Cloud Security • ISO 27017 • ISO 27018 • SaaS Risk • Customer Data
7 Cloud Security Myths That Are Putting Your Data at Risk
Cloud platforms are powerful, but they do not remove your security responsibilities. These seven myths can leave SaaS, healthcare, fintech, and service platforms exposed.
Cloud platforms are powerful, but they do not remove your security responsibilities. These seven myths can leave SaaS, healthcare, fintech, and service platforms exposed to access gaps, weak privacy controls, poor evidence, and customer trust problems.
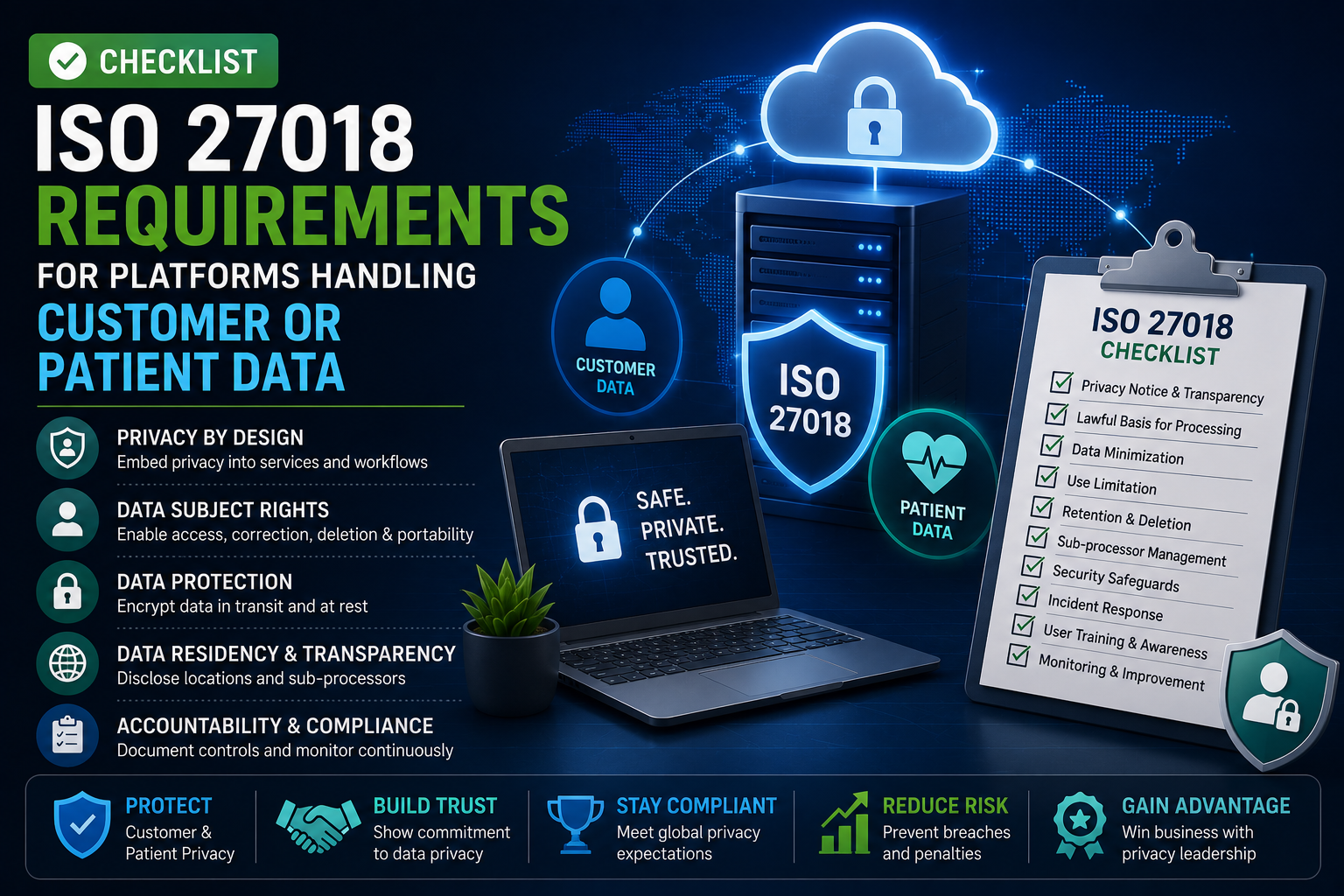
ISO/IEC 27017 provides cloud-specific information security guidance for both the provision and use of cloud services, including additional implementation guidance and cloud-specific controls. ISO/IEC 27018 focuses on protecting personally identifiable information, or PII, in public cloud environments where the cloud provider acts as a PII processor.
