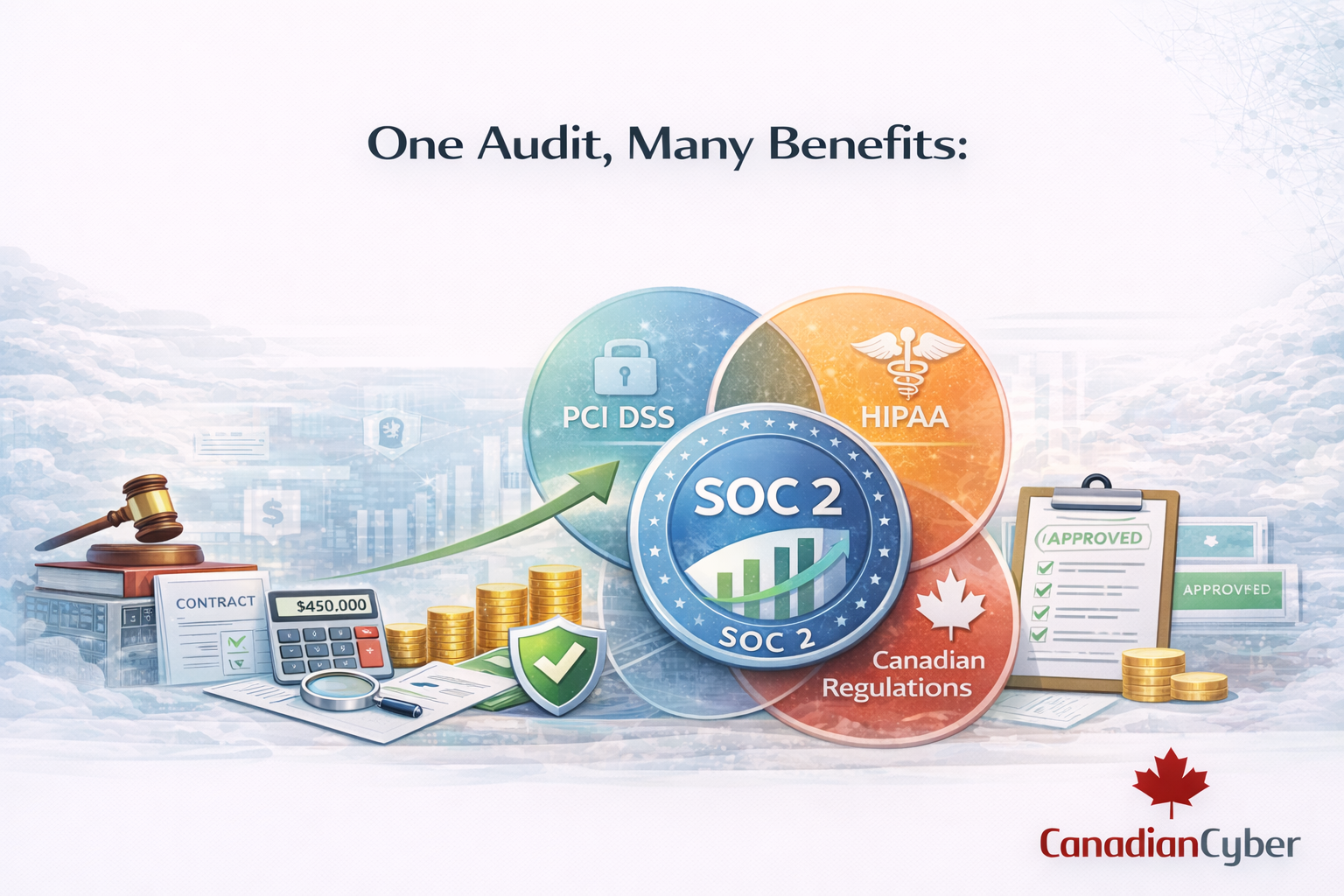
One Audit, Many Benefits: Using SOC 2 Compliance to Satisfy PCI, HIPAA, and Other Requirements
You don’t need separate compliance programs for every regulation. Here is how SOC 2’s controls map to PCI DSS, HIPAA, and Canadian privacy laws turning one audit into multiple wins.
