Saved by the Standard
How Following ISO 27018 Prevented a Cloud Data Breach
It was 6:42 PM on a Thursday.
Most of the team at NorthBridge SaaS, a Toronto-based HR platform, had already logged off.
But one developer hadn’t.
He was deploying a new feature to improve customer analytics dashboards. The change was small. Routine. Harmless.
Except it wasn’t.
Within minutes, an internal monitoring alert triggered.
An object storage bucket had been configured with broader access permissions than intended.
Inside that bucket?
Customer PII names, emails, employee records, payroll data.
In most companies, this is where the breach story begins.
For NorthBridge, it was where the breach story ended.
Company Snapshot
What Could Have Happened
If NorthBridge had been operating without structured privacy controls, the outcome could have been severe:
- Public exposure of cloud storage
- Unauthorized download of payroll records
- Mandatory breach notification under Québec’s Law 25
- Potential federal investigation as privacy expectations tighten
- Reputational damage + enterprise contract termination
- Cyber insurance claims and renewal premium spikes
- Litigation risk and long-term trust loss
Estimated impact: seven figures.
Actual impact: zero breach, zero exposure, zero notification.
The Controls That Made the Difference
ISO 27018 focuses on protecting Personally Identifiable Information (PII) in public cloud environments.
NorthBridge had implemented controls that were designed to do one thing: limit exposure even when mistakes happen.
1️⃣ Strict Role-Based Access Control (RBAC)
