SOC 2 • SaaS Buyers • 2026 Readiness
Checklist: SOC 2 Controls SaaS Buyers Expect to See in 2026
A practical buyer-ready checklist for SaaS companies preparing for SOC 2 audits, procurement reviews, and enterprise security questionnaires.
Introduction
SaaS buyers in 2026 are not just asking, “Do you have SOC 2?”
They are asking better questions.
They want to know whether your controls actually protect their data, support availability, manage access, govern vendors, and reduce risk across the systems that matter.
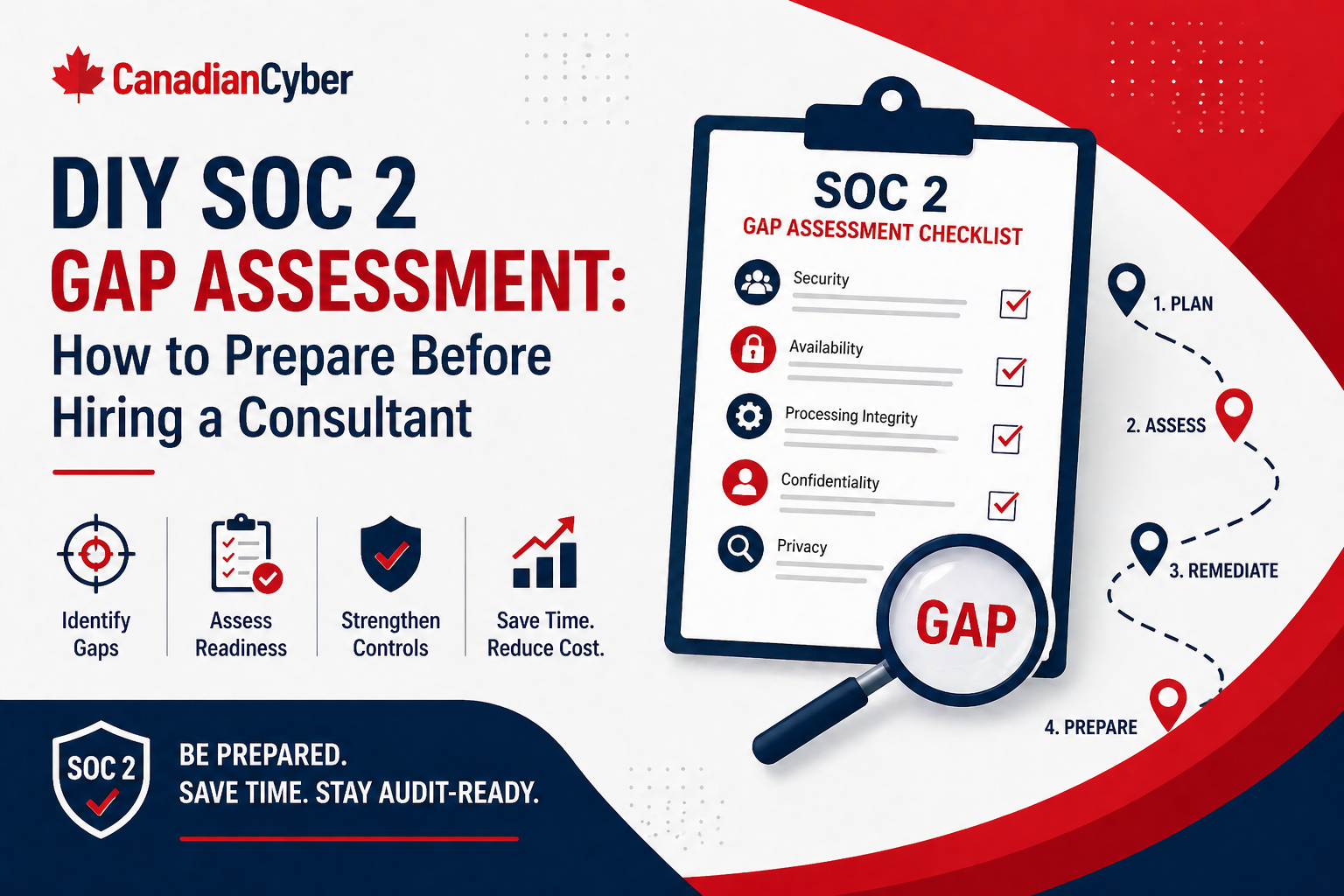
SOC 2 reports cover controls relevant to Security, Availability, Processing Integrity, Confidentiality, and Privacy, depending on the selected scope. In simpler terms: buyers do not only want the badge. They want confidence that your SaaS company is controlled, responsive, and ready to handle enterprise data.
Quick Snapshot
| Category | Detail |
|---|---|
| Topic | SOC 2 controls SaaS buyers expect in 2026 |
| Audience | SaaS startups, cloud service providers, procurement-ready vendors, and security teams |
| Goal | Prepare controls that stand up to audits and buyer security reviews |
| Key Insight | SOC 2 is not just about passing an audit. It is about proving operational trust. |
Why This Checklist Matters
For SaaS companies, SOC 2 has become a trust signal.
