Case Study • SOC 2 Type I • SaaS Readiness
Case Study: From Zero to SOC 2 Type I in 4 Months
A realistic breakdown of how a fictional SaaS startup moved from scattered security practices to SOC 2 Type I readiness in four focused months.
Quick Snapshot
| Timeline | Focus | Outcome |
|---|---|---|
| Month 1 | Scope and gap assessment | Clear boundary, control owners, quick wins |
| Month 2 | Core controls | Policies, access cleanup, vendor reviews, change process |
| Month 3 | Risk and incident readiness | Risk register, incident plan, tabletop exercise |
| Month 4 | Evidence and audit prep | Evidence library, mock review, final cleanup |
Introduction
Going from zero to SOC 2 Type I in four months sounds aggressive.
But for many SaaS startups, it can be realistic.
Not easy. Not automatic. Not something that happens by uploading a few policies. But realistic with focus, leadership support, and clear ownership.
SOC 2 Type I looks at whether controls are suitably designed at a point in time. That means the company needs to show a clear control environment, not months of operating history like Type II.
In simpler terms: SOC 2 Type I is often the fastest way for a growing startup to prove it has built the foundation of a security program.
Need SOC 2 Type I Quickly?
Canadian Cyber helps startups build practical SOC 2 readiness roadmaps with clear scope, control owners, evidence structure, and audit preparation.
The Company
Let’s call the company BrightLayer SaaS.
BrightLayer was a 35-person B2B SaaS startup selling into mid-market and enterprise customers.
The platform handled:
- customer account data
- workflow records
- file uploads
- API integrations
- support tickets
- user activity logs
The company had strong engineers and a good product, but no formal compliance program. They had:
- MFA in some systems
- basic cloud security
- informal code reviews
- scattered policies
- no vendor register
- no formal risk register
- no incident response testing
- no central evidence library
Then a major prospect asked: “Do you have SOC 2?” That question became the trigger.
Month 1: Scope, Gap Assessment, and Quick Wins
The first month focused on clarity.
The team defined the SOC 2 scope around:
- production SaaS platform
- cloud infrastructure
- customer data stores
- identity provider
- source control
- CI/CD pipeline
- support tooling
- monitoring and logging
- key vendors
Then they ran a gap assessment across core areas: access control, change management, vendor management, incident response, policies, endpoint security, security awareness, backup and recovery, and logging and monitoring.
| Key Fixes in Month 1 |
|---|
| Enforced MFA across critical systems |
| Created a system inventory |
| Identified control owners |
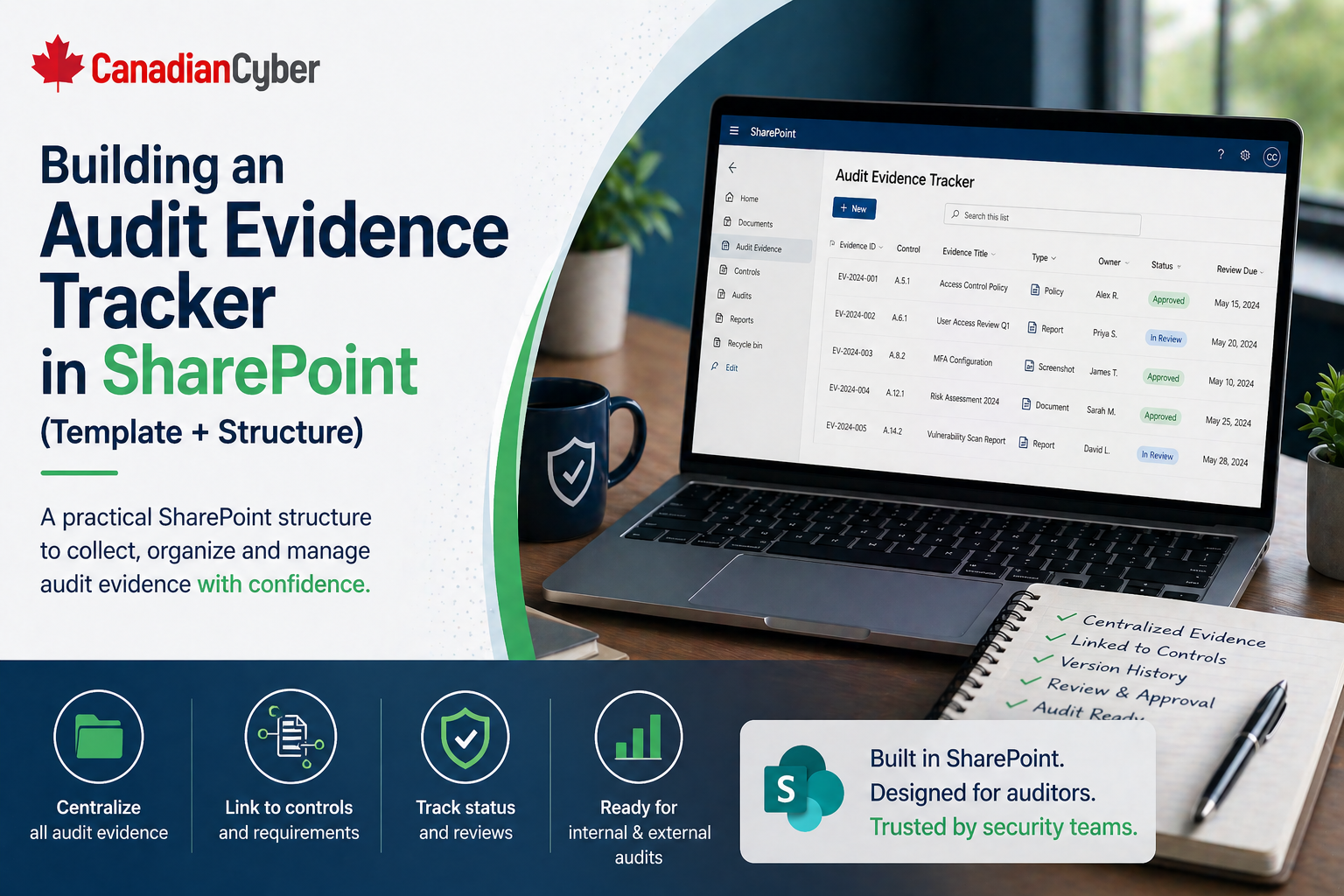
| Created an evidence workspace in SharePoint |
| Started drafting core policies |
| Documented the SOC 2 scope |
Start With the Right SOC 2 Scope
We help startups avoid over-scoping their first SOC 2 report so the project stays realistic, useful, and buyer-focused.
