Cloud Privacy • ISO 27018 • Customer Data • Patient Data • SaaS Compliance
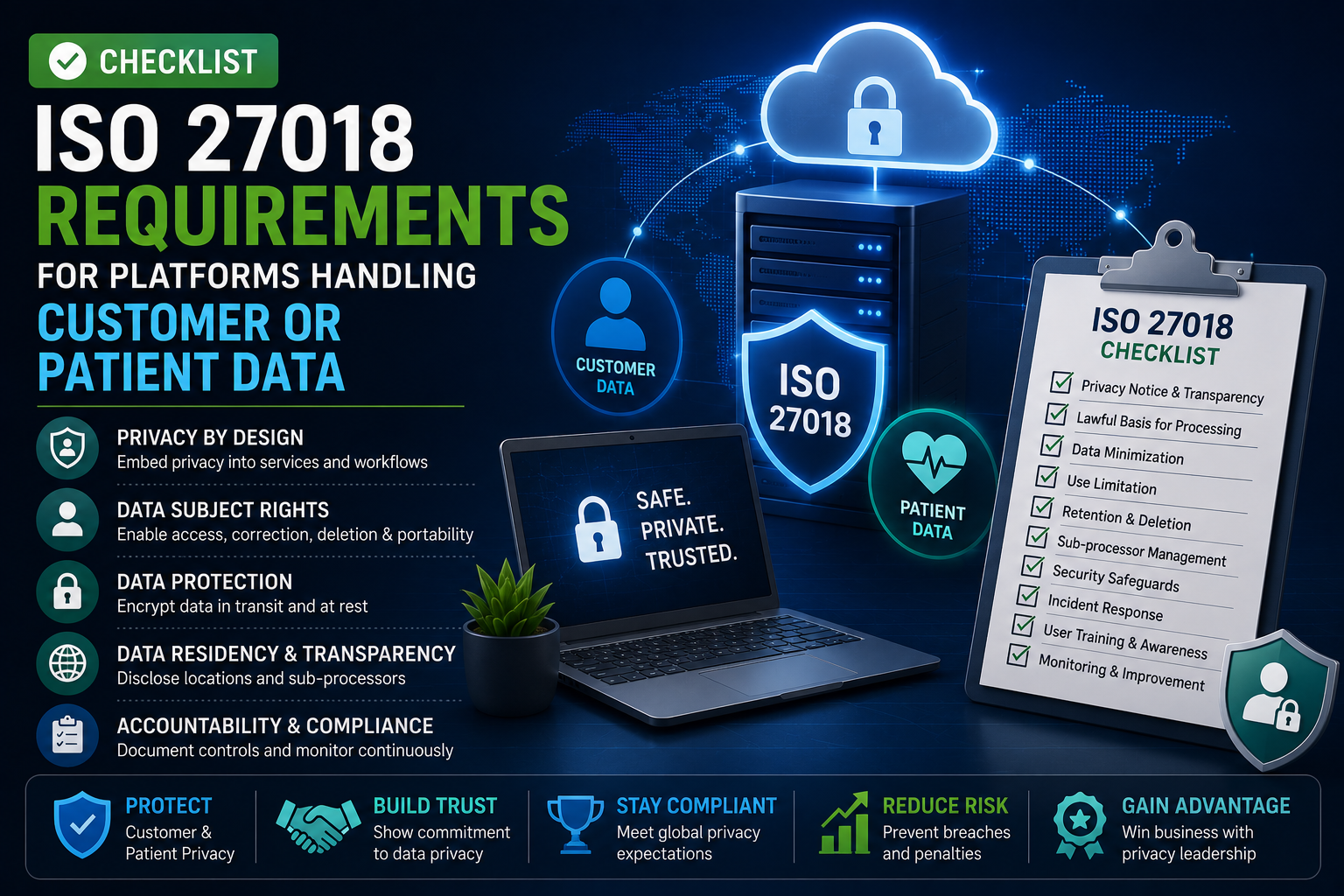
Checklist: ISO 27018 Requirements for Platforms Handling Customer or Patient Data
A practical privacy-readiness checklist for SaaS, healthtech, medtech, patient portals, cloud platforms, and service providers handling sensitive personal data.
Platforms that handle customer or patient data need more than basic cloud security. They need clear privacy controls, strong evidence, and a simple way to prove how personal data is protected in the cloud.
ISO/IEC 27018 gives guidance for protecting personally identifiable information, or PII, in public cloud services when the cloud provider acts as a PII processor. The current ISO/IEC 27018:2025 edition is designed around PII protection in public cloud environments and is based on ISO/IEC 27002:2022 guidance.
Quick Snapshot
| Checklist Area | What to Confirm |
|---|---|
| Data Scope | Customer data, patient data, account records, support tickets, backups, logs, exports, and integrations. |
| Privacy Roles | Who is the controller, processor, sub-processor, system owner, and data owner. |
| Key Controls | Consent support, purpose limitation, access control, encryption, deletion, breach response, logging, and vendor oversight. |
| Evidence Needed | Data inventory, privacy notices, contracts, access reviews, deletion records, encryption proof, vendor reviews, and incident records. |
| Outcome | A clear ISO 27018 readiness checklist that helps prove cloud privacy controls are designed, assigned, and operating. |
Introduction
Customer and patient data changes the security conversation.
A normal SaaS platform may already need strong access control, logging, vendor management, and incident response.
But once the platform handles sensitive personal information, healthcare records, appointment details, claims data, intake forms, support tickets, uploaded documents, or patient identifiers, the bar gets higher.
- Buyers want proof.
- Healthcare clients want confidence.
- Auditors want evidence.
- Privacy teams want clear responsibility.
- Regulators expect personal data to be handled with care.
That is where ISO 27018 becomes useful.
ISO 27018 helps cloud platforms organize privacy controls for personal data processed in public cloud environments. It does not replace privacy law. It does not replace healthcare compliance. It helps create a practical control structure that supports trust, contracts, audits, and customer due diligence.
This checklist is written for SaaS, healthtech, medtech, patient portals, cloud platforms, and service providers that handle customer or patient data.
Need Help With ISO 27018 Readiness?
Canadian Cyber helps SaaS and healthcare platforms map ISO 27018 controls, organize privacy evidence, review cloud vendors, and prepare customer-ready trust documentation.
Why ISO 27018 Matters for Customer and Patient Data
ISO 27018 matters because cloud privacy is not only about where data is stored.
It is about how data is collected, used, accessed, retained, deleted, disclosed, monitored, and protected. For platforms handling customer or patient data, the hard questions usually sound like this:
- Who can access patient records?
- Where is customer data stored?
- Which vendors process personal data?
- How is data deleted when a customer leaves?
- Are support staff access actions logged?
- Can administrators export sensitive data?
- How are privacy incidents handled?
- Are sub-processors reviewed?
- Can the platform prove encryption is enabled?
- Are backups covered by retention and deletion rules?
ISO 27018 helps turn those questions into a control checklist.
Common High-Risk Data Types
| Data Type | Why It Matters |
|---|---|
| Patient identifiers | May link directly to a person’s care, appointment, or health record. |
| Medical notes or forms | Often sensitive and highly regulated. |
| Customer account data | Can expose identity, billing, or usage patterns. |
| Uploaded documents | May contain hidden personal or health information. |
| Support tickets | Often include screenshots, names, emails, IDs, or health context. |
| API payloads | May move personal data between systems. |
| Logs and metadata | Can expose user activity, location, device, or account details. |
| Backups and exports | Often forgotten during deletion and retention reviews. |
The goal is simple: know where personal data lives, who touches it, and what proves it is protected.
The ISO 27018 Readiness Checklist
Use this checklist before a customer review, ISO audit, healthcare vendor assessment, privacy review, or security questionnaire.
1. Define the Personal Data in Scope
Start with a clear data inventory.
Do not write policies first. First, understand what personal data your platform actually processes.
What to Check
| Question | Evidence to Collect |
|---|---|
| What customer or patient data is collected? | Data inventory |
| Where is it stored? | System and storage map |
| How does it move through the platform? | Data flow diagram |
| Which teams can access it? | Access matrix |
| Which vendors process it? | Sub-processor register |
| How long is it retained? | Retention schedule |
| How is it deleted? | Deletion workflow |
Practical Tip:
Include hidden data locations: logs, backups, support tickets, analytics tools, email notifications, admin exports, data warehouses, and testing environments. Many privacy gaps are not in the main database. They are in the places teams forget to map.
2. Confirm Privacy Roles and Responsibilities
ISO 27018 readiness depends on role clarity.
