Why subprocessors are now a top audit and deal blocker
In 2026, buyers don’t only ask “Do you use AWS/Azure?” They ask who else touches their data,
where it’s processed, and how you control changes.
If you can’t answer quickly, reviews drag. If you can’t evidence it, audits get painful.
Subprocessor governance is one of the fastest ways to move from “we’re secure” to “we’re approve-able.”
What ISO 27017 is really asking you to do (plain English)
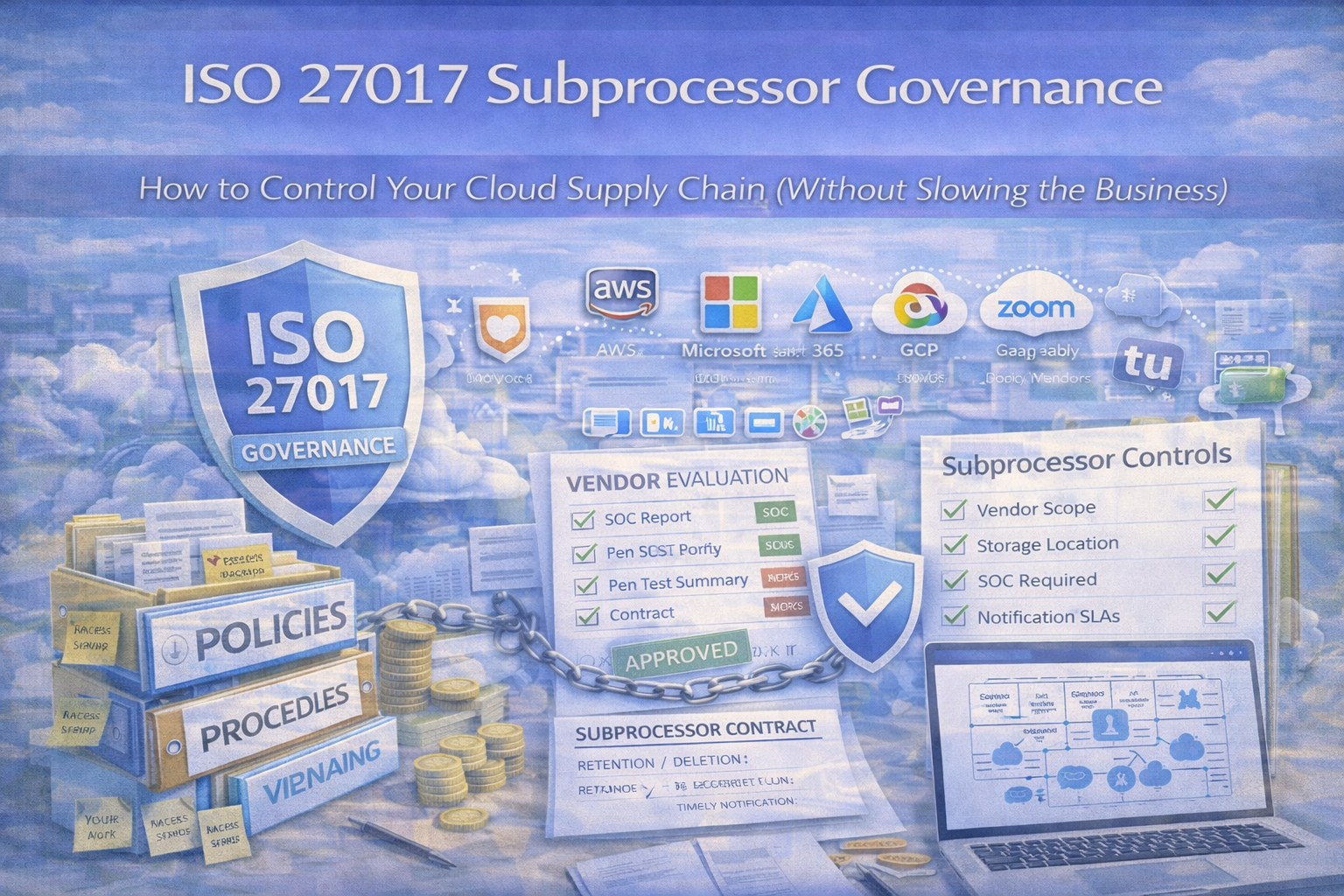
For subprocessors, auditors typically expect proof that you:
- know who your subprocessors are (and which ones matter)
- assess them before use (risk-based)
- contractually bind them (security + privacy obligations)
- monitor them over time (not one-time)
- control change (notification + objection + re-review)
- maintain evidence (so renewals and audits aren’t scrambles)
Step 1: Define your cloud supply chain (so you don’t over-govern everything)
Not every vendor needs the same level of scrutiny. Start by separating: primary providers, subprocessors, and non-processors.
Simple subprocessor test
If a vendor stores, processes, transmits, or can access customer data to deliver your service, treat it as a subprocessor.
Common subprocessors
Cloud hosting, email/SMS, support platforms, monitoring/logging, payments (if applicable), CDN/storage, analytics (depending on data).
Goal
Make the list accurate and defensible without turning it into a 200-vendor monster.
