Outsourced IT • Cybersecurity Ownership • vCISO • Risk Management • Strategic Leadership
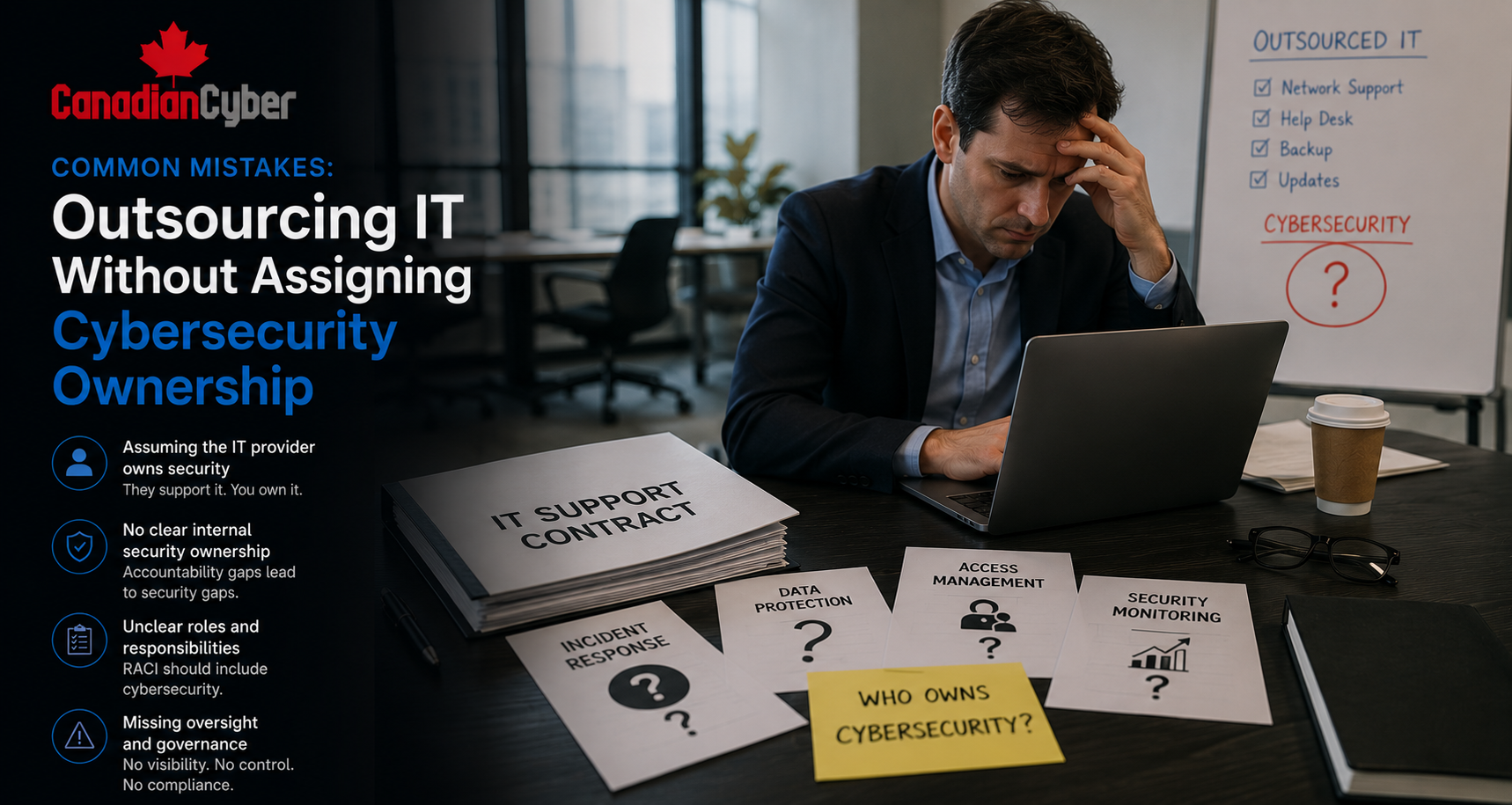
Common Mistakes: Outsourcing IT Without Assigning Cybersecurity Ownership
Outsourcing IT can improve daily support. But managed IT is not the same as cybersecurity ownership.
