SOC 2 • Evidence Gaps • Audit Readiness
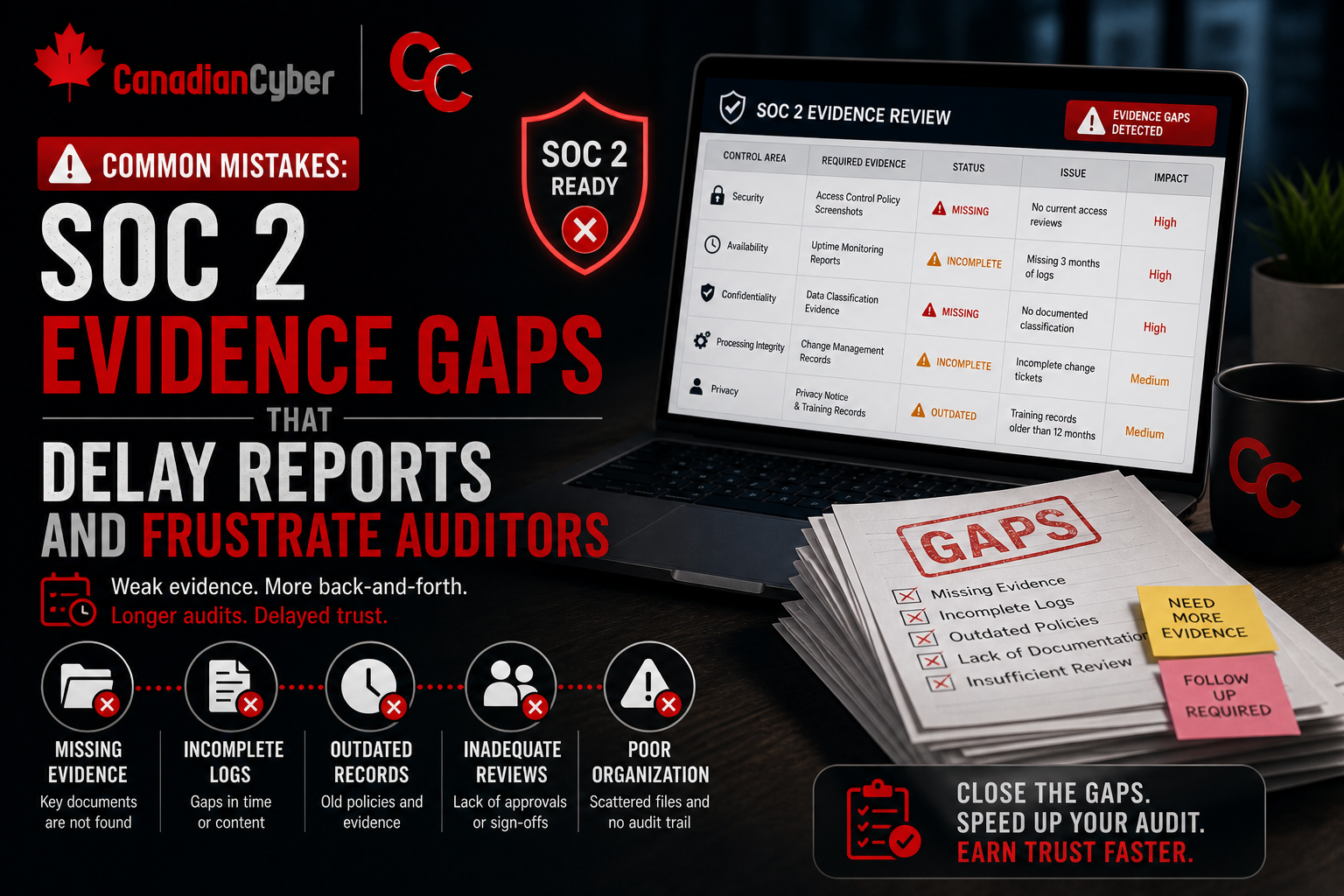
Common Mistakes: SOC 2 Evidence Gaps That Delay Reports and Frustrate Auditors
Why unclear, incomplete, or poorly organized evidence can slow down SOC 2 reports even when controls are operating.
Introduction
SOC 2 delays usually do not happen because the company has no controls.
They happen because the evidence does not prove the controls clearly enough.
- A control owner says access was reviewed, but the report is missing the review date.
- A vendor was assessed, but there is no approval record.
- A backup exists, but no restore test was documented.
- A policy was updated, but nobody can show who approved it.
