Why Startups Think ISO 27001 Is Out of Reach — And Why They’re Wrong
Before laying out the implementation roadmap, it is worth addressing the specific reasons startup teams delay because most of them are based on a misunderstanding of the standard.
“We don’t have a compliance person.”
ISO 27001 does not require a compliance person — it requires someone to own the ISMS. In a startup, that is typically the CTO or a co-founder with operational accountability. For most startups, combining this with a part-time vCISO covers the gap at a fraction of a full-time hire.
“It will take 18 months and cost $200,000.”
At startup scale with a focused cloud-based SaaS product, a realistic timeline is four to six months of focused effort. A realistic all-in cost including consultant support and certification body fees is $15,000 to $40,000 — and scope decisions are within your control.
“The documentation will bury us.”
ISO 27001:2022 reduced the mandatory document count compared to the 2013 version and explicitly acknowledges that documentation depth should be proportionate to organizational complexity. A startup with 12 employees does not produce the same volume as a regulated financial institution.
“Our tech stack isn’t mature enough.”
ISO 27001 is assessed against your risk profile not against an absolute technical standard. If you have identified your risks and implemented proportionate controls, your technology maturity is sufficient. Organizations using a “not ready” rationale are using a moving target to justify inaction.
The shortcut that breaks most startup implementations is treating the standard as a documentation exercise rather than a risk management discipline. Auditors spot this within the first 30 minutes of a Stage 2 audit, and the result is a non-conformity that costs months of rework and another audit fee.
The 8-Step ISO 27001 Implementation Roadmap for Startups
1
Define Your ISMS Scope — Start Small, Expand Later
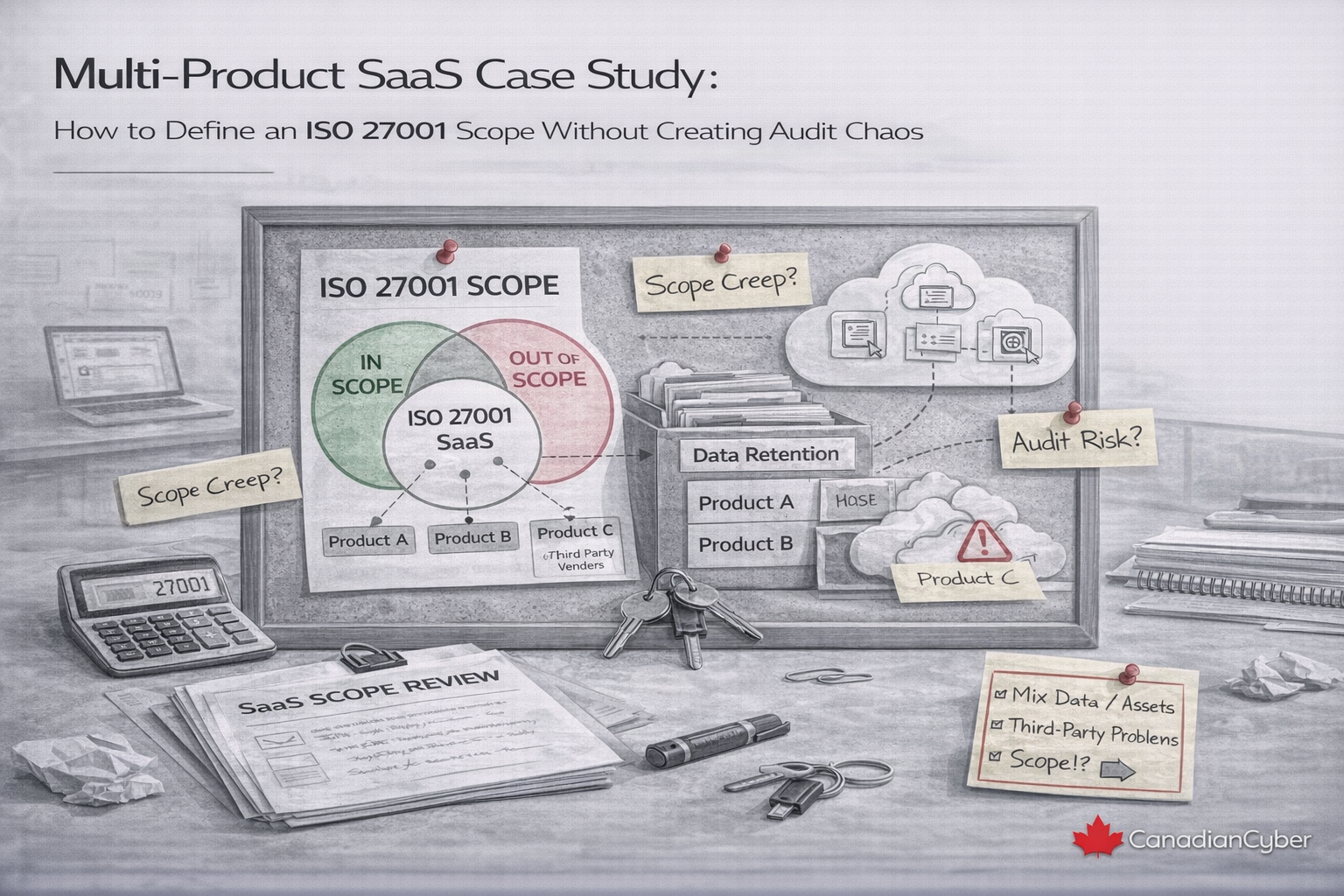
What It Is: The ISMS scope is the formally documented boundary of what is included in your certification the systems, processes, locations, teams, and assets within your ISO 27001 programme.
The scope decision is the single most consequential choice in a startup ISO 27001 implementation. Too broad, and you create a compliance burden that will overwhelm a lean team with evidence gaps you cannot fill. Too narrow, and your certificate covers so little that enterprise buyers will question its value.
What to Include in Your Scope
→Your production cloud environment (AWS, Azure, GCP — whichever you use)
→Your customer-facing application and APIs
→Your customer data stores and backup systems