Your team needs to know whether your platform acts as a processor, sub-processor, service provider, or controller in each context.
This is especially important for patient data because one platform may support clinics, employers, insurers, labs, healthcare providers, or other SaaS companies.
Privacy Responsibility Table
| Role | What to Define |
|---|---|
| Customer / Client | Usually decides why personal data is processed. |
| Platform Provider | Usually processes data on behalf of the customer. |
| Sub-processor | Vendor that supports hosting, analytics, support, monitoring, or storage. |
| Data Owner | Internal person responsible for the data set. |
| System Owner | Internal person responsible for the platform or tool. |
| Privacy Contact | Person responsible for privacy requests and escalations. |
| Security Contact | Person responsible for technical control evidence. |
Evidence auditors and buyers like:
- role and responsibility matrix
- data processing agreement
- sub-processor list
- privacy escalation process
- security ownership map
- vendor owner register
Need Role Clarity Before a Customer Review?
Canadian Cyber can help map privacy and security responsibilities across your platform, vendors, and cloud environment.
Map My Privacy Responsibilities
View Canadian Cyber Services
3. Limit Processing to Approved Purposes
Customer and patient data should not be used casually.
Your platform should define why data is processed and make sure internal teams do not use it outside those approved purposes.
| Requirement Area | Practical Check |
|---|---|
| Purpose limitation | Is each data use tied to a business or service purpose? |
| Internal access | Can staff only access data for approved work? |
| Analytics use | Is personal data minimized or de-identified where possible? |
| Product testing | Is real patient or customer data restricted in test environments? |
| AI or automation | Is personal data use reviewed before new processing begins? |
| Support access | Is access tied to a ticket, request, or approved need? |
Strong evidence includes:
- data processing purpose register
- privacy review for new features
- support access procedure
- test data policy
- approval record for new data uses
- customer-facing privacy terms
4. Keep Customer and Patient Data Separated
For SaaS and health platforms, data separation is a trust issue.
Customers want confidence that one client cannot access another client’s records. Patients expect their data to be protected from unauthorized viewing.
| Area | Evidence |
|---|---|
| Tenant separation | Architecture diagram. |
| Role-based access | Permission model. |
| Database access | Row-level access or schema separation explanation. |
| Object storage | Bucket or container permission review. |
| Admin access | Privileged access logs. |
| Support access | Ticket-linked access record. |
| Testing | Tenant isolation test evidence. |
You do not always need one database per customer. You do need a clear, tested, and evidenced model that shows how customer or patient data is separated.
5. Enforce Strong Access Control
Access control is one of the highest-impact parts of ISO 27018 readiness.
If staff, contractors, developers, or vendors can access customer or patient data too easily, trust breaks quickly.
Access Control Checklist
| Control | Evidence Needed |
|---|---|
| MFA for all privileged users | MFA policy or report. |
| SSO where possible | Identity provider configuration. |
| Least privilege roles | Role matrix. |
| Quarterly access reviews | Completed review record. |
| Joiner, mover, leaver process | Onboarding and offboarding samples. |
| Contractor access expiry | Contractor access register. |
| Break-glass control | Break-glass account review. |
| Support access logging | Ticket and audit log sample. |
High-intent buyer question: “Can your team prove who accessed our data, why they accessed it, and whether that access was approved?”
6. Encrypt Data in Storage, Transit, and Backups
Encryption is expected. But saying “we use encryption” is not enough.
You need to prove where encryption is enabled and how keys are managed.
Encryption Evidence Table
| Area | What to Prove |
|---|---|
| Data in transit | TLS configuration. |
| Databases | Encryption at rest setting. |
| Object storage | Storage encryption setting. |
| Backups | Backup encryption proof. |
| Key management | KMS or key management configuration. |
| Key access | Key admin access review. |
| Rotation | Key rotation policy or evidence. |
| Secrets | Secrets manager usage proof. |
Practical Tip: Do not forget exports. CSV exports, reports, file downloads, and backup snapshots often create privacy risk if they are not controlled.
7. Control Data Retention and Deletion
Retention and deletion are where many platforms fail privacy reviews.
Customer or patient data may be deleted from the application but still remain in logs, backups, exports, support tickets, or analytics tools.