This is where SOC 2 evidence gaps create frustration. In simpler terms: SOC 2 evidence needs to show what happened, when it happened, who did it, what was reviewed, and what action was taken.
Quick Snapshot
| Evidence Issue | Why It Delays SOC 2 |
|---|---|
| Missing dates | Auditors cannot confirm whether the activity happened during the audit period. |
| Missing owners | It is unclear who performed, reviewed, or approved the control activity. |
| Incomplete samples | The evidence does not fully prove the control operated as expected. |
| Screenshots without context | Auditors cannot easily understand what the screenshot proves or where it came from. |
Why Evidence Gaps Delay SOC 2 Reports
Auditors need evidence that supports the control being tested.
If evidence is unclear, incomplete, outdated, or hard to trace, the auditor has to ask follow-up questions.
That creates delays. Common delay triggers include:
- missing dates
- missing owners
- incomplete samples
- screenshots without context
- evidence outside the audit period
- unclear approval records
- missing follow-up proof
- inconsistent documentation across systems
The control may be operating, but if the evidence does not prove it, the audit slows down.
Need Help Cleaning Up SOC 2 Evidence?
Canadian Cyber helps SaaS teams organize audit-ready evidence, clean up gaps, and reduce painful follow-up requests from auditors.
Common SOC 2 Evidence Gaps
| Mistake | Why It Frustrates Auditors | Better Evidence |
|---|---|---|
| 1. Access reviews without follow-up proof | An access review is not complete just because someone looked at a user list. Auditors need to see review decisions and follow-up actions. | Reviewed user list, reviewer name, review date, approval, removal tickets, and retained access justification. |
| 2. Offboarding evidence that only shows HR closure | An HR termination record does not prove access was removed from critical systems. | Termination ticket, identity provider deactivation, SaaS access removal, device return or wipe record, and date access was disabled. |
| 3. Vendor reviews with no risk decision | A vendor SOC 2 report alone does not prove your company evaluated the vendor. | Vendor risk rating, evidence reviewed, reviewer, review date, approval decision, follow-up actions, and next review date. |
| 4. Backup evidence without restore testing | Backups prove very little if recovery capability is never tested. | Backup success report, restore test record, system tested, test date, result, issues found, and corrective actions. |
| 5. Change management evidence missing approval | A deployment record shows a change happened. It does not always show that the change was controlled. | Pull request review, approval record, test results, deployment log, and emergency change notes if applicable. |
| 6. Policy evidence with no approval history | Policies need governance. Auditors need to see who owns, approved, and reviewed them. | Policy owner, approval date, approver, current version, review schedule, and archived prior versions. |
| 7. Security training records missing new hires | SOC 2 evidence should show onboarding training and recurring training. | Annual completion report, new-hire training records, overdue reminders, completion dates, and targeted retraining if applicable. |
| 8. Incident response plan with no test or record | A plan is stronger when the team can prove it has been used or tested. | Incident response plan, tabletop exercise record, incident or near-miss log, lessons learned, and corrective actions. |
| 9. Screenshots without context | A screenshot without date, source, owner, or control reference is weak evidence. | Source system, date captured, control area, period covered, owner, and reviewer status. |
| 10. Evidence outside the audit period | SOC 2 testing depends heavily on the period being reviewed. | Track period covered for every item, such as Q1 2026, January to March 2026, or audit start and end dates. |
Want Cleaner Evidence Before Audit Fieldwork?
We help SaaS companies build evidence folders, assign control owners, track audit requests, and prepare proof before auditors start asking follow-up questions.
A Simple SOC 2 Evidence Quality Checklist
Before submitting evidence, ask:
| Question | Yes / No |
|---|---|
| Does it match the control being tested? | ☐ Yes ☐ No |
| Is it within the audit period? | ☐ Yes ☐ No |
| Does it show a date? | ☐ Yes ☐ No |
| Does it show who performed or approved the action? | ☐ Yes ☐ No |
| Does it show what was reviewed? | ☐ Yes ☐ No |
| Does it show follow-up if issues were found? | ☐ Yes ☐ No |
| Is the evidence stored in the right place? | ☐ Yes ☐ No |
| Can someone outside the team understand it? | ☐ Yes ☐ No |
If the answer is “no” to several of these, the evidence probably needs cleanup.
Canadian Cyber’s Take
At Canadian Cyber, we often see SOC 2 projects delayed by evidence quality, not control absence.
The company may be doing the right work.