Quick Snapshot
| Cloud Security Myth | Real Risk |
|---|---|
| “The cloud provider handles security.” | Shared responsibility gaps remain unmanaged. |
| “ISO 27001 is enough for cloud.” | Cloud-specific controls may be missed. |
| “Encryption means our data is safe.” | Access, key management, logs, and exports may still expose data. |
| “We know where customer data lives.” | Data often appears in logs, support tickets, backups, and integrations. |
| “Vendor SOC reports cover us.” | Provider assurance does not prove your own controls work. |
| “Admin access is under control.” | Privileged roles often grow without review. |
| “Privacy is a legal issue, not a cloud issue.” | Poor cloud privacy controls can create breach, contract, and trust risk. |
Introduction
Cloud security feels simple at first.
You move to AWS, Azure, Google Cloud, Microsoft 365, or another trusted platform. You enable MFA. You use encryption. You collect a few vendor reports. You tell customers your data is hosted in a secure cloud.
But that is not enough.
Cloud platforms give you powerful security tools. They do not automatically configure them correctly. They do not decide who should access customer data. They do not review your vendors for you. They do not prove your deletion process works across backups, logs, support tickets, and exports.
That is why cloud security myths are dangerous. They create false confidence.
ISO 27017 and ISO 27018 help cut through that false confidence. ISO 27017 focuses on cloud security controls and shared responsibility. ISO 27018 focuses on protecting personal data in public cloud environments. Together, they help SaaS and cloud platforms prove that customer data is not only hosted securely, but governed properly.
Worried Your Cloud Controls Are Based on Assumptions?
Canadian Cyber helps organizations map ISO 27017 and ISO 27018 controls across cloud platforms, SaaS tools, vendors, customer data flows, and evidence packs.
Myth 1: “The Cloud Provider Handles Security”
This is the biggest cloud security myth.
Cloud providers secure the infrastructure they operate. But your organization still controls many important decisions.
- You control users.
- You control permissions.
- You control data flows.
- You control application logic.
- You control vendor choices.
- You control logging review.
- You control retention rules.
- You control customer support access.
The provider gives you the tools. Your team must use them correctly.
What This Myth Causes
| Assumption | What Can Go Wrong |
|---|---|
| “AWS handles security.” | IAM roles may still be over-permissioned. |
| “Azure is compliant.” | Your tenant may still have weak admin controls. |
| “Google Cloud encrypts data.” | Your keys, exports, and access paths may still be poorly governed. |
| “Our SaaS vendors are certified.” | You may not know what customer data they process. |
| “The provider logs activity.” | Logs may not be enabled, retained, reviewed, or linked to alerts. |
What ISO 27017 Helps You Do
ISO 27017 pushes teams to clarify cloud responsibility. That means documenting:
- what the provider manages
- what your team manages
- where responsibility is shared
- which controls are inherited
- which controls must be configured by you
- which evidence proves control operation
Evidence to Collect
| Evidence | Why It Matters |
|---|---|
| Shared responsibility matrix | Shows what the provider handles and what your team owns. |
| Cloud configuration review | Proves settings are not assumed. |
| IAM access review | Shows privileged access is checked. |
| Logging review | Proves activity is monitored. |
| Vendor assurance review | Shows provider reports were actually reviewed. |
Canadian Cyber Tip: Do not tell customers, “Our cloud provider is secure.” Tell them, “Here is how we manage our responsibilities in the cloud.”