→Your development and deployment pipeline (CI/CD)
→Supporting processes: access management, incident response, supplier management, HR security
→The people who operate all of the above
What You Can Legitimately Exclude
→Non-production environments where no customer data is processed (test and development environments, if properly isolated)
→Marketing and sales tools that do not process customer personal data
→Physical office security, if your team is fully remote and no sensitive data is processed on-site
Example Scope Statement: “The ISMS covers the development, operation, and support of [Product Name], a SaaS platform delivering [description], including the production infrastructure hosted on AWS ca-central-1, the engineering and operations teams responsible for its delivery, and the supporting processes for access management, incident response, supplier management, and information security governance.”
Pro Tip: Your scope statement must be honest it cannot exclude systems that process customer data simply because you would prefer not to secure them. Auditors will ask about systems that appear to be in-scope and are not listed, and the explanation must be defensible.
2
Assign Roles Without Hiring Headcount
What It Is: ISO 27001 requires defined roles for ISMS governance and operation. In a startup, these roles are assigned to existing team members. The goal is not to add headcount it is to make accountability explicit and documented.
Minimum Role Set for a Startup ISMS
ISMS Owner: Accountable for the overall ISMS — its implementation, operation, and continuous improvement. Typically the CTO or a technical co-founder. Owns the risk assessment process and chairs the management review.
Risk Owner(s): Named person responsible for each significant risk and its treatment plan. In small startups, the ISMS owner may hold most risk ownership roles — that is acceptable as long as accountability is explicit.
Asset Owners: Named person responsible for each information asset (database, code repository, customer data stores) and its security.
Internal Audit Lead: Conducts the internal audit. Cannot be the person primarily responsible for the controls being audited — independence is required.
Management Representative: Senior leader (CEO or COO) who demonstrates executive commitment to the ISMS and participates in the management review.
What Auditors Verify
ISO 27001 Clause 5 (Leadership) requires visible executive commitment to the ISMS not just delegation to a technical team. Auditors look for a signed Information Security Policy, documented management review records, and named role assignments with clear accountability.
