A practical guide to SOC 2 security awareness, showing how to prove training happened and demonstrate real behavioral improvement.
A lot of companies can prove they assigned security awareness training.
Far fewer can prove it actually mattered.
That is a problem under SOC 2. Auditors do not only want to see a screenshot from a training tool or a completion report. They want to know whether the company runs awareness as a real control.
This is where many teams get stuck. They have annual training records, a policy acknowledgment report, maybe a few phishing simulations, and a spreadsheet that says everyone completed the course.
But when someone asks a harder question like “How do you know the training changed anything?” the answer gets weaker.
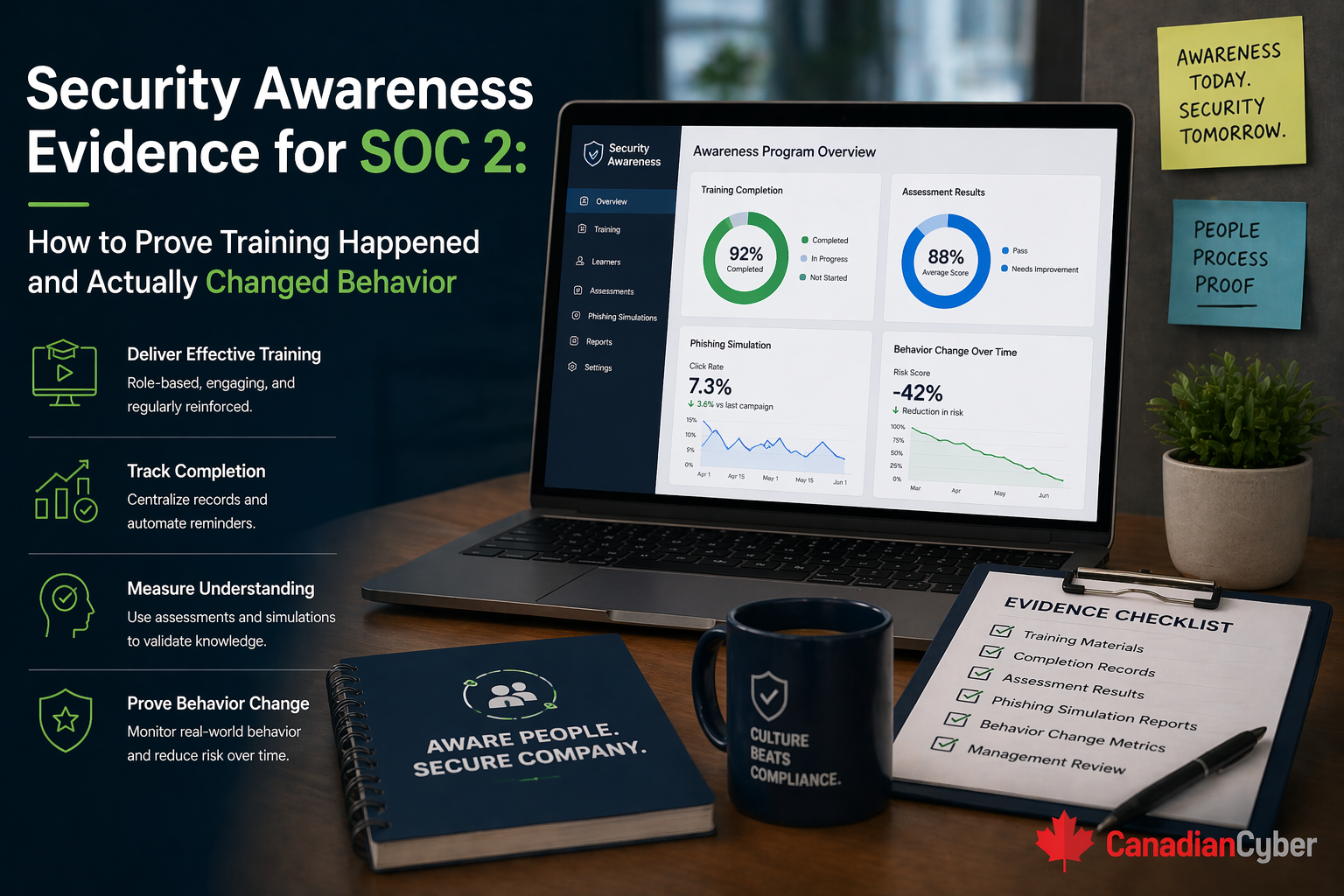
A strong SOC 2 awareness story should show more than attendance. It should show that the organization delivers training consistently, tracks completion, follows up on gaps, and uses real signals to see whether secure behavior is improving.
Security awareness is not a side topic in SOC 2. It sits close to the heart of whether controls actually work in a real environment.
Why? Because even strong technical controls can be weakened by human behavior.
