Fintech • vCISO • Bank Security Reviews • Vendor Due Diligence • Client Trust
Case Study: vCISO Support for a Fintech Preparing for Bank Security Reviews
Bank security reviews can slow fintech growth when answers are scattered, evidence is incomplete, and no one owns the security story.
Quick Snapshot
| Case Study Area | What the Fintech Focused On |
|---|---|
| Business Context | A growing fintech prepared for bank partner security reviews. |
| Main Pressure | Bank due diligence, customer trust, vendor risk, incident readiness, and compliance evidence. |
| vCISO Focus | Risk register, access control, cloud security, vendor governance, questionnaires, and board reporting. |
| Key Outcome | The fintech moved from reactive answers to a structured bank security review pack. |
| Main Lesson | Banks do not only want security claims. They want proof, ownership, and repeatable governance. |
Introduction
Fintech companies often move fast.
They build products quickly. They integrate with payment systems. They handle sensitive financial data. They rely on cloud platforms, APIs, processors, KYC tools, and support systems.
Then the bank security review arrives.
Suddenly, the company needs clear answers about access control, encryption, cloud security, vendor oversight, incident response, business continuity, data retention, audit logging, risk management, privacy, and governance.
For many fintech teams, the security work exists in pieces.
Engineering knows the cloud setup. IT knows identity. Operations knows vendors. Legal knows contracts. Leadership knows customer promises. But no one has pulled it into one clear security story.
Preparing for a Bank Security Review?
Canadian Cyber helps fintech companies prepare for bank due diligence, vendor security reviews, compliance evidence requests, and executive-level cyber risk reporting.
Meet the Fintech
Let’s call the company PayBridge Financial.
PayBridge is a growing fintech platform that helps businesses automate payment workflows, vendor payouts, customer onboarding, and transaction reporting.
The company works with:
- banking partners
- payment processors
- KYC and identity verification providers
- cloud infrastructure providers
- API integrations
- customer support tools
- business customers with sensitive financial data
PayBridge was preparing for two bank partner security reviews.
The reviews mattered. Without bank partner approval, the company could not expand into new markets or support several planned customer use cases.
PayBridge had security activity, but not enough security governance.
The Starting Point
PayBridge was not starting from zero.
The company already had several good controls in place. But the bank review exposed gaps in evidence, ownership, and consistency.
| Area | Existing Control |
|---|---|
| Identity | MFA enabled for most internal systems. |
| Cloud | Production workloads hosted in a major cloud provider. |
| Development | Pull requests required before production changes. |
| Encryption | Data encrypted in transit and at rest. |
| Incidents | Basic incident response plan drafted. |
Initial Problems
| Problem | Why It Mattered |
|---|---|
| Answers were scattered. | Engineering, operations, legal, and leadership gave different versions. |
| Evidence was incomplete. | Controls existed, but proof was not organized. |
| Vendor reviews were informal. | Banks wanted documented third-party risk decisions. |
| Access reviews were inconsistent. | Privileged access evidence was weak. |
| Incident response was untested. | The plan existed, but no tabletop had been completed. |
The issue was not that PayBridge had no security. The issue was that it could not prove its security posture in the way banks expected.
Why the Fintech Chose a vCISO
PayBridge considered hiring a full-time security leader.
But the company was not ready for a full internal security department.
It needed senior guidance quickly. It needed structure. It needed better evidence. It needed executive-level support during bank due diligence.
| Business Need | Why a vCISO Helped |
|---|---|
| Fast security leadership | Senior guidance without full-time CISO hiring delay. |
| Bank review preparation | Experience with due diligence language and evidence. |
| Risk prioritization | Clear roadmap instead of scattered tasks. |
| Executive reporting | Better board and leadership communication. |
Workstream 1: Building the Bank Security Review Pack
The first priority was the bank security review pack.