A single-page Roles and Responsibilities document naming each role, naming the person filling it, and describing their responsibilities in three to five bullet points is the expected evidence. This document is referenced in your ISMS scope and reviewed annually.
Pro Tip: If your team is too small to separate the Internal Audit Lead from the control implementers, budget for a part-time ISO 27001 Lead Auditor or vCISO to conduct your internal audit independently. The cost is typically $1,500 to $3,000 and it satisfies the independence requirement cleanly without creative org chart labelling that auditors will see through.
3
Conduct Your Risk Assessment Properly
What It Is: The risk assessment identifies the information security risks relevant to your organization, evaluates their likelihood and impact, and produces a risk register that drives your control selection and implementation priorities.
The risk assessment is simultaneously the most important component of ISO 27001 and the most commonly done badly. The most frequent failure mode is treating it as a documentation formality populating a template with generic risks copied from the internet. Auditors can identify a superficial risk assessment within minutes, and a non-conformity here undermines the entire implementation.
How to Conduct a Risk Assessment That Holds Up
→Define your methodology first — likelihood scale (1–5), impact scale (1–5), risk rating formula, and your risk appetite statement before you start identifying risks
→Identify risks by information asset — not by generic category. Ask: what could go wrong with this asset that would compromise its confidentiality, integrity, or availability?
→Assess realistically — likelihood reflects the threat landscape, not your personal history of being breached. A startup with a public API has real credential theft risk regardless of prior incidents.
→Document treatment decisions for every risk above your appetite threshold: mitigate, accept, transfer, or avoid — and link the specific control that implements the treatment
Required Outputs
Risk Methodology Document: Your documented approach — likelihood scale, impact scale, rating formula, and risk appetite statement. This is the foundation your entire ISMS is built on.
Risk Register: A structured list of identified risks with likelihood, impact, risk rating, treatment option, linked controls, owner, and treatment status.
ISO 27001 Clause 6.1 requires your risk assessment to be reviewed at planned intervals and when significant changes occur. A risk assessment completed during implementation and never revisited fails the standard.
Pro Tip: Conduct the risk assessment as a facilitated workshop with your key technical and operational people — not as a solo exercise by the ISMS owner. The people who build and operate your systems know the threats better than any template. A two-hour workshop produces a better risk register than two weeks of solo documentation work.
4
Build Your Minimum Viable Documentation Set
What It Is: The specific set of policies, procedures, and records that ISO 27001:2022 mandates sized appropriately for a startup’s complexity and scope.
Mandatory Documents (Non-Negotiable)
→ISMS Scope Document
→Information Security Policy (signed by executive leadership)
→Risk Assessment Methodology and Risk Register
→Statement of Applicability (SoA) — all 93 Annex A controls with applicability and justification
→Risk Treatment Plan
→Information Security Objectives (with measurable targets)
→Competence and Awareness Records
→Internal Audit Programme and Reports
→Management Review Records
→Non-Conformity and Corrective Action Records
Supporting Policy Set (Required for Audit Evidence)
→Access Control Policy
→Acceptable Use Policy
→Data Classification Policy
→Incident Response Policy and Procedures
→Supplier Security Policy
→Business Continuity and Disaster Recovery Policy
→Cryptography and Encryption Policy
→Physical and Environmental Security Policy
→Secure Development Policy (if development is in scope)
→Human Resources Security Policy
Sizing Guidance: Each policy should be proportionate to the risk it addresses and the operational reality it governs. An Access Control Policy for a 10-person startup that uses a cloud IdP, enforces MFA, and reviews access quarterly can be three pages. What matters is that it accurately describes what you actually do not what a large enterprise does.
Pro Tip: Start with your Statement of Applicability. The SoA is the backbone of your Annex A control programme it forces you to make explicit decisions about every control before you start writing policies. Controls you exclude need a written justification. Controls you include need a link to a policy or procedure that implements them. Building the SoA first prevents the common mistake of writing policies for controls you do not actually need.
Not Sure Where Your ISMS Stands?
Get an honest ISO 27001 gap assessment before you begin
Canadian Cyber works with SaaS startups across Canada to scope, build, and certify ISMS programmes from gap assessment and risk methodology through to internal audit support, Stage 1 preparation, and certification body coordination.