Retention and Deletion Checklist
| Question | Evidence |
|---|---|
| Is there a retention schedule? | Retention policy. |
| Are customer deletion requests tracked? | Deletion ticket. |
| Are backups covered? | Backup retention rules. |
| Are logs covered? | Log retention settings. |
| Are support tickets covered? | Support data retention rule. |
| Are exports controlled? | Export procedure. |
| Is deletion verified? | Deletion completion record. |
Common gap: The application has a delete button, but the company cannot prove what happens to data in downstream systems.
8. Manage Sub-Processors and Vendors
Cloud platforms rarely process personal data alone.
They rely on hosting providers, email services, analytics tools, monitoring platforms, ticketing systems, payment processors, identity tools, and support vendors.
For patient data, this becomes even more sensitive.
Vendor Checklist
| Vendor Question | Evidence |
|---|---|
| Does the vendor process personal data? | Vendor register. |
| Does it process patient data? | Data classification field. |
| Is the vendor critical? | Vendor risk rating. |
| Is assurance reviewed? | SOC 2, ISO certificate, or security review. |
| Is there a contract or DPA? | Contract record. |
| Is the vendor approved? | Approval decision. |
| Is the vendor reviewed regularly? | Review date and owner. |
| Is there an exit plan? | Exit or contingency note. |
A folder full of SOC 2 reports is not enough. You need a decision trail showing who reviewed the vendor, what data it handles, what risks were accepted, what conditions apply, and when the next review is due.
9. Log Access and Monitor Activity
For platforms handling customer or patient data, logging is not optional.
You need to know what happened, when it happened, who did it, and whether anything looked suspicious.
Logging Checklist
| Log Area | What to Capture |
|---|---|
| User login | Successful and failed logins. |
| Admin access | Privileged actions. |
| Patient or customer record access | View, edit, export, delete. |
| API activity | Client ID, endpoint, result, rate limit events. |
| Support access | Staff access tied to support tickets. |
| Vendor access | Third-party admin or support activity. |
| Security alerts | Suspicious access, impossible travel, bulk export. |
| Data export | Who exported what and when. |
Evidence auditors trust:
- log source inventory
- retention settings
- sample audit log
- monthly log review
- alert-to-ticket sample
- incident escalation record
- access review sign-off
Good logs are not just collected. They are reviewed and acted on.
10. Make Privacy Incidents Reportable and Traceable
Privacy incidents need clear handling.
A privacy incident may involve unauthorized access, accidental disclosure, wrong-recipient email, exposed storage, lost device, vendor incident, excessive access, or data sent to the wrong customer.
Incident Response Checklist
| Requirement Area | Evidence |
|---|---|
| Privacy incident definition | Incident response plan. |
| Escalation path | Privacy and security contact list. |
| Triage process | Incident severity matrix. |
| Customer notification process | Notification procedure. |
| Regulator support process | Legal or privacy escalation notes. |
| Vendor incident handling | Vendor escalation workflow. |
| Lessons learned | Post-incident review template. |
| Testing | Tabletop exercise record. |
High-impact control: Run a privacy incident tabletop.
Use a realistic scenario, such as a support employee accessing the wrong patient record, a vendor notifying you of unauthorized access, a database export shared with the wrong customer, or a cloud storage bucket exposing uploaded intake forms.
11. Support Data Subject and Customer Requests
Platforms handling personal data need a way to support privacy requests.
Depending on contracts and laws, this may include access, correction, deletion, export, restriction, or investigation support.
Your platform may not respond directly to the individual if your customer is the controller. But you still need a process to support your customer.
Request Support Checklist
| Request Type | What to Have |
|---|---|
| Access request | Process to locate relevant data. |
| Correction request | Workflow to update records. |
| Deletion request | Deletion and verification steps. |
| Export request | Controlled export process. |
| Investigation request | Audit log retrieval process. |
| Customer support request | Intake and tracking process. |
Evidence to keep:
- request workflow
- sample ticket
- response timeline
- approval record
- export or deletion proof
- customer communication sample
12. Protect Support, Admin, and Engineering Workflows
Many privacy failures happen outside the main product.
Support teams use tickets. Engineers use logs. Admins use dashboards. Customer success teams view account records. Developers troubleshoot production issues.
These workflows need controls.