Banks usually ask detailed questions. The answers must be consistent, clear, and supported by evidence.
| Pack Section | What It Included |
|---|---|
| Security Overview | Short explanation of the security program and governance model. |
| System Scope | Key systems, cloud environments, data flows, and vendors. |
| Access Control | MFA, SSO, privileged access, onboarding, and offboarding evidence. |
| Cloud Security | Encryption, logging, cloud configuration, backups, and monitoring. |
| Vendor Risk | Critical vendor register and review decisions. |
| Incident Response | IR plan, escalation process, tabletop plan, and contacts. |
Example Before and After
| Before vCISO | After vCISO |
|---|---|
| “We use MFA.” | “MFA is enforced for all staff and privileged users. Evidence includes the MFA policy, enforcement report, and exception register.” |
| “We review vendors.” | “Critical vendors are risk-rated, assigned owners, reviewed for assurance, and approved with a documented decision.” |
| “We have an incident plan.” | “The incident response plan defines roles, escalation, notification triggers, and tabletop testing actions.” |
Need a Bank Security Review Pack?
Canadian Cyber helps fintech teams build due diligence packs with security summaries, control evidence, vendor reviews, risk registers, and questionnaire-ready responses.
Workstream 2: Creating a Fintech Risk Register
The bank review asked how PayBridge identified and managed security risk.
The company had risks in people’s heads. It needed a formal register.
| Risk | Business Impact | Treatment |
|---|---|---|
| API abuse or credential misuse. | Unauthorized transaction access or data exposure. | Strengthen API logging, token review, and alerting. |
| Bank partner integration outage. | Customer payment disruption. | Improve continuity plan and escalation workflow. |
| Privileged account compromise. | Unauthorized access to financial systems. | Review admin roles and enforce stronger access controls. |
| Vendor breach affecting customer data. | Data exposure and bank trust impact. | Formalize critical vendor reviews. |
PayBridge moved from informal risk discussion to formal risk governance. Each top risk had an owner, treatment plan, due date, status, and evidence link.
Workstream 3: Strengthening Access Control Evidence
Access control was one of the bank’s main focus areas.
That was expected. Fintech platforms handle sensitive financial workflows. Banks want to know who can access systems, customer data, APIs, admin consoles, and production environments.
| Access Area | What Was Checked |
|---|---|
| Microsoft 365 / Entra ID | MFA, admin roles, Conditional Access, and offboarding. |
| Cloud Console | Privileged roles, IAM groups, and break-glass access. |
| Source Control | Repository admins, branch protections, and user access. |
| Customer Support Tool | Staff access to customer records and support logs. |
| API Keys | Ownership, scope, rotation, and storage. |
What the vCISO Helped Implement
- quarterly access review schedule
- privileged access review template
- service account register
- offboarding evidence checklist
- support access logging review
- exception register
- access review sign-off process
Workstream 4: Formalizing Vendor Risk Management
Fintech companies rely on vendors.
PayBridge used vendors for KYC, payment processing, cloud hosting, email delivery, logging, analytics, customer support, development, accounting, and security tooling.
The bank wanted to know which vendors affected confidentiality, integrity, availability, and transaction reliability.
| Vendor Field | Example |
|---|---|
| Vendor Name | Cloud Provider |
| Service Provided | Production hosting |
| Data Handled | Customer and transaction data |
| Criticality | High |
| Review Decision | Approved with annual assurance review |
The company stopped treating vendor reviews as document collection. It started recording decisions.
Workstream 5: Improving Incident Response Readiness
PayBridge had an incident response plan.
But it had not been tested.
That is a common fintech gap. Banks care about incident response because cyber incidents can affect customers, transactions, reporting, notification timelines, and bank partner confidence.
| Bank Question | What PayBridge Needed |
|---|---|
| Who leads incident response? | Named roles and escalation path. |
| How are incidents classified? | Severity matrix. |
| When are bank partners notified? | Notification triggers. |
| Has the plan been tested? | Tabletop record. |
| Are lessons learned tracked? | Corrective action register. |
The Tabletop Scenario
The vCISO ran a realistic fintech tabletop.
A suspicious API token was used to access customer transaction records from an unusual location. The team had to investigate, contain the token, assess customer data impact, notify leadership, and decide whether bank partners needed to be informed.
Result: Technical response was strong, but executive escalation needed clearer triggers. That was fixed before the bank review.
Workstream 6: Creating the 90-Day Security Roadmap
The vCISO helped PayBridge avoid trying to fix everything at once.
