.
Workstream 2: Creating a Risk Register Buyers Could Trust
Enterprise buyers often ask how a SaaS company manages security risk.
WorkFlowStack had risk discussions, but no formal risk register. The vCISO helped create one that was simple, useful, and evidence-based.
| Example SaaS Risk | Business Impact | Treatment |
|---|---|---|
| Excessive admin access to production. | Unauthorized access to customer data. | Complete privileged access review and reduce standing access. |
| Vendor breach affects customer records. | Customer trust and contract impact. | Review critical vendors and document approval decisions. |
| Incident response is untested. | Slow containment or poor customer communication. | Run tabletop exercise and track actions. |
| Cloud misconfiguration exposes files. | Data exposure and enterprise trust loss. | Review cloud baseline and monitoring evidence. |
The risk register showed buyers that security was being managed intentionally.
Workstream 3: Strengthening Access Reviews
Enterprise buyers care deeply about access.
They want to know who can access customer data, production systems, source code, support tools, cloud environments, and admin consoles.
| Access Area | Why It Mattered |
|---|---|
| Microsoft 365 / Entra ID | Identity, staff access, email, and documents. |
| Cloud Console | Production infrastructure access. |
| Source Control | Code and deployment risk. |
| Support Platform | Customer ticket and account data. |
| Customer Admin Tools | Privileged customer support functions. |
The vCISO helped implement:
- quarterly access reviews
- privileged access review templates
- offboarding evidence checklists
- service account registers
- support access reviews
- exception approval processes
Before, the company said “we restrict access based on roles.” After, it could prove access was role-based, reviewed, and evidenced.
Need Access Review Evidence Before a Big Deal?
Canadian Cyber helps SaaS teams set up access review workflows, privileged access evidence, offboarding proof, and exception registers for enterprise due diligence.
Workstream 4: Creating a Vendor and Sub-Processor Program
SaaS companies rarely operate alone.
WorkFlowStack used vendors for cloud hosting, email delivery, monitoring, analytics, customer support, identity, source control, CI/CD, and security tooling.
Enterprise buyers asked for a sub-processor list and vendor risk evidence.
| Vendor Field | Example |
|---|---|
| Vendor Name | Cloud Provider |
| Service Role | Production hosting |
| Data Handled | Customer data |
| Criticality | High |
| Review Decision | Approved with annual assurance review |
The company stopped collecting vendor documents randomly. It started recording decisions, owners, assurance evidence, data handled, and next review dates.
Workstream 5: Building the Customer Trust Pack
Enterprise buyers do not want scattered attachments.
They want clear, current, easy-to-review information. The vCISO helped WorkFlowStack create a customer trust pack.
| Trust Pack Section | What It Included |
|---|---|
| Security Overview | Plain-language summary of the security program. |
| Data Protection | Encryption, access control, backups, and data handling. |
| Cloud Security | Hosting, logging, monitoring, and configuration controls. |
| Vendor Management | Sub-processors, vendor reviews, and assurance evidence. |
| Compliance Roadmap | SOC 2 and ISO 27001 readiness path. |
The trust pack gave sales and customer success a reliable source of truth. It reduced back-and-forth and made the company look organized.
Want a Customer Trust Pack?
Canadian Cyber helps SaaS companies build customer-ready trust packs, questionnaire libraries, sub-processor lists, and evidence folders for enterprise due diligence.
Workstream 6: Testing Incident Response
WorkFlowStack had an incident response plan, but it had not been tested.
Enterprise buyers asked whether the company ran tabletop exercises. The answer was not yet.
The vCISO helped run a practical tabletop based on a customer support account compromise.
| Tabletop Tested | Evidence Created |
|---|---|
| Account containment. | Scenario notes and decision log. |
| Customer data impact analysis. | Lessons learned and owner list. |
| Legal and privacy escalation. | Corrective action register. |
| Customer communication. | Due dates and action tracking. |
The company could now say, “We test our incident response process and track corrective actions.” That was much stronger than saying, “We have a plan.”
Workstream 7: Preparing for SOC 2 and ISO 27001
Enterprise readiness often leads to formal assurance.