Operational Privacy Checklist
| Workflow | Control |
|---|---|
| Support ticket review | Limit sensitive data in tickets. |
| Production troubleshooting | Require approved access. |
| Developer access | Restrict direct database access. |
| Screenshots | Redact patient or customer identifiers. |
| Logs | Avoid secrets and sensitive payloads. |
| Admin dashboard | Log privileged actions. |
| Data exports | Require approval for bulk export. |
| Test environments | Use synthetic or masked data. |
Create a “minimum necessary access” rule for support and operations. Staff should only access the customer or patient data needed to resolve the task.
13. Prove Privacy by Design in Product Changes
Privacy should not be reviewed only after launch.
New features can introduce new data collection, new integrations, new analytics, new exports, or new AI processing.
Product Change Checklist
| Question | Evidence |
|---|---|
| Does the feature collect new personal data? | Privacy review checklist. |
| Does it involve patient data? | Data classification review. |
| Does it create a new vendor dependency? | Vendor review. |
| Does it change data retention? | Updated retention record. |
| Does it create new logs or exports? | Logging and export review. |
| Does it affect user consent or notice? | Privacy notice update. |
| Does it require security testing? | Test record. |
Strong evidence includes:
- privacy impact review
- secure design review
- change approval
- data flow update
- release record
- customer notice update
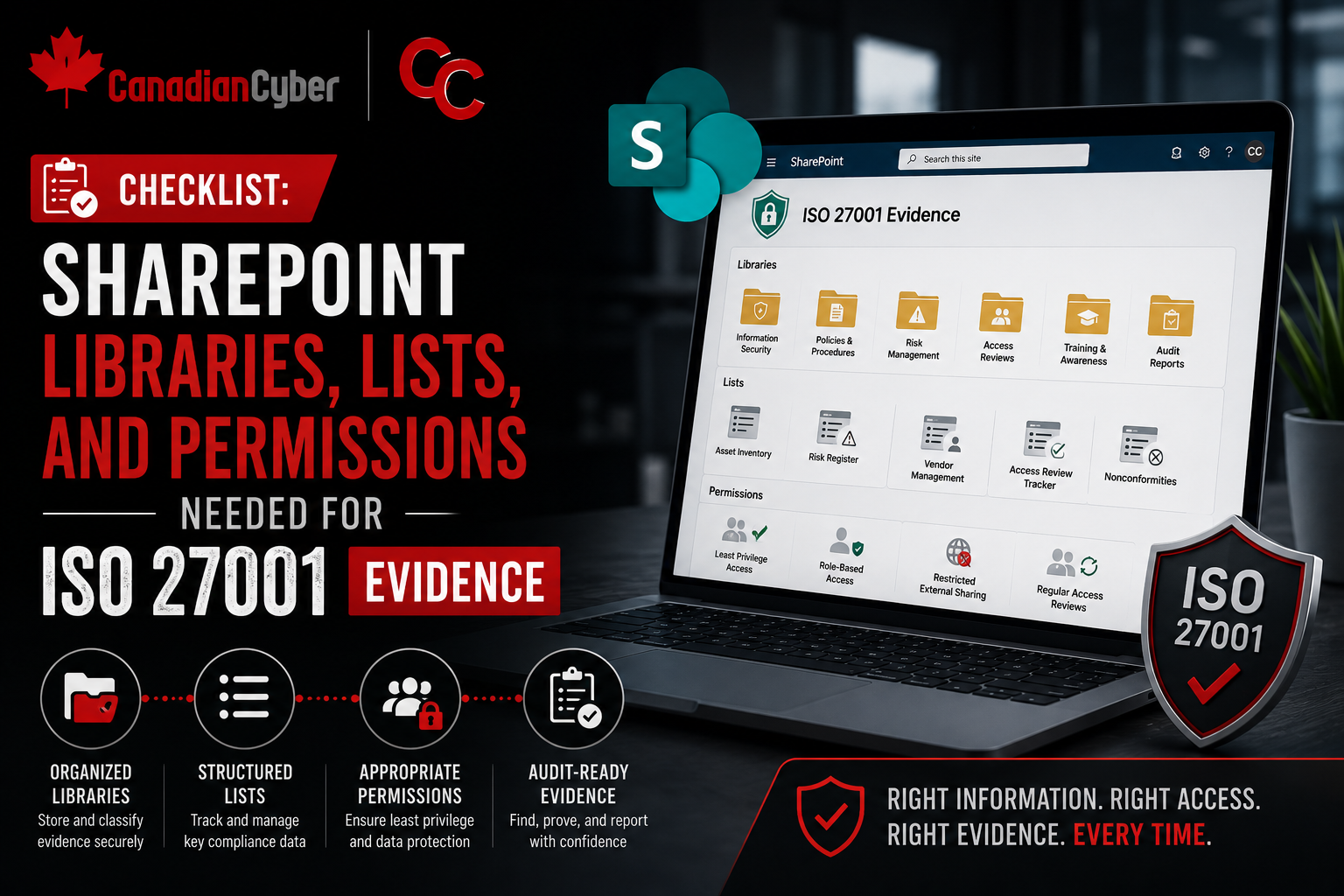
ISO 27018 Evidence Pack
A good ISO 27018 evidence pack should be simple, current, and easy to defend.
