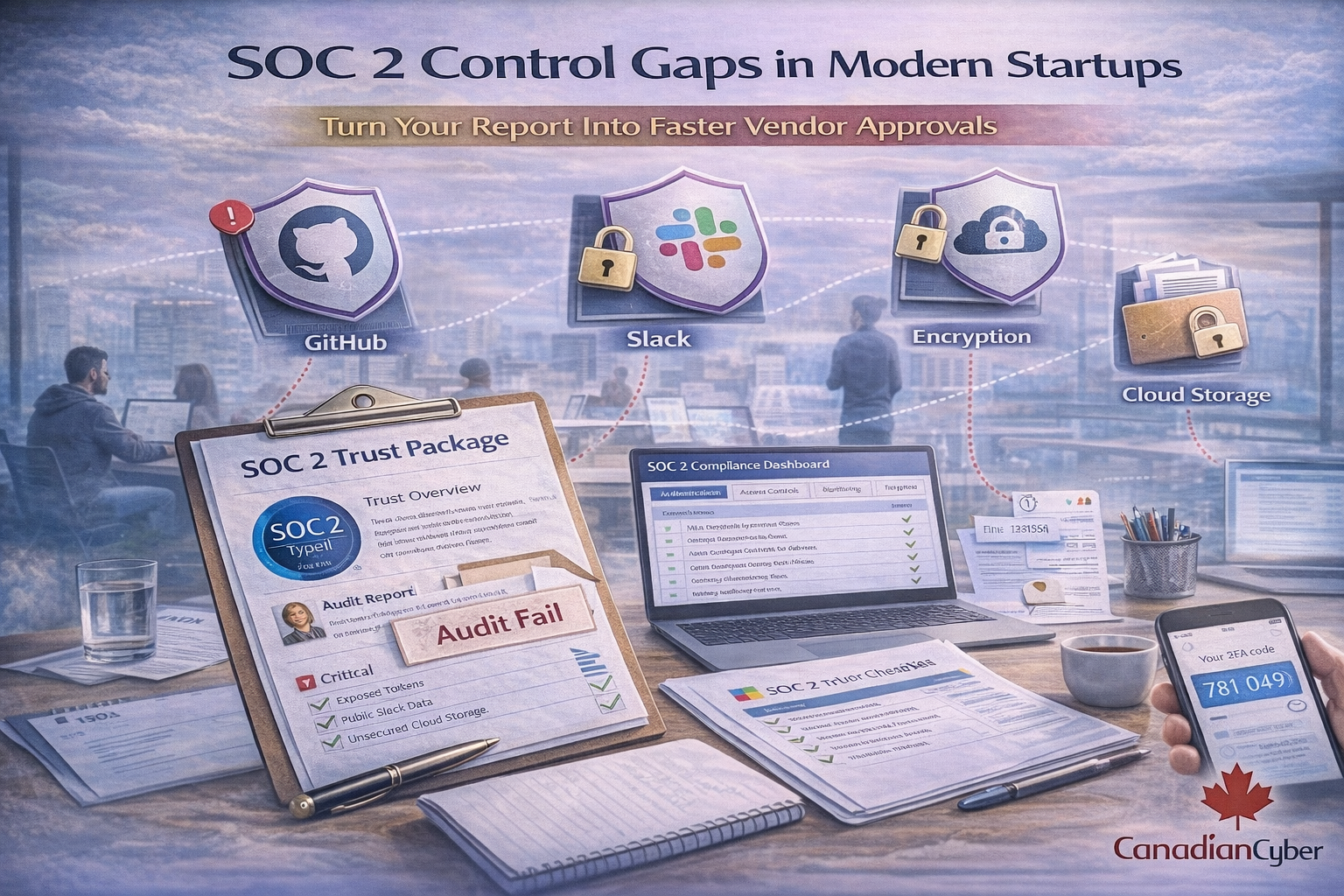
Most SOC 2 audit failures in startups come from tool defaults. This guide explains the most common SOC 2 control gaps in GitHub, Slack, and cloud environments and the evidence auditors expect.
Most SOC 2 failures in startups don’t happen because teams don’t care about security.
They happen because modern tools ship with permissive defaults and nobody tightens them until an auditor asks.
This is a realistic, audit-focused breakdown of the control gaps we see most in GitHub, Slack, and cloud environments (AWS/Azure/GCP), plus exactly what evidence auditors expect.
A startup hits a growth milestone. Enterprise deals start appearing. Then procurement asks:
The team is capable and moving fast. But the environment often looks like this:
That is enough to break a SOC 2 audit. Not because you are unsafe, but because you cannot prove consistent control.
SOC 2 auditors test whether controls are designed (documented and appropriate) and operating (working consistently over time).
Startups often do the right thing informally. The audit problem is that it isn’t recorded.