Quick Snapshot
| Mistake Area | What Usually Goes Wrong |
|---|---|
| IT Support | The MSP manages tickets, devices, and systems, but not business-level cyber risk. |
| Cybersecurity Ownership | No one owns risk decisions, the security roadmap, policies, or board reporting. |
| Incident Response | The IT provider may respond technically, but executive escalation is unclear. |
| Compliance | Evidence is scattered because no one owns ISO 27001, SOC 2, insurance, or customer requirements. |
| vCISO Role | A vCISO provides strategic leadership, governance, risk oversight, and executive-level cyber direction. |
Introduction
Many businesses outsource IT for good reasons.
They need help desk support, device management, Microsoft 365 administration, backups, patching, and network support.
A good managed IT provider can be valuable.
But there is a common mistake.
The business assumes that outsourcing IT also means cybersecurity is fully owned.
That assumption creates risk. An IT provider may manage systems, but the business still needs someone to own cyber risk, security priorities, vendor oversight, incident decisions, compliance evidence, and executive reporting.
Outsourced IT but No Clear Cyber Owner?
Canadian Cyber helps organizations add vCISO strategic leadership on top of managed IT, so cybersecurity risk, governance, compliance, and executive reporting are properly owned.
Why Outsourced IT Is Not the Same as Cybersecurity Ownership
Outsourced IT and cybersecurity leadership are related.
But they are not the same thing.
Managed IT usually focuses on operations. Cybersecurity ownership focuses on risk.
| Area | Managed IT Usually Handles | Cybersecurity Ownership Requires |
|---|---|---|
| Devices | Setup, support, patching, and troubleshooting. | Endpoint risk, policy, exceptions, and security reporting. |
| Microsoft 365 | User accounts, email, licensing, and basic admin. | Access governance, Conditional Access, audit logs, and risk review. |
| Backups | Backup configuration and monitoring. | Recovery strategy, restore testing, evidence, and business impact. |
| Incidents | Technical response support. | Executive escalation, legal coordination, and lessons learned. |
| Reporting | Ticket and service reports. | Cyber risk reporting for executives and the board. |
A business can have excellent IT support and still have weak cybersecurity governance.
Mistake 1: Assuming the MSP Owns Cyber Risk
This is the biggest mistake.
Many leaders assume the outsourced IT provider owns cybersecurity because the provider manages systems.
But cyber risk belongs to the business.
| Assumption | Reality |
|---|---|
| “Our IT provider handles security.” | They may handle technical controls, not business risk governance. |
| “They manage our systems, so they own the risk.” | Risk ownership remains with leadership. |
| “They will tell us what to do.” | They may recommend actions, but leadership must prioritize and approve. |
| “If something happens, they will handle it.” | They may handle technical response, but legal, client, and executive decisions still need ownership. |
During an audit, incident, insurance renewal, or customer review, the business must answer:
- Who owns cyber risk?
- Who approves security priorities?
- Who accepts residual risk?
- Who reports to leadership?
- Who decides incident notification?
Practical rule: You can outsource IT tasks. You cannot outsource accountability.
Mistake 2: Treating Cybersecurity as a Technical Support Issue
Cybersecurity is not only technical.
It affects revenue, trust, legal exposure, compliance, customer contracts, insurance, vendor decisions, and business continuity.
If cyber is treated only as an IT ticket category, important decisions get missed.
| Technical Issue | Business Risk Question |
|---|---|
| MFA is not enabled for all users. | Which accounts create the highest takeover risk? |
| Backups are configured. | Can we restore critical operations within business tolerance? |
| A vendor has admin access. | What data can the vendor access, and has that risk been accepted? |
| Logs are collected. | Who reviews them, and what happens when suspicious activity appears? |
If cyber discussions only happen inside IT tickets, the business is missing the leadership layer.
Mistake 3: No One Owns the Cybersecurity Roadmap
Without ownership, security becomes reactive.
The business responds to whatever is urgent:
- a customer questionnaire
- an insurance form
- a phishing scare
- a vendor recommendation
- an audit finding
- a board question
That is not a roadmap. That is reaction.
| Roadmap Area | Example Actions |
|---|---|
| Access Control | MFA, Conditional Access, access reviews, and offboarding. |
| Vendor Risk | Vendor register, risk ratings, and assurance reviews. |
| Incident Response | Plan update, tabletop, and escalation process. |
| Compliance | ISO 27001, SOC 2, cyber insurance, and customer evidence. |
| Governance | Board reporting, risk register, and management review. |
Need a Cybersecurity Roadmap on Top of Outsourced IT?
Canadian Cyber helps organizations turn managed IT activity into a risk-based cybersecurity roadmap with vCISO strategic leadership.
Mistake 4: No Clear Line Between MSP Duties and Business Duties
A managed IT contract may describe technical services.
But it may not define cybersecurity governance clearly.
This creates confusion, especially during audits, incidents, and customer reviews.
| Security Area | MSP / IT Provider | Business Owner | vCISO |
|---|---|---|---|
| User onboarding | Creates account. | Approves access. | Reviews process. |
| Access reviews | Provides user exports. | Reviews and approves access. | Designs review method. |
| Backups | Monitors backup jobs. | Defines recovery priorities. | Reviews restore testing evidence. |
| Incidents | Provides technical response. | Makes business decisions. | Leads playbook and escalation review. |
Practical rule: If ownership is not written down, it will fail under pressure.
Mistake 5: Security Reporting Is Just an IT Service Report
Many MSPs provide reports.
They may include tickets closed, patch status, backup success, device health, antivirus status, uptime, and alerts.
These reports are useful. But they are not the same as cyber risk reporting.
| IT Service Report | Cyber Risk Report |
|---|---|
| Tickets closed. | Top cyber risks. |
| Backup job status. | Recovery readiness. |
| Patch status. | Critical exposure and remediation SLA. |
| Tool activity. | Control health and risk reduction. |
Executives need to know:
- Are we more or less exposed than last quarter?
- What are our top cyber risks?
- Which controls are weak?
- Which risks need funding?
- Are we ready for an incident?
Mistake 6: Vendor Risk Falls Between IT, Procurement, and Leadership
Outsourced IT is only one vendor relationship.
Most businesses rely on many vendors, including cloud providers, payroll systems, HR platforms, finance tools, CRM systems, support platforms, email providers, and payment processors.
Each vendor can create cyber risk. But vendor risk often falls into a gap.
| Vendor Risk Question | Why It Matters |
|---|---|
| Does the vendor process sensitive data? | Determines risk level. |
| Is the vendor critical to operations? | Affects continuity planning. |
| Does the vendor have access to systems? | Creates access risk. |
| Who owns the vendor internally? | Assigns accountability. |
If a vendor can access your data or systems, someone must own that cyber risk.
Mistake 7: Incident Response Is Treated as the MSP’s Problem
During an incident, the MSP may be critical.
They may investigate systems, disable accounts, restore backups, review logs, isolate devices, and support containment.
But incidents are not only technical. They also involve business decisions.
| Decision | Who Should Be Involved |
|---|---|
| Is this a security incident? | Security, IT, and leadership. |
| Is customer data affected? | Privacy, legal, and business owner. |
| Do we notify clients? | Leadership, legal, and communications. |
| What corrective actions are required? | vCISO, IT, and control owners. |
The MSP may help fight the fire. The business still decides how to protect clients, operations, and reputation.
Mistake 8: Compliance Evidence Is Collected but Not Owned
Many businesses ask their MSP for audit evidence.
The MSP may provide screenshots, reports, ticket exports, patch summaries, backup status, and security tool evidence.
That helps. But compliance still needs ownership.
| Evidence Problem | Why It Hurts |
|---|---|
| Screenshots have no context. | Auditors may not know what they prove. |
| Evidence is not mapped to controls. | ISO 27001 or SOC 2 readiness suffers. |
| Reports are outdated. | Evidence may not cover the audit period. |
| Evidence is scattered. | Audit prep takes too long. |
Good evidence needs:
- owner
- date
- control mapping
- period covered
- review sign-off
- clear storage location
Mistake 9: Cyber Risk Acceptance Happens Silently
Every business accepts some cyber risk.
That is normal.
The problem is silent acceptance. This happens when risks are not fixed, not funded, not documented, and not formally approved.
| Risk Acceptance Field | Example |
| Risk | Legacy system cannot support MFA. |
| Reason | Replacement planned in six months. |
| Compensating Controls | Network restriction, monitoring, and limited users. |
| Approver | CEO / CTO. |
| Review Date | September 2026. |
If a cyber risk is not funded or fixed, it should be accepted intentionally. Not accidentally.
Cybersecurity Ownership Checklist
Use this checklist to test whether your outsourced IT model has clear cybersecurity ownership.
| Question | Yes / No |
|---|---|
| Do we have a named cyber risk owner inside the business? | |
| Do we know our top 5 cyber risks? | |
| Do we have a 90-day cybersecurity roadmap? | |
| Are MSP responsibilities clearly documented? | |
| Are access reviews performed and evidenced? | |
| Are vendors risk-rated and reviewed? | |
| Has incident response been tested? | |
| Does leadership receive cyber risk reporting? | |
| Is compliance evidence mapped to controls? |
If you answered “no” several times, the issue may not be your IT provider. The issue may be missing cybersecurity ownership.
What Good Looks Like
A strong outsourced IT model with cybersecurity ownership has:
- clear MSP responsibilities
- clear business responsibilities
- vCISO strategic leadership
- risk register
- security roadmap
- access review process
- vendor risk process
- incident response plan
- tabletop exercises
- backup restore evidence
- executive reporting
- compliance evidence packs
The MSP keeps systems running. The vCISO helps ensure cybersecurity is governed. Leadership owns the risk.
Canadian Cyber’s Take
At Canadian Cyber, we often see businesses with good managed IT support but weak cybersecurity ownership.
The IT provider may be doing useful work. Devices may be patched. Backups may be running. Tickets may be handled. Security tools may be deployed.
But leadership still does not have a clear view of cyber risk.
That is not always an MSP failure.
It is often a role clarity problem. Managed IT is not the same as strategic cybersecurity leadership. A vCISO fills that gap by helping the business define risk, set priorities, oversee vendors, prepare for incidents, organize evidence, and report to executives.
The best result is not MSP versus vCISO. It is MSP plus vCISO, with clear ownership.
Takeaway
Outsourcing IT is a smart move for many businesses.
But it does not remove the need for cybersecurity ownership.
If no one owns cyber risk, incident readiness, vendor oversight, compliance evidence, and executive reporting, the business may still be exposed.
The answer is not always another security tool.
The answer is often clearer ownership and vCISO strategic leadership.
Keep your managed IT provider focused on operational support. Use a vCISO to guide cybersecurity governance, risk, compliance, roadmap, and leadership reporting.
How Canadian Cyber Can Help
Canadian Cyber helps organizations add vCISO strategic leadership to outsourced IT environments.
- cybersecurity ownership reviews
- vCISO strategic leadership
- MSP responsibility mapping
- cyber risk registers
- 90-day security roadmaps
- executive cyber reporting
- vendor risk management
- incident response planning
- tabletop exercises
- ISO 27001 and SOC 2 readiness
- cyber insurance evidence
- customer security questionnaire support
Stay Connected With Canadian Cyber
Follow Canadian Cyber for practical guidance on vCISO services, outsourced IT, cyber risk, ISO 27001, SOC 2, vendor risk, and security governance.