The roadmap focused on the gaps most likely to affect bank approval.
| Priority | Action | Owner | Outcome |
|---|---|---|---|
| 1 | Complete critical vendor reviews. | Operations / vCISO | Bank-ready vendor evidence. |
| 2 | Finish privileged access review. | IT / Security | Stronger access control proof. |
| 3 | Run incident response tabletop. | vCISO / Leadership | Tested response readiness. |
| 4 | Build questionnaire response library. | Compliance / vCISO | Faster bank and customer responses. |
Results Before the Bank Review
By the time the bank review began, PayBridge was better prepared.
The company did not become perfect. It became prepared. That is what mattered.
| Before vCISO | After vCISO |
|---|---|
| Security answers scattered. | Standard bank security review pack. |
| Risks discussed informally. | Risk register with owners and treatment plans. |
| Vendor reviews incomplete. | Critical vendor register and decisions. |
| Incident plan untested. | Tabletop completed with action items. |
| Questionnaire responses rebuilt each time. | Response library with evidence links. |
Lessons for Other Fintech Companies
| Lesson | Why It Matters |
|---|---|
| Banks want proof, not claims. | Show settings, reviews, records, approvals, and evidence. |
| Vendor risk matters early. | Critical vendors need ratings, owners, assurance reviews, and decisions. |
| Incident response must be tested. | A plan that has never been exercised is weak evidence. |
| Access control is always reviewed. | MFA, privileged roles, service accounts, support access, and offboarding must be ready. |
| Leadership needs a security story. | Bank reviews test whether leadership understands and governs cyber risk. |
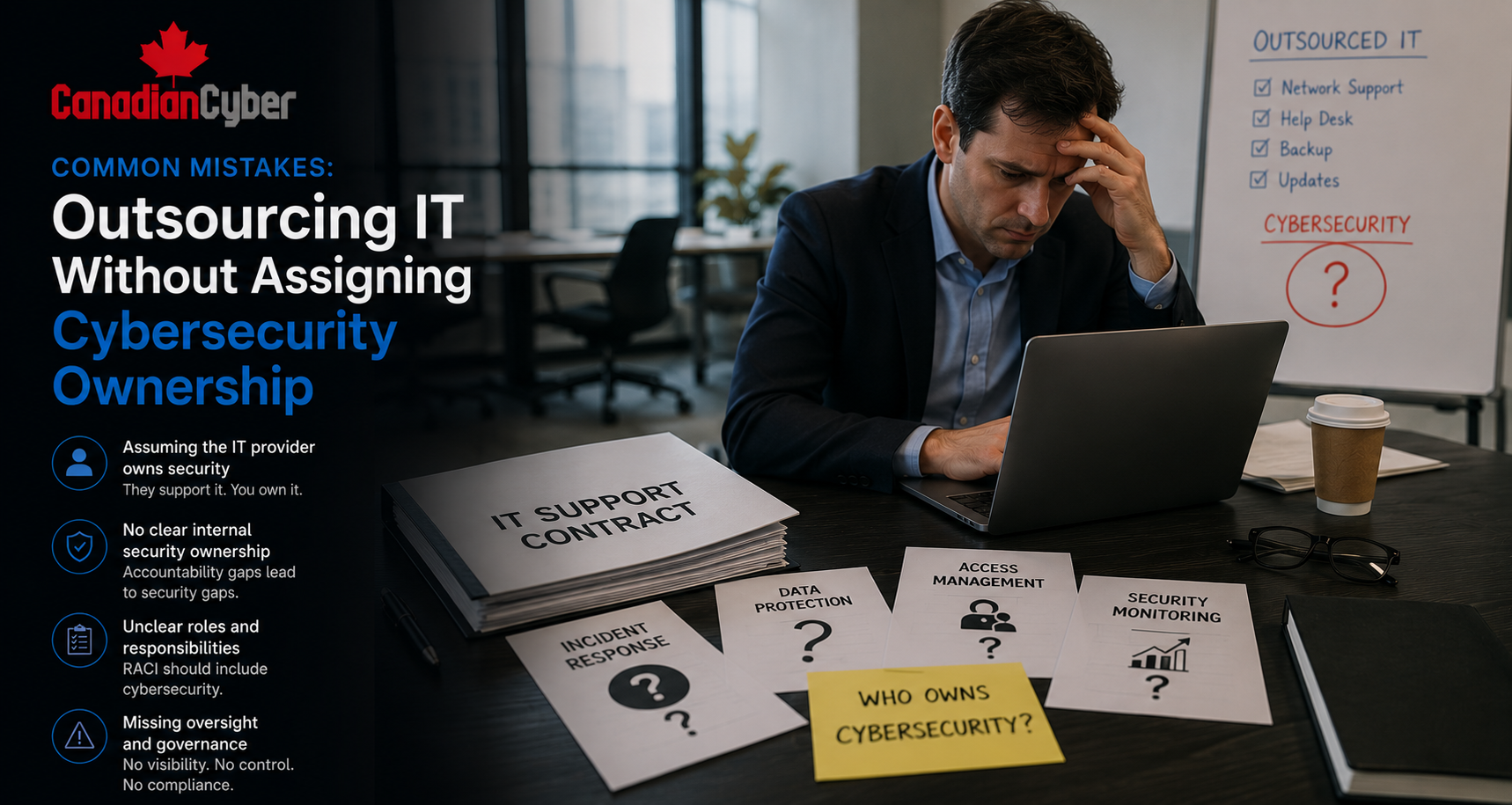
Common Mistakes to Avoid
- Mistake 1: Waiting for the bank questionnaire before organizing evidence. By then, the timeline is already tight.
- Mistake 2: Giving inconsistent answers. Engineering, legal, operations, and leadership should work from the same security story.
- Mistake 3: Treating vendor risk like a list of tools. Banks want criticality, data handled, assurance, ownership, and decisions.
- Mistake 4: Ignoring API security evidence. Authentication, rate limits, logging, tokens, and monitoring should be documented.
- Mistake 5: Having no risk register. Banks expect risk management to be intentional.
- Mistake 6: Skipping executive reporting. Leadership should understand top risks and decisions before bank meetings.
- Mistake 7: Overbuilding instead of prioritizing. Focus on bank-review blockers first.