The Compliance Sprawl Problem
You need SOC 2 for enterprise customers.
You need PCI DSS because you handle payment data.
You need HIPAA because of that healthcare client.
And Canadian privacy regulations? Those are coming too.
Before you know it, you’re managing multiple compliance programs each with its own evidence, deadlines, and spreadsheet from hell.
This is compliance sprawl. And it kills productivity.
The Cost of Sprawl
| Problem | Impact |
|---|---|
| Duplicate controls | Same evidence collected multiple ways |
| Multiple audits | Different auditors, different timelines, different requests |
| Conflicting requirements | One standard says X, another says Y |
| Team burnout | Compliance becomes full-time work for people who already have full-time jobs |
The good news: these frameworks overlap far more than they differ. Build around SOC 2 and you get one audit with multiple benefits.
The Overlap: How SOC 2 Maps to Other Frameworks
SOC 2 is built around five Trust Services Criteria: Security, Availability, Processing Integrity, Confidentiality, and Privacy.
These map remarkably well to other frameworks.
| Framework | Overlap with SOC 2 |
|---|---|
| PCI DSS | 60–70% (access control, monitoring, vulnerability management) |
| HIPAA | 50–60% (security rule, access controls, incident response) |
| ISO 27001 | 80%+ (risk-based control frameworks) |
| PIPEDA / Canadian privacy laws | 40–50% (privacy criteria, data governance) |
Practical takeaway: If you build your compliance program around SOC 2, you are already a long way toward other requirements.
SOC 2 + PCI DSS: For Organizations That Handle Payments
If your organization processes, stores, or transmits payment card data, PCI DSS is non-negotiable.
The mistake is building a separate program from scratch.
How SOC 2 Covers PCI DSS Requirements
| Control Area | SOC 2 Coverage | PCI DSS Mapping |
|---|---|---|
| Access control | Logical and physical access controls | Req. 7 (access restrictions) |
| Network security | System operations, secure configurations | Req. 1 (firewall / network controls) |
| Vulnerability management | Risk mitigation, monitoring | Req. 11 (regular testing) |
| Encryption | Confidentiality criteria | Req. 3 + 4 (protect data / encrypt in transit) |
| Incident response | System operations | Req. 12 (incident response planning) |
The gap: PCI adds requirements SOC 2 may not test explicitly (e.g., PCI-specific reporting, ASV scans, and cardholder data retention/disposal).
The strategy: Use SOC 2 as the foundation, then layer PCI-specific controls.
SOC 2 + HIPAA: For Healthcare and Healthtech
HIPAA applies to organizations handling protected health information (PHI).
The HIPAA Security Rule aligns closely with SOC 2’s Security and Confidentiality criteria.
How SOC 2 Covers HIPAA Requirements
| HIPAA Requirement | SOC 2 Coverage |
|---|---|
| Administrative safeguards | Security criteria, risk assessments |
| Physical safeguards | Logical and physical access controls |
| Technical safeguards | Access control, encryption, audit logging |
| Policies and procedures | Documentation requirements across TSC |
| Breach notification | Incident response procedures |
HIPAA adds: BAAs (business associate agreements), HIPAA privacy rule items, and specific risk analysis expectations.
The strategy: Use SOC 2 as your core evidence engine, and add HIPAA-specific overlays where needed.
SOC 2 + Canadian Privacy Laws (PIPEDA and Beyond)
Canadian privacy obligations are governed by PIPEDA federally, with provincial requirements (like Québec’s Law 25) adding additional expectations.
SOC 2’s Privacy criteria can support real evidence of privacy governance.
How SOC 2 Privacy Criteria Align with Canadian Law
| PIPEDA Principle | SOC 2 Privacy Support |
|---|---|
| Accountability | Privacy policies, designated roles |
| Consent | Notice and choice mechanisms |
| Limiting collection | Data minimization practices |
| Safeguards | Security controls protecting personal information |
| Access and correction | DSR / request procedures |
| Challenging compliance | Complaint handling processes |
Opportunity: Document SOC 2 controls once, then reuse evidence across privacy requests, vendor questionnaires, and regulator inquiries.