5
Implement Controls That Fit a Startup Environment
What It Is: The actual technical and operational work of putting security controls in place the practices, configurations, and procedures that your ISMS policies describe and that auditors will verify are operating.
Not all 93 Annex A controls require the same implementation effort, and not all are equally critical for a startup’s risk profile. Here are the controls that carry the most audit weight and genuine risk reduction for a typical Canadian SaaS startup.
Priority Controls for Cloud-First SaaS Startups
Identity & Access (A 5.15–5.18): MFA on all production accounts — no exceptions. RBAC with least privilege. Quarterly access reviews. 24-hour offboarding procedure.
Cryptography (A 8.24): AES-256 at rest, TLS 1.2+ in transit, documented key management procedure.
Vulnerability Management (A 8.8): Regular scans, annual independent pen test, defined SLA for critical patch remediation (typically 30 days).
Logging & Monitoring (A 8.15–8.16): Security-relevant event logging, defined retention policy, anomaly detection and privilege escalation alerts.
Secure Development (A 8.25–8.29): Code review process, secrets management (no hardcoded credentials), dependency scanning for known vulnerabilities.
Supplier Management (A 5.19–5.22): Subprocessor list documented, pre-onboarding security review, DPAs in place with all suppliers handling personal data.
Incident Response (A 5.24–5.28): Documented and tested IRP, incident log maintained, post-incident review process defined.
Controls Implementation Tracker
For each control, create a one-line entry in a Controls Implementation Tracker with:
Control reference — the Annex A reference number
Implementation status — Not Started / In Progress / Implemented
Implementation owner — the named person responsible
Evidence reference — where the evidence that this control is operating can be found
This tracker is one of the most useful working documents in your ISMS — and exactly what your internal auditor will work from at Stage 2 preparation.
Pro Tip: Documenting your SDLC security controls is a significant differentiator. Application-layer vulnerabilities (OWASP Top 10 flaws, API security issues) are the source of many high-profile breaches and buyers in regulated sectors know this. Vendors who can demonstrate a structured development security process stand apart from those who can only describe their scanning tools.
6
Collect Evidence From Day One
What It Is: The ongoing practice of capturing and organizing documented proof that your controls are operating not assembling it retroactively the week before your audit.
ISO 27001 certification is an evidence-based assessment. Startup teams implement controls operationally and then have nothing to show an auditor. The access reviews happen but no record was kept. Controls that exist but are not evidenced are treated as absent at Stage 2 audit.
Evidence Collection by Control Category
Access management: IdP screenshots showing MFA enforcement and role assignments. Access review logs with reviewer, date, accounts reviewed, and changes made. Offboarding records confirming access revoked upon departure.
Vulnerability management: Scan reports with dates and finding records. Pen test report and remediation tracking document. Patch management log.
Training and awareness: Completion records showing all in-scope staff completed security awareness training, with dates and content description. Phishing simulation results if conducted.
Supplier management: Subprocessor list with last-reviewed date. DPAs or security addenda. Pre-onboarding security review records for critical suppliers.
Incident management: Incident log entries for any security events, even minor ones. Post-incident review records. Evidence the IR plan has been tested (tabletop exercise records).
Management review: Dated meeting minutes covering required ISO 27001 inputs — audit results, risk register status, objectives progress, incidents, and resource decisions.
How to Organize Your Evidence Repository
Create a structured evidence repository — a SharePoint library or similar — organized by ISO 27001 clause and Annex A control.
Every piece of evidence should have a filename that includes the control reference, the evidence type, and the date. When your auditor asks for evidence of access control reviews, you navigate to that folder and produce a clean list of documented reviews.
This is the operational difference between an audit that runs smoothly and one that stalls.
Set recurring calendar reminders for every periodic evidence-generating activity: quarterly access reviews, annual policy reviews, annual pen test commissioning, management review scheduling. Missing a cycle does not just create a gap in evidence — it creates a non-conformity finding.