But buyers are getting more mature.
They often ask for:
- the SOC 2 report
- scope details
- covered systems
- exceptions or findings
- security questionnaire answers
- evidence of remediation
- data handling explanations
- vendor and subprocessor details
- incident response readiness
Your controls need to be more than audit-friendly. They need to be buyer-friendly.
Need Help Preparing for SOC 2 Buyer Reviews?
Canadian Cyber helps SaaS companies build SOC 2 controls, evidence libraries, and buyer-ready security responses that stand up to audits and procurement reviews.
1. Access Control
Buyers expect strong access governance. They want to see:
- MFA on critical systems
- SSO where possible
- least privilege
- onboarding and offboarding controls
- privileged access reviews
- production access restrictions
- contractor access management
- removal of stale accounts
Evidence buyers may ask for:
Access review records, MFA enforcement reports, admin role exports, offboarding tickets, and privileged access approval records.
2. Change Management
SaaS buyers want confidence that production changes are controlled. They expect:
- pull request reviews
- testing before deployment
- deployment records
- approval for high-risk changes
- emergency change process
- rollback capability
- source control protections
Buyer tip: For API-first or multi-tenant SaaS, buyers may also ask how authorization, tenant isolation, and data exposure risks are reviewed before release.
3. Vendor and Subprocessor Management
Buyers know your vendors can affect their risk. They expect:
- vendor inventory
- risk ranking
- security reviews for critical vendors
- SOC 2 or ISO evidence where available
- contracts or DPAs where needed
- subprocessor tracking
- reassessment schedule
Evidence buyers may ask for: vendor register, completed vendor reviews, subprocessor list, security reports from critical vendors, and next review dates.
4. Incident Response
Buyers want to know you can respond when something goes wrong. They expect:
- incident response plan
- severity levels
- escalation process
- customer notification workflow
- evidence preservation
- post-incident review
- corrective action tracking
- tabletop testing
A plan that has never been tested is weaker than a plan supported by a tabletop exercise.
Want Buyer-Ready SOC 2 Evidence?
We help SaaS teams organize evidence for access, vendors, incidents, change management, monitoring, and procurement questionnaires.
5–12. Additional SOC 2 Control Areas Buyers Review
Beyond access, change management, vendors, and incident response, buyers commonly review these control areas:
| Control Area | What Buyers Expect | Evidence Buyers May Ask For |
|---|---|---|
| Security Awareness | Onboarding training, annual awareness, phishing awareness, completion tracking, overdue follow-up, and role-based training. | Training reports, phishing simulation results, new-hire records, reminders, and retraining evidence. |
| Endpoint and Device Security | Managed laptops, disk encryption, endpoint protection, patching, screen locks, device inventory, remote wipe, and local admin restrictions. | Device inventory, encryption report, EDR coverage report, patch compliance report, and lost device procedure. |
| Logging and Monitoring | Centralized logs, admin activity logging, authentication logs, high-risk alerts, ownership, retention, and incident linkage. | Alert rules, logging configuration, sample security logs, dashboards, and alert investigation tickets. |
| Backup and Recovery | Backup coverage, backup monitoring, restore testing, recovery procedures, restricted access, retention rules, and recovery priorities. | Backup reports, restore test records, recovery runbooks, retention settings, and corrective actions from failed tests. |
| Risk Management | Risk register, owners, ratings, treatment actions, residual risk review, leadership visibility, and corrective actions tied to risks. | Risk register sample, risk treatment plan, management review notes, and corrective action tracker. |
| Data Protection and Confidentiality | Encryption in transit and at rest, data classification, access restrictions, secure deletion, retention rules, export controls, tenant segregation, and support access controls. | Encryption settings, data flow diagram, retention policy, deletion procedure, support access logs, and tenant isolation explanation. |
| Secure Development | Secure coding, code review, dependency management, vulnerability scanning, secrets management, security testing, and remediation tracking. | Secure development policy, code review samples, vulnerability scan results, remediation tickets, and secrets management controls. |
| Governance and Policies | Approved, current, and actively used policies for information security, access control, incident response, vendor management, change management, acceptable use, data handling, and backup recovery. | Approved policy library, approval dates, review dates, policy owner list, and version history. |
Practical 2026 Buyer-Ready Checklist
| Control Area | Buyer Expectation |
|---|---|
| Access | MFA, least privilege, access reviews |
| Change | Reviewed and tested production changes |
| Vendors | Critical vendor reviews and subprocessor visibility |
| Incidents | Tested response plan and escalation process |
| Awareness | Tracked training and follow-up |
| Endpoints | Managed, encrypted, protected devices |
| Monitoring | Logs, alerts, and investigation process |
| Backups | Tested recovery, not just configured backups |
| Risk | Risk register and treatment actions |
| Data Protection | Encryption, retention, segregation, support controls |
| Secure Development | Code review, scanning, secrets protection |
| Governance | Approved policies and review cycles |
Canadian Cyber’s Take
At Canadian Cyber, we often see SaaS companies think SOC 2 alone will answer every buyer question.
It helps, but buyers still want to understand the control story behind the report.
The strongest SaaS companies prepare for both:
- the audit
- and the procurement review that follows
That means building controls that are not only compliant, but easy to explain, evidence, and defend.
Takeaway
In 2026, SaaS buyers expect SOC 2 controls that prove real operational maturity.
The most important areas are:
- access control
- change management
- vendor risk
- incident response
- awareness training
- endpoint security
- logging and monitoring
- backup and recovery
- risk management
- data protection
- secure development
- governance
Buyers are not just asking whether you passed SOC 2. They are asking whether they can trust your SaaS platform with their data, operations, and customers.
How Canadian Cyber Can Help
At Canadian Cyber, we help SaaS companies prepare SOC 2 control environments that stand up to both audits and buyer security reviews.
- SOC 2 readiness assessments
- control gap reviews
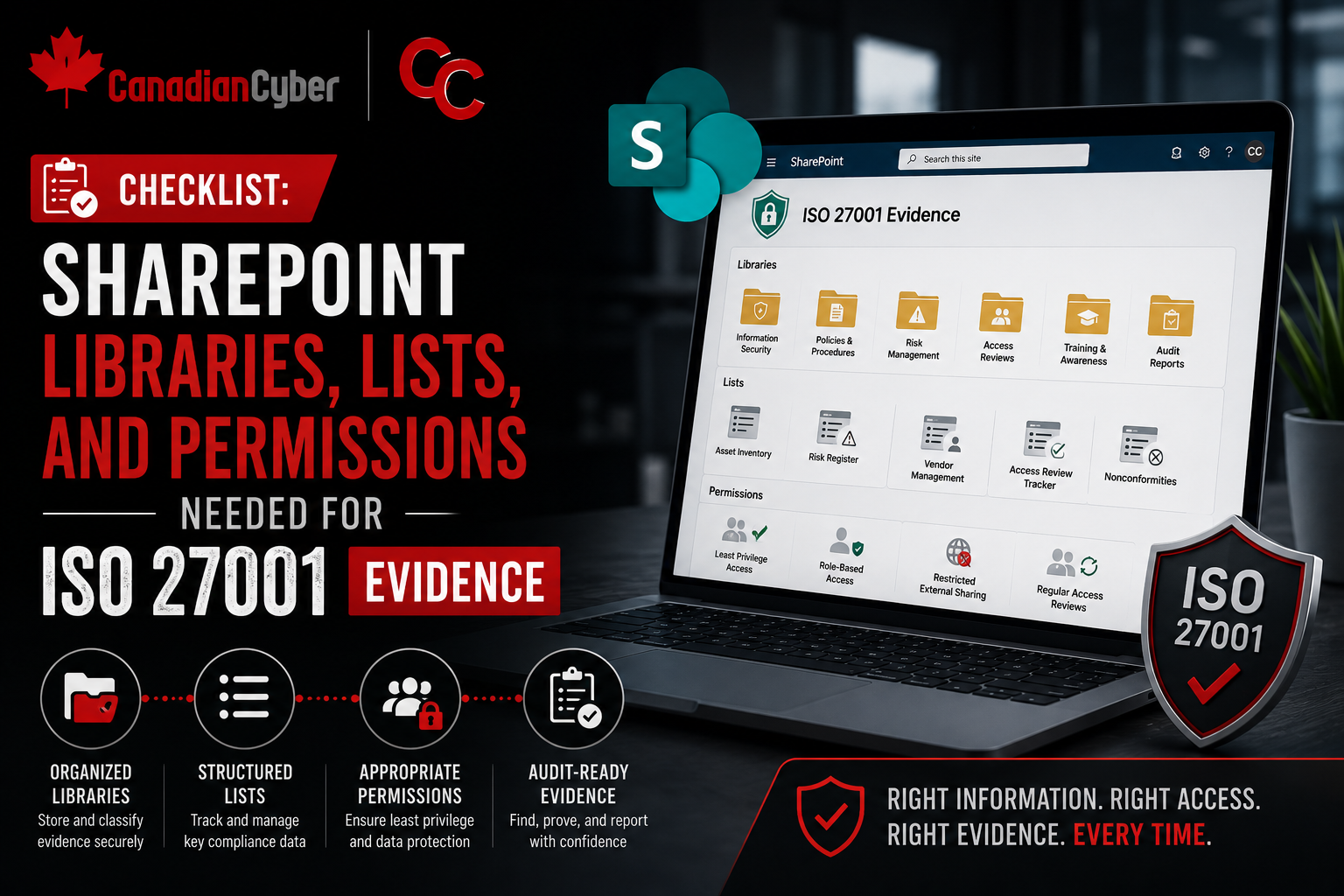
- evidence library setup
- access, vendor, and incident workflow design
- SaaS procurement readiness
- security questionnaire support
- vCISO guidance for buyer trust and audit readiness
If buyers are asking harder SOC 2 questions, we can help you build the controls and evidence needed to answer with confidence.
Stay Connected With Canadian Cyber
Follow Canadian Cyber for practical guidance on SOC 2, SaaS security, buyer readiness, audit preparation, and vCISO support.