Step 2: Build a Subprocessor Register (your single source of truth)
Auditors love registers. Buyers do too. This is the fastest way to answer “who touches our data?” with proof.
| Field group |
Fields |
Notes |
| Identity |
Subprocessor name, service purpose, owner (business + security) |
Ownership prevents “nobody owns it” |
| Data & location |
Data types (PII/confidential/logs), hosting/processing regions (if known) |
Buyers care about cross-border processing |
| Tiering |
Criticality tier (Critical/High/Medium/Low) |
Tie to business impact and data sensitivity |
| Contract & assurance |
DPA/security addendum (Y/N), assurance (SOC2/ISO/questionnaire), incident notification requirement |
Contracts + assurance are audit proof |
| Review & evidence |
Last review date, next review due, evidence links (SOC report, review notes, contract), change log |
Evidence links are the “wow” factor |
Pro tip: Tier vendors by business impact. “Critical” = outage or breach would materially affect customers.
Step 3: Set subprocessor security requirements (baseline + enhanced)
ISO 27017-aligned governance works best with two levels. Demand more where risk is higher.
Baseline requirements (all subprocessors with customer data)
- access controls + least privilege
- encryption in transit (and at rest where applicable)
- incident notification requirement
- data retention and deletion terms
- confidentiality obligations for personnel
- flow-down obligations if they use their own subprocessors
Enhanced requirements (critical/high risk)
- independent assurance (SOC 2 Type II / ISO 27001 or equivalent)
- vulnerability management expectations (SLA where feasible)
- stronger incident timelines + cooperation duties
- change notification and approval expectations for major changes
- audit log availability where applicable
Key principle
Don’t demand “everything for everyone.” Demand more where the risk is higher.
Step 4: Control subprocessor onboarding (no more “someone bought a tool”)
This is where most organizations leak risk. A simple onboarding workflow makes governance repeatable and auditable.
vCISO onboarding workflow (audit-friendly)
- Request — business case + what data will be shared
- Classification — data type + criticality tier
- Due diligence — assurance review + questionnaire (risk-based)
- Contracting — security terms + DPA + incident notification
- Approval — business owner + security sign-off
- Register update — add subprocessor + evidence links
- Customer notice — update list / notify where required
Step 5: Change control for subprocessors (the part buyers care about most)
Subprocessor governance fails when changes are invisible. Use a clear “change event” model.
Trigger a review when
- a new subprocessor is added
- hosting/processing region changes
- terms/subprocessors change materially
- a breach or major outage occurs
- new data types start flowing
What to implement (practical)
- subprocessor change log (what changed, impact, decision)
- customer notification window for material changes (commonly 30 days)
- objection handling process (review, alternatives, decision record)
- re-review for critical vendors after material changes
Step 6: Monitoring and re-review cadence (not just at onboarding)
A simple cadence keeps subprocessors from going stale and gives you operating evidence.
| Tier |
Review cadence |
What “monitoring” can be |
| Critical |
Annual deep review + quarterly monitoring check |
Incidents/outages, assurance current, changes announced, open conditions |
| High |
Annual review |
Assurance refresh + contract terms check |
| Medium |
Every 18–24 months or triggered review |
Light questionnaire + change confirmation |
| Low |
Onboarding only + triggered review |
Review only if risk changes |
Evidence tip
Store a one-page “quarterly monitoring note” even if nothing changed. Auditors love that.
Step 7: Evidence pack (what auditors and customers will request)
If you can produce this quickly, you’re ahead of most vendors.
Minimum subprocessor evidence pack
- Subprocessor register (current)
- Customer-facing subprocessor list (if applicable)
- Due diligence records for sampled subprocessors (SOC2/ISO/questionnaire + review notes + decision)
- Contract term evidence (incident notification, confidentiality, retention/deletion)
- Change log records (if any)
Strong evidence pack (high trust)
- Risk tiering methodology
- Quarterly monitoring notes (critical)
- Risk acceptances for exceptions (with expiry)
- Offboarding/exit plans for critical subprocessors
Common subprocessor governance failures (and how to fix them)
- “We don’t have a subprocessor list” → create a register and publish a customer-facing list (or NDA version).
- “We review once, then forget” → add cadence + due dates + reminders.
- Contracts don’t include security terms → standardize a security addendum + DPA clauses.
- Changes happen silently → maintain a change log + customer notification process.
- Exceptions live in email → use a risk acceptance workflow with expiry and compensating controls.
Want buyers to stop stalling on “subprocessors”?
We’ll set up the register, review calendar, change notifications, and an auditor-ready evidence pack in SharePoint so procurement can approve faster.
The fast-start subprocessor governance checklist (copy/paste)
- Identify subprocessors (who touches customer data)
- Create a subprocessor register (tier, data types, owners, evidence links)
- Define baseline + enhanced security requirements
- Implement onboarding approval workflow
- Set change notification and objection process
- Set annual review cadence (quarterly monitoring for critical)
- Store review notes + decisions (not just PDFs)
- Track exceptions with expiry dates
- Build a customer-facing subprocessor list (or NDA version)
Follow Canadian Cyber
Practical cybersecurity + compliance guidance: