ISO 27001 • DIY Implementation • Small Teams • Audit Readiness • vCISO
DIY ISO 27001 Implementation Plan for Companies Without a Security Team
You do not need a large security department to start ISO 27001. You do need a clear scope, simple ownership, practical evidence, and a plan your team can actually operate.
Quick Snapshot
| Implementation Area | What to Do First |
|---|---|
| Scope | Define the product, service, systems, teams, and locations the ISMS will cover. |
| Ownership | Assign an ISMS owner, control owners, risk owners, and leadership reviewer. |
| Core Controls | Start with access, assets, vendors, incidents, backups, logging, training, and change management. |
| Evidence | Build simple quarterly evidence packs instead of chasing screenshots at the end. |
| Outcome | A lean ISO 27001 implementation plan that works even without a full security team. |
Introduction
ISO 27001 can feel impossible when you do not have a security team.
- There is no CISO.
- No compliance department.
- No GRC analyst.
- No dedicated audit manager.
- No one whose full-time job is collecting evidence.
That does not mean ISO 27001 is out of reach.
It means the implementation has to be practical.
Companies without a security team usually fail ISO 27001 when they try to copy enterprise programs. They build too much documentation, include too much scope, assign vague ownership, and wait too long to collect evidence.
A lean ISO 27001 implementation works differently. It focuses on the service customers care about. It assigns responsibility to real people. It starts with the controls that buyers and auditors test most often. It keeps evidence simple. It uses leadership review to make decisions instead of creating a paperwork machine.
Trying to Start ISO 27001 Without a Security Team?
Canadian Cyber helps lean teams build practical ISO 27001 programs with the right scope, clear ownership, simple evidence packs, SharePoint ISMS workspaces, and vCISO support.
Why ISO 27001 Feels Hard Without a Security Team
ISO 27001 is not just a checklist.
It is a management system.
That means it needs recurring work, leadership decisions, risk reviews, evidence, corrective actions, and improvement over time.
For companies without a security team, the hard part is not understanding that security matters. The hard part is making ISO 27001 fit into normal business operations.
Common Problems
| Problem | What Usually Happens |
|---|---|
| No dedicated owner | ISO work gets passed between IT, operations, engineering, and leadership. |
| Too much scope | The company tries to certify every tool, team, and process at once. |
| Policy-first approach | Documents are written before controls actually operate. |
| Evidence chaos | Screenshots, exports, tickets, and approvals are scattered everywhere. |
| Weak risk ownership | Risks are listed but not reviewed or treated properly. |
| Last-minute audit prep | The team tries to prove six months of work in one week. |
The solution is not to overbuild. The solution is to build a small ISMS that works.
Step 1: Choose a Practical ISO 27001 Scope
Scope is the first major decision.
It can also be the biggest cost driver.
Without a security team, do not start by including everything. Start with the product, service, or business function that customers care about most.
Good First Scope Examples
| Company Type | Practical First Scope |
|---|---|
| SaaS startup | The customer-facing SaaS platform and supporting cloud operations. |
| Managed service provider | The managed service delivery environment. |
| Consulting company | Client data handling, delivery systems, and core business operations. |
| Healthtech platform | Patient-facing platform, cloud hosting, support workflows, and key vendors. |
| Fintech platform | Production platform, financial data workflows, cloud infrastructure, and integrations. |
Include These in Scope
- production systems
- cloud infrastructure
- identity provider
- source control
- CI/CD pipeline
- customer support platform
- customer data stores
- key vendors
- people who operate the service
- policies and processes that support the service
Avoid This at the Start
- Do not include every internal tool just because it exists.
- Do not include experimental products too early.
- Do not include systems no one can evidence.
- Do not include vendors that do not support the scoped service.
- Do not include business units that are not ready to operate controls.
Practical rule: If you cannot assign an owner and collect evidence for it, think carefully before putting it in scope.
Need Help Right-Sizing Scope?
Canadian Cyber helps companies define ISO 27001 scope before they overbuild, overpay, or create avoidable audit gaps.
Step 2: Assign ISO 27001 Roles Without Hiring a Security Team
You still need ownership.
But ownership does not have to mean a full security department. A lean team can assign ISO responsibilities across existing roles.
Simple Ownership Model
| Role | Who Can Own It | Main Responsibility |
|---|---|---|
| ISMS Owner | COO, CTO, Operations Lead, Compliance Lead | Runs the ISO 27001 program. |
| Executive Sponsor | CEO, Founder, Managing Director | Approves scope, risk decisions, and resources. |
| Risk Owners | Department leads | Own risks and treatment actions. |
| Control Owners | IT, Engineering, HR, Operations | Operate controls and provide evidence. |
| Evidence Coordinator | Ops, Admin, Compliance, Project Manager | Tracks evidence and reminders. |
| External Support | vCISO or consultant | Guides implementation and reviews readiness. |
Do not make one person responsible for everything. ISO 27001 needs shared accountability.
Step 3: Build the Minimum Policy Set
You need policies.
But you do not need a huge policy library on day one. Start with a small set that reflects how your company actually works.
| Policy / Procedure | Why It Matters |
|---|---|
| Information Security Policy | Sets leadership commitment and security direction. |
| Access Control Policy | Defines MFA, permissions, onboarding, offboarding, and reviews. |
| Asset Management Procedure | Tracks systems, devices, applications, and data owners. |
| Risk Management Procedure | Explains how risks are identified, rated, treated, and reviewed. |
| Incident Response Plan | Defines how security events are reported and handled. |
| Supplier Security Procedure | Shows how vendors are reviewed and approved. |
| Backup and Recovery Procedure | Explains backup coverage, retention, and restore testing. |
| Change Management Procedure | Defines how system changes are reviewed and deployed. |
Practical rule:
A policy is only useful if it produces evidence. Do not write policies that describe a perfect future state. Write policies that describe controls you can actually operate.
Step 4: Build a Simple Risk Register
ISO 27001 is risk-based.
That means your risk register is not optional.
But it does not need to be complex. A simple spreadsheet or SharePoint List can work well.
Risk Register Fields
| Field | Purpose |
|---|---|
| Risk ID | Gives each risk a unique reference. |
| Risk Description | Explains what could go wrong. |
| Owner | Assigns accountability. |
| Likelihood and Impact | Scores probability and business effect. |
| Treatment Decision | Mitigate, accept, transfer, or avoid. |
| Evidence Link | Connects treatment to proof. |
Example Risks
| Risk | Treatment |
|---|---|
| Former employees retain access to cloud systems. | Implement offboarding checklist and quarterly access reviews. |
| Critical vendor outage affects service availability. | Review vendor assurance and document continuity plan. |
| Backups fail during a real recovery event. | Run restore test and document results. |
| Excessive admin permissions expose customer data. | Review privileged roles and enforce least privilege. |
Step 5: Build the First Control Set
Without a security team, start with the controls that create the most audit value.
Do not try to mature everything at once.
| Control Area | Lean First Step |
|---|---|
| Access Control | Enforce MFA and complete an access review. |
| Asset Inventory | List systems, owners, and data types. |
| Vendor Management | Create a vendor register and review critical vendors. |
| Incident Response | Approve the plan and run a tabletop. |
| Backup and Recovery | Confirm backups and run a restore test. |
| Logging and Monitoring | Identify critical logs and review alerts. |
Fastest early win: Complete an access review. Access control is one of the first areas auditors and customers check.
Step 6: Create Evidence Packs Before You Need Them
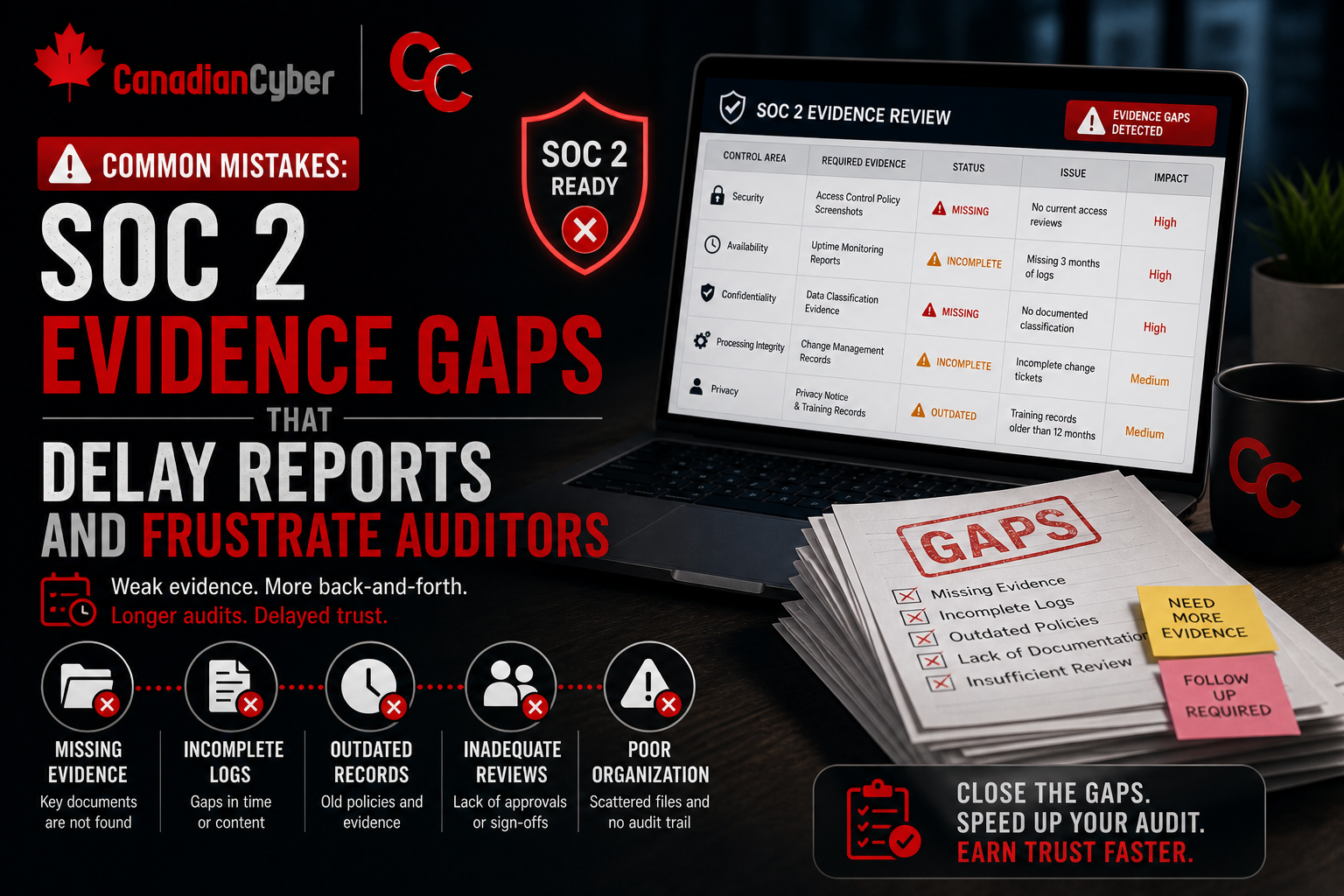
Evidence is where many DIY ISO 27001 projects become stressful.
The team does the work but forgets to save proof.
The fix is simple: create evidence packs early.
| Evidence Pack | What to Include |
|---|---|
| Access Reviews | User exports, review sign-off, removals, exceptions. |
| Vendor Reviews | Vendor register, assurance review, approval decisions. |
| Change Management | Pull requests, deployment records, emergency changes. |
| Backup and Restore | Backup settings, restore test, recovery notes. |
| Incident Response | Incident log, tabletop record, lessons learned. |
| Management Review | Meeting minutes, decisions, action items. |
Evidence naming example:
AccessReview-2026-Q1.pdf, VendorReview-CriticalVendors-2026-Q1.xlsx, RestoreTest-ProductionDB-2026-03.pdf, IncidentTabletop-2026-Q2.pdf.
Need a Simple ISO Evidence Workspace?
Canadian Cyber helps teams build SharePoint-based ISO 27001 evidence workspaces with folders, metadata, review dates, owners, and audit-ready evidence packs.
Step 7: Create a 90-Day Implementation Plan
A DIY ISO 27001 project needs momentum.
A 90-day plan helps your team move from scattered work to an operating ISMS.
| Phase | Key Tasks | Output |
|---|---|---|
| First 30 Days: Foundation | Define scope, assign ISO roles, build system inventory, identify customer data, create vendor register, draft core policies. | Scope statement, ownership matrix, asset list, data inventory, vendor list, evidence workspace. |
| Days 31 to 60: Control Operation | Confirm MFA, run first access review, review critical vendors, build risk register, approve incident plan, run backup restore test. | MFA evidence, access review record, vendor decisions, risk register, approved IR plan, restore evidence. |
| Days 61 to 90: Review and Improve | Run tabletop, review risk register, complete training tracking, prepare management review, run mini internal audit, close urgent gaps. | Tabletop record, training report, management review minutes, findings, corrective actions, next-quarter roadmap. |
The goal is not certification in 90 days. The goal is to make the ISMS real.
Step 8: Prepare for Internal Audit
Internal audit is required before certification.
For a company without a security team, this step can feel intimidating. Keep it practical.
| Question | Evidence |
|---|---|
| Is scope defined and approved? | Scope statement. |
| Are policies approved? | Policy approval records. |
| Are risks identified and reviewed? | Risk register. |
| Are access reviews completed? | Access review evidence. |
| Are vendors reviewed? | Vendor register and reviews. |
| Has management reviewed the ISMS? | Management review minutes. |
Step 9: Run Management Review
Management review is where leadership proves the ISMS is not just an admin project.
It shows that leadership understands security performance, risks, incidents, audit results, and resource needs.
| Management Review Input | Example |
|---|---|
| Risk register status | High risks and treatment progress. |
| Internal audit results | Findings and corrective actions. |
| Incident summary | Incidents or tabletop outcomes. |
| Vendor risk summary | Critical vendors and open issues. |
| Resource needs | Tools, staff, external support, or budget. |
Management review minutes should show decisions. A meeting that only says “ISO was discussed” is weak evidence.
Step 10: Decide Where You Need Help
DIY does not mean doing everything alone.
Companies without a security team often move faster when they use outside help for specific parts.
| Area | Why It Helps |
|---|---|
| Scope definition | Prevents over-scoping and audit rework. |
| Gap assessment | Shows what is missing before certification. |
| Risk methodology | Keeps risk scoring consistent. |
| Policy review | Avoids generic or unrealistic policies. |
| Internal audit | Provides independence and objectivity. |
| vCISO support | Gives senior guidance without full-time hiring. |
Common Mistakes to Avoid
- Mistake 1: Starting with too much scope. A broad scope creates too much evidence work for a lean team.
- Mistake 2: Writing policies before checking reality. Policies should match operations.
- Mistake 3: Giving one person all ISO responsibility. ISO 27001 needs business ownership.
- Mistake 4: Ignoring evidence until audit time. Evidence needs to be collected as controls operate.
- Mistake 5: Treating vendor reviews as document collection. A SOC 2 report is not enough.
- Mistake 6: Skipping restore tests and tabletops. Backups and incident plans need testing.
- Mistake 7: Closing findings without verification. Corrective actions need proof and review.
DIY ISO 27001 Gap Register Example
Track gaps clearly from the start.
| Gap | Risk | Owner | Priority | Evidence Needed |
|---|---|---|---|---|
| No formal access review | Excessive access may remain active | IT Lead | High | Completed access review |
| Vendor register incomplete | Third-party risk not visible | Operations | High | Vendor list and reviews |
| Incident response plan untested | Team may respond poorly during incident | ISMS Owner | Medium | Tabletop record |
| Restore test not documented | Recovery capability unproven | DevOps | High | Restore test evidence |
| Risk register not reviewed | Risk treatment may stall | ISMS Owner | High | Risk review notes |
What Good Looks Like After Six Months
After six months, a company without a security team should not look like a large enterprise.
It should look organized, consistent, and honest.
| Area | What Good Looks Like |
|---|---|
| Scope | Clear and approved. |
| Ownership | ISMS owner and control owners assigned. |
| Policies | Core policies approved and reviewed. |
| Risks | Risk register active with treatment actions. |
| Access | MFA enforced and access reviews completed. |
| Evidence | Quarterly evidence packs started. |
Canadian Cyber’s Take
At Canadian Cyber, we often see small teams delay ISO 27001 because they think they need a full security department first.
They usually do not.
What they need is a realistic implementation model.
A small company can build a strong ISO 27001 program if it keeps scope practical, assigns ownership clearly, collects evidence as work happens, and uses leadership review to make decisions.
ISO 27001 is not about having the biggest security team. It is about showing that security is managed, risks are reviewed, controls operate, and improvement is happening.
Takeaway
You can start ISO 27001 without a dedicated security team.
- Start small.
- Define scope.
- Assign owners.
- Build a minimum policy set.
- Create a risk register.
- Operate the first controls.
- Collect evidence early.
- Run management review.
- Use internal audit to find gaps.
- Bring in targeted support where it saves time.
The goal is not to build a perfect ISMS on day one. The goal is to build an ISMS your team can actually run.
How Canadian Cyber Can Help
Canadian Cyber helps companies without security teams build practical ISO 27001 programs.
- ISO 27001 scope definition
- DIY implementation planning
- gap assessments
- risk register setup
- policy and procedure development
- SharePoint ISMS workspace setup
- evidence pack design
- access and vendor review workflows
- incident tabletop exercises
- internal audit support
- management review preparation
- vCISO support for lean teams
Stay Connected With Canadian Cyber
Follow Canadian Cyber for practical guidance on ISO 27001, audit readiness, lean security programs, evidence management, and vCISO support.