Month 2: Policies, Access, Vendors, and Change Management
Month 2 focused on building the control foundation.
The team finalized core policies:
- information security policy
- access control policy
- incident response plan
- vendor management policy
- change management policy
- acceptable use policy
- data handling policy
- backup and recovery procedure
Access Work Completed
- reviewed production access
- removed stale accounts
- restricted admin roles
- documented onboarding and offboarding
- created an access review template
- stored evidence of privileged access review
Vendor Work Completed
The team created a vendor register with:
- vendor name
- business owner
- data handled
- criticality
- security evidence
- review date
- next review date
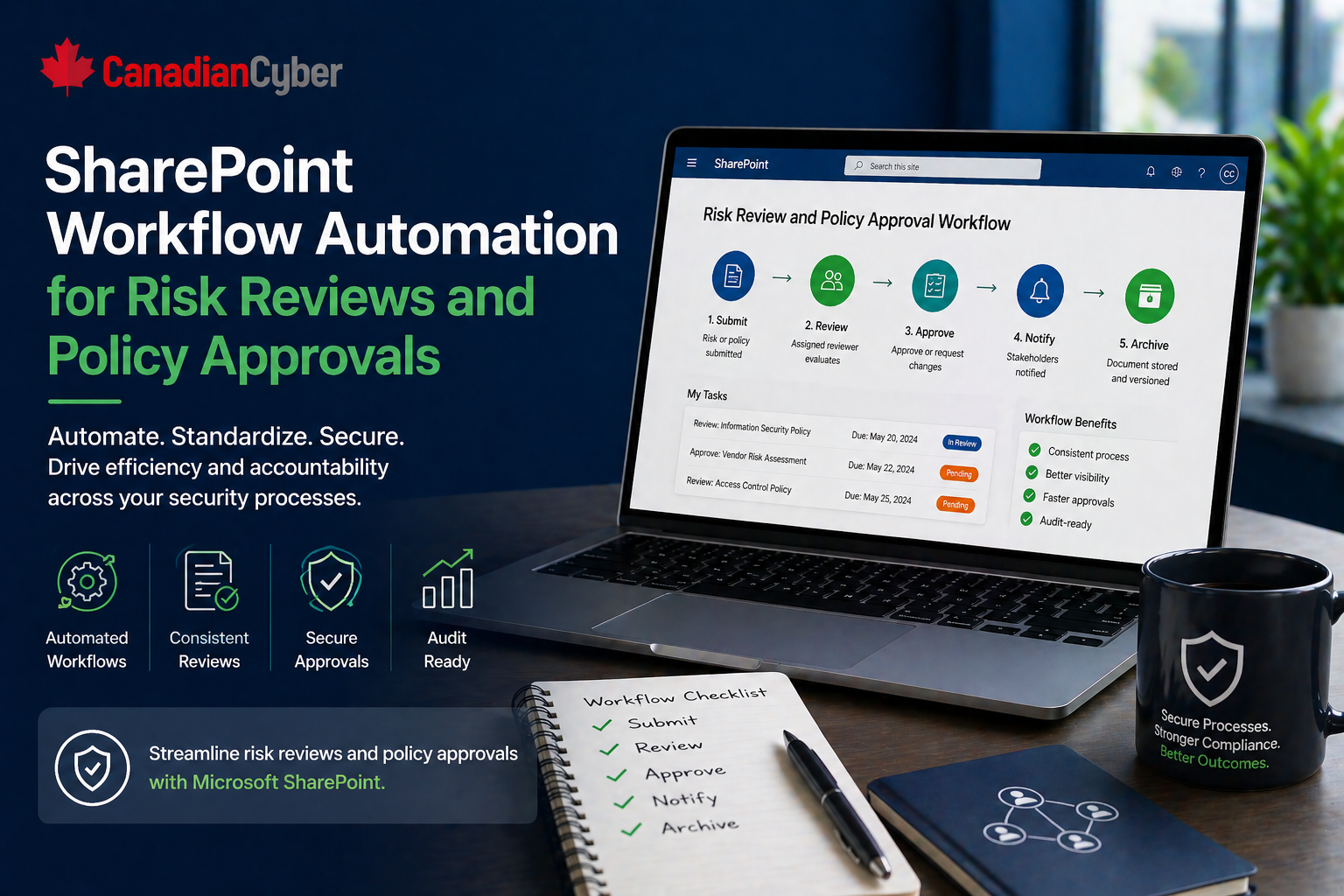
Change Management Work Completed
Engineering formalized:
- pull request review
- branch protection
- deployment approval evidence
- emergency change handling
This turned informal good practice into auditable control design.
