ISO 27002's control on configuration management ensures that hardware, software, services, and networks are securely configured and maintained. This includes creating standard templates, monitoring configurations, and managing changes. Security hardening reduces vulnerabilities by restricting unnecessary services and privileges. Tools like Microsoft Intune help streamline configuration management, automating assessments and enforcing security policies across systems.

Information security is a top priority for organizations of all sizes, as they strive to protect their sensitive data and systems from unauthorized access, use, disclosure, disruption, modification, or destruction. One key aspect of information security is the proper configuration and maintenance of hardware, software, services, and networks, and this is where the ISO 27002 (new control published in 2022) control on configuration management comes into play. In this article we will be talking about what is the Configuration Management control all about, what is security hardening, and how you can use tools like Microsoft Intune to master them.
According to the ISO 27002 control on configurations, “Configurations, including security configurations, of hardware, software, services and networks should be established, documented, implemented, monitored and reviewed.”
This control is designed to ensure that organizations have a framework in place for properly configuring and maintaining their hardware, software, services, and networks in a secure manner.
One key component of this control is the development of standard templates for the secure configuration of these assets. The control states that these templates should be “defined using publicly available guidance (e.g. pre-defined templates from vendors and from independent security organizations), considering the level of protection needed in order to determine a sufficient level of security, supporting the organization’s information security policy, topic-specific policies, standards and other security requirements, and considering the feasibility and applicability of security configurations in the organization’s context.”
In addition to establishing standard templates, the control also emphasizes the importance of managing and documenting changes to configurations. It states that “established configurations of hardware, software, services and networks should be recorded and a log should be maintained of all configuration changes. These records should be securely stored.” Changes to configurations should follow the organization’s change management process, and configuration records should include up-to-date owner or point of contact information, the date of the last change, the version of the configuration template, and any relevant information about the relationship between the configurations of different assets.
The control also recommends regularly monitoring configurations to ensure they are in compliance with the defined templates. This includes using a comprehensive set of system management tools to compare actual configurations to the defined target templates and addressing any deviations through automatic enforcement or manual analysis and corrective action. You can do this with tools like CIS CAT Assessor, Microsoft Intune etc.
Security hardening is the process of improving the security of a system by identifying and reducing vulnerabilities. It is an important aspect of information security management and is often included as part of an organization’s information security management system (ISMS) as defined by the ISO 27001 standard.
In addition to the activities outlined in the ISO 27002 control on configurations, security hardening may also include system hardening techniques such as “minimizing the number of identities with privileged or administrator level access rights, disabling unnecessary, unused or insecure identities, disabling or restricting unnecessary functions and services, restricting access to powerful utility programs and host parameter settings, synchronizing clocks, changing vendor default authentication information such as default passwords immediately after installation and reviewing other important default security-related parameters, invoking time-out facilities that automatically log off computing devices after a predetermined period of inactivity, and verifying that license requirements have been met.”
Overall, the ISO 27002 control on configurations provides a comprehensive framework for managing and securing the configurations of hardware, software, services, and networks within an organization. By following this control and implementing appropriate security hardening measures, organizations can protect their sensitive information and reduce the risk of cyber threats. By demonstrating their commitment to information security and the privacy of the individuals whose information they hold, organizations can build trust with their customers, regulators, and other stakeholders. The ISO 27002 control on configurations provides a comprehensive framework for managing and securing the configurations of hardware, software, services, and networks within an organization. However, implementing this control can be a complex and time-consuming process. Fortunately, there are tools like Microsoft Intune available that can help organizations efficiently and effectively implement this control.
Canadian Cyber team led by Waqar Mehboob has experience if planning and implementing configuration management at clients using the CIS CAT Pro tools. The key benefit of this tool is that it is automated and, hence, assessment against established can baselines can be done quickly and more frequently. Waqar has successfully led this engagement for Ubuntu, Windows 2019, 2016, 2012 and RHEL.
In addition to the operating system, he has also led engagements for other systems including Oracle Database Management System, Google Chrome, Firefox and IIS server.
Deployment of the tools has several architectural considerations including resource requirements on the TOE (Target of Evaluation), Bandwidth and permissions.
In our experience once the tools have been setup, it takes less than 10 minutes to complete the scanning process. The remediation, however, must be strategized depending on the type of TOE. So, for example, a new system may be hardened using a GPO, Intune or scripts and Live Operational System may be hardened in a gradual approach over time and requires more formal change management processes including testing.
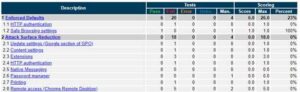
Below is a sample illustration of what configuration areas may be in scope for Google Chrome.
Another tool that can be helpful in implementing the ISO 27002 control on configurations is the Defense Information Systems Agency (DISA) Security Technical Implementation Guide (STIG). STIG is a set of guidelines and recommendations for secure configuration of Department of Defense (DOD) information systems. It provides detailed instructions for configuring systems to meet the requirements of the ISO 27002 control on configurations, as well as other security standards and best practices.
By using tools like CIS CAT and STIG, organizations can streamline their efforts to implement the ISO 27002 control on configurations and ensure that their systems are properly configured and secure. This not only helps organizations meet their information security requirements, but also demonstrates their commitment to protecting their sensitive data and systems, and the privacy of the individuals whose information they hold.
In Waqar’s experience, auditors for SOC2 and SWIFT also asked configuration management to be demonstrated for compliance. They typically expect to see a FIM (File Integrity Monitoring) tool to be implemented to reinforce the process. FIM tools detect and alert any changes to underlying configurations. These alerts can be used to verify if the change was authorized and desired or not.
Another way to achieve security configuration management for endpoints running the Windows 10 operating system is by using the Windows Security Baseline for Windows 10 on Microsoft Intune.
The Windows Security Baseline is a set of security policies and configurations that have been developed and tested by Microsoft to help organizations secure their systems and meet regulatory and compliance requirements. It includes recommendations for configuring various aspects of the operating system, including user accounts, networking, and system services.
By implementing the Windows Security Baseline for Windows 10 on Intune, organizations can ensure that their systems are configured in a secure manner and meet the requirements of the ISO 27002 control on configurations. Intune is a cloud-based management tool that allows organizations to manage and secure their devices, apps, and data from anywhere. By using Intune to deploy and enforce the Windows Security Baseline, organizations can achieve security hardening for their systems in a convenient and efficient manner.
Waqar Mehboob and his team at Canadian Cyber have experience working on Microsoft Intune deployment projects for multiple organizations. We have deployed configuration policies in Intune for Security Baseline which maps to CIS Benchmarks. In Waqar’s experience with Intune and Azure AD, when Intune Security baselines configuration policies are used in conjunction with Conditional access policies, it gives a significant attack surface reduction to organizations especially in a BYOD environment or in environments where the users have privileged accesses on their machines. Using these 2 technologies together can help mitigate the issue of ‘configuration drift’ on the endpoints.
We would love to hear from you about this article that we have written. Please leave us your comments below.
Looking for help or would just like to chat about what the Configuration Management control all about, what is security hardening, and how you can use tools like Microsoft Intune to master them? Please feel free to book an appointment with Waqar.