Recommended Evidence Pack Structure
| Folder / Section | What to Include |
|---|---|
| 01 Data Inventory | Data map, data flow, system list. |
| 02 Roles and Contracts | Responsibility matrix, DPA, sub-processor list. |
| 03 Access Control | MFA proof, access reviews, role matrix. |
| 04 Encryption and Keys | Encryption settings, KMS evidence, key access review. |
| 05 Retention and Deletion | Retention schedule, deletion tickets, backup retention. |
| 06 Logging and Monitoring | Log inventory, retention proof, alert samples. |
| 07 Vendor Management | Vendor reviews, assurance records, approval decisions. |
| 08 Incident Response | IR plan, privacy incident tabletop, incident records. |
| 09 Product Privacy Reviews | Privacy by design reviews, feature assessments. |
| 10 Customer Request Support | Request workflows and sample evidence. |
Want a Cleaner ISO 27018 Evidence Pack?
Canadian Cyber can organize your privacy and cloud evidence in SharePoint so customer reviews, audits, and healthcare vendor assessments are easier to answer.
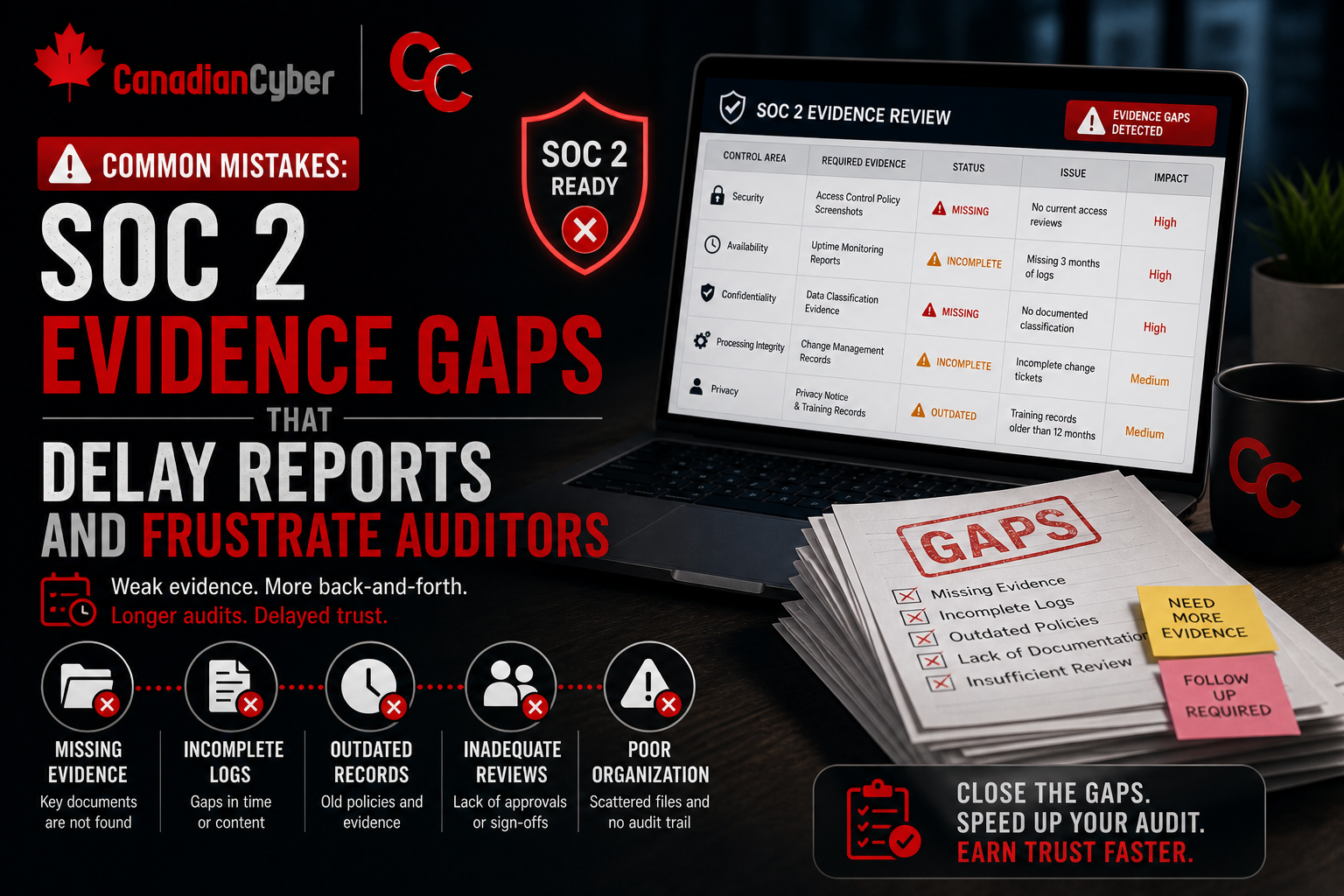
Common Mistakes to Avoid
- Mistake 1: Treating ISO 27018 like a policy checklist. Policies help, but buyers want proof that privacy controls actually operate.
- Mistake 2: Forgetting support tickets and logs. Customer and patient data often appears in tickets, logs, screenshots, and exports.
- Mistake 3: Assuming the cloud provider covers everything. Cloud provider assurance does not prove your access controls, deletion process, tenant model, or support workflows are working.