But the evidence does not clearly show:
- ownership
- timing
- review
- approval
- follow-up
- operating proof
Evidence design should start early. Do not wait until audit fieldwork to organize proof.
Takeaway
SOC 2 evidence gaps delay reports because they force auditors to ask for clarification, replacement samples, or additional proof.
The most common gaps include:
- incomplete access reviews
- weak offboarding proof
- vendor reviews without decisions
- backups without restore tests
- changes without approval evidence
- policies without approval history
- training records missing new hires
- incident plans without testing
- screenshots without context
- evidence outside the audit period
SOC 2 is not only about having controls. It is about proving those controls operated clearly, consistently, and within the audit period.
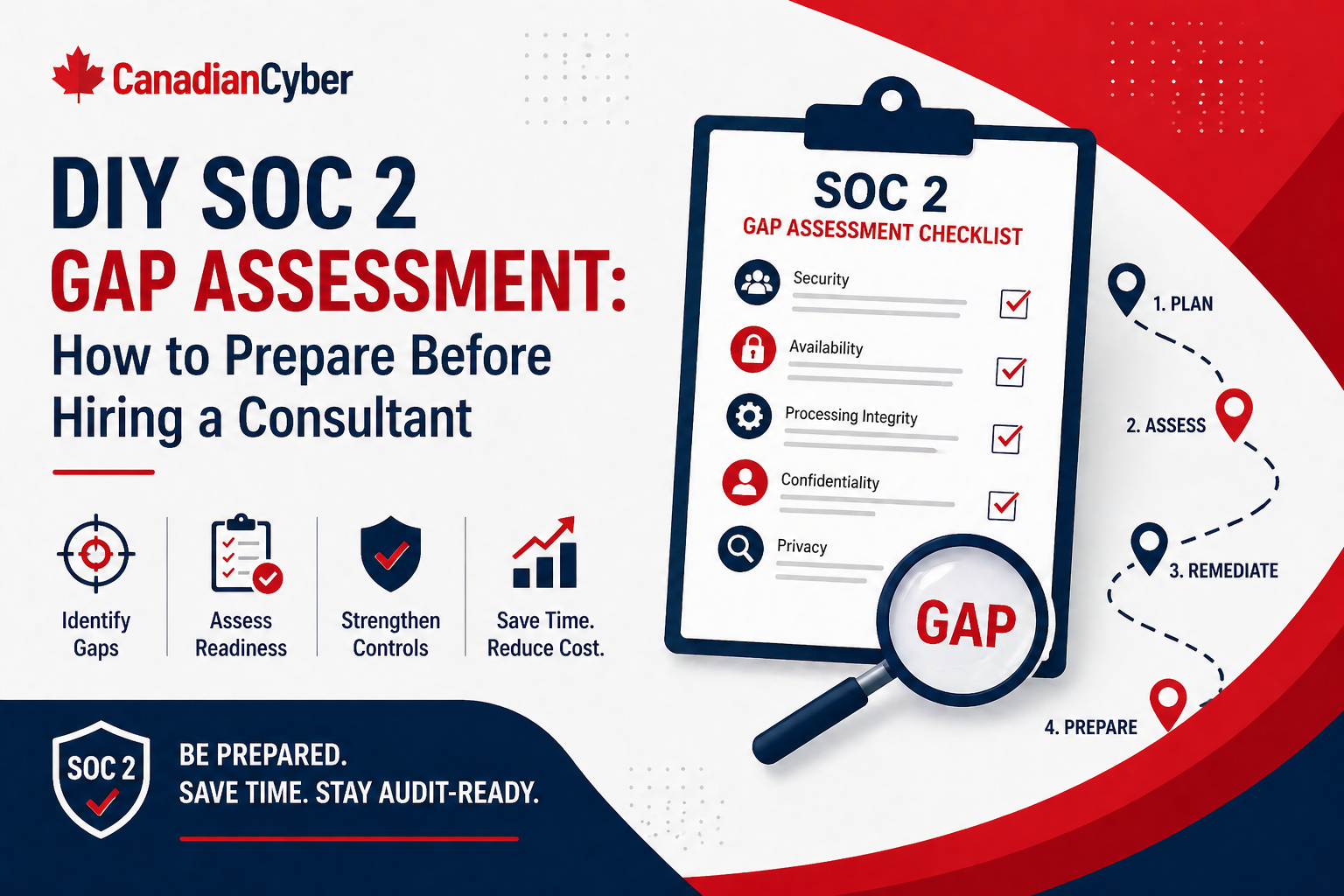
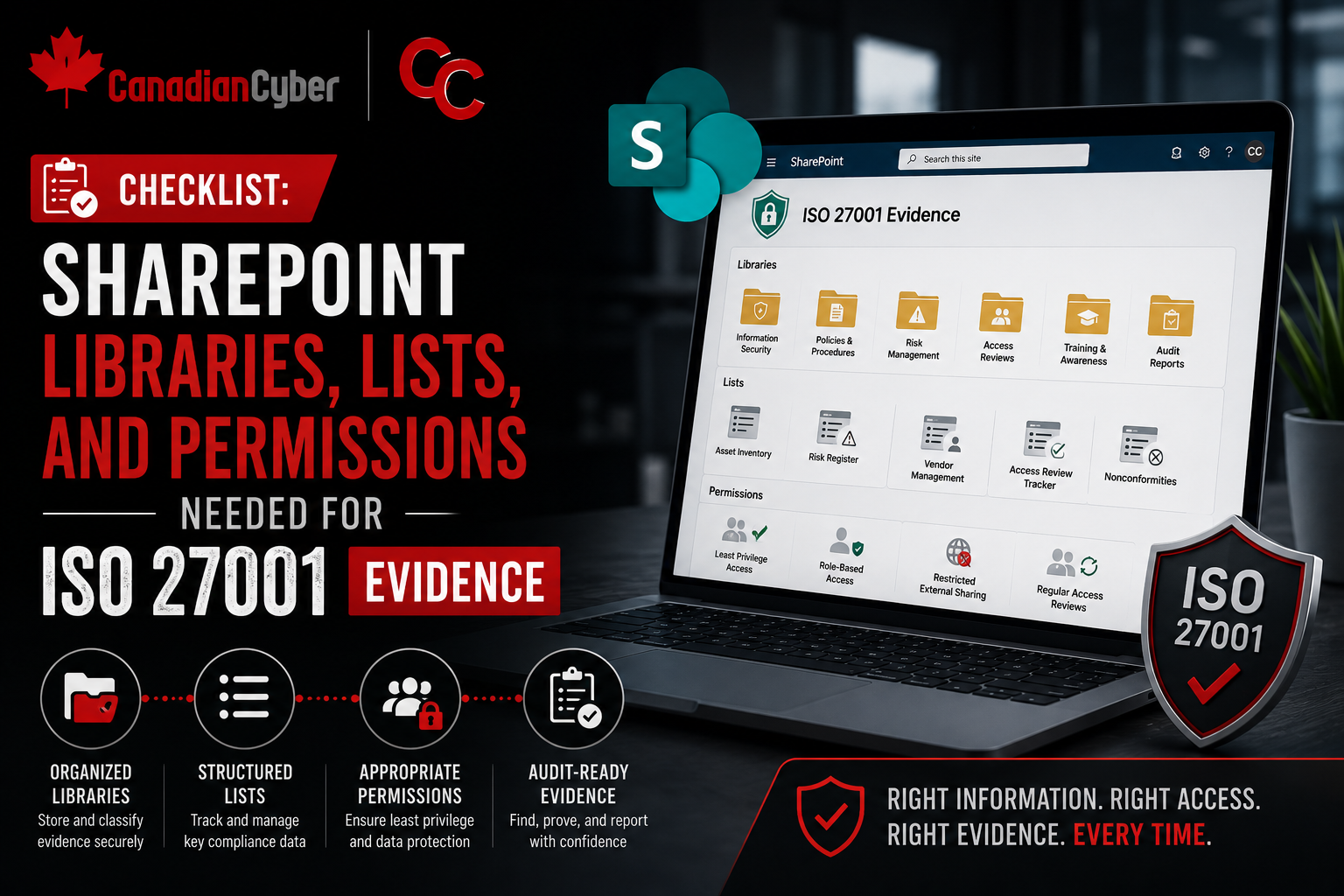
How Canadian Cyber Can Help
At Canadian Cyber, we help SaaS companies clean up SOC 2 evidence before auditors start asking painful follow-up questions.
- SOC 2 evidence readiness reviews
- SharePoint evidence library setup
- access and vendor evidence cleanup
- control owner workflows
- audit request tracking
- corrective action management
- vCISO guidance for continuous compliance
If evidence gaps are slowing your SOC 2 report, we can help you build a cleaner process before audit delays grow.
Stay Connected With Canadian Cyber
Follow Canadian Cyber for practical guidance on SOC 2, audit readiness, evidence management, SaaS security, and vCISO support.