What Good Looks Like
A fintech is better prepared for bank security reviews when it can show:
- clear system scope
- data flow diagrams
- access control evidence
- privileged access reviews
- API security controls
- cloud security evidence
- vendor risk register
- incident response plan and tabletop record
- risk register
- board cyber summary
- questionnaire response library
The goal is not to look like a mature bank. The goal is to show that security is governed, risks are known, controls are operating, and evidence is ready.
Canadian Cyber’s Take
At Canadian Cyber, we often see fintech companies wait until a bank review is already underway before organizing security evidence.
That creates pressure.
The team may have good controls, but the evidence is scattered. Answers are inconsistent. Vendors have not been reviewed formally. Incident response has not been tested.
A vCISO helps solve that problem by creating structure quickly. The best vCISO work does not slow the business down. It helps the company focus on the actions most likely to unlock trust, pass due diligence, and support growth.
For fintech companies, bank security reviews are not just compliance exercises. They are business milestones.
Takeaway
Bank security reviews can expose the difference between security activity and security governance.
A fintech may have tools, policies, cloud controls, and smart engineers. But banks want evidence, ownership, risk management, and tested processes.
A vCISO can help turn scattered security work into a clear due diligence story:
- start with the bank review pack
- build the risk register
- review access
- formalize vendor risk
- test incident response
- prepare leadership reporting
- create a 90-day roadmap
That is how a fintech moves from reactive answers to bank-ready confidence.
How Canadian Cyber Can Help
Canadian Cyber helps fintech companies prepare for bank security reviews, customer due diligence, and compliance readiness.
- vCISO support for fintechs
- bank security review preparation
- security questionnaire response packs
- risk register development
- vendor risk management
- API security evidence reviews
- access control reviews
- cloud security evidence packs
- incident response tabletop exercises
- board cyber reporting
- SOC 2 and ISO 27001 readiness
- 90-day security roadmaps
Stay Connected With Canadian Cyber
Follow Canadian Cyber for practical guidance on fintech security, vCISO services, bank due diligence, SOC 2, ISO 27001, cloud controls, and cyber risk governance.