SOC 2 • Zero Trust • Access Control • Audit Logging • Security Controls
From “Zero Trust” to “Zero Evidence Surprises” — The SOC 2 Overlap Nobody Talks About
You already built Zero Trust for security. Congrats, you may be closer to SOC 2 readiness than you think. The missing piece is proving those controls are designed, operating, reviewed, and tied to audit-ready evidence.
Quick Snapshot
| Zero Trust Area | SOC 2 Overlap |
|---|---|
| Verify every user | Access control, MFA, SSO, and identity governance. |
| Use least privilege | Role-based access, privileged access reviews, and user lifecycle controls. |
| Monitor activity | Audit logging, alerting, investigation, and review evidence. |
| Segment systems | Network security, cloud access, and production isolation. |
| Protect data | Encryption, retention, data access, backup, and recovery. |
| Outcome | Zero Trust becomes easier to defend when it is mapped to SOC 2 evidence. |
Introduction
Zero Trust gets attention because it sounds modern.
- Never trust.
- Always verify.
- Limit access.
- Monitor activity.
- Assume breach.
- Protect every system.
SOC 2 gets attention because buyers ask for it.
- Show us your report.
- Show us your controls.
- Show us your evidence.
- Show us who reviewed access.
- Show us logs.
- Show us vendor risk.
- Show us incident response.
Most SaaS teams treat these as separate projects.
That is a mistake.
If you have already invested in Zero Trust, you may have already done a large part of the security work needed for SOC 2. Strong identity controls, least privilege, logging, monitoring, device trust, cloud segmentation, and access reviews all support SOC 2 readiness.
But there is a gap. Zero Trust is often built for security operations. SOC 2 requires proof.
That missing proof layer is the difference between Zero Trust and zero evidence surprises.
Why Zero Trust and SOC 2 Belong in the Same Conversation
Zero Trust and SOC 2 are not the same thing.
Zero Trust is a security strategy. SOC 2 is an assurance framework.
But they overlap in practical ways. A Zero Trust program asks:
- Who is accessing the system?
- Is the device trusted?
- Is access appropriate?
- Is activity monitored?
- Can unusual behavior be detected?
- Can access be removed quickly?
A SOC 2 auditor asks similar questions, but with an evidence lens:
- Where is the policy?
- Where is the access review?
- Where is the log sample?
- Where is the approval?
- Where is the ticket?
- Where is the exception?
| Zero Trust Focus | SOC 2 Focus |
|---|---|
| Make access safer. | Prove access is controlled. |
| Monitor activity. | Prove logs are collected and reviewed. |
| Reduce implicit trust. | Prove roles, approvals, and reviews exist. |
| Segment systems. | Prove production and sensitive environments are protected. |
| Validate continuously. | Prove exceptions and failures are tracked. |
Zero Trust reduces risk. SOC 2 proves the risk reduction is governed.
The Big Overlap: Access Control
Access control is where Zero Trust and SOC 2 meet first.
Most Zero Trust programs start with identity. That is also one of the first places buyers and auditors look.
Zero Trust Control
Users should only access what they need, when they need it, from trusted conditions.
SOC 2 Evidence Need
Your team must prove that access is approved, limited, reviewed, and removed when no longer needed.
| Zero Trust Practice | SOC 2 Evidence |
|---|---|
| SSO enforced | Identity provider configuration. |
| MFA required | MFA enforcement report. |
| Least privilege roles | Role matrix and access model. |
| Privileged access limited | Admin role export and review. |
| Quarterly access reviews | Review record, sign-off, removals, and exceptions. |
| Break-glass accounts controlled | Break-glass procedure and monitoring record. |
What Teams Often Miss
- MFA is enabled, but exceptions are not documented.
- SSO is used, but some admin tools still allow local login.
- Access reviews happen, but no sign-off is saved.
- Offboarding works, but tickets do not show all systems removed.
- Admin roles are limited, but no one reviews them quarterly.
The Second Overlap: Audit Logging
Zero Trust assumes you need visibility.
SOC 2 asks whether that visibility is logged, reviewed, and acted on.
| Zero Trust Practice | SOC 2 Evidence |
|---|---|
| Identity logs collected | Entra ID or Okta log settings. |
| Cloud admin activity logged | AWS CloudTrail, Azure Activity Logs, or GCP Audit Logs. |
| Privileged actions monitored | Admin activity review. |
| Alerts configured | Alert rule list. |
| Logs retained | Retention setting evidence. |
| Suspicious activity reviewed | Alert-to-ticket sample. |
SOC 2 does not only care that logs exist. It cares that logs support detection, investigation, and accountability.