- Mistake 4: Weak sub-processor tracking. If a vendor processes personal or patient data, it needs ownership, review, approval, and monitoring.
- Mistake 5: No deletion evidence. Many platforms say data can be deleted but cannot prove the deletion path across systems.
- Mistake 6: Logging without review. Logs are weak evidence if nobody reviews them or turns alerts into action.
- Mistake 7: Using real patient data in testing. This creates avoidable risk and is hard to defend during privacy reviews.
- Mistake 8: No privacy incident rehearsal. A plan that has never been tested often fails under pressure.
What Buyers and Auditors Usually Want to See
For platforms handling customer or patient data, buyers and auditors usually want proof that:
- personal data is inventoried
- patient data is identified and protected
- sub-processors are known
- access is limited and reviewed
- encryption is enabled
- logs are collected and reviewed
- deletion is controlled
- support access is monitored
- privacy incidents are handled quickly
- contracts define responsibilities
- evidence is current and retrievable
They do not want vague assurances. They want clear evidence.
Canadian Cyber’s Take
At Canadian Cyber, we often see platforms with strong technical teams but weak privacy evidence.
The product may be secure. The cloud may be well configured. The team may care deeply about patient or customer trust.
But when a healthcare client, enterprise buyer, auditor, or privacy reviewer asks for proof, the evidence is scattered.
That creates friction.