ISO 27018 requires limiting access to PII strictly to authorized personnel. NorthBridge implemented:
- Segmented production access
- Least privilege enforcement
- Privileged account monitoring
- Conditional access policies
Result: When the bucket misconfiguration occurred, only two internal admin accounts could technically view the data.
No broad internal exposure. No external exposure.
2️⃣ Data Masking & Encryption
ISO 27018 emphasizes encryption and minimizing exposure of PII. NorthBridge used:
- Encryption at rest and in transit
- Tokenization for certain payroll fields
- Masked non-essential PII in analytics exports
Result: Even if data had been accessed improperly, critical identifiers were protected and exposure impact would have been limited.
3️⃣ Automated Cloud Monitoring Alerts
ISO 27018 aligns with continuous monitoring of cloud environments. NorthBridge configured:
- Automated misconfiguration alerts
- Storage exposure detection rules
- Security center integration
- Daily review dashboards
Result: The alert triggered within minutes. The configuration was rolled back in 12 minutes.
No prolonged exposure window.
4️⃣ Data Minimization Strategy
ISO 27018 expects collection and retention of only necessary data. NorthBridge reduced:
- Legacy PII retention
- Historical payroll exports
- Redundant storage copies
Result: The affected bucket contained only current data no deep historical archive. The risk surface was smaller by design.
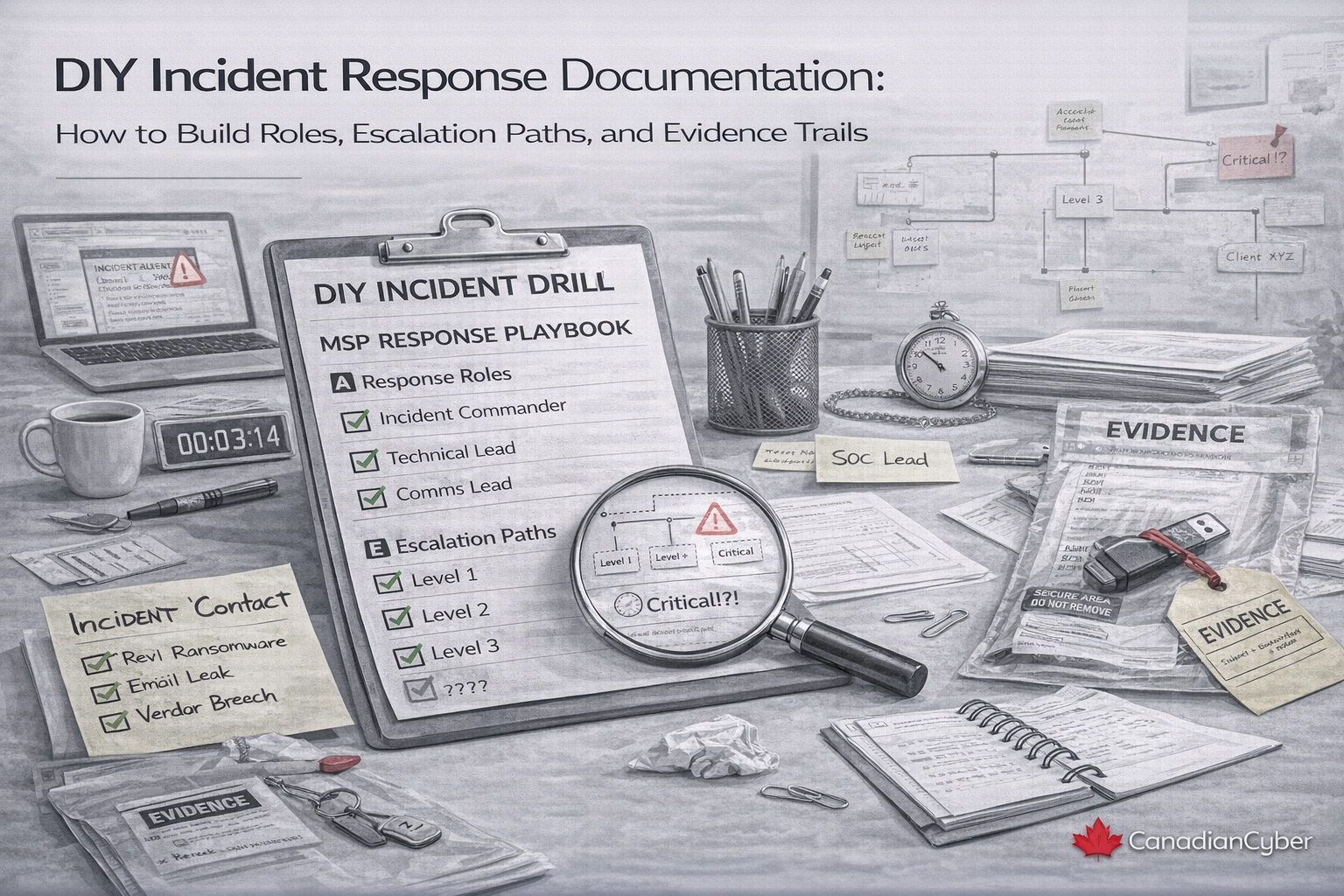
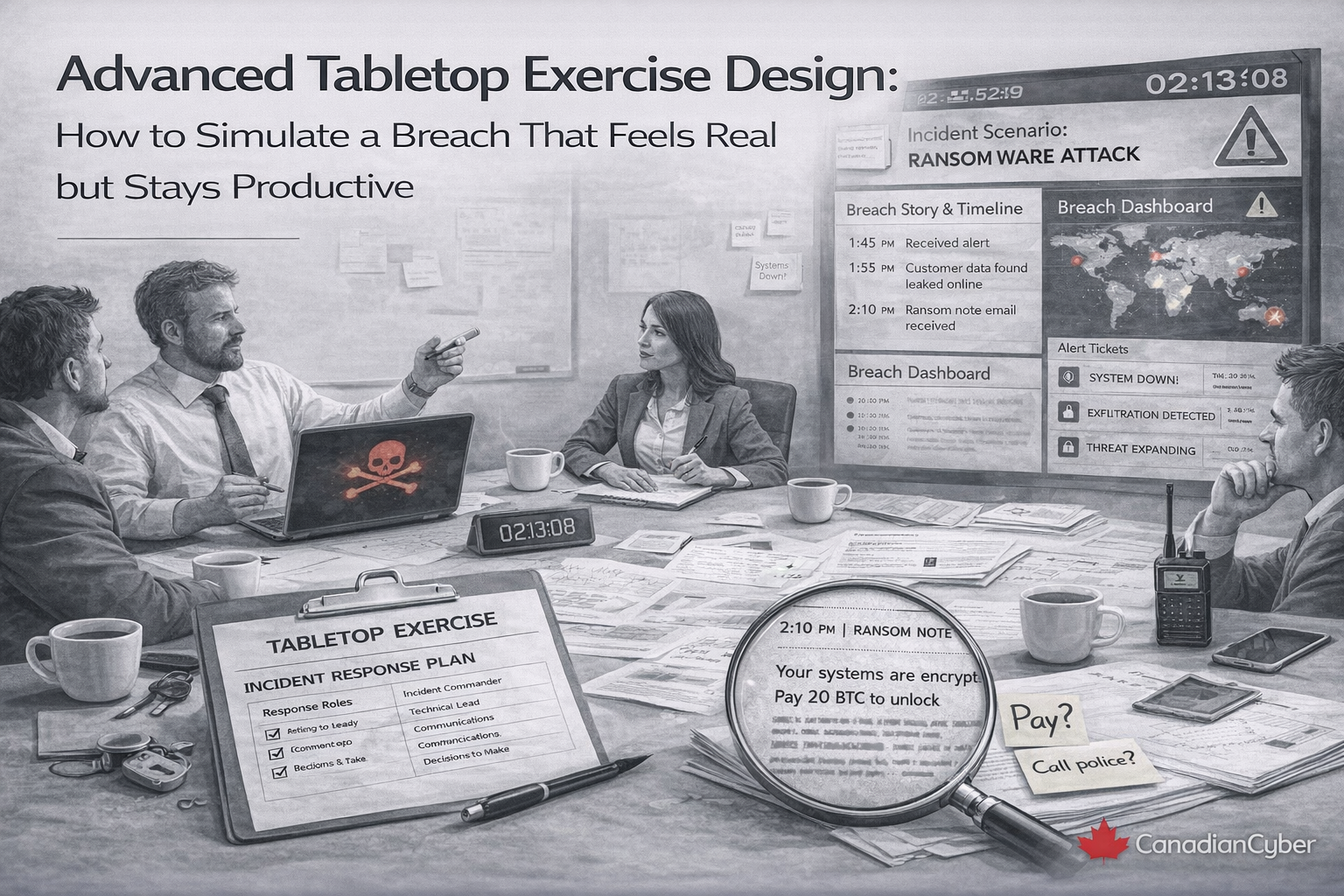
5️⃣ Incident Response Playbook