Myth 2: “ISO 27001 Is Enough for Cloud Security”
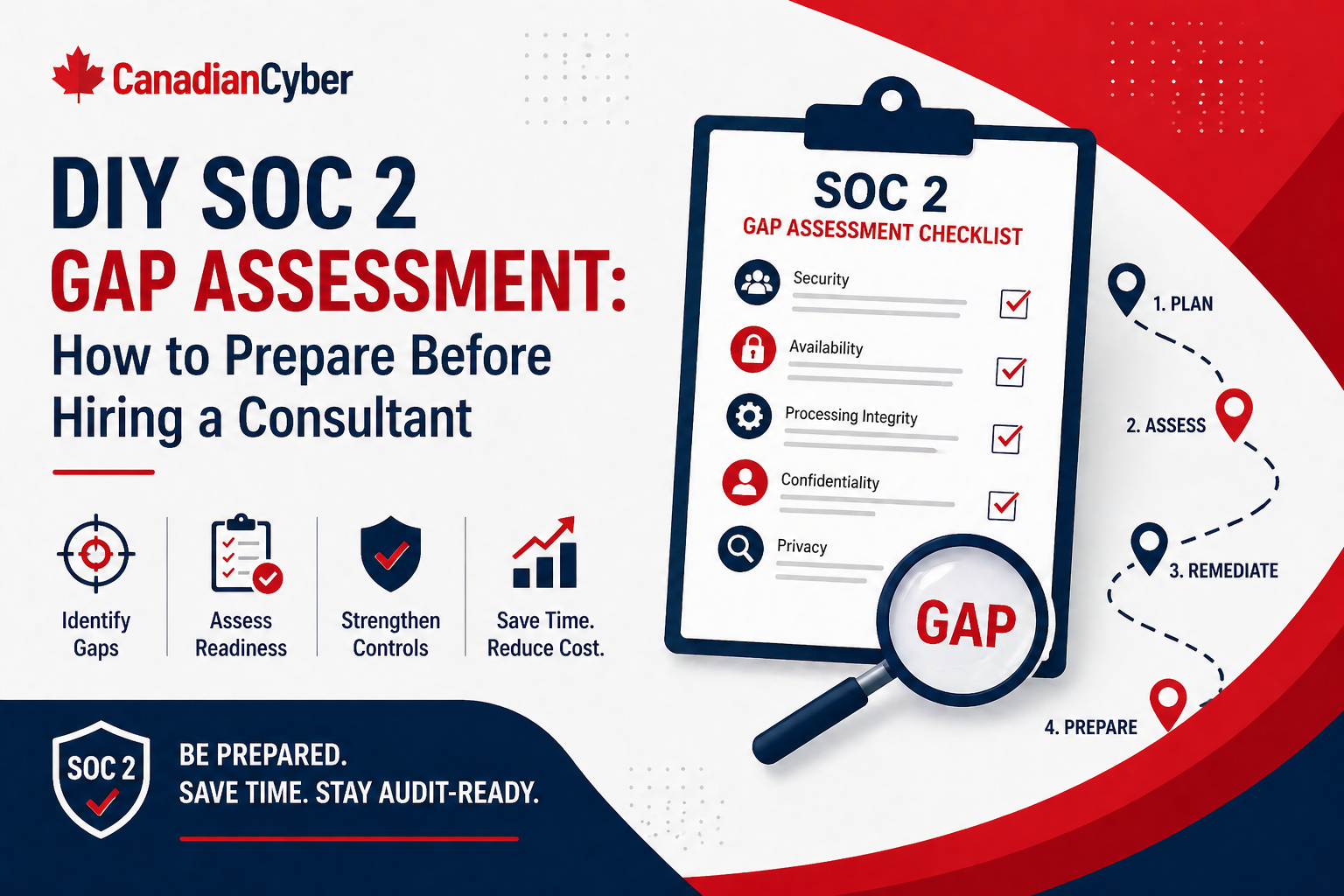
ISO 27001 is valuable. But cloud environments create specific risks that general security programs often miss.