The Third Overlap: System and Network Security
Zero Trust reduces broad internal trust.
SOC 2 cares whether systems are protected from unauthorized access, misconfiguration, and exposure. This includes cloud environments, production systems, APIs, databases, and internal admin tools.
| Zero Trust Practice | SOC 2 Evidence |
|---|---|
| Production separated from development | Architecture diagram. |
| Admin access restricted | Privileged access review. |
| Private network paths used | Cloud network configuration. |
| Cloud configurations monitored | CSPM or configuration review report. |
| Secrets managed centrally | Secrets manager configuration and access review. |
Strong cloud architecture still needs clear evidence. Good security without proof still creates audit friction.
The Fourth Overlap: Device Trust
Zero Trust often includes device trust.
SOC 2 buyers and auditors may ask how endpoints are managed, especially for employees with access to customer data or production systems.
| Zero Trust Practice | SOC 2 Evidence |
|---|---|
| Managed devices required | MDM enrollment report. |
| Disk encryption enforced | Device encryption report. |
| Endpoint protection installed | EDR or antivirus coverage report. |
| Screen lock configured | MDM policy evidence. |
| Unmanaged devices restricted | Conditional Access policy. |
If devices are part of your Zero Trust model, include endpoint evidence in your SOC 2 evidence pack.
The Fifth Overlap: Data Protection
Zero Trust assumes data should be protected even when perimeter controls fail.
SOC 2 asks how data is protected from unauthorized access, disclosure, loss, and misuse.
| Zero Trust Practice | SOC 2 Evidence |
|---|---|
| Encrypt data in transit | TLS configuration. |
| Encrypt data at rest | Database and storage encryption settings. |
| Restrict data access | Role-based access and review evidence. |
| Monitor data access | Audit log samples. |
| Test recovery | Restore test evidence. |
The Missing 30%: Evidence Operations
Here is the real point.
Zero Trust may get you close to SOC 2 from a control design perspective.
But SOC 2 Type II needs evidence that controls operated over time. That means the missing 30% is usually not security architecture. It is evidence operations.
| Evidence Area | What It Means |
|---|---|
| Control inventory | List of controls and owners. |
| Evidence map | Which evidence proves each control. |
| Owner sign-off | Human review and accountability. |
| Exception tracking | Known gaps, approval, expiry, and closure. |
| Remediation records | Tickets and proof of correction. |
| Audit workspace | Central location for evidence. |
| Zero Trust Control Exists | Missing SOC 2 Evidence |
|---|---|
| MFA enabled. | MFA exception register. |
| SSO implemented. | List of systems not covered by SSO. |
| Logs collected. | Monthly log review sign-off. |
| Backups running. | Restore test evidence. |
| Admin access limited. | Quarterly privileged access review. |
If a control is not evidenced, it will still create audit friction.
The “Zero Evidence Surprises” Model
The goal is simple.
You should not find missing evidence at the end of the audit period.
Zero evidence surprises means:
- access reviews are scheduled and tracked
- policy reviews have owners and due dates
- vendor reviews are monitored
- logs are reviewed and signed off
- cloud configuration issues create tickets
- exceptions have expiry dates
- restore tests are planned and recorded
- audit evidence is stored as work happens
| Control Area | Evidence Surprise to Avoid | Better Process |
|---|---|---|
| Access | Review missing for GitHub. | Quarterly system access review tracker. |
| Logging | Logs collected but not reviewed. | Monthly log review sign-off. |
| Vendors | SOC 2 report collected but not assessed. | Vendor review decision record. |
| Backups | Backup jobs pass but no restore test. | Quarterly restore test evidence. |
| Incidents | Plan exists but no tabletop. | Annual tabletop with action tracking. |
How to Map Zero Trust to SOC 2
Start with the controls you already have.