ISO 27018 supports defined incident response for PII. NorthBridge already had:
- Documented incident response plan
- Escalation roles and responsibilities
- Privacy/legal involvement path
- Pre-drafted communications templates
Result: Even though notification wasn’t required, the team executed impact assessment, log analysis, forensic review, and a leadership briefing.
The response was structured not reactive.
The Post-Incident Review
The next morning, leadership met. The CTO opened with a simple statement:
“We didn’t get lucky. Our controls worked.”
The root cause was human error a configuration mistake.
The prevention was governance.
The team approved two improvements as part of continuous improvement:
- Add automated permission validation checks before deployment
- Introduce additional code review for infrastructure changes
That’s what maturity looks like: not “nothing ever goes wrong,” but “when something goes wrong, controls contain it.”
What If ISO 27018 Had Not Been Implemented?
Let’s compare the near-miss in two realities:
| Without ISO 27018 | With ISO 27018 |
|---|---|
| Broad cloud access | Role-based access control |
| No monitoring | Real-time misconfiguration alerts |
| Raw PII exposure risk | Encrypted + masked fields |
| Delayed detection | 12-minute resolution |
| Breach notification + client panic | No breach + stronger client confidence |
The difference wasn’t luck. It wasn’t a firewall. It was structured privacy governance.
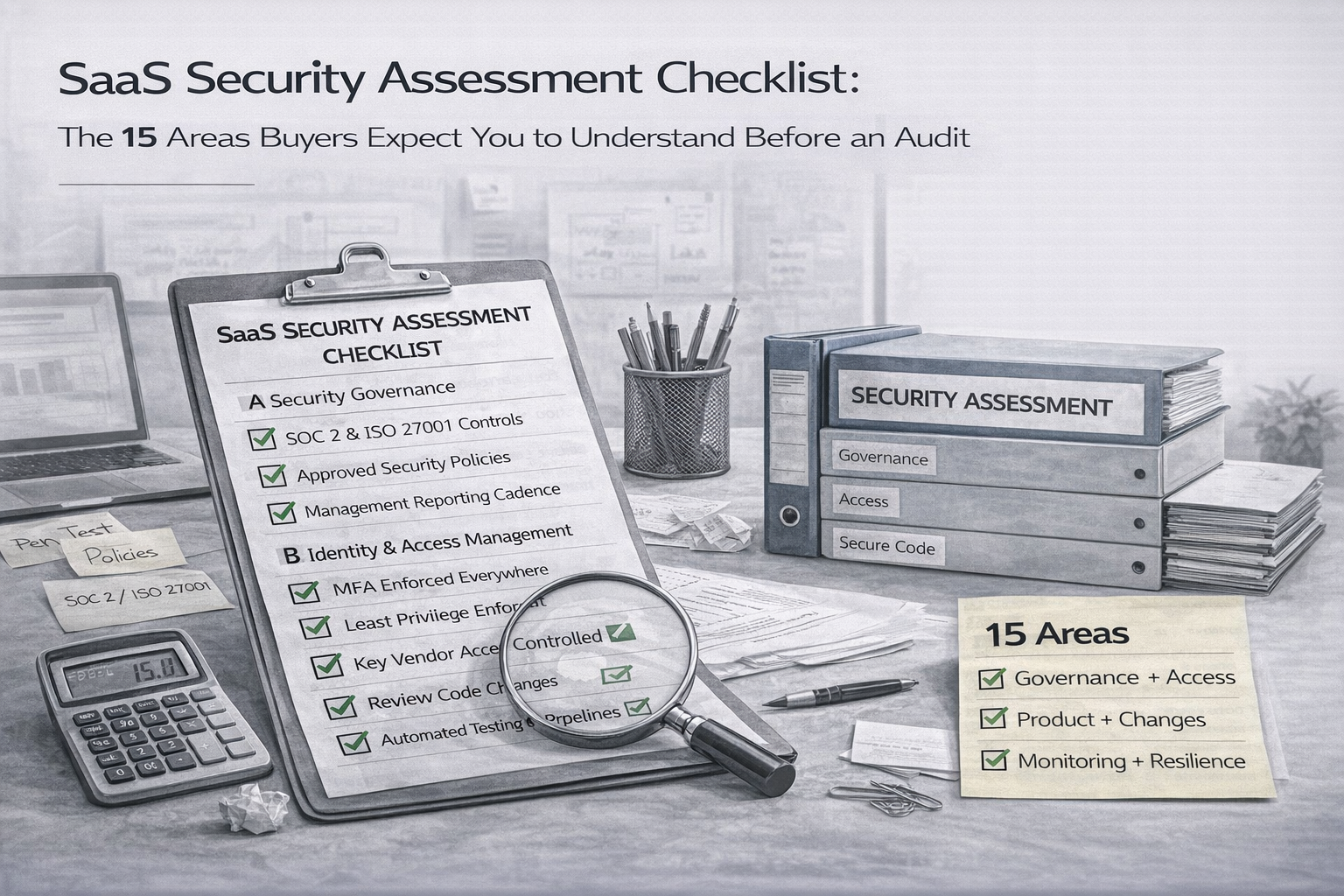
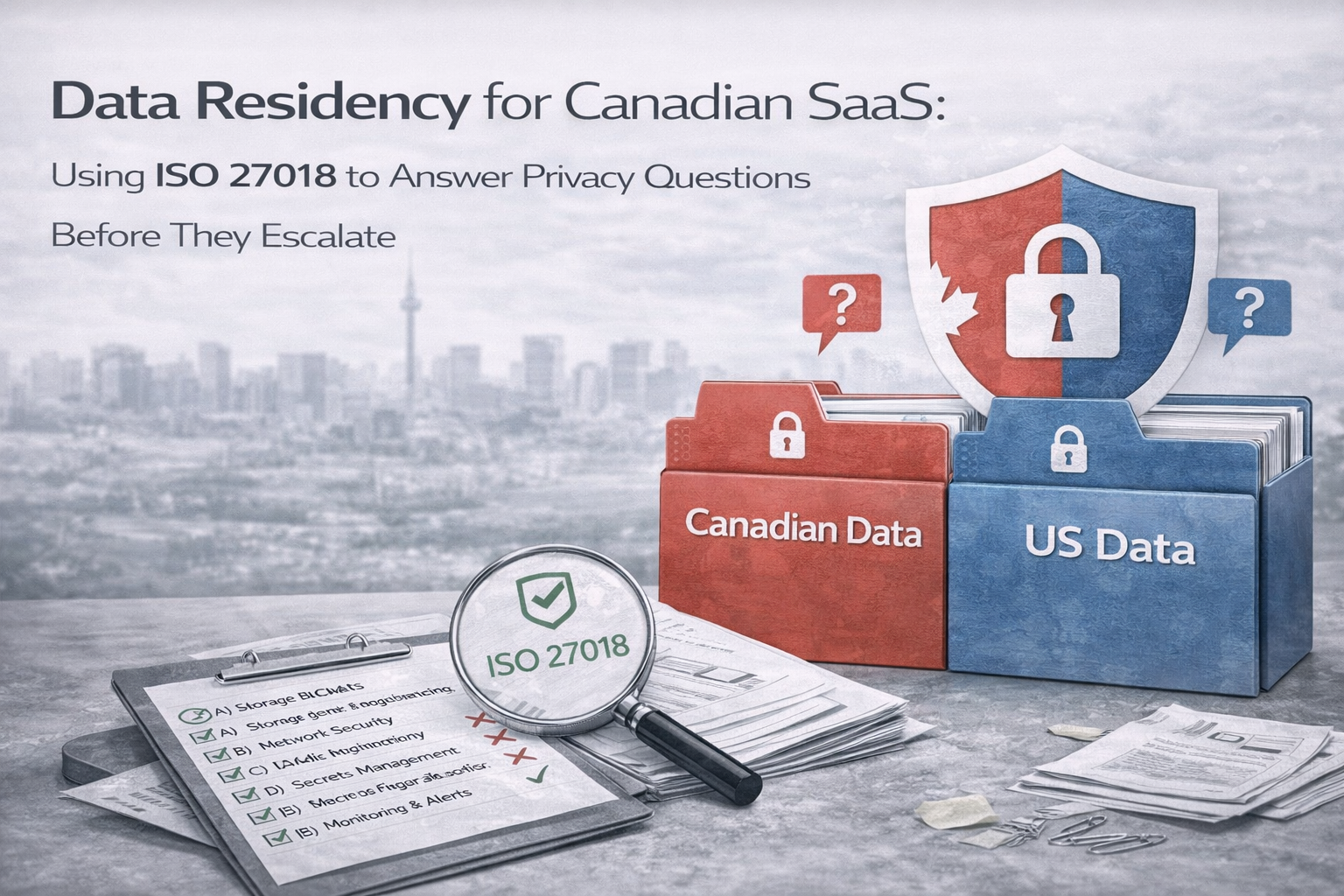
Why ISO 27018 Matters for Canadian SaaS Companies