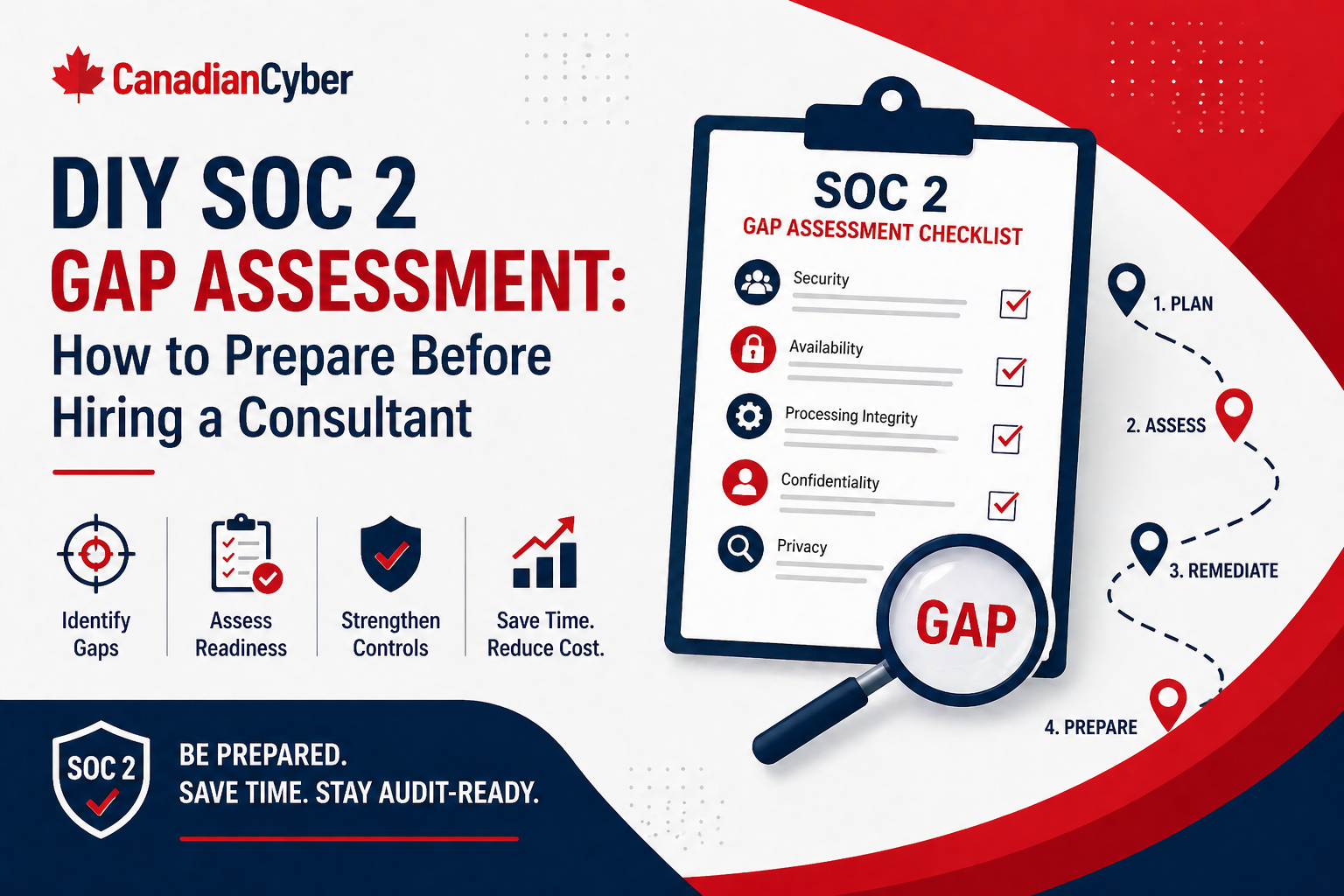
ISO 27018 readiness works best when teams treat privacy controls as an operating system, not a one-time document project.
The strongest platforms can show what data they process, where it lives, who can access it, which vendors support it, how it is protected, how it is deleted, and how incidents are handled. That is what turns privacy from a sales blocker into a trust advantage.
Takeaway
ISO 27018 is valuable for platforms that handle customer or patient data because it gives cloud privacy work a practical structure.
Start with your data inventory. Then:
- map privacy roles
- limit processing
- review access
- protect tenant separation
- encrypt sensitive data
- control retention and deletion
- manage sub-processors
- log access
- test privacy incident response
- support customer requests
- build privacy review into product changes
The goal is not to create a bigger compliance binder. The goal is to prove that personal data is protected, governed, and handled with care across your cloud platform.
How Canadian Cyber Can Help
Canadian Cyber helps SaaS, healthtech, and cloud platforms prepare for ISO 27018-aligned privacy reviews.
- ISO 27018 readiness reviews
- privacy evidence pack design
- customer and patient data inventory
- cloud privacy control mapping
- sub-processor reviews
- SharePoint evidence workspace setup
- access review workflows
- privacy incident tabletop exercises
- retention and deletion evidence design
- vendor risk management
- ISO 27001, ISO 27017, and ISO 27018 alignment
- vCISO support for privacy and cloud security governance
Stay Connected With Canadian Cyber
Follow Canadian Cyber for practical guidance on ISO 27018, cloud privacy, SaaS security, healthcare data protection, audit readiness, and vCISO support.