SOC 2 • AI Policy Drafting • Human Review Evidence • SaaS Compliance • Audit Readiness
AI Wrote Our SOC 2 Policies — Then the Auditor Asked for “Human Review Evidence”
AI can help draft SOC 2 policies fast. But it cannot approve them, prove they match your real operations, or show that leadership reviewed and accepted them.
Quick Snapshot
| Area | What SaaS Teams Need to Know |
|---|---|
| AI-Generated Policies | Useful for first drafts, but not enough for audit readiness. |
| Auditor Concern | Policies must be reviewed, approved, and aligned with actual controls. |
| Human Review Evidence | Proof that a real owner checked, updated, approved, and accepted the policy. |
| Common Gap | Teams upload AI-written policies with no review trail, no owner, and no operating evidence. |
| Outcome | A simple workflow for using AI without creating weak SOC 2 evidence. |
Introduction
The founder was proud.
They had used AI to draft the full SOC 2 policy set in one afternoon.
- Access Control Policy
- Incident Response Policy
- Vendor Management Policy
- Risk Management Policy
- Change Management Policy
- Business Continuity Policy
- Acceptable Use Policy
- Information Security Policy
Everything looked polished. The language was professional. The formatting was clean. The policy library looked complete.
Then the auditor asked one painful question:
“Can you show evidence that these policies were reviewed and approved by management?”
Silence.
That is the problem.
AI can draft. AI can summarize. AI can suggest policy language. AI can help organize controls. But AI cannot:
- sign off on risk decisions
- prove your team follows the policy
- confirm the policy matches your actual systems
- approve exceptions
- show management commitment
- replace human review evidence
This blog explains how SaaS teams can use AI for SOC 2 policy drafting without creating audit problems.
Why AI-Written Policies Are So Tempting
It is easy to understand why founders use AI.
SOC 2 policy writing can feel slow and repetitive.
Most early-stage SaaS teams do not have:
- a compliance manager
- a security policy writer
- a full-time CISO
- a GRC analyst
- a legal operations team
- weeks to write documentation
AI looks like a shortcut. And sometimes, it is useful.
AI can help:
- create a first draft
- simplify policy language
- identify missing sections
- turn notes into cleaner wording
- standardize document format
- compare policy topics against common SOC 2 control areas
The mistake is not using AI. The mistake is treating the AI output as finished evidence.
| AI Draft | Audit-Ready Policy |
|---|---|
| Looks professional. | Matches actual operations. |
| Uses common compliance language. | Uses company-specific owners and workflows. |
| Includes expected sections. | Includes realistic control commitments. |
| Can be produced quickly. | Has review, approval, and version history. |
| Is a starting point. | Is a governed document. |
Practical rule: AI can write the first draft. Your business must own the final policy.
The Auditor’s Real Concern
When an auditor asks for human review evidence, they are not trying to be difficult.
They are testing whether the policy is real.
A policy is not just a document. It is a commitment.
For example:
- If your Access Control Policy says access reviews happen quarterly, the auditor may ask for access review records.
- If your Vendor Management Policy says critical vendors are reviewed annually, the auditor may ask for the vendor register and review evidence.
- If your Incident Response Policy says tabletop exercises happen once per year, the auditor may ask for the tabletop record.
- If your Change Management Policy says production changes require review, the auditor may sample pull requests or deployment approvals.
The policy must match what the company actually does.
| Auditor Question | Evidence Needed |
|---|---|
| Who owns this policy? | Policy owner field or assignment. |
| Who reviewed it? | Review record or workflow approval. |
| Who approved it? | Management approval evidence. |
| When was it approved? | Approval date. |
| What changed during review? | Review notes or version history. |
| Is it followed? | Operating evidence. |
The auditor is not only asking, “Does the policy exist?” They are asking, “Is this policy governed?”
Common Mistake 1: Uploading AI Policies With No Review Trail
This is the most common problem.
The team generates policies, uploads them to Google Drive, SharePoint, Notion, or a GRC platform, and marks them complete.
But there is no evidence of:
- who reviewed the policy
- what changes were made
- whether the policy matches operations
- who approved it
- when it was approved
- whether leadership accepted the commitments
A polished policy without review evidence can look like audit theater.
The better approach is to create a simple review workflow.
| Review Step | Evidence |
|---|---|
| Draft created. | AI draft or initial document version. |
| Owner assigned. | Policy owner metadata. |
| Operational review completed. | Comments or review notes. |
| Security review completed. | Security or vCISO sign-off. |
| Management approval completed. | Approval record. |
| Next review scheduled. | Review date metadata. |
Every SOC 2 policy should have a human owner and an approval record.
Common Mistake 2: Policies Promise Controls the Company Does Not Operate
AI tends to write mature-sounding policies.
That can be dangerous.
AI may say:
- access is reviewed quarterly
- vendors are risk-rated before onboarding
- all changes require documented approval
- logs are reviewed monthly
- restore tests are performed quarterly
- incidents are tested annually
These may be good controls. But if your company does not actually do them, the policy creates audit risk.
| Weak AI-Generated Language | Better SaaS-Friendly Language |
|---|---|
| All vendor security risks are continuously monitored. | Critical vendors that process customer data or support production services are reviewed before approval and at least annually. |
| All access is reviewed monthly by the security team. | Access to critical systems is reviewed at least quarterly by the assigned system owner or IT lead. |
| All changes require formal CAB approval. | Production changes are reviewed through the approved engineering workflow, including pull request review, testing, and deployment records. |
Do not let AI make your company sound more mature than your evidence can prove.
Common Mistake 3: No One Checks Whether the Policy Matches the Product
SOC 2 policies should reflect the real SaaS environment.
AI does not know your exact product unless you carefully provide context.
It may not know:
- your hosting provider
- your identity provider
- your deployment process
- your support workflow
- your data flow
- your vendors
- your incident escalation process
That means AI may write policies that sound fine but do not fit.
| AI Policy Says | Reality |
|---|---|
| All access is managed through SSO. | Some admin tools still have local accounts. |
| All customer data is deleted within 30 days. | Backups retain data longer. |
| Security logs are reviewed daily. | Logs are reviewed monthly or after alerts. |
| Vendors are reviewed by procurement. | Founder, operations lead, or security owner approves vendors. |
Who Should Review Each Policy?
| Policy | Who Should Review |
|---|---|
| Access Control Policy | IT, Security, Engineering |
| Change Management Policy | Engineering / DevOps |
| Vendor Management Policy | Operations, Legal, Security |
| Incident Response Plan | Security, Leadership, Legal / Privacy |
| Risk Management Policy | Leadership, vCISO, Compliance |
The person who operates the control should review the policy. Not just the person preparing the audit.
Common Mistake 4: Approval Happens in Slack or Email and Gets Lost
A founder may reply, “Looks good.”
A CTO may send, “Approved.”
A compliance lead may say, “Uploaded.”
But if approval happens in Slack, email, or a meeting with no record, it may be hard to prove later.
| Approval Detail | Why It Matters |
|---|---|
| Policy name | Shows what was approved. |
| Version | Shows which document was approved. |
| Approver | Shows who accepted the policy. |
| Approval date | Shows when approval happened. |
| Review notes | Shows what was checked. |
Common Mistake 5: No Version History
Version history matters.
Auditors may ask:
- When was this policy created?
- Was it reviewed before approval?
- What changed?
- Who edited it?
- Is this the current version?
- Are old versions controlled?
If the policy is a copied document with no version record, that story is harder to tell.
| Version | Date | Change | Approved By |
|---|---|---|---|
| v0.1 | 2026-02-10 | AI-assisted first draft. | Not approved. |
| v0.2 | 2026-02-15 | Updated access review cadence and owner roles. | Security Lead. |
| v1.0 | 2026-02-20 | Approved for use. | CTO. |
| v1.1 | 2026-05-12 | Added support access logging requirement. | CTO. |
Do not overwrite policy history. Keep the evidence trail.
Common Mistake 6: Human Review Is Treated as a One-Time Step
Human review is not only needed before the audit.
Policies need ongoing review.
SOC 2 Type II focuses on operating effectiveness over time. If policies are approved once and then forgotten, the control environment may weaken.
| Policy Type | Suggested Review Cadence |
|---|---|
| Information Security Policy | Annual. |
| Access Control Policy | Annual or after major identity changes. |
| Incident Response Plan | Annual and after incidents or tabletops. |
| Vendor Management Policy | Annual. |
| Data Retention Policy | Annual or after privacy/product changes. |
Policy review is not a one-time audit task. It is part of the control lifecycle.
How to Use AI Without Weakening SOC 2 Readiness
AI can still be useful.
The key is to use it inside a controlled process.
| Step | What to Do | Evidence |
|---|---|---|
| 1 | Use AI to create a first draft. | Draft version. |
| 2 | Assign a policy owner. | Owner metadata. |
| 3 | Review against real operations. | Comments or review notes. |
| 4 | Remove unrealistic commitments. | Updated version. |
| 5 | Map policy to evidence. | Evidence checklist. |
| 6 | Get management approval. | Approval record. |
| 7 | Schedule next review. | Review date. |
Use AI as a drafting assistant, not as the control owner.
The Human Review Evidence Pack
If you used AI to draft policies, create a human review evidence pack.
This helps show that the documents were not blindly accepted.
| Evidence | What It Proves |
|---|---|
| Policy owner list | Each policy has accountability. |
| Review checklist | Human review was structured. |
| Review comments | Content was checked and updated. |
| Version history | Drafts changed before approval. |
| Approval record | Management signed off. |
| Policy mapping | Policy aligns to controls and evidence. |
Human Review Checklist
- Does this policy match how we actually work?
- Are all roles accurate?
- Are review frequencies realistic?
- Are control commitments evidence-backed?
- Are vendors, systems, and tools named correctly?
- Are exceptions handled?
- Is the policy approved by the right person?
- Can we prove the control operates?
Want Your AI-Drafted Policies Audit-Checked?
Canadian Cyber can review AI-generated SOC 2 policies, identify unrealistic commitments, map them to evidence, and help create human review records auditors can trust.
Example: AI-Drafted Access Control Policy Review
AI draft said: “Access to all systems is reviewed monthly by the security team.”
Reality:
- The company has no security team.
- Access is reviewed quarterly by IT and system owners.
- Some SaaS tools are reviewed manually.
- Privileged access is reviewed first.
Human-reviewed policy language:
Access to critical systems is reviewed at least quarterly by the assigned system owner or IT lead. Reviews include Microsoft 365, Entra ID, production cloud access, source control, support tools, and other systems that process customer data. Review evidence includes user exports, reviewer sign-off, removed accounts, and documented exceptions.
Evidence needed:
- system list
- quarterly access review
- user exports
- reviewer sign-off
- removed users
- exception register
Example: AI-Drafted Vendor Management Policy Review
AI draft said: “All vendors are continuously monitored for security risk.”
Reality: The team reviews critical vendors annually and before onboarding. Low-risk vendors get lighter review. Vendor monitoring is not continuous.
Human-reviewed policy language:
Vendors are reviewed based on risk tier. Critical vendors that process customer data or support production services are reviewed before approval and at least annually. Reviews include service role, data handled, criticality, assurance evidence, risk rating, owner, approval decision, and next review date.
Evidence needed:
- vendor register
- risk tiering
- SOC 2 or ISO report review
- approval decision
- owner
- next review date
Common Mistakes to Avoid
- Mistake 1: Treating AI output as approved policy. AI output is a draft. It still needs review and approval.
- Mistake 2: Keeping unrealistic commitments. Do not promise monthly reviews, continuous monitoring, or mature controls unless you can prove them.
- Mistake 3: No named owner. Every SOC 2 policy needs an accountable human owner.
- Mistake 4: No version history. Keep draft, review, and approval history.
- Mistake 5: No operating evidence. A policy without proof is weak.
- Mistake 6: No management approval. Leadership must approve policy commitments and risk decisions.
- Mistake 7: Not updating policies after real changes. If systems, vendors, data, or workflows change, policies may need review.
What Auditors Appreciate
Auditors appreciate when SaaS teams are honest and organized.
They do not expect every company to write every policy from scratch. But they do expect governance.
Good audit story: “We used AI to assist with first drafts. Each policy was then reviewed by the assigned owner, updated to match our actual operations, approved by management, version-controlled, and linked to operating evidence.”
| Evidence Auditors Like | Why It Helps |
|---|---|
| Policy owner list | Shows accountability. |
| Version history | Shows document control. |
| Review notes | Shows human review occurred. |
| Approval records | Shows leadership approval. |
| Evidence links | Shows the policy is operating. |
What Good Looks Like
A strong AI-assisted SOC 2 policy process has:
- AI-assisted drafts
- human owners
- operational review
- security or vCISO review
- management approval
- version history
- realistic control language
- evidence mapping
- review cadence
- next review dates
The goal is not to avoid AI. The goal is to avoid fake maturity.
Canadian Cyber’s Take
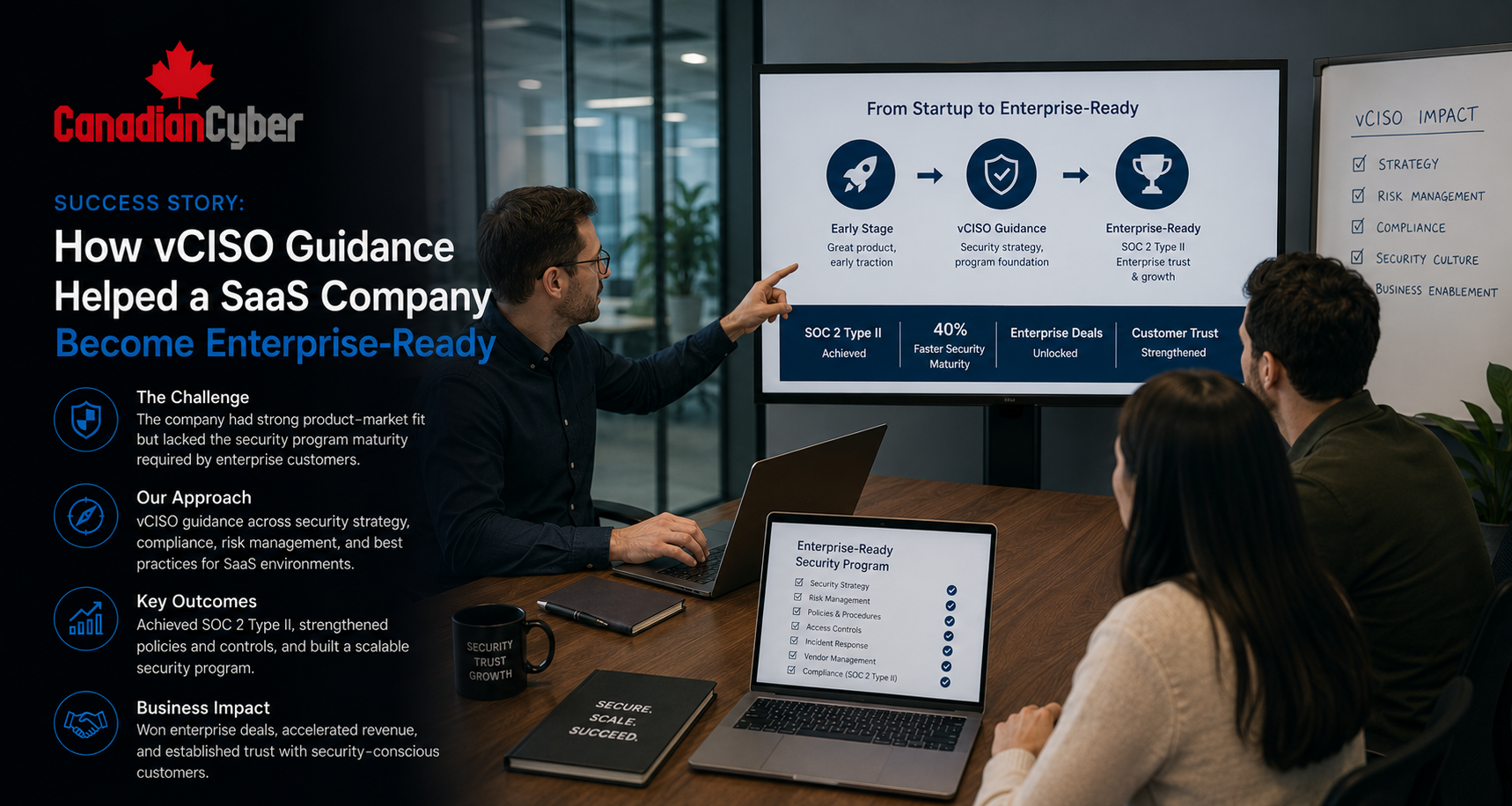
At Canadian Cyber, we often see SaaS teams using AI to move faster on SOC 2 preparation.
That is understandable. AI can help reduce blank-page pain.
But SOC 2 is not about having nice documents. It is about proving that controls are designed, approved, operating, and reviewed.
The risk with AI-generated policies is that they sound mature before the company is operationally ready.
The best approach is to use AI for drafting, then apply human review, operational validation, management approval, and evidence mapping.
AI can help write the policy. But people have to own it. That is the difference between a document and a control.
Takeaway
AI can draft SOC 2 policies.
But it cannot sign off.
It cannot:
- prove leadership reviewed the policy
- confirm the policy matches your real workflow
- show access reviews happened
- approve vendor risk
- test incident response
- produce management accountability
Use AI to speed up drafting. Then add the missing audit layer:
- human review
- policy ownership
- version history
- approval evidence
- realistic commitments
- control mapping
- operating evidence
- review schedule
That is how SaaS teams use AI without creating weak SOC 2 evidence.
How Canadian Cyber Can Help
Canadian Cyber helps SaaS teams turn AI-generated SOC 2 drafts into audit-ready policy and evidence programs.
- SOC 2 policy review
- AI-drafted policy cleanup
- human review evidence design
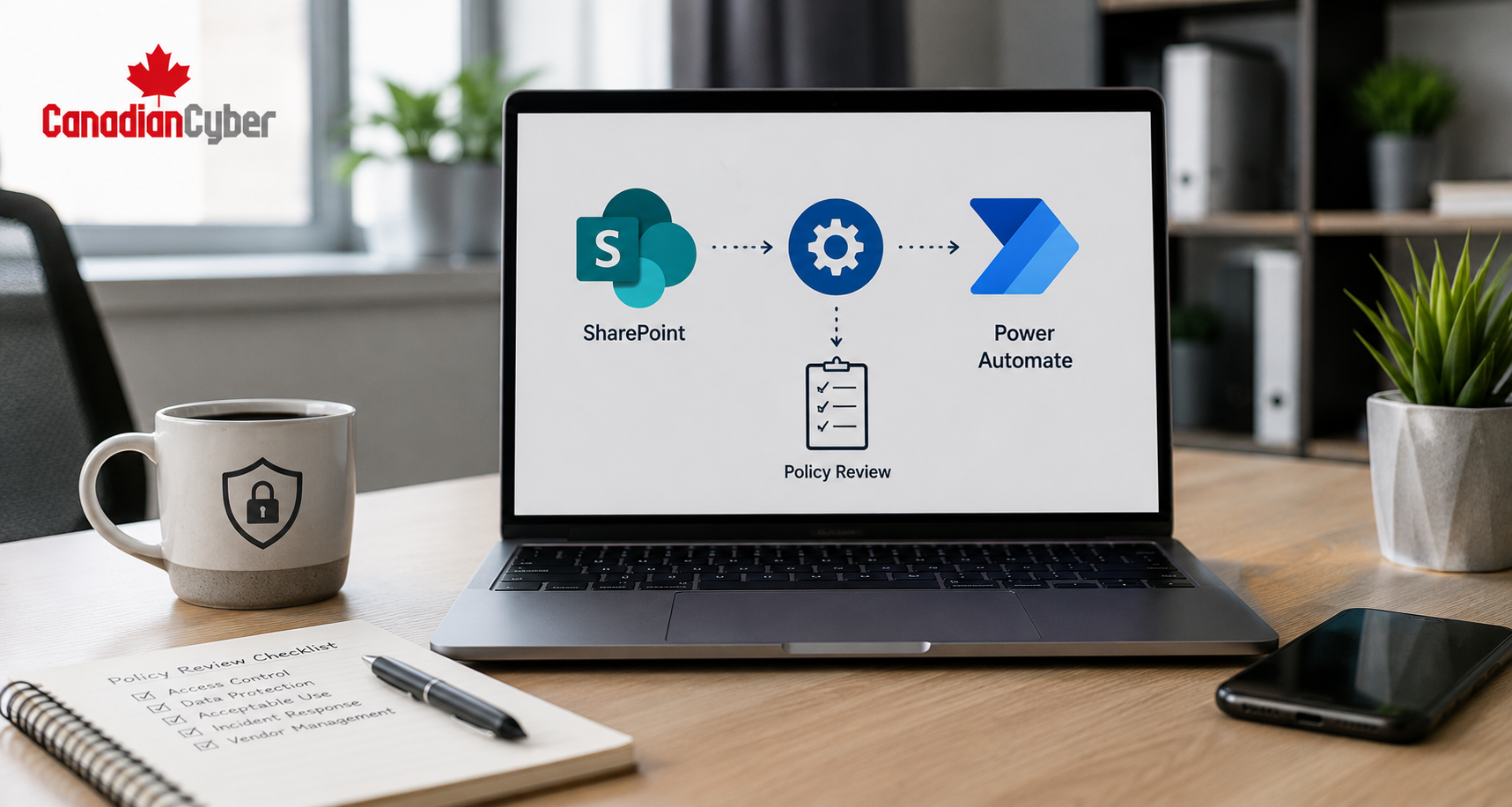
- policy approval workflows
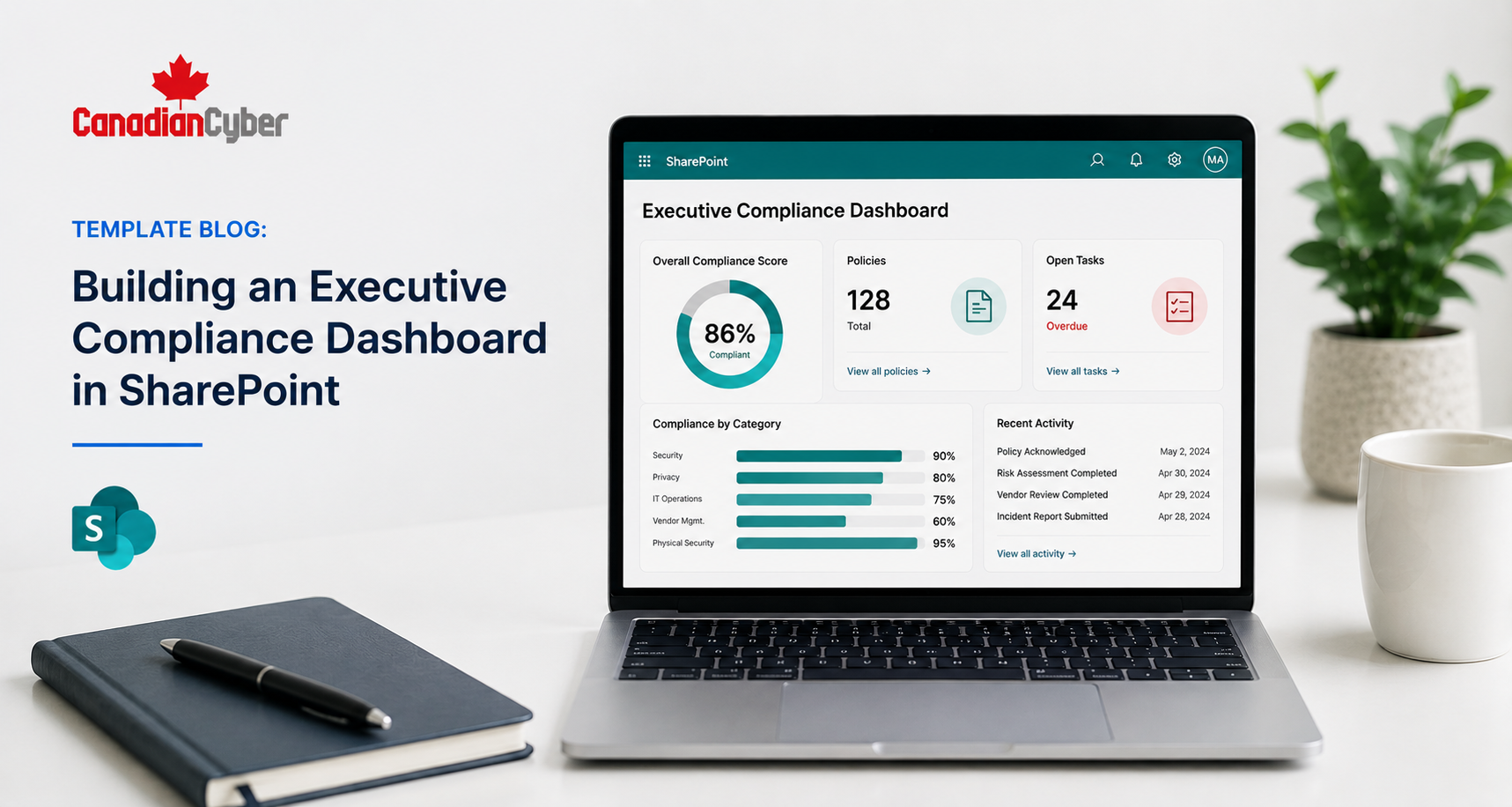
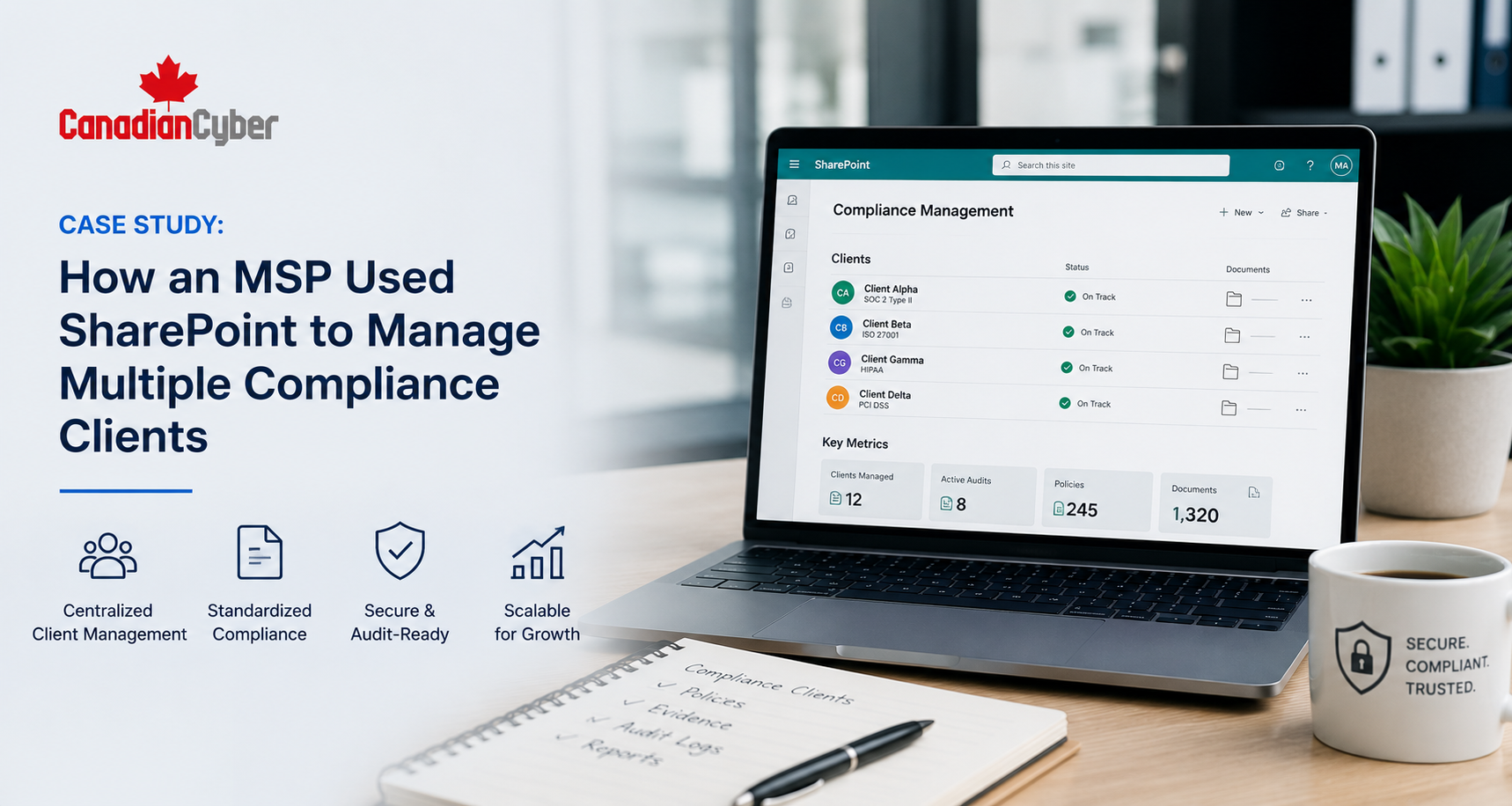
- SharePoint policy libraries
- SOC 2 evidence mapping
- access review evidence
- vendor management evidence
- incident response tabletop evidence
- management review preparation
- SOC 2 readiness roadmaps
- vCISO support for SaaS compliance
Stay Connected With Canadian Cyber
Follow Canadian Cyber for practical guidance on SOC 2, SaaS compliance, AI policy drafting, SharePoint ISMS, audit readiness, and vCISO support.