Canada’s privacy and cybersecurity expectations are tightening:
- Québec Law 25 enforcement pressure
- Federal privacy modernization momentum
- Enterprise procurement scrutiny and vendor risk demands
- Public sector and regulated-industry requirements (finance, healthcare)
Enterprise customers increasingly ask:
- How is PII protected in your cloud environment?
- How do you restrict and monitor processor access?
- How do you detect and respond to misconfigurations?
- How do you minimize retention and limit exposure surface?
- Can you prove privacy governance maturity?
ISO 27018 answers these questions with a clear, defensible structure.
Protect PII Before It Becomes a Problem
If you process customer PII in AWS, Azure, or GCP ISO 27018 controls can prevent the exact incident you hope never happens.
No pressure. Just clarity on gaps, monitoring blind spots, and quick wins.
The Business Outcome
Three months later, NorthBridge was negotiating with a major Canadian financial institution.
During due diligence, the bank’s security team asked:
“Describe a real incident and how your controls performed.”
NorthBridge shared the near-miss story and the improvements they implemented immediately afterward.
The bank’s response: “That’s exactly what we want to see controls working before a breach.”
They won the contract. Compliance became credibility.
The Strategic Lesson
Security incidents are not always preventable.
But breaches often are.
The difference is rarely “more tools.” It’s:
- Control maturity
- Governance discipline
- Cloud configuration oversight
- Privacy-by-design architecture