Pro Tip: Missing a periodic evidence cycle does not just create a gap it creates a non-conformity because the process did not operate as documented. Set recurring calendar reminders for every periodic activity the moment your policies define their frequency. Evidence collection is a habit, not a sprint.
7
Run Your Internal Audit Before the Certification Body Does
What It Is: A formal, documented audit of your ISMS conducted by an independent reviewer before your certification audit required under ISO 27001 Clause 9.2 and essential for finding and fixing non-conformities before an external auditor finds them first.
How to Structure a Startup Internal Audit
→Scope the audit against your controls tracker — verify each control is documented, operating as documented, and evidenced
→Sample, don’t audit everything — review two to three instances of each periodic activity and one recent output from each continuous control
→Document findings formally — every non-conformity or observation is logged with control reference, description, and recommended corrective action
→Resolve non-conformities before Stage 2 — corrective actions must be completed and evidenced before your certification audit
What Makes an Internal Audit Credible
Non-conformities found at Stage 2 that were also identified in your internal audit — and not corrected — indicate that your ISMS corrective action process is not functioning. This is itself a non-conformity under Clause 10.1.
An internal audit with no findings in a first-time implementation is almost certainly superficial. A genuine internal audit finds genuine gaps. Finding and fixing them before Stage 2 is the entire point of the exercise.
The independence requirement matters. An ISMS owner who reviews their own work and finds nothing is not conducting an audit — they are doing a self-check that will not satisfy a certification body.
Pro Tip: If you can only invest in one piece of external support during your DIY ISO 27001 implementation, make it the internal audit. An experienced ISO 27001 Lead Auditor conducting your internal audit will find the same gaps your certification body will find before they count against you. The cost is typically $2,000 to $4,000 and it is the highest-ROI investment in your certification journey.
8
Prepare for and Navigate the Certification Audit
What It Is: The two-stage audit process conducted by an accredited certification body that results in ISO 27001 certification.
How the Audit Works
Stage 1 — Documentation Review: The auditor reviews your ISMS documentation to confirm your documented system is ready for Stage 2 assessment. Typically one to two days, often conducted remotely. Outcome: ready to proceed, or a list of documentation gaps to address.
Stage 2 — Evidence Verification: The auditor tests whether your policies and controls are being followed in practice — interviews, evidence review, access log sampling, incident history check. Typically two to three days for a startup ISMS.
Post-Certification: Certification is valid for three years, subject to annual surveillance audits in years one and two. Surveillance audits are lighter-touch reviews of a subset of controls — not a full re-certification.
How to Prepare Your Team for Stage 2 Interviews
Every team member who may be interviewed should be able to clearly explain:
→ What the ISMS is and why it exists
→ Their specific role and responsibilities under the ISMS
→ How to find and demonstrate the policies that apply to their work
→ What the incident reporting process is and how to use it
→ Where to direct the auditor for specific evidence
Auditors assess not just whether controls exist but whether the people responsible for them can describe how they work. A developer who cannot explain how credentials are managed creates a concern that the control is only documented — not operational.
Pro Tip: Choose your certification body early — before Stage 1. Ensure your certification body is accredited by a recognized national accreditation body (in Canada, the Standards Council of Canada). Certification from an unaccredited body is not recognized by enterprise buyers and will not satisfy their security questionnaire requirements.
The 5 Mistakes That Derail Startup ISO 27001 Implementations
Even well-intentioned startup implementations stumble on a consistent set of avoidable errors. Here is what to watch for.
1
Scoping too broadly to demonstrate maturity
Including systems that add audit surface area without adding certification value creates evidence collection obligations your lean team cannot sustain. The goal is a defensible scope that covers what matters to your buyers — not a scope that tries to impress by covering everything.
2
Treating the risk assessment as a one-time exercise
ISO 27001 requires your risk assessment to be reviewed at planned intervals and when significant changes occur. A risk assessment completed during implementation and never revisited fails Clause 6.1 and demonstrates to auditors that your ISMS is not being actively managed.
