SOC 2 • Gap Assessment • SaaS Readiness
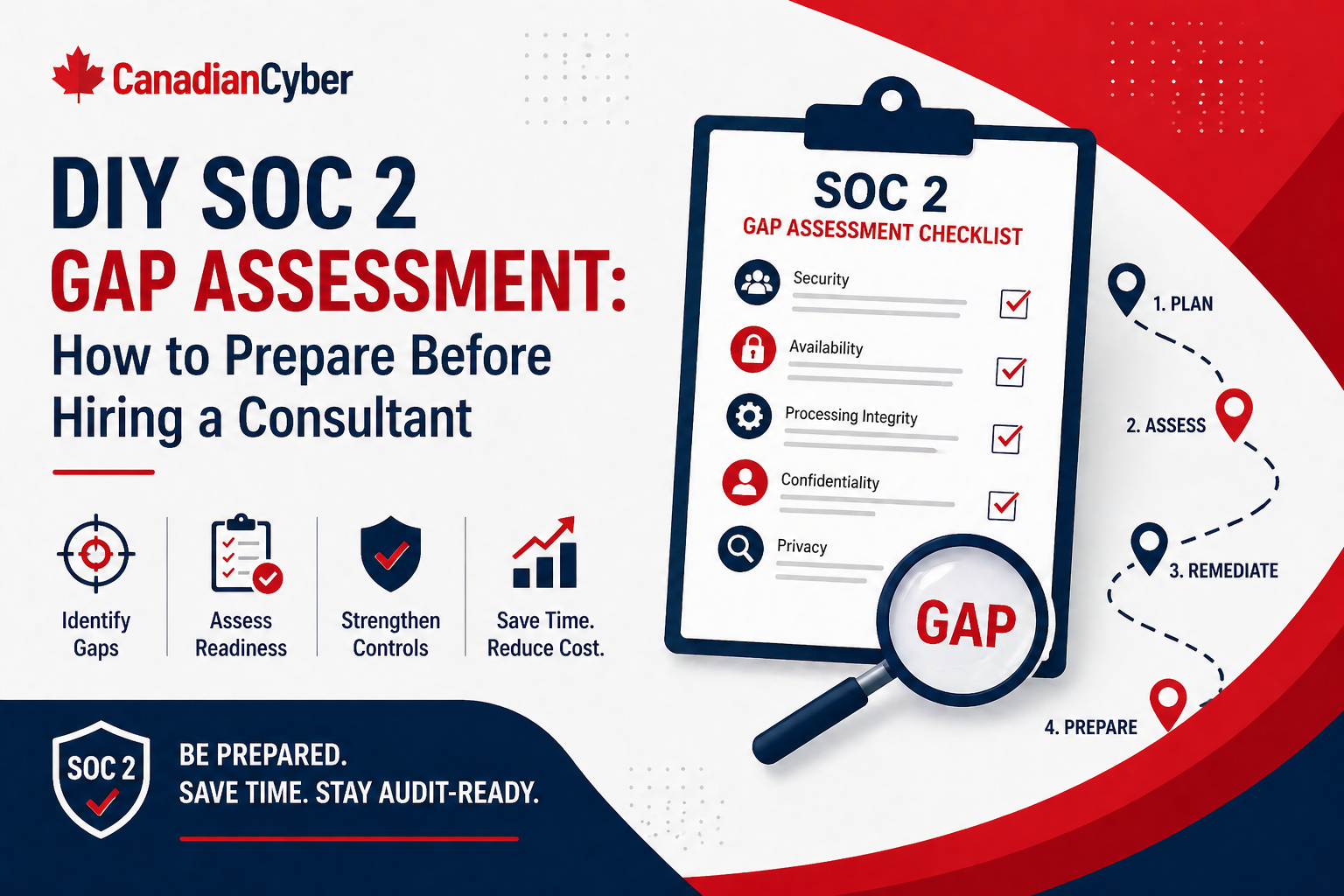
DIY SOC 2 Gap Assessment: How to Prepare Before Hiring a Consultant
A DIY SOC 2 gap assessment helps your team understand what is missing, where evidence lives, and what to fix before bringing in expert support.
Quick Snapshot
| Assessment Area | What to Check |
|---|---|
| Scope | Production app, cloud infrastructure, APIs, databases, support tools, vendors, and data stores |
| Core Controls | Access, change management, vendors, incidents, training, endpoints, backups, logging, and policies |
| Evidence | Collect what already exists before paying someone to find basic gaps |
| Outcome | A clear gap register, readiness priorities, and consultant-ready materials |
Introduction
Hiring a SOC 2 consultant can be extremely helpful.
But many companies bring in a consultant too early.
- They have not reviewed their current controls.
- They do not know where evidence lives.
- They have not mapped key systems.
- They are unsure who owns access, vendors, incidents, or change management.
- They expect the consultant to figure everything out from scratch.
A DIY SOC 2 gap assessment helps you understand what is missing before you pay someone else to confirm it.
This does not mean doing everything alone. It means preparing enough internally so that when a consultant is brought in, the work is focused, efficient, and based on real information.