- Monitoring and response cadence
ISO 27018 operationalizes privacy. It turns principles into mechanisms and mechanisms stop breaches.
Are You Protected Or Hoping?
Quick self-check:
- Do you monitor cloud storage exposure in real time?
- Are PII fields encrypted and masked appropriately?
- Is least privilege truly enforced for production data?
- Are retention schedules automated and defensible?
- Do you test incident response — not just document it?
- Can you prove privacy governance maturity to enterprise clients?
If the answer is uncertain, your exposure is higher than you think.
How Canadian Cyber Helps SaaS Companies Implement ISO 27018
Canadian Cyber supports organizations with practical, audit-ready ISO 27018 implementation designed for SaaS reality:
- ISO 27018 gap assessments
- Cloud privacy risk analysis
- Data protection architecture review
- PII governance workflows and accountability models
- Access control frameworks (least privilege + monitoring)
- Incident response development and testing
- Audit readiness preparation (ISO 27001 + SOC 2 alignment)
We don’t just help you pass. We help your controls work under pressure.
Free Cloud Privacy Risk Review
Before a near miss becomes a headline, validate your cloud privacy controls and monitoring visibility.
Final Thought
NorthBridge did not avoid a breach because nothing went wrong.
They avoided a breach because something did go wrong and their controls worked.
Standards are not bureaucracy. They are safeguards.
ISO 27018 is not paperwork. It is protection.
In the cloud era, protection is non-negotiable.