SOC 2 is about whether the organization operates controls effectively. People are part of that control environment. So auditors want to see that your workforce is not only given a policy to read, but trained in a way that supports secure behavior.
A lot of teams lean heavily on one metric: training completion rate. That metric matters, but it is not enough on its own.
A company can still show 100% completion while real behavior stays weak.
That does not mean completion rates are useless. It means they are only one part of the evidence story.
A strong SOC 2 narrative usually needs to show two things: training happened and the organization has reason to believe it influenced behavior.
Picture this. A SaaS company is preparing for its SOC 2 audit. The compliance lead gathers awareness evidence and finds a screenshot from the training platform, an export showing staff completed annual security awareness, a signed policy acknowledgment, and a phishing summary from six months ago.
That seems decent at first. Then the auditor asks harder questions.
Now the gap becomes obvious. The company can prove training was assigned, but it has a weaker story around whether awareness is being managed as a real control.
For SOC 2, auditors usually want evidence in a few connected areas:
Before looking at completions, auditors usually want to know the organization actually has a defined awareness approach.
This matters because training is stronger when it is not treated like a one-time annual event.
This is the most basic layer, but it still needs to be clean. The company should be able to show what training was assigned, to whom, when, and whether it was completed in the right review period.
| Useful evidence | Why it helps |
|---|---|
| LMS or training-platform completion report | Shows assignment and completion clearly |
| Exported training records | Provides stronger evidence than a basic screenshot |
| Completion certificates or acknowledgments | Supports user-level proof |
| Attendance logs for live sessions | Supports instructor-led training evidence |
The best records usually show employee name or ID, training title, assigned date, completion date, status, and the training period covered.
A mature awareness program does not rely only on one annual campaign. Auditors often want to see that new hires receive training, training repeats on a set cadence, mid-cycle hires are not missed, and awareness is part of normal operating rhythm.
This helps prove awareness is maintained continuously, not rebuilt once a year before audit.
This is one of the easiest ways to strengthen the control story. Training completion is more credible when the company can show what happens if someone does not complete it.
This shows the company is managing awareness actively rather than hoping everyone gets around to it.
This is where the program moves from “training happened” to “training may actually be working.” You do not need to prove perfect behavior. But it helps a lot to show that the organization tracks signals that awareness is improving.
This kind of evidence is powerful because it shows the company is watching for outcomes, not just completions.
A strong awareness program reflects actual business risk, not generic internet safety alone. That means the training should connect to what employees really face.
If your company faces obvious risks in these areas but the awareness program never touches them, the evidence story becomes weaker.
This phrase sounds intimidating, but it does not require impossible proof. You do not need to prove that every employee became permanently security-perfect.
A more realistic standard is to show that the organization measures behavior-related signals, follows up when behavior is weak, reinforces expectations over time, and adjusts awareness when real problems appear.
That is much more practical than trying to prove a cultural transformation in one dashboard.
| Evidence item | Why it matters |
|---|---|
| Awareness policy or training standard | Shows the process exists |
| Annual or recurring training plan | Shows the cadence is defined |
| Completion report | Proves training occurred |
| New-hire training evidence | Shows onboarding coverage |
| Reminder or escalation records | Proves follow-up on gaps |
| Phishing simulation results | Shows behavior testing |
| Targeted retraining records | Shows response to weak behavior |
| Security bulletins or awareness reminders | Shows reinforcement between formal trainings |
| Management review or metric summary | Shows the program is monitored |
This package is much stronger than a single training screenshot.
Not every awareness metric is equally useful. The most helpful ones usually fall into three groups.
These help compliance leads answer both key questions: Did the training happen? and Are we learning anything from it?
These do not always mean the program is bad. But they make it much harder to prove the control is operating in a meaningful way.
A lot of organizations already have the right ingredients. They just have not connected them well.
This does not require a giant awareness maturity program. It requires a more complete and organized evidence trail.
At Canadian Cyber, we often see organizations underestimate awareness evidence because the training platform says “completed” and that feels sufficient. Sometimes it is enough for a basic conversation. But for a stronger SOC 2 story, it usually is not enough on its own.
The strongest awareness evidence usually includes three layers: proof the program exists, proof people completed it, and proof the company pays attention to whether behavior is improving or still weak.
That is what separates a checkbox training record from a more credible control narrative.
For SOC 2, security awareness evidence should do more than show that employees clicked through training.
It should help prove that the organization runs awareness as a defined program, assigns and tracks training consistently, includes onboarding and recurring cadence, follows up on missed completion, reinforces awareness after weak signals or incidents, and uses behavior-related indicators to judge whether the program is helping.
Because in the end, the strongest training evidence is not just “everyone completed the module.” It is “we trained people, tracked the results, followed up on weak spots, and can show signs that the program is influencing behavior over time.”