Month 3: Evidence, Risk Register, and Incident Readiness
Month 3 was about making the program prove itself.
The team created a risk register covering:
- unauthorized access
- cloud misconfiguration
- vendor failure
- data leakage
- backup failure
- weak incident response
- insecure code changes
Each risk had:
- owner
- inherent risk
- existing controls
- residual risk
- treatment action
- status
Incident Response Work Completed
- defined severity levels
- assigned response roles
- created decision log template
- created incident record template
- ran a short tabletop exercise
- documented lessons learned
The tabletop revealed two gaps: customer notification was unclear, and incident evidence storage was not defined. Both were corrected before audit readiness review.
Need Incident Readiness Before SOC 2?
Canadian Cyber helps teams build incident response plans, templates, tabletop scenarios, and evidence records that support SOC 2 readiness.
Month 4: Readiness Review and Audit Preparation
The final month focused on cleanup and audit readiness.
The team reviewed all evidence against the SOC 2 control set. Evidence included:
- approved policies
- MFA screenshots
- access review records
- onboarding and offboarding examples
- vendor register
- vendor security reviews
- change management samples
- backup configuration
- restore test evidence
- incident response plan
- tabletop records
- training completion evidence
- risk register
- asset inventory
They also ran a mock audit request exercise. The compliance lead asked control owners to produce evidence quickly.
| Small Issue Found | Fix Before Audit |
|---|---|
| One policy lacked approval date | Approval record updated |
| One vendor review was incomplete | Review completed and stored |
| One access removal ticket had no closure note | Closure evidence added |
| One backup test needed better documentation | Restore test notes improved |
What Made the 4-Month Timeline Work
- They chose Type I first: They did not try to jump straight into Type II before controls were designed.
- Scope was controlled: They did not include every internal tool unnecessarily.
- Leadership stayed involved: Security was treated as a sales and trust priority.
- Evidence was centralized: SharePoint became the single evidence workspace.
- Owners were accountable: Control owners were assigned early.
- The team fixed gaps quickly: Findings were treated like sprint work.
What Could Have Delayed the Project
The timeline would have slipped if the company had:
- unclear scope
- no executive support
- weak engineering participation
- scattered evidence
- no access cleanup
- unfinished policies
- unreviewed vendors
- no risk register
- no incident response plan
- no readiness review before audit
SOC 2 Type I can move quickly, but only when decisions are made quickly.
What Type I Did Not Prove
SOC 2 Type I was a strong milestone, but it did not prove everything.
It did not prove months of operating effectiveness. That would come later with Type II.
Type I helped BrightLayer show:
- controls were designed
- policies existed
- owners were assigned
- key processes were defined
- evidence was organized
- the security foundation was real
Make Type I the Foundation for Type II
Canadian Cyber helps startups use Type I readiness to build operating discipline for a stronger future Type II report.
Canadian Cyber’s Take
At Canadian Cyber, we often see startups underestimate SOC 2 Type I in two ways.
Some think it is just paperwork. Others think it is impossible without a long timeline.
The truth is in the middle. SOC 2 Type I can be achieved quickly if the company focuses on scope, ownership, access control, vendor review, change management, incident response, risk tracking, and evidence readiness.
Takeaway
Going from zero to SOC 2 Type I in four months is realistic for a startup that is focused, responsive, and willing to build real controls.
A strong Type I project should create:
- clear scope
- approved policies
- controlled access
- vendor oversight
- change management
- incident readiness
- risk register
- organized evidence
SOC 2 Type I is not just about getting a report. It is about building the foundation for a security program customers can trust.
How Canadian Cyber Can Help
We help startups move from zero to SOC 2 readiness with practical implementation support and clear evidence structure.
- SOC 2 Type I readiness planning
- gap assessments
- scope and control mapping
- policy and process development
- access and vendor review workflows
- evidence library setup
- mock audit preparation
- vCISO support for startup security leadership
Stay Connected With Canadian Cyber
Follow Canadian Cyber for practical guidance on SOC 2, SaaS security, evidence readiness, audit preparation, and vCISO support.