Do not start from a blank compliance checklist.
| Step | What to Do |
|---|---|
| 1. Inventory Zero Trust controls | List current controls across identity, devices, cloud, network, applications, data, logging, vendors, and incident response. |
| 2. Map controls to SOC 2 areas | Use practical categories such as access control, logging, system security, vendor management, and incident response. |
| 3. Identify evidence | Define source system, evidence type, owner, frequency, storage location, and review requirement. |
| 4. Find gaps | Ask whether the control is documented, owned, reviewed, evidenced, and exception-tracked. |
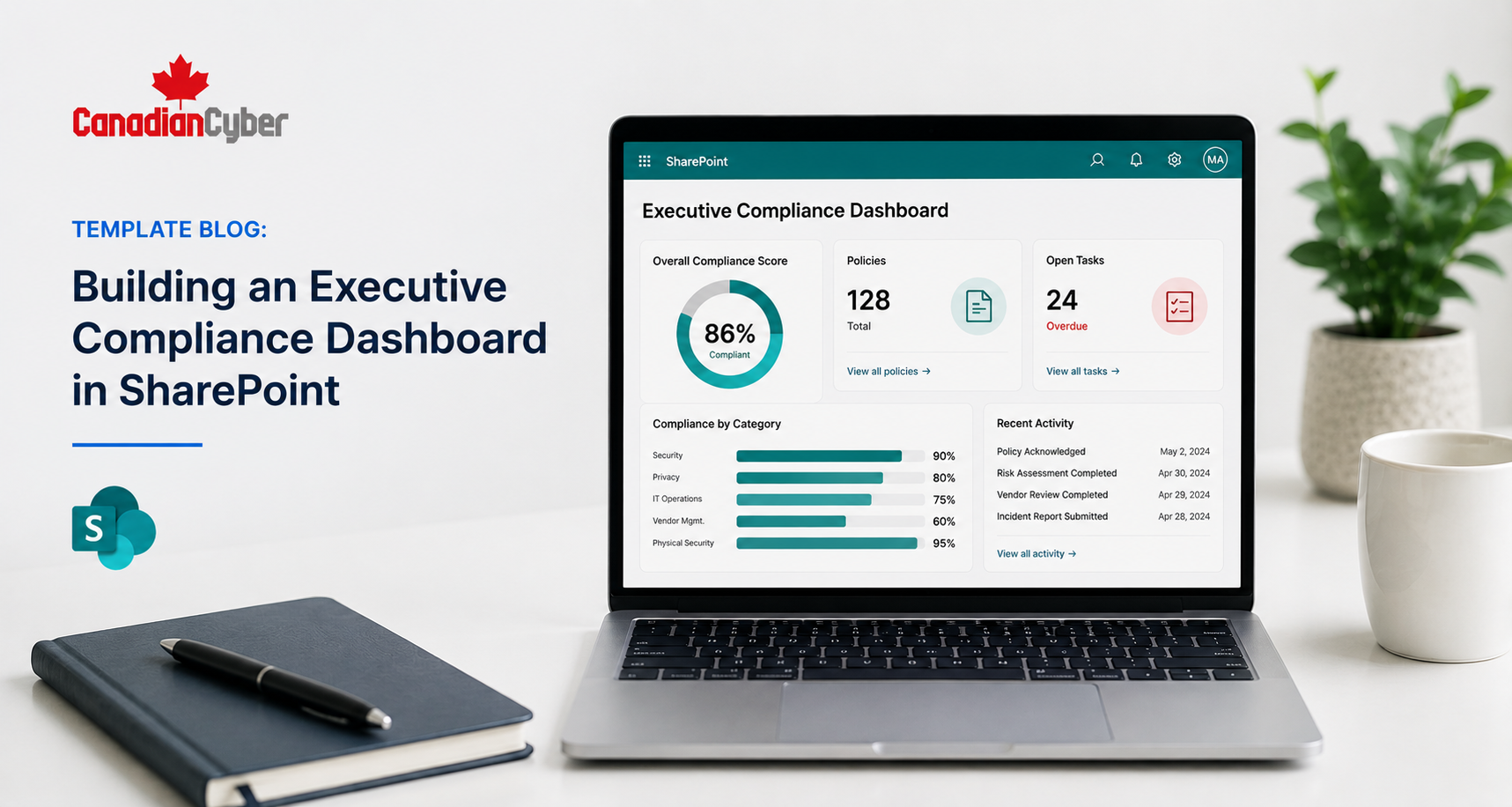
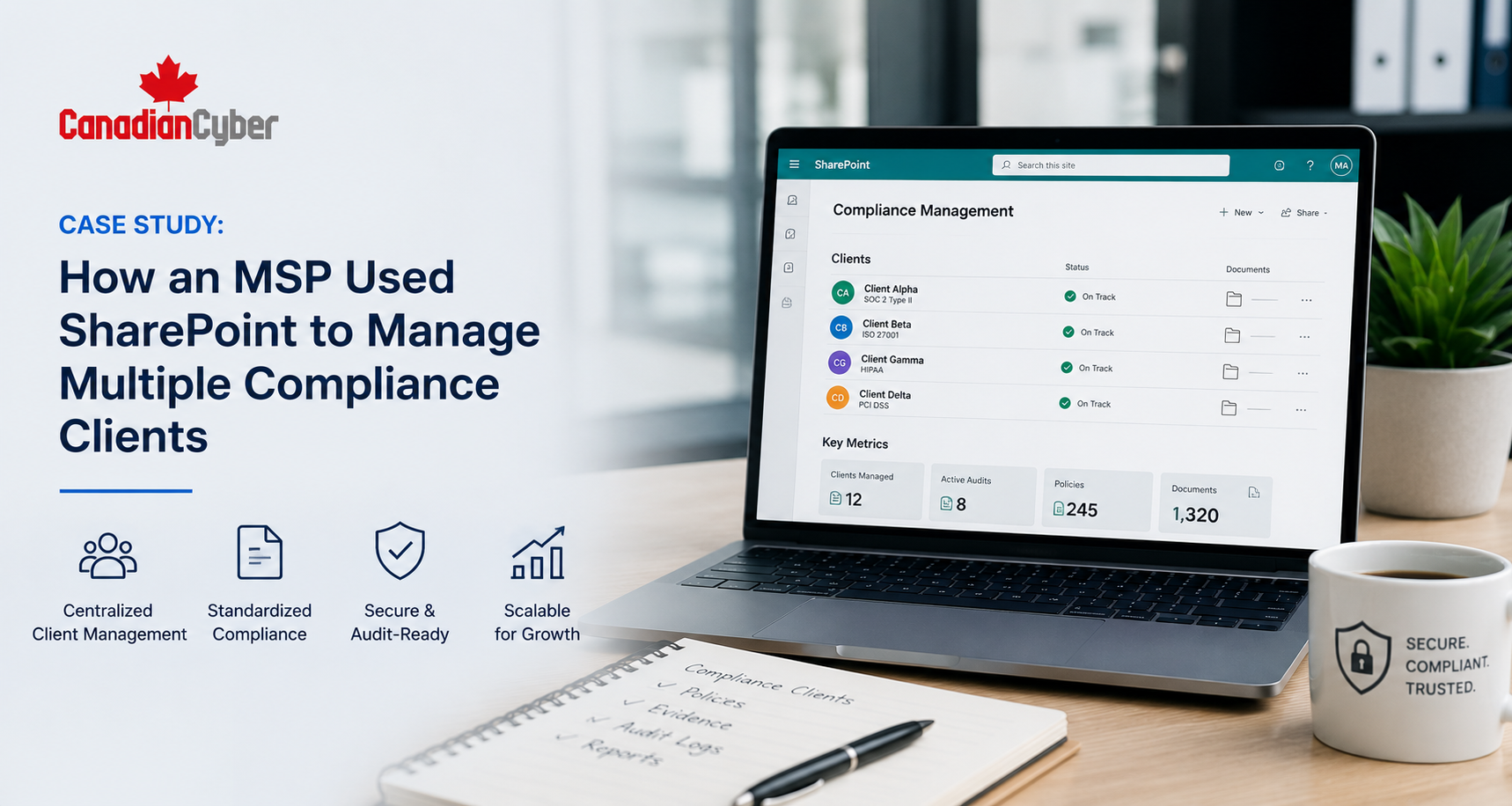
| 5. Build the evidence workflow | Use a GRC platform, SharePoint evidence vault, Power Automate reminders, Jira tickets, GitHub exports, cloud logs, access review trackers, and vendor registers. |
Example Mapping
| Zero Trust Control | SOC 2 Area |
|---|---|
| SSO and MFA | Access Control |
| Admin activity logging | Audit Logging |
| Cloud segmentation | System Security |
| Change approvals | Change Management |
| Backup restore testing | Availability and Recovery |
SOC 2 Evidence Pack for Zero Trust Teams
If your SaaS team has already built Zero Trust, create a SOC 2 evidence pack around it.
| Evidence Folder | What to Include |
|---|---|
| Identity and Access | MFA, SSO, access reviews, offboarding, and privileged access. |
| Device Trust | MDM, encryption, endpoint protection, and device compliance. |
| Cloud Security | Network segmentation, cloud configuration, and admin logs. |
| Logging and Monitoring | Log sources, retention, alert rules, and review records. |
| Vendor Risk | Vendor register, reviews, sub-processors, and approvals. |
| Management Review | Leadership reports, decisions, and risk acceptance. |
Good Evidence Naming Examples
- AccessControl-EntraID-MFAStatusExport-2026-Q1.pdf
- AccessControl-GitHub-PrivilegedAccessReview-2026-Q1.pdf
- LoggingMonitoring-CloudTrail-AdminActivityReview-2026-04.pdf
- CloudSecurity-AWS-SecurityGroupReview-2026-Q1.pdf
- VendorManagement-CriticalVendors-ReviewDecision-2026-Q2.xlsx
Good evidence naming reduces audit confusion.
How to Explain This to Leadership
Leadership may see SOC 2 as a compliance burden.
Frame it differently.
If the company has already invested in Zero Trust, SOC 2 becomes a way to prove that investment.
Executive message: “We already built many of the controls that SOC 2 buyers care about. The remaining work is to map those controls to evidence, document review cycles, track exceptions, and package the proof for auditors and enterprise buyers.”
| Security Investment | SOC 2 Value |
|---|---|
| Identity controls | Proves access governance. |
| Logging | Proves monitoring and investigation readiness. |
| Cloud segmentation | Proves system protection. |
| Vendor reviews | Proves third-party risk oversight. |
| Backup testing | Proves resilience. |
Common Mistakes to Avoid
- Mistake 1: Saying “We have Zero Trust” with no evidence. The phrase does not prove the control. Show access reviews, logs, exceptions, and monitoring.
- Mistake 2: Mapping only tools, not processes. Zero Trust tools help, but SOC 2 also needs human review, approvals, and governance.
- Mistake 3: Ignoring exceptions. Every Zero Trust program has exceptions. Track them with owners, reasons, expiry dates, and approvals.
- Mistake 4: Forgetting vendors. Your Zero Trust model may cover internal systems, but buyers still care about sub-processors and third parties.
- Mistake 5: Treating logs as enough. Logs need retention, review, alerting, and incident linkage.
- Mistake 6: Not preparing control owners. Control owners should know what evidence they provide and why it matters.
- Mistake 7: Waiting until audit time. Zero evidence surprises require evidence collection during the year.
What Good Looks Like
A strong Zero Trust to SOC 2 program has:
- SSO and MFA evidence
- least privilege access reviews
- privileged access monitoring
- device compliance reports
- cloud segmentation evidence
- audit log reviews
- alert-to-ticket samples
- vendor review decisions
- restore test evidence
- incident tabletop records
- policy approval history
- exception registers
- management review reports
The company does not just say “we use Zero Trust.” It proves how the model operates.
Canadian Cyber’s Take
At Canadian Cyber, we often see SaaS teams with strong security engineering and weak audit evidence.
They have SSO. They have MFA. They have logs. They have cloud controls. They have least privilege goals. They have modern tools.
But they have not mapped those controls into a SOC 2 evidence model.
That creates unnecessary audit stress.
The real work is translating Zero Trust into audit language:
- who owns the control
- what evidence proves it
- how often it is reviewed
- where exceptions live
- what happens when it fails
- how leadership sees the risk
That is how Zero Trust becomes zero evidence surprises.
Takeaway
If you already built Zero Trust, you may be closer to SOC 2 readiness than you think.
The missing piece is evidence.
Map your identity controls, logging, cloud segmentation, device trust, vendor risk, and incident response work to SOC 2 control areas.
Then build the operating layer:
- owners
- review cadence
- evidence vault
- exception tracking
- remediation records
- management reporting
- audit-ready summaries
SOC 2 does not have to be a separate nightmare. It can be the proof layer for the security work you already did.
How Canadian Cyber Can Help
Canadian Cyber helps SaaS companies turn Zero Trust controls into SOC 2-ready evidence programs.
- Zero Trust to SOC 2 mapping
- SOC 2 readiness reviews
- control inventory development
- evidence source mapping
- SharePoint evidence vault setup
- Vanta, Drata, and Secureframe support
- access review workflows
- logging and monitoring evidence
- vendor risk evidence
- exception registers
- incident response tabletop evidence
- management review reporting
- vCISO support for SaaS security governance
Stay Connected With Canadian Cyber
Follow Canadian Cyber for practical guidance on SOC 2, Zero Trust, SharePoint ISMS, audit readiness, ISO 27001, evidence mapping, and vCISO support.