- Multi-tenant architecture
- Shared responsibility
- Cloud admin roles
- Virtual networks
- Cloud storage permissions
- Sub-processors
- API integrations
- Customer data deletion
- Cloud monitoring
- Provider assurance
That is why ISO 27017 and ISO 27018 matter. ISO 27017 adds cloud-specific security guidance. ISO 27018 adds privacy guidance for protecting PII in public cloud environments.
Where ISO 27001 Alone May Not Be Enough
| Area | Common Gap |
|---|---|
| Shared responsibility | No clear split between provider and customer duties. |
| Cloud configuration | No evidence that settings are reviewed. |
| Tenant separation | SaaS isolation model is not tested or documented. |
| Sub-processors | Vendor data handling is not mapped. |
| Privacy controls | PII handling is treated as legal paperwork. |
| Cloud logs | Logs exist but are not reviewed. |
| Deletion | Data removal is not proven across backups and tools. |
Practical Control Map
| Standard | Best Use |
|---|---|
| ISO 27001 | Overall information security management system. |
| ISO 27017 | Cloud service security and shared responsibility. |
| ISO 27018 | PII protection in public cloud environments. |
Need to Align ISO 27001, 27017, and 27018?
Canadian Cyber can help map your cloud controls into one practical evidence model for audits, customer reviews, and vendor assessments.
Align My Cloud Compliance Program
Explore ISO 27001 Services
Myth 3: “Encryption Means Our Data Is Safe”
Encryption is important. But encryption alone does not stop every cloud data risk.
Encrypted data can still be exposed if:
- admins have too much access
- keys are poorly controlled
- exports are downloaded locally
- logs contain sensitive data
- support tickets include patient or customer information
- backups are retained too long
- API tokens are abused
- a vendor receives data without proper review
Encryption protects data under certain conditions. It does not replace governance.
Encryption Reality Check
| Question | Why It Matters |
|---|---|
| Who can access encryption keys? | Key admins may have powerful access. |
| Are keys rotated? | Long-lived keys increase risk. |
| Are exports encrypted? | Reports and downloads often escape normal controls. |
| Are backups encrypted? | Backup storage is frequently overlooked. |
| Are logs sanitized? | Logs may expose PII or secrets. |
| Are secrets stored properly? | Hard-coded secrets can bypass encryption benefits. |
Better Message for Buyers
Weak answer: “We encrypt all data.”
Stronger answer: “We encrypt data in transit and at rest, restrict key access, review key administrators, control exports, and monitor privileged data access.”
Myth 4: “We Know Where Customer Data Lives”
Many teams think customer data lives only in the production database.
It rarely does.
Customer or patient data may also appear in:
- support tickets
- application logs
- analytics tools
- email notifications
- backups
- data warehouses
- admin exports
- error reports
- screen recordings
- file uploads
- API payloads
- vendor systems
- test environments
This is one of the biggest ISO 27018 readiness problems. If you do not know where PII lives, you cannot protect it, delete it, or explain it clearly to customers.
Data Discovery Checklist
| Location | What to Check |
|---|---|
| Production databases | Main customer or patient records. |
| Object storage | Uploaded files, images, forms, attachments. |
| Logs | User IDs, IP addresses, record IDs, error payloads. |
| Support tools | Screenshots, tickets, customer messages. |
| Backups | Retention, encryption, restoration, deletion handling. |
| Analytics | Event data, user behavior, metadata. |
| Test environments | Real data, masked data, or synthetic data. |
| Vendors | Sub-processors and integration partners. |
High-impact fix: Create a customer data map before writing more policies. Most privacy gaps become obvious once the real data paths are visible.