WorkFlowStack did not need to rush into every certification at once. The vCISO helped sequence the work.
| Phase | Focus | Output |
|---|---|---|
| Phase 1 | Enterprise readiness basics. | Trust pack, access reviews, and vendor register. |
| Phase 2 | SOC 2 readiness. | Control mapping and evidence collection. |
| Phase 3 | ISO 27001 planning. | Scope, risk register, and ISMS structure. |
| Phase 4 | Internal audit readiness. | Evidence testing and gap closure. |
The company did not waste time creating policies no one followed. It built operating evidence first.
Need a SOC 2 or ISO 27001 Readiness Path?
Canadian Cyber helps SaaS companies decide what to do first, what evidence to collect, which controls need owners, and how to prepare for formal assurance without wasting time.
Workstream 8: Creating Executive Cyber Reporting
Enterprise readiness is not only about buyer-facing evidence.
Leadership also needs visibility. The vCISO created a simple executive cyber report.
| Report Section | Purpose |
|---|---|
| Top Risks | Shows what could affect enterprise readiness. |
| Control Health | Shows access, vendors, incidents, backups, and logging. |
| Customer Due Diligence | Shows questionnaire status and buyer friction. |
| Compliance Roadmap | Shows SOC 2 and ISO 27001 progress. |
| 90-Day Plan | Shows near-term actions. |
The Results
After vCISO guidance, WorkFlowStack was much better prepared for enterprise buyers.
The company did not become perfect overnight. It became credible. That is what enterprise buyers needed to see.
| Before vCISO | After vCISO |
|---|---|
| Security answers were reactive. | Standard trust pack and response library. |
| Risk discussions were informal. | Risk register with owners and treatment plans. |
| Access reviews were inconsistent. | Quarterly access review process. |
| Vendors were known but not reviewed formally. | Vendor register and sub-processor review process. |
| Incident response plan was untested. | Tabletop completed with corrective actions. |
Lessons for Other SaaS Companies
| Lesson | Why It Matters |
|---|---|
| Enterprise readiness starts before certification. | Buyers may ask hard questions before SOC 2 or ISO 27001 is complete. |
| Access reviews are a high-value quick win. | Buyers care about who can access customer data. |
| Vendor governance matters. | Sub-processors are a major enterprise concern. |
| Incident response must be tested. | A plan is good. A tested plan is better. |
| Trust packs speed up sales. | Clear answers and evidence links reduce repeated work. |
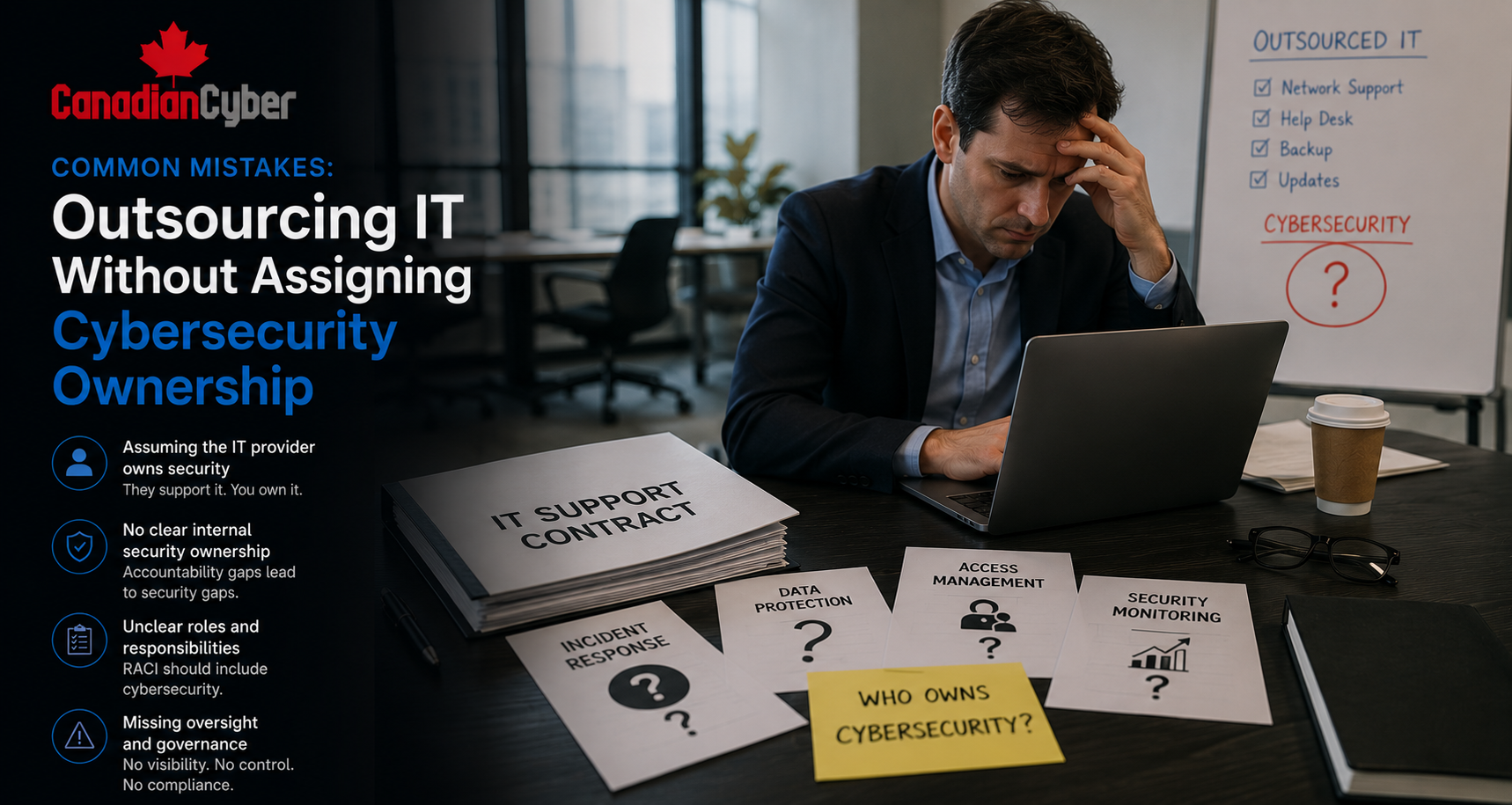
Common Mistakes to Avoid
- Mistake 1: Waiting for enterprise buyers to ask first. By then, the timeline is tight.
- Mistake 2: Treating questionnaires as one-off tasks. Each questionnaire should improve your response library.
- Mistake 3: Saying controls exist without proof. Enterprise buyers want evidence.
- Mistake 4: Ignoring vendor risk. If a vendor processes customer data, it belongs in the trust story.
- Mistake 5: Overbuilding policies before operations. Policies should match real controls.
- Mistake 6: Not involving leadership. Enterprise readiness needs executive support, funding, and risk decisions.
- Mistake 7: Buying tools without governance. Tools help only when owners, processes, and evidence exist.
What Good Looks Like
A SaaS company is enterprise-ready when it can show:
- clear security ownership
- risk register
- access review evidence
- vendor and sub-processor register
- incident response plan
- tabletop exercise evidence
- cloud security controls
- encryption and logging evidence
- customer trust pack
- questionnaire response library
- SOC 2 or ISO 27001 roadmap
The goal is not to look like a large enterprise immediately. The goal is to show that security is governed, improving, and supported by evidence.
Canadian Cyber’s Take
At Canadian Cyber, we often see SaaS companies that are technically strong but not yet enterprise-ready.
They have good engineers. They care about customer data. They use reputable cloud platforms. They have some controls in place.
But enterprise buyers need more than that.
They need clear governance, reliable evidence, vendor oversight, incident readiness, access review proof, and leadership accountability. That is where vCISO guidance creates value.
Enterprise readiness is not about pretending to be bigger than you are. It is about proving you are mature enough to be trusted.
Takeaway
A SaaS company becomes enterprise-ready when security is no longer reactive.
It has:
- a roadmap
- owners
- evidence
- risk management
- vendor governance
- incident readiness
- executive reporting
- a customer trust story
vCISO guidance helps build that structure without forcing the company to hire a full-time CISO too early.
How Canadian Cyber Can Help
Canadian Cyber helps SaaS companies become enterprise-ready with practical vCISO guidance.
- vCISO guidance for SaaS companies
- enterprise security readiness reviews
- customer trust pack development
- security questionnaire response libraries
- SOC 2 readiness planning
- ISO 27001 readiness planning
- risk register development
- access review workflows
- vendor and sub-processor reviews
- incident response tabletop exercises
- cloud security evidence packs
- 90-day enterprise readiness roadmaps
Stay Connected With Canadian Cyber
Follow Canadian Cyber for practical guidance on SaaS security, vCISO services, enterprise readiness, SOC 2, ISO 27001, customer trust, and cyber governance.