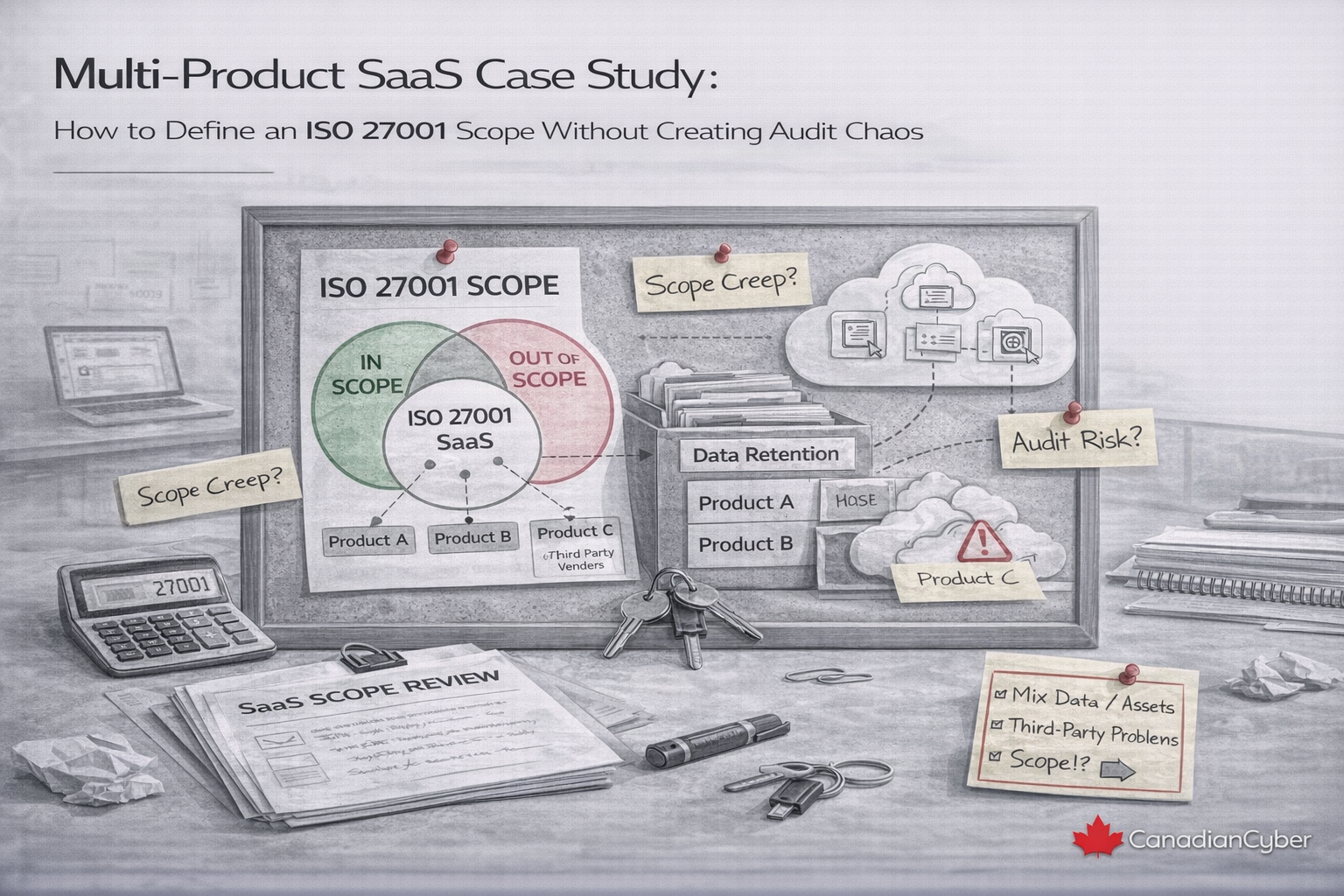
The SOC 2+ Advantage
SOC 2+ is a customized SOC 2 report that integrates additional frameworks beyond the standard Trust Services Criteria.
It reduces duplication by making one audit cover multiple requirements.
| Step | Description |
|---|---|
| 1) Scope definition | Identify which frameworks you need (PCI, HIPAA, ISO 27001, Canadian privacy) |
| 2) Control mapping | Map SOC 2 controls to additional requirements |
| 3) Gap analysis | Identify what’s missing for the added frameworks |
| 4) Implementation | Implement only the extra controls needed |
| 5) Single audit | One auditor tests controls against all included frameworks |
| 6) One report | One integrated report for customers, partners, and regulators |
Result: Instead of separate audits for SOC 2, PCI, and HIPAA, you get one integrated process with one audit rhythm.
The Shared Control Library (Where the Efficiency Comes From)
Integrated compliance works when you maintain one control set, mapped to multiple frameworks.
Evidence is collected once and reused.
Example: Access Control
| Your Control | SOC 2 Mapping | PCI DSS Mapping | HIPAA Mapping |
|---|---|---|---|
| Quarterly access reviews | CC6.2 | Req. 7.1 | §164.308(a)(4) |
| MFA for privileged access | CC6.1 | Req. 8.3 | §164.312(d) |
| Termination within 24 hours | CC6.2 | Req. 8.1.3 | §164.308(a)(3) |
Example: Vulnerability Management
| Your Control | SOC 2 Mapping | PCI DSS Mapping | HIPAA Mapping |
|---|---|---|---|
| Weekly vulnerability scans | CC7.1 | Req. 11.2 | §164.308(a)(8) |
| Critical patches within 7 days | CC7.2 | Req. 6.2 | §164.308(a)(5) |
| Annual penetration testing | CC7.1 | Req. 11.3 | Risk analysis requirement |
Insight: When you document a control for SOC 2, you are also creating evidence you can reuse across other frameworks.
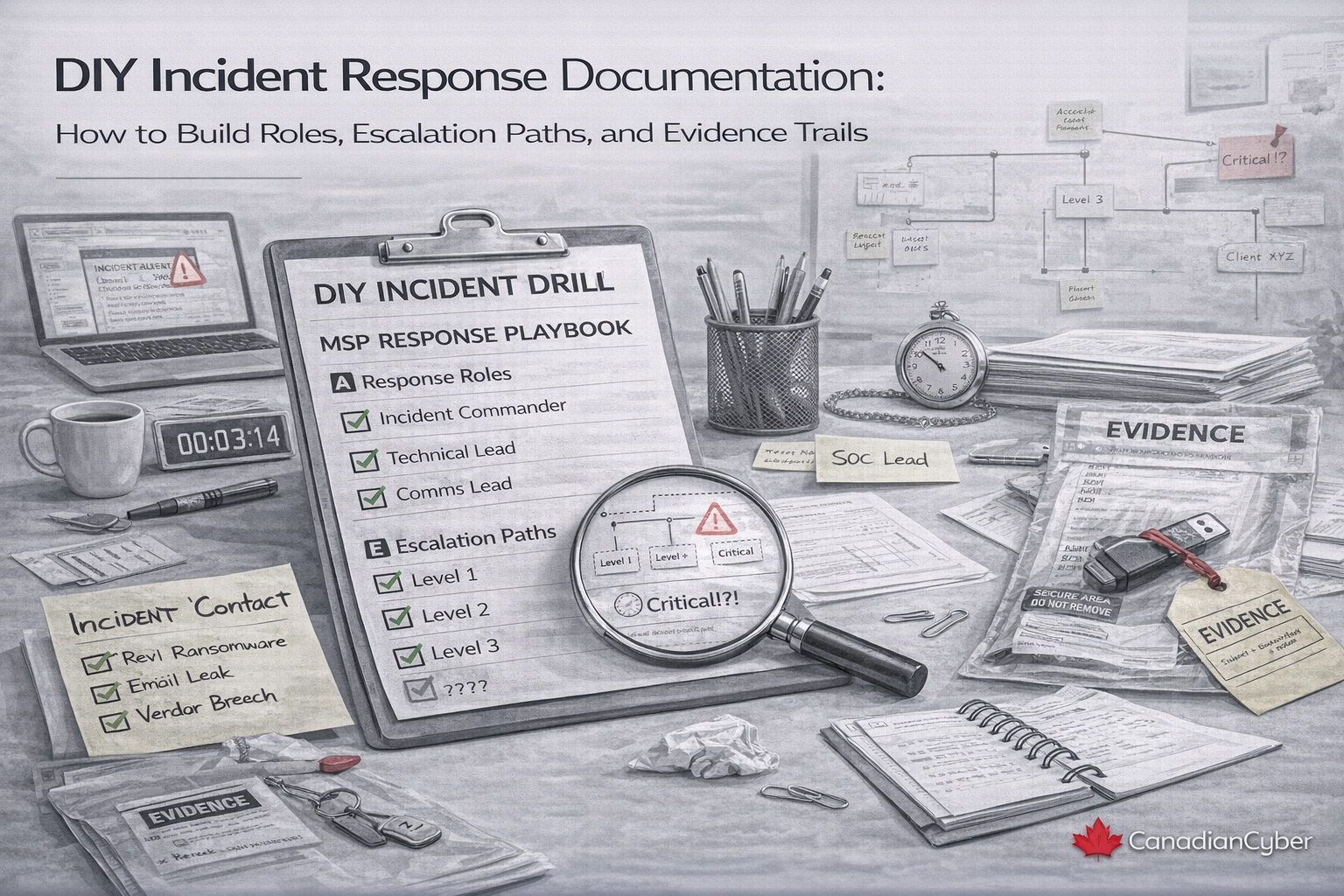
Implementation Roadmap: From Siloed to Integrated
Phase 1 (Months 1–3): Foundation
• Identify all applicable frameworks
• Build a shared control library and map requirements
• Run one integrated gap analysis
Phase 2 (Months 4–9): Implementation
• Implement controls that satisfy multiple frameworks first
• Address framework-specific gaps
• Collect evidence once (by control, not by framework)
Phase 3 (Months 10–12): Audit
• Engage an auditor experienced in SOC 2+ style testing
• Present evidence organized by control
• Receive an integrated report
Phase 4 (Ongoing): Maintenance
• Maintain mappings and the shared control library
• Run quarterly reviews across frameworks
• Update mapping when standards change
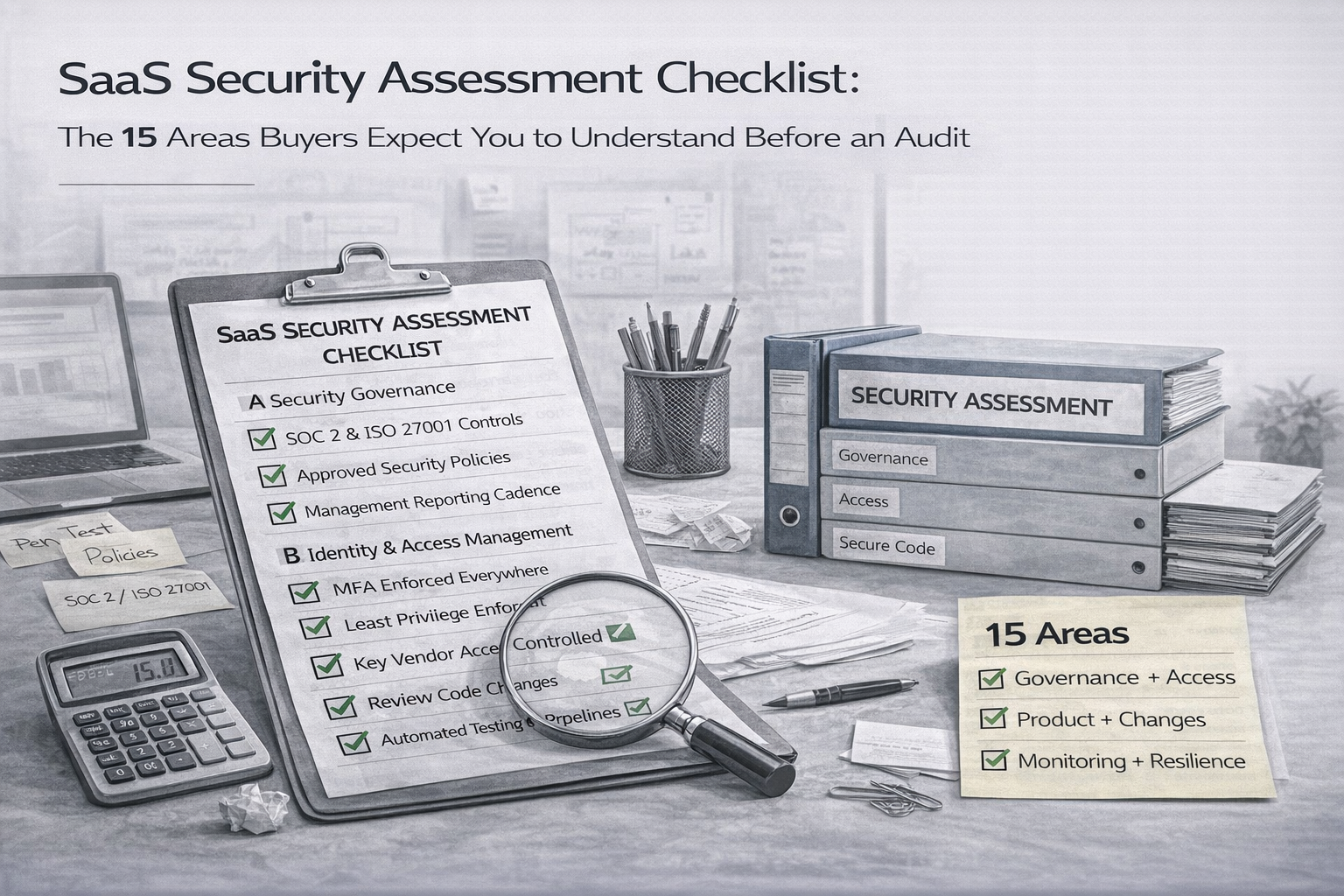
The Canadian Cyber Advantage
Canadian Cyber’s SharePoint ISMS platform is designed for integrated compliance from day one.
| Feature | How It Enables Integrated Compliance |
|---|---|
| Multi-framework mapping | Map each control to SOC 2, PCI DSS, HIPAA, and Canadian requirements |
| Shared evidence repository | One piece of evidence can support multiple frameworks |
| Automated workflows | Quarterly reviews and reminders trigger across frameworks together |