Want to Know Your SOC 2 Gaps First?
Canadian Cyber can help validate your internal gap assessment and turn scattered findings into a practical SOC 2 readiness roadmap.
Why Do a DIY Gap Assessment First?
A DIY gap assessment gives your team a clearer starting point.
It helps you identify:
- which controls already exist
- which controls are missing
- where evidence is scattered
- who owns each process
- which systems are in scope
- what needs cleanup before audit readiness
- where a consultant can add the most value
SOC 2 is not just about policies. It is about proving that controls are designed, operating, and supported by evidence.
Step 1: Define Your Likely SOC 2 Scope
Start by listing the service or platform customers care about.
Include:
- production application
- cloud infrastructure
- databases
- APIs
- identity provider
- source control
- CI/CD pipeline
- support tools
- monitoring and logging
- customer data stores
- key vendors
Do not overcomplicate this yet. The goal is to understand what systems support the service you want covered by SOC 2.
Step 2: Identify the Trust Services Criteria You Need
Most startups begin with Security.
Depending on your business, you may also need:
- Availability
- Confidentiality
- Processing Integrity
- Privacy
For many SaaS companies, the first SOC 2 report starts with Security, then expands later if buyers ask for more. Your DIY review should note which criteria customers are already asking about.
Not Sure What Should Be in Scope?
We help SaaS teams define practical SOC 2 scope before they overbuild, overpay, or overcomplicate the first report.
Step 3: Review Core Control Areas
Focus on the areas auditors and buyers commonly test.
| Control Area | What to Check |
|---|---|
| Access Control | MFA, SSO, onboarding, offboarding, access reviews |
| Change Management | Code review, deployment approval, change tracking |
| Vendor Management | Vendor list, risk ranking, security reviews |
| Incident Response | Plan, roles, incident records, tabletop testing |
| Endpoint Security | Device inventory, encryption, EDR, patching |
| Logging and Monitoring | Alerts, logs, ownership, review process |
| Backup and Recovery | Backup coverage, restore testing, evidence |
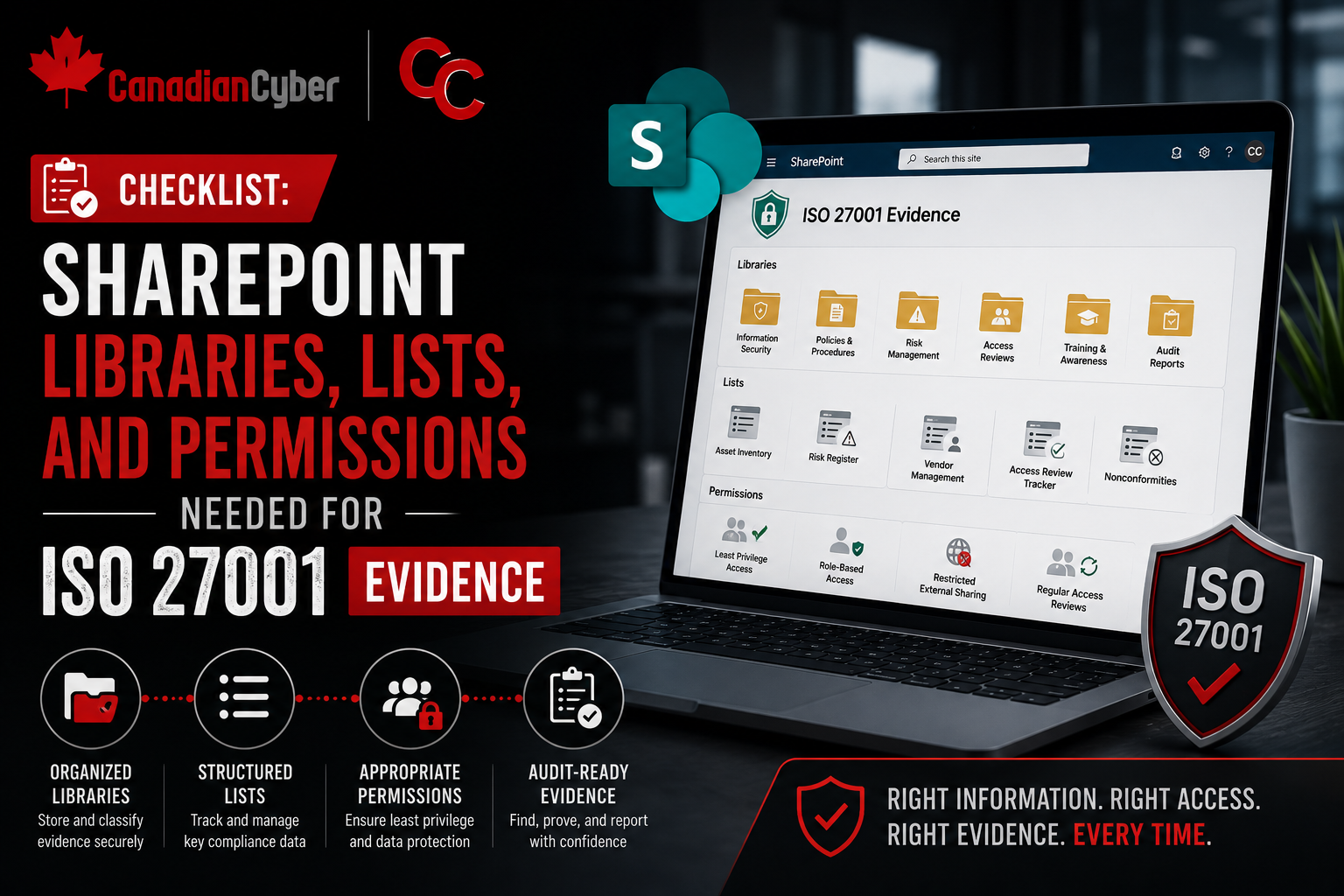
Step 4: Gather Existing Evidence
Create a simple evidence folder or SharePoint workspace.
