A practical ISO 27018-aligned checklist for Canadian SaaS privacy addendums. Covers subprocessors, retention, deletion, breach notification, and buyer-ready contract language.
Enterprise customers aren’t only asking for SOC 2 or ISO 27001 anymore. They’re asking for privacy contract terms especially when your SaaS processes personal information in the cloud. This blog gives Canadian SaaS teams a practical, ISO 27018-aligned checklist for privacy addendums (DPAs): what customers expect, what to include, and how to avoid overpromising.
Deals stall when privacy terms are unclear: where data is processed, how subprocessors are managed, what happens after termination, and whether you can prove deletion.
ISO 27018 is guidance for protecting personally identifiable information (PII) in public cloud environments, especially when the provider acts as a PII processor.
Contract alignment usually means you can clearly describe your role, permitted processing, retention and deletion, subprocessors, safeguards, breach notification, cross-border processing, and assurance mechanisms.
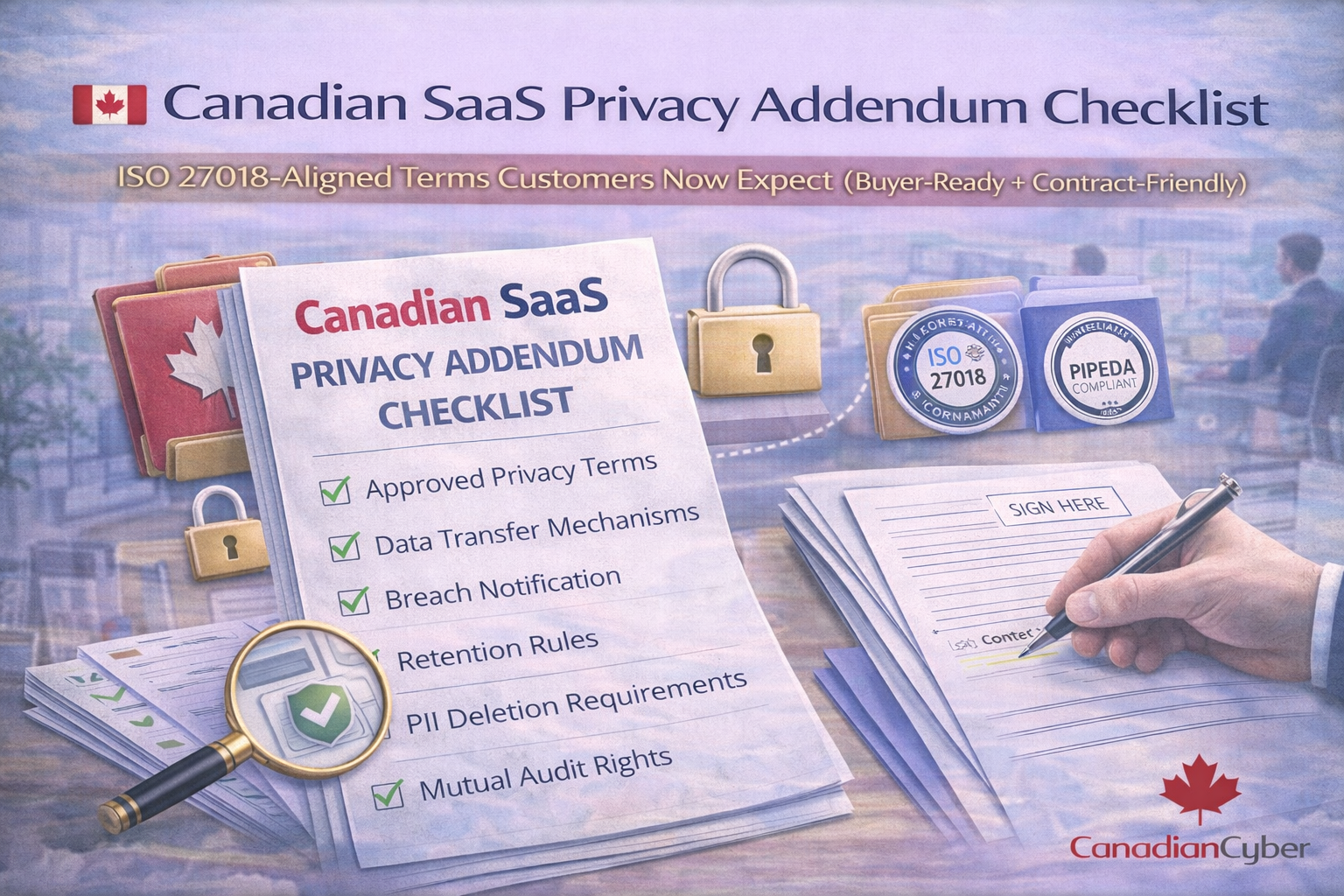
Use this as a buyer-ready checklist to review your DPA/privacy addendum. Keep each clause factual and tied to how your service really works.
Summarize your DPA with these bullets so buyers can approve faster.