| Vendor management | Track vendor assessments against multiple standards |
| Audit-ready reporting | Generate views filtered by any framework or customer request |
Client-style insight: “We were managing SOC 2 and PCI separately double the spreadsheets and double the audit prep.
Mapping everything once changed everything.”
The 15-Minute Integrated Compliance Assessment
You don’t need to guess whether your SOC 2 work can satisfy PCI, HIPAA, or Canadian privacy expectations.
We’ll tell you what you already cover, where the gaps are, and how to run one program instead of three.
Conclusion: Compliance Without Duplication
SOC 2 is not just another checkbox. It’s a foundation.
| Framework | SOC 2 Coverage |
|---|---|
| PCI DSS | 60–70% |
| HIPAA | 50–60% |
| ISO 27001 | 80%+ |
| Canadian privacy laws | 40–50% |
With a shared control library, automated evidence collection, and an integrated audit approach, you get:
• Less time chasing evidence
• Fewer audit disruptions
• Lower overall compliance costs
• Higher team morale
• Better security outcomes
Because compliance shouldn’t be a collection of silos.
It should be one program that works for everything.
Ready to Turn One Audit into Multiple Wins?
Let’s map your controls once, centralize your evidence, and build an audit rhythm that scales.
Stay Connected With Canadian Cyber
Follow Canadian Cyber for SOC 2 strategy, integrated compliance, and audit readiness insights: