Multi-Cloud SaaS • ISO 27017 • Shared Responsibility • Evidence Mapping
DIY Guide: Mapping ISO 27017 Controls to Multi-Cloud SaaS Environments
Turn shared responsibility, cloud configuration, logging, access, and vendor evidence into a practical ISO 27017 control map your SaaS team can actually use.
ISO 27017 control mapping gets harder when your SaaS environment runs across more than one cloud. One product may rely on AWS for production workloads, Microsoft Entra ID for identity, Google Cloud for analytics, GitHub for source control, Datadog for monitoring, and Zendesk for support workflows.
ISO/IEC 27017:2015 provides cloud-specific guidance for information security controls, including guidance for both cloud service providers and cloud service customers. It extends ISO/IEC 27002-style control implementation with cloud-specific considerations.
Quick Snapshot
| Mapping Area | What to Check |
|---|---|
| Cloud Scope | AWS, Azure, GCP, SaaS platforms, CI/CD, identity, logging, storage, and customer-facing services. |
| Shared Responsibility | What your cloud provider manages, what your SaaS team manages, and where responsibility is shared. |
| Core Control Areas | Access, tenant separation, VM/container hardening, logging, network controls, supplier risk, incident response, and secure configuration. |
| Evidence Needed | Architecture diagrams, cloud configuration exports, access reviews, logging reviews, vendor assurance, change records, and policy links. |
| Outcome | A clear ISO 27017 control map that connects cloud risks, owners, systems, evidence, and remediation priorities. |
Introduction
Multi-cloud SaaS environments are powerful.
They let teams use the best parts of different platforms. But that flexibility creates a compliance problem.
When a customer, auditor, or enterprise buyer asks how your cloud environment is controlled, the answer cannot be “AWS handles that” or “Azure is certified.”
In a multi-cloud SaaS environment, ISO 27017 mapping needs to show:
- which cloud services are in scope
- who owns each control
- which provider controls you inherit
- which controls your team must operate
- where evidence lives
- how controls work consistently across clouds
- how customer data is protected across the full service
A DIY ISO 27017 control map helps your team organize that picture before the audit, customer review, or cloud security assessment becomes stressful.
Need Help Mapping ISO 27017 Across Clouds?
Canadian Cyber can help SaaS teams turn scattered cloud controls into a practical ISO 27017 evidence map across AWS, Azure, GCP, Microsoft 365, GitHub, CI/CD, and SaaS tools.
Why ISO 27017 Mapping Is Different in Multi-Cloud SaaS
ISO 27017 is not just another policy exercise. It is about proving that cloud-specific security controls are understood, assigned, implemented, and evidenced.
That becomes harder in multi-cloud environments because control ownership is split across multiple layers. For example:
- AWS may secure the underlying infrastructure.
- Your DevOps team may configure IAM, security groups, encryption, and logging.
- Azure may handle identity services.
- GitHub may control code repositories and deployment workflows.
- Datadog may collect monitoring data.
- A support platform may store customer tickets and attachments.
The risk is not that one provider is weak. The risk is that no one has mapped how all these services work together.
Common Multi-Cloud Mapping Problems
| Problem | Why It Matters |
|---|---|
| Cloud controls are documented separately | Auditors cannot see the full SaaS environment clearly. |
| Shared responsibility is assumed, not mapped | Control gaps appear between provider and customer responsibilities. |
| Evidence is stored by platform, not by control | Reviews take longer and evidence requests become harder. |
| Cloud owners are unclear | Remediation gets delayed when nobody owns the gap. |
| Logging varies by cloud | Incident response and audit trails become inconsistent. |
| Vendor assurance is collected but not linked | SOC reports and ISO certificates do not prove your own control operation. |
Step 1: Define the SaaS Service in Scope
Start with the service your customers actually rely on.
Do not begin by listing every tool your company uses. Start with the product, platform, or service that buyers expect to be secure.
Your scope should include:
- production application
- customer-facing APIs
- cloud infrastructure
- databases and storage
- identity provider
- CI/CD pipeline
- source code repositories
- logging and monitoring platforms
- support and ticketing tools
- admin access paths
- customer data stores
- critical SaaS vendors
Simple Scope Table
| System / Platform | Role in SaaS Service | Cloud / Vendor | Handles Customer Data? | Owner |
|---|---|---|---|---|
| Production app | Hosts customer platform | AWS | Yes | Engineering |
| Identity provider | SSO and admin login | Microsoft Entra ID | Yes | IT / Security |
| Data warehouse | Analytics and reporting | GCP | Yes | Data Team |
| Source control | Code repository | GitHub | No direct customer data | Engineering |
| Monitoring | Logs and alerts | Datadog | Possible metadata | DevOps |
| Support platform | Customer tickets | Zendesk | Yes | Customer Ops |
Not Sure What Belongs in Scope?
Canadian Cyber helps SaaS teams define practical cloud security scope before they over-map, over-document, or miss critical systems.
Step 2: Build a Shared Responsibility Matrix
ISO 27017 mapping should make responsibility clear.
In cloud environments, some controls are handled by the provider, some by the SaaS company, and some are shared. A shared responsibility matrix helps you avoid vague ownership.
| Control Area | Cloud Provider Responsibility | SaaS Company Responsibility | Evidence Needed |
|---|---|---|---|
| Physical data center security | Provider controls facilities | Review provider assurance reports | SOC 2 / ISO certificate review |
| Cloud IAM | Provides IAM capability | Configure roles, MFA, least privilege, reviews | IAM export, access review record |
| Encryption | Provides encryption services | Enable encryption, manage keys, review settings | KMS config, encryption evidence |
| Logging | Provides logging features | Enable logs, retain logs, review alerts | Logging config, review sign-off |
| Network security | Provides network controls | Configure segmentation, firewalls, private access | Security group / firewall export |
| Backup and recovery | Provides backup tools | Configure backups and test restores | Backup settings, restore test evidence |
Step 3: Map ISO 27017 Controls to Real Cloud Areas
Do not map controls only to policy names. Map them to real systems, real owners, and real evidence.
A practical control map should include:
- control reference
- cloud security topic
- applicable systems
- control owner
- implementation summary
- evidence location
- testing or review cadence
- gap status
| ISO 27017 Area | SaaS Control Topic | Multi-Cloud Example | Owner | Evidence |
|---|---|---|---|---|
| Shared roles and responsibilities | Responsibility mapping | AWS, Azure, GCP, SaaS vendors | Security Lead | Shared responsibility matrix |
| Customer asset return / removal | Data deletion and offboarding | Customer data deletion workflow | Product / Engineering | Deletion procedure, ticket sample |
| Virtual environment protection | Tenant and workload separation | VPCs, projects, subscriptions, namespaces | DevOps | Architecture diagram, config export |
| Administrative operations | Privileged access control | Cloud admin roles, break-glass accounts | IT / Security | Access review, MFA proof |
| Cloud customer monitoring | Logging and monitoring | CloudTrail, Azure Monitor, GCP logs, SIEM | Security / DevOps | Log config, alert review |
| Network alignment | Cloud network segmentation | VPCs, VNets, private endpoints, firewall rules | Cloud Lead | Network diagrams, firewall export |
This moves your map from “we follow ISO 27017” to “here is how this control works in our actual SaaS environment.”
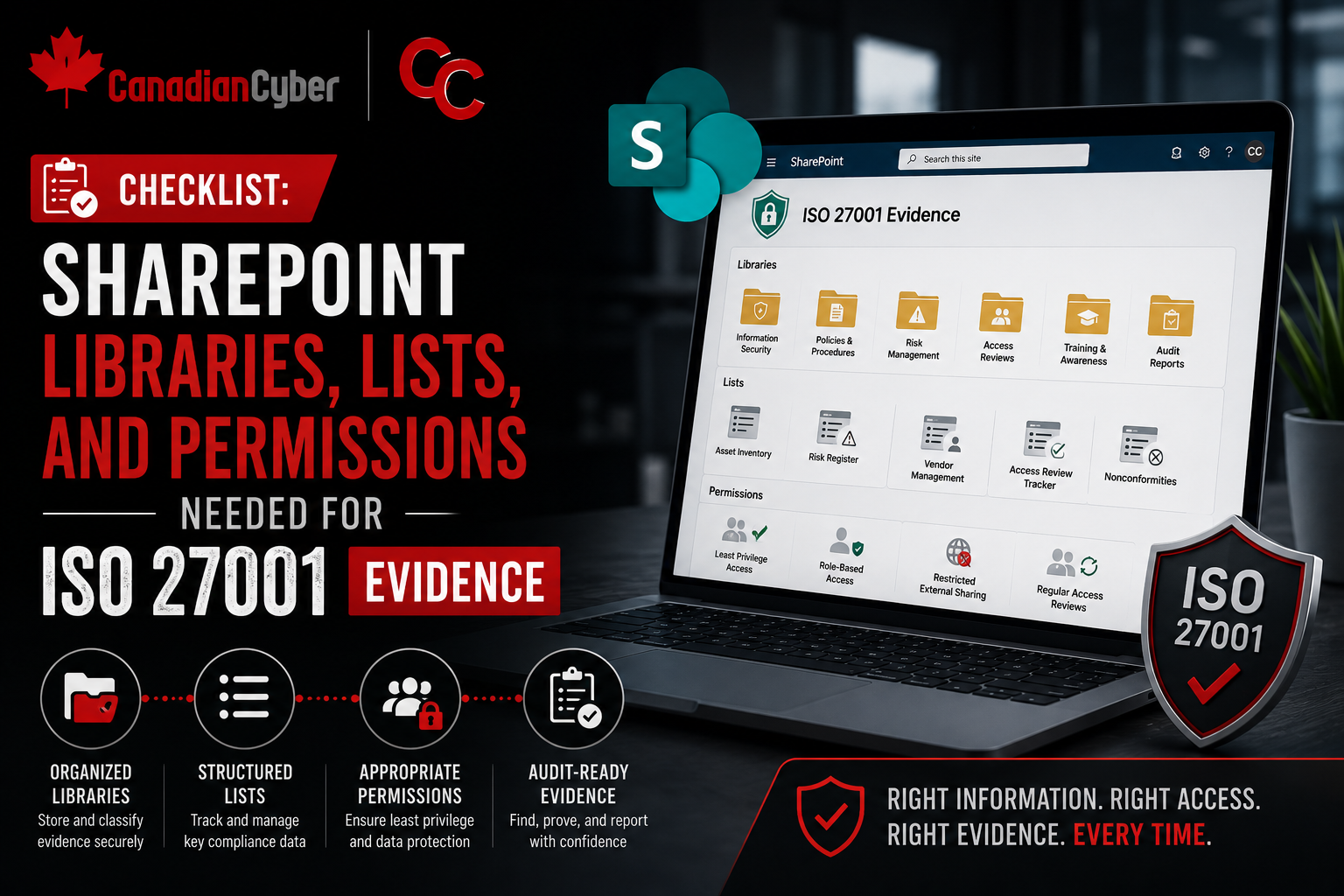
Step 4: Group Evidence by Control, Not by Cloud
A common mistake is storing evidence by platform only. That creates folders like AWS, Azure, GCP, GitHub, Datadog, and Zendesk.
That may help engineers, but it does not help auditors. Auditors and buyers usually ask by control area, not by cloud platform.
A better evidence model groups evidence like this:
- Access Control
- Logging and Monitoring
- Network Security
- Encryption and Key Management
- Backup and Recovery
- Vendor Assurance
- Incident Response
- Change Management
- Tenant Separation
- Secure Configuration
Evidence Pack Example
| Evidence Pack | What to Include |
|---|---|
| Access Control | MFA proof, admin list, quarterly access review, privileged access approval. |
| Logging and Monitoring | Log sources, retention settings, alert rules, monthly review record. |
| Encryption | Storage encryption screenshots, KMS settings, key rotation evidence. |
| Network Security | Firewall rules, private endpoint config, segmentation diagram. |
| Vendor Assurance | SOC 2 reports, ISO certificates, vendor risk reviews. |
| Change Management | Pull requests, deployment records, approval evidence. |
| Backup and Recovery | Backup configuration, restore test record, recovery notes. |
| Incident Response | IR plan, tabletop exercise, incident log, escalation record. |
Make Evidence Easier to Review
Canadian Cyber helps teams build SharePoint evidence packs mapped to ISO 27017 control areas, cloud services, owners, and review periods.
Step 5: Map Identity and Access Across Every Cloud
Access control is one of the most important parts of ISO 27017 mapping.
In multi-cloud SaaS, access is rarely in one place. You may need to map access across:
- Microsoft Entra ID
- AWS IAM
- Azure RBAC
- GCP IAM
- GitHub
- Kubernetes
- CI/CD tooling
- databases
- support tools
- monitoring tools
Access Mapping Checklist
| Question | Evidence to Collect |
|---|---|
| Is MFA enforced for cloud admins? | MFA policy screenshot or report. |
| Are privileged roles limited? | Admin role export. |
| Are access reviews performed? | Quarterly review record. |
| Are service accounts owned? | Service account register. |
| Are break-glass accounts controlled? | Break-glass policy and test record. |
| Are leavers removed from all cloud tools? | Offboarding ticket sample. |
| Are contractor accounts time-bound? | Contractor access list and expiry proof. |
Step 6: Map Tenant Separation and Data Isolation
For SaaS companies, tenant separation is one of the highest-value ISO 27017 topics.
Buyers want to know whether one customer can access another customer’s data. Your mapping should cover:
- application-level tenant controls
- database separation model
- object storage permissions
- API authorization checks
- admin support access
- logging of privileged customer access
- test coverage for tenant isolation
- data export controls
| Area | Evidence |
|---|---|
| Architecture | SaaS tenancy diagram. |
| Authorization | Role and permission model. |
| Database controls | Row-level access logic or schema separation notes. |
| Storage controls | Bucket/container permissions. |
| Testing | Tenant isolation test results. |
| Admin access | Support access approval and logging. |
| Monitoring | Alerts for unusual access patterns. |
This does not mean every SaaS company needs a separate database per customer. It means your control map must explain how your chosen tenancy model is protected, tested, and monitored.
Step 7: Map Logging and Monitoring Across Clouds
Logging is where multi-cloud environments often get messy.
AWS logs may go one place. Azure logs may go somewhere else. GCP logs may have different retention. SaaS vendor logs may only be available through exports or APIs.
Your ISO 27017 map should show:
- what logs are collected
- which systems generate them
- where they are retained
- who reviews them
- which alerts exist
- how incidents become tickets
- how long logs are kept
- whether logs contain sensitive data
Logging Map Example
| Log Source | What It Captures | Destination | Retention | Review Cadence | Owner |
|---|---|---|---|---|---|
| AWS CloudTrail | Admin and API activity | SIEM | 1 year | Monthly | Security |
| Azure Activity Logs | Subscription and admin activity | SIEM | 1 year | Monthly | IT |
| GCP Audit Logs | Project and service activity | SIEM | 1 year | Monthly | DevOps |
| GitHub Audit Log | Repository and admin activity | Export / SIEM | 1 year | Monthly | Engineering |
| SaaS App Logs | Customer and admin events | Application logging platform | 1 year | Monthly | Product Security |
Evidence auditors trust usually shows operation over time, not just screenshots.
Good logging evidence includes a log source inventory, retention settings, alert rules, monthly review sign-off, sample alert ticket, incident escalation record, and log access control evidence.
Step 8: Map Cloud Configuration and Hardening
Cloud misconfiguration is one of the most common SaaS risks.
Your ISO 27017 map should show how cloud resources are configured securely and how configuration drift is detected. Focus on:
- secure baselines
- public exposure controls
- storage permissions
- encryption settings
- network segmentation
- container and VM hardening
- Kubernetes security
- infrastructure as code review
- configuration scanning
- remediation tracking
| Control Topic | Evidence |
|---|---|
| Secure baseline | Cloud baseline standard. |
| Infrastructure as code | Pull request and approval sample. |
| Public storage prevention | Storage permission report. |
| Encryption | Encryption setting export. |
| Container hardening | Image scan results. |
| Kubernetes controls | Cluster configuration review. |
| Drift detection | CSPM or cloud security scan report. |
| Remediation | Ticket showing fix and validation. |
A policy saying “cloud systems must be secure” is weak. A baseline, scan report, remediation ticket, and review record are much stronger.
Step 9: Map Vendors and Cloud Dependencies
Multi-cloud SaaS environments rely heavily on vendors. Some vendors are infrastructure providers. Others are SaaS platforms that store customer data, support security operations, or affect availability.
Your ISO 27017 map should include a vendor control section.
| Vendor | Service Role | Data Handled | Criticality | Assurance Evidence | Owner |
|---|---|---|---|---|---|
| AWS | Production hosting | Customer data | High | SOC 2 / ISO reports | Cloud Lead |
| Microsoft | Identity / M365 | Employee and admin identity | High | Trust Center evidence | IT |
| GitHub | Source control | Source code | High | SOC 2 report | Engineering |
| Datadog | Monitoring | Logs and metadata | Medium / High | Security review | DevOps |
| Zendesk | Support tickets | Customer data | Medium / High | Vendor assessment | Customer Ops |
Vendor evidence to collect includes:
- vendor register
- risk rating
- data handled
- service owner
- SOC 2 or ISO report
- contractual security terms
- review date
- approval decision
- renewal review timing
- exit or contingency notes
Vendor governance is not about collecting PDFs. It is about proving that third-party risk is understood, reviewed, accepted, and monitored.
Step 10: Create a Gap Register
Once your mapping is done, you will almost always find gaps.
That is the point. A gap register helps turn control mapping into action.
ISO 27017 Gap Register Example
| Gap | Risk | Owner | Priority | Evidence Needed |
|---|---|---|---|---|
| No centralized cloud log review | Suspicious activity may not be detected across clouds | Security Lead | High | Log review record and alert workflow |
| GCP IAM not included in access review | Excessive access may remain active | DevOps | High | Quarterly GCP access review |
| Vendor reviews not linked to ISO 27017 map | Supplier risk evidence is incomplete | Compliance Lead | Medium | Vendor register and review records |
| Tenant isolation testing not documented | Customer data separation is not provable | Engineering | High | Tenant isolation test evidence |
| Cloud network diagrams outdated | Auditor cannot validate segmentation | Cloud Lead | Medium | Updated architecture and network diagrams |
| Backup restore testing inconsistent | Recovery capability is not proven | DevOps | High | Restore test record |
Need a Prioritized Cloud Control Roadmap?
Canadian Cyber can review your ISO 27017 control map and identify which gaps are audit-blocking, buyer-facing, or lower priority.
What Good ISO 27017 Mapping Looks Like
A strong ISO 27017 control map should answer five questions clearly.
| Question | What the Map Should Show |
|---|---|
| 1. What cloud services are in scope? | Systems, platforms, environments, and SaaS tools that support the customer-facing service. |
| 2. Who owns each control? | A named role or team owner for each control. |
| 3. What does the cloud provider handle? | Provider responsibility through shared responsibility models, assurance reports, and vendor review evidence. |
| 4. What does your SaaS team operate? | Configuration, access control, monitoring, change management, review records, and incident readiness. |
| 5. Where is the evidence? | Every mapped control should link to evidence that proves the control is designed and operating. |
Common Mistakes to Avoid
- Mapping only to policies: Policies matter, but auditors want to see cloud configuration and operating evidence.
- Assuming provider certification covers your environment: A cloud provider’s certification does not prove your IAM, logging, network, or tenant controls are configured correctly.
- Treating each cloud separately: Multi-cloud evidence needs a common control view, not disconnected evidence piles.
- Ignoring SaaS vendors: Support tools, monitoring platforms, source control, CI/CD, and analytics systems may all affect the SaaS control environment.
- Forgetting review cadence: A control that is configured once but never reviewed becomes weak evidence over time.
- Not assigning owners: If no one owns the control, no one owns the evidence.
- Overbuilding the first map: Start with critical systems and high-value control areas. Expand as the program matures.
What Auditors and Buyers Usually Want to See
Auditors and enterprise buyers usually care less about how fancy the control map looks and more about whether it proves real control.
They want to see that:
- cloud scope is clear
- shared responsibility is understood
- admin access is reviewed
- tenant separation is designed and tested
- logs are collected and reviewed
- critical vendors are assessed
- cloud configurations are monitored
- incidents can be investigated
- evidence is current
- owners know their responsibilities
The strongest control maps are simple, traceable, and evidence-backed.
Canadian Cyber’s Take
At Canadian Cyber, we often see SaaS teams struggle with ISO 27017 because their cloud environment grew faster than their control structure.
That is normal.
Most teams adopt AWS, Azure, GCP, GitHub, monitoring tools, CI/CD systems, and SaaS platforms because they need to move quickly. The problem appears later, when customers and auditors ask how all those systems are governed together.
The answer is not more paperwork.
The answer is a practical control map.
A good ISO 27017 map shows what is in scope, who owns each control, what the provider handles, what your team operates, where evidence lives, and which gaps need attention first.
Takeaway
DIY ISO 27017 control mapping is one of the most useful things a multi-cloud SaaS team can do before an audit, customer security review, or cloud security assessment.
Start with scope. Build the shared responsibility matrix. Map controls to real systems. Organize evidence by control area. Review access, logging, tenant separation, configuration, vendors, and incident readiness.
The goal is not to create a perfect spreadsheet. The goal is to prove that your SaaS cloud environment is understood, owned, reviewed, and controlled.
How Canadian Cyber Can Help
Canadian Cyber helps SaaS companies map ISO 27017 controls across real-world cloud environments.
- ISO 27017 control mapping
- multi-cloud scope definition
- shared responsibility matrices
- cloud evidence pack design
- SharePoint ISMS setup
- vendor risk mapping
- access review workflows
- logging and monitoring evidence
- tenant separation evidence
- cloud configuration review
- ISO 27001 and ISO 27017 readiness
- vCISO support for SaaS security governance
Stay Connected With Canadian Cyber
Follow Canadian Cyber for practical guidance on ISO 27017, ISO 27001, cloud security, SaaS governance, audit readiness, and vCISO support.