Myth 5: “Vendor SOC Reports Cover Us”
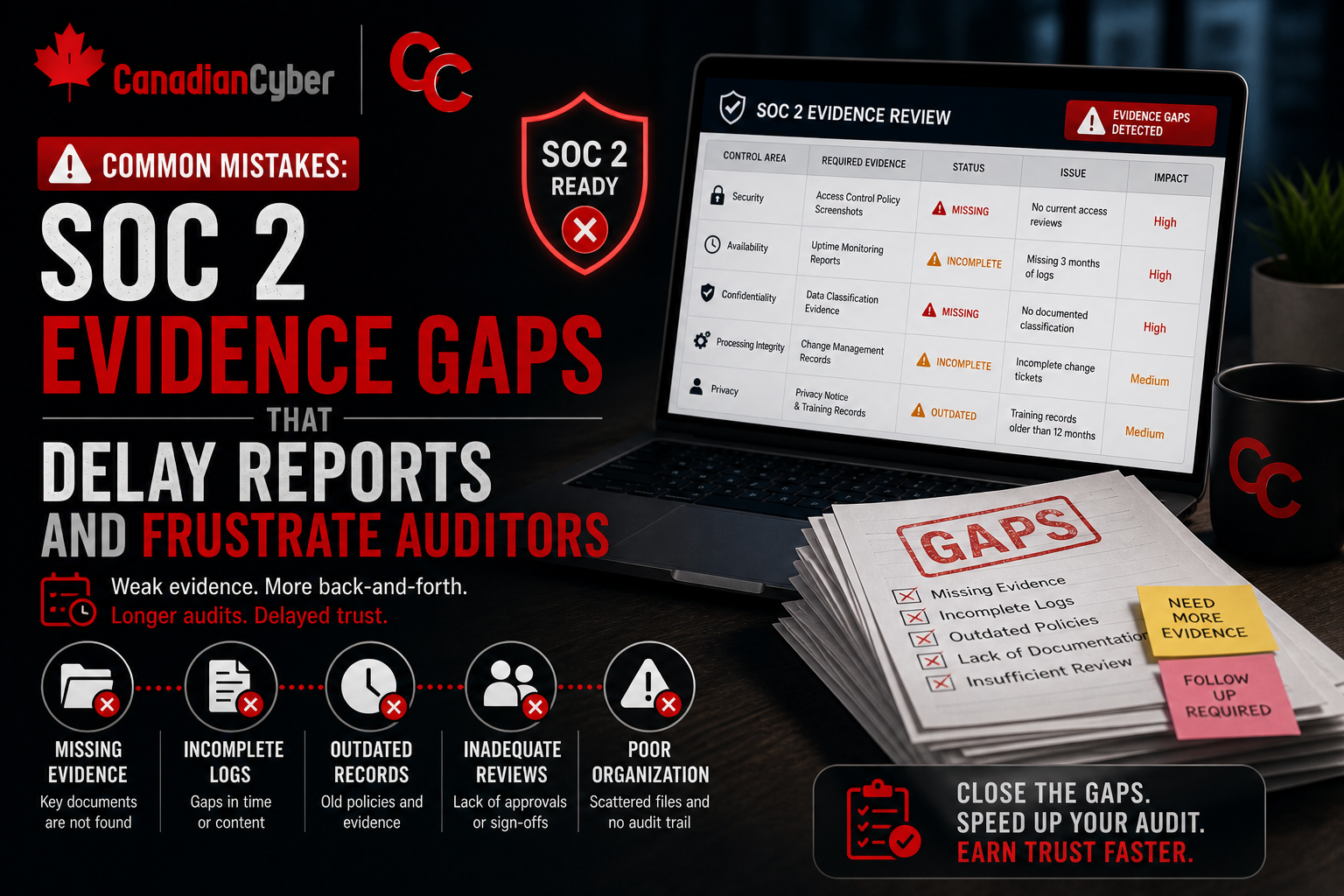
Vendor assurance matters. But a vendor SOC 2 report, ISO certificate, or cloud provider compliance page does not prove your own controls are working.