3
Copying policies without customizing them
Template policies are a useful starting point. Policies submitted to an auditor that describe processes your organization does not actually follow are a liability. If the policy says access reviews happen monthly and your team does them quarterly, that is a non-conformity. Make every policy accurately describe your actual practice, even if that means adjusting the policy to fit what is operationally sustainable.
4
Skipping the penetration test
Many startup teams assume their cloud-provider security posture and internal practices are sufficient without external validation. Auditors routinely ask for penetration test evidence as proof that controls are operating effectively. A startup that cannot produce a recent pen test summary will receive an observation or non-conformity at Stage 2.
5
Not treating the internal audit seriously
An internal audit conducted as a rubber-stamp exercise — where the ISMS owner reviews their own work and finds no findings — is not credible to an external auditor. A genuine internal audit finds genuine gaps. Finding and fixing them before Stage 2 is the point. An internal audit with no findings in a first-time implementation is almost certainly a superficial one.
Best Practices for Lean Team ISO 27001 Implementation
The organizations that move through enterprise security reviews fastest do the preparation before the questionnaire arrives. Here is what that looks like in practice.
1
Assign one person as the ISMS driver with protected time
The ISMS implementation cannot be someone’s twentieth priority. Even if it is not a full-time role, whoever owns the implementation needs calendar-protected time at minimum, half a day per week during the implementation period. Everything else can be adapted, but the absence of protected time is the most reliable predictor of a delayed or failed certification.
2
Use a vCISO for strategic guidance at key milestones
You do not need a full-time consultant embedded in your team. Experienced guidance at the moments that matter most — scoping, risk assessment methodology, SoA decisions, internal audit conduct, and Stage 1 preparation — is more valuable than hundreds of hours of generic advisory. A good vCISO or ISO 27001 consultant engaged for 15 to 20 hours at the right milestones delivers disproportionate value.
3
Build the ISMS into your operational rhythm, not alongside it
Access reviews should be on a recurring calendar event. Policy reviews should happen at the same time every year. The management review should be a standing quarterly agenda item. An ISMS that requires separate operational infrastructure to maintain will always be deprioritized against product and commercial demands. One that is embedded in existing processes will survive the growth of your team.
4
Document what you actually do, not what you aspire to do
The most maintainable ISMS is one that documents the practices your team already follows, secures the systems your team already uses, and reviews the risks your team actually faces. Starting with aspiration and retrofitting reality is backward and it produces non-conformities when the aspiration and the evidence diverge.
5
Plan your certification timeline around a business milestone
For most startups, ISO 27001 certification becomes urgent because of a specific enterprise deal, a specific RFP, or a specific compliance deadline. Working backward from that milestone with four to six months of lead time produces a realistic schedule. Starting the process in response to an RFP that closes in six weeks produces stress, shortcuts, and a Stage 1 failure.
Certification Is Not the Goal — Closing Deals Is
The reason Canadian SaaS startups pursue ISO 27001 certification is almost never philosophical. It is commercial. Enterprise buyers require it. Procurement teams use it to filter vendor lists. CISOs at potential clients treat a current certificate as evidence that the vendor is serious about security governance.
Understanding that context changes how you approach the implementation. You are not building an ISMS to satisfy an auditor. You are building an ISMS that makes your product genuinely more secure and your organization genuinely more trustworthy and that produces a certificate that enterprise buyers recognize and respect.
The good news is that a small, focused team can achieve exactly that. The implementation is not beyond a startup’s capacity. It requires clear scope decisions, honest risk assessment, documentation that reflects operational reality, and consistent evidence collection. It does not require a compliance department, a GRC platform, or an enterprise budget.
Ready to start your ISO 27001 implementation or looking for an honest assessment of where your current programme stands? Canadian Cyber works with SaaS startups across Canada to scope, build, and certify ISMS programmes that close enterprise deals faster. From gap assessment and risk methodology through to internal audit support, Stage 1 preparation, and certification body coordination we meet lean teams where they are and get them to certified.
Ready to Get Certified?
Book a No-Cost ISO 27001 Gap Assessment
We’ll tell you exactly where you stand against the ISO 27001:2022 requirements nd what it will take to get your certificate in the timeline your business needs.