Start collecting:
- approved policies
- MFA screenshots or reports
- access review records
- employee onboarding and offboarding examples
- vendor security reviews
- training completion reports
- incident response plan
- backup restore test evidence
- code review examples
- deployment logs
- risk register
- asset inventory
Do not worry if evidence is incomplete. The purpose of the gap assessment is to see what exists and what is missing.
Step 5: Score Each Control Area
Use a simple rating system.
| Score | Meaning |
|---|---|
| 1 | Missing |
| 2 | Exists informally |
| 3 | Documented but inconsistent |
| 4 | Operating with evidence |
| 5 | Mature and reviewed regularly |
For each control area, ask:
- Is there a process?
- Is it documented?
- Is someone responsible?
- Is there evidence?
- Has it operated recently?
- Would it stand up to audit review?
Need Help Scoring Your Controls?
Canadian Cyber can review your self-assessment and help identify which gaps are truly audit-blocking.
Step 6: Find the Common Gaps
Most companies discover similar issues during a DIY SOC 2 gap assessment.
Common Early SOC 2 Gaps
- MFA not enforced everywhere
- no formal access review
- weak offboarding evidence
- vendor reviews incomplete
- incident response plan untested
- policies outdated or generic
- backups configured but not restore-tested
- change management not consistently evidenced
- logs collected but not reviewed
- security training assigned but not tracked cleanly
Step 7: Build a Simple Gap Register
Track findings in a simple table.
| Gap | Risk | Owner | Priority | Evidence Needed |
|---|---|---|---|---|
| No quarterly access review | Excessive access may remain active | IT Lead | High | Completed access review report |
| Vendor reviews incomplete | Third-party risk not assessed | Ops Lead | Medium | Vendor register and reviews |
| Restore testing not documented | Recovery capability unproven | Cloud Lead | High | Restore test record |
| Policies not approved | Governance evidence weak | Compliance Lead | Medium | Approval records |
Step 8: Prioritize Before You Hire
Not every gap needs to be fixed immediately.
Prioritize gaps that are:
- high-risk
- easy to fix
- likely to block audit readiness
- commonly requested by customers
- evidence-heavy
- foundational for other controls
Good early priorities usually include MFA enforcement, access review, offboarding evidence, vendor register, incident response plan, backup restore test, policy approval, security awareness records, code review evidence, and asset inventory.
Want a Prioritized SOC 2 Roadmap?
We help teams separate urgent audit blockers from nice-to-have improvements, so your readiness work stays focused.
Step 9: Prepare Consultant-Ready Materials
Before hiring a consultant, organize:
- system list
- data flow overview
- current policies
- evidence folder
- gap register
- vendor list
- access control notes
- incident response plan
- current roadmap
- customer security requirements
This saves time and helps the consultant focus on higher-value work. Instead of spending the first few weeks discovering basics, they can help validate scope, refine controls, improve evidence, and prepare for audit.
What Not to Do
- Waiting for a consultant to define everything: You know your systems and workflows best.
- Writing policies before checking reality: Policies should match actual operations.
- Ignoring evidence: SOC 2 depends heavily on proof.
- Over-scoping the first report: Start with what buyers need and what you can operate well.
- Treating SOC 2 like a one-time project: Controls need to keep operating after the report.
Canadian Cyber’s Take
At Canadian Cyber, we often see companies start SOC 2 with good intentions but weak preparation.
The fastest projects usually begin with a simple internal gap assessment.
It does not need to be perfect. It just needs to show what exists, what is missing, who owns what, where evidence lives, and what needs expert help.
Takeaway
A DIY SOC 2 gap assessment is not a replacement for expert support.
It is preparation.
The better prepared you are, the faster and more useful the SOC 2 readiness project becomes.
How Canadian Cyber Can Help
We help SaaS companies prepare for SOC 2 with practical gap assessments, evidence reviews, and readiness roadmaps.
- DIY gap assessment validation
- SOC 2 readiness planning
- control mapping
- evidence organization
- policy and process cleanup
- vendor and access review workflows
- vCISO support for audit readiness
Stay Connected With Canadian Cyber
Follow Canadian Cyber for practical guidance on SOC 2, SaaS security, evidence readiness, audit preparation, and vCISO support.