It does not prove that:
- your IAM roles are correct
- your tenant settings are secure
- your data deletion process works
- your logs are reviewed
- your support staff access is appropriate
- your API tokens are rotated
- your customer data is mapped
- your vendor risk decisions are documented
Vendor reports are inputs. They are not your full control evidence.
Vendor Assurance vs Your Evidence
| Vendor Evidence | Your Evidence |
|---|---|
| Cloud provider SOC 2 report | Your cloud configuration review. |
| Vendor ISO certificate | Your vendor risk decision. |
| SaaS security page | Your data processing review. |
| Provider uptime commitment | Your business continuity plan. |
| Vendor incident process | Your escalation and notification process. |
| Platform encryption claim | Your tenant encryption settings. |
Canadian Cyber Tip: Do not collect vendor reports just to fill a folder. Record the decision. Approve, conditionally approve, reject, or monitor.
Myth 6: “Admin Access Is Under Control”
Admin access often looks controlled until someone reviews it closely. Then the gaps appear.
- Former employees still have access.
- Contractors have no expiry date.
- Developers have standing production access.
- Service accounts have broad permissions.
- Break-glass accounts are not reviewed.
- Cloud roles are inherited from old projects.
- Support staff can view too much customer data.
- No one knows who owns some privileged accounts.
This is a serious cloud risk. It is also one of the most common customer due diligence topics.
Admin Access Review Table
| Area | What to Check |
|---|---|
| Cloud admins | AWS, Azure, GCP privileged roles. |
| Identity admins | Microsoft Entra ID, Okta, Google Workspace. |
| Source control admins | GitHub, GitLab, Bitbucket. |
| CI/CD admins | Deployment and pipeline permissions. |
| Database admins | Production data access. |
| Support admins | Customer and patient record access. |
| Service accounts | Ownership, scope, rotation. |
| Break-glass accounts | MFA, storage, review, testing. |
Evidence auditors and buyers trust:
- MFA report
- privileged access list
- quarterly access review
- offboarding sample
- contractor access expiry record
- service account register
- admin role approval
- break-glass review
- support access log
Admin access should be approved, limited, logged, reviewed, time-bound where possible, and removed quickly when no longer needed.
Myth 7: “Privacy Is a Legal Issue, Not a Cloud Security Issue”
Privacy is not only legal. It is operational.
A privacy promise fails when cloud controls fail. For example:
- a support employee views the wrong patient record
- a log stores sensitive personal data
- a backup keeps data longer than agreed
- a vendor processes customer data without review
- an export is sent to the wrong client
- a cloud bucket exposes uploaded documents
- a deletion request is not completed across downstream systems
These are not just legal issues. They are cloud control failures. ISO 27018 is useful because it connects privacy protection to cloud control operation.
Privacy Control Checklist
| Privacy Risk | Cloud Control |
|---|---|
| Unauthorized access to PII | Least privilege, MFA, access reviews. |
| Excessive data collection | Data minimization and privacy review. |
| Poor deletion | Retention and deletion workflow. |
| Vendor exposure | Sub-processor register and review. |
| Log leakage | Log sanitization and review. |
| Export misuse | Approval and export logging. |
| Incident delay | Privacy incident response process. |
| Unclear responsibility | Controller / processor responsibility matrix. |
High-impact fix: Run a privacy incident tabletop.
Use a realistic cloud scenario, such as a support user accessing the wrong patient file, a vendor reporting unauthorized access, or an admin export being shared with the wrong client.
The Cloud Myth Reality Check
Use this table to test whether your cloud security program is based on proof or assumptions.
| Myth | Reality | Evidence You Need |
|---|---|---|
| The provider handles security | Security is shared | Shared responsibility matrix |
| ISO 27001 is enough | Cloud needs cloud-specific control mapping | ISO 27017 / 27018 control map |
| Encryption solves data risk | Access, keys, logs, and exports still matter | Encryption and key evidence |
| We know where data lives | Data spreads into tools, logs, backups, and vendors | Data inventory and flow map |
| Vendor reports cover us | Your controls still need evidence | Vendor review decision trail |
| Admin access is controlled | Privileged access must be reviewed | Access review records |
| Privacy is legal only | Privacy depends on cloud control operation | PII evidence pack |
What Good Looks Like
A strong cloud security program can answer these questions clearly:
- What cloud services are in scope?
- What customer or patient data is processed?
- Who owns each cloud control?
- What does the cloud provider handle?
- What does your team handle?
- Which vendors process sensitive data?
- Who can access production and customer records?
- How are logs reviewed?
- How is deletion proven?
- How are privacy incidents handled?
- Where is the evidence stored?
The answer should not live in one person’s head. It should live in a control map, evidence workspace, and operating cadence.
Common Warning Signs
Your cloud security program may be exposed if:
- no shared responsibility matrix exists
- admin access has not been reviewed recently
- customer data is not mapped outside production
- support tickets contain sensitive data with no handling rules
- logs are enabled but never reviewed
- vendor reports are collected but not assessed
- cloud storage permissions are not checked regularly
- data deletion is not verified across backups and tools
- privacy incidents have never been rehearsed
- evidence is scattered across inboxes, chats, and folders
These are exactly the gaps that make audits, customer reviews, and incident response harder than they need to be.
Canadian Cyber’s Take
At Canadian Cyber, we often see organizations with strong cloud platforms but weak cloud governance.
They use reputable providers. They have modern tools. They care about security.
But their risk comes from assumptions:
- They assume the provider covers more than it does.
- They assume encryption solves more than it can.
- They assume vendor reports prove more than they do.
- They assume customer data only lives in one place.
- They assume privacy is handled by legal language.
ISO 27017 and ISO 27018 help replace those assumptions with evidence.
The strongest cloud programs do not just say the cloud is secure. They show how cloud responsibility is assigned, how personal data is protected, how access is reviewed, how vendors are governed, and how evidence is kept current. That is what builds customer trust.
Takeaway
Cloud security myths are dangerous because they sound reasonable.
The provider does handle some security. Encryption does help. Vendor reports do matter. ISO 27001 is valuable. Privacy teams do play a key role.
But none of those things replace your own cloud control responsibilities.
If your organization handles customer data, patient data, financial data, or sensitive SaaS workloads, you need more than assumptions.
You need a clear control map, a shared responsibility model, a data inventory, access reviews, vendor decisions, privacy evidence, logging reviews, and incident readiness.
ISO 27017 and ISO 27018 help turn cloud security from a set of beliefs into a set of controls you can prove.
How Canadian Cyber Can Help
Canadian Cyber helps SaaS, healthcare, fintech, and service organizations strengthen cloud security and privacy controls.
- ISO 27017 readiness reviews
- ISO 27018 readiness reviews
- cloud control mapping
- shared responsibility matrices
- customer and patient data inventories
- cloud privacy evidence packs
- vendor and sub-processor reviews
- SharePoint evidence workspaces
- access review workflows
- logging and monitoring evidence
- privacy incident tabletop exercises
- ISO 27001, ISO 27017, and ISO 27018 alignment
- vCISO support for cloud security governance
Stay Connected With Canadian Cyber
Follow Canadian Cyber for practical guidance on ISO 27017, ISO 27018, cloud security, SaaS governance, privacy evidence, and vCISO support.