Learn what SOC 2 incident evidence should include after a security event or near miss, with practical examples of detection, response, and audit-ready documentation.
Many SaaS companies worry that an alert spike, suspicious login pattern, malware detection, misconfiguration, or near miss during the audit period will look like a failure.
That is not usually the real problem. Auditors know security events happen. What they want to understand is much more practical: did your organization detect it, respond to it, document it, learn from it, and keep evidence that the process actually worked?
This is where many teams get uncomfortable. Not because they failed to respond, but because the proof after the event is scattered across Slack, tickets, screenshots, email threads, SIEM logs, and people’s memory.
SOC 2 is not just about whether controls exist on paper. It is about whether those controls operate effectively over time.
A real security event, or even a near miss, can become strong audit evidence because it shows whether your response process worked in practice.
Many organizations focus only on major incidents. But SOC 2 auditors may care about both confirmed incidents and near misses.
Why does this matter? Because a near miss can still prove that monitoring worked, escalation happened, investigators followed procedure, decisions were documented, and remediation was taken seriously.
In many cases, a near miss is one of the clearest ways to show that your response process is real, not theoretical.
Imagine a SaaS company detects unusual login activity against an internal admin account. MFA is enabled, and no confirmed compromise is found. But the alert triggers a quick investigation.
The team reviews identity logs, resets credentials, checks for lateral movement, confirms there was no unauthorized production access, records the issue in a ticket, discusses it in Slack, and closes the event the next day.
Operationally, that may be a good response. But three months later, when SOC 2 evidence is requested, the team realizes the story is incomplete.
Now the organization is rebuilding the incident after the fact. That is exactly what strong incident evidence should prevent.
Auditors are usually not looking for dramatic storytelling. They want clean, traceable proof that your incident response controls operated as designed.
That usually means evidence in a few consistent categories.
The first question is simple: how was the event detected? Auditors want to see that detection came from real monitoring activity, not luck.
Good detection evidence answers four simple questions: what triggered the response, when was it detected, who or what noticed it, and was the source appropriate for the kind of event involved?
Once an event is detected, auditors usually want to know whether it was assessed properly. This is where triage and classification matter.
| Field | Why it matters |
|---|---|
| Date and time opened | Establishes the timeline |
| Event type | Shows how the issue was categorized |
| Severity | Proves the organization uses response logic consistently |
| Initial impact assessment | Shows early risk thinking |
| Owner or handler | Establishes accountability |
| Status | Shows progression through the response process |
This does not need to be complicated. It just needs to be structured enough that an auditor can follow the logic without guessing.
This is often the most important section. Auditors want to see what your team actually did after the issue was identified.
Useful support here may include ticket work logs, screenshots from admin consoles, identity or system logs, EDR action records, copied chat summaries, or linked change records. What this proves is simple: the organization followed through, actions were timely, and response was operational, not just procedural.
SOC 2 auditors also want to see whether communication followed a defined path. That does not mean every event needs a dramatic war room. It means you should be able to show who was notified, when escalation happened, and whether the right stakeholders were involved.
This becomes especially important when the event could have affected customer data, production systems, privileged accounts, availability, or regulated information.
A surprising number of incident records show how an event started, but not how it ended. That creates audit problems fast.
Without this, the record feels unfinished, even if the team handled the issue well operationally.
This is one of the clearest signs of maturity. Auditors often want to see whether the organization learned anything from the event.
| Review area | Example question |
|---|---|
| Detection | Did we detect the issue quickly enough? |
| Escalation | Was the right team involved soon enough? |
| Response | Were actions effective and documented properly? |
| Control gap | Did this reveal a process or control weakness? |
| Improvement | What should change going forward? |
This kind of review does not always require a huge formal report. But meaningful events and near misses should usually leave behind some written learning.
If the event exposed a weakness, auditors may want to see that the organization did more than close the ticket. They may look for follow-up work such as corrective actions, policy updates, extra logging, retraining, threshold changes, hardening tasks, or ownership changes.
This is especially powerful for near misses. A near miss often reveals a weakness before major harm occurs. If the organization used that signal to improve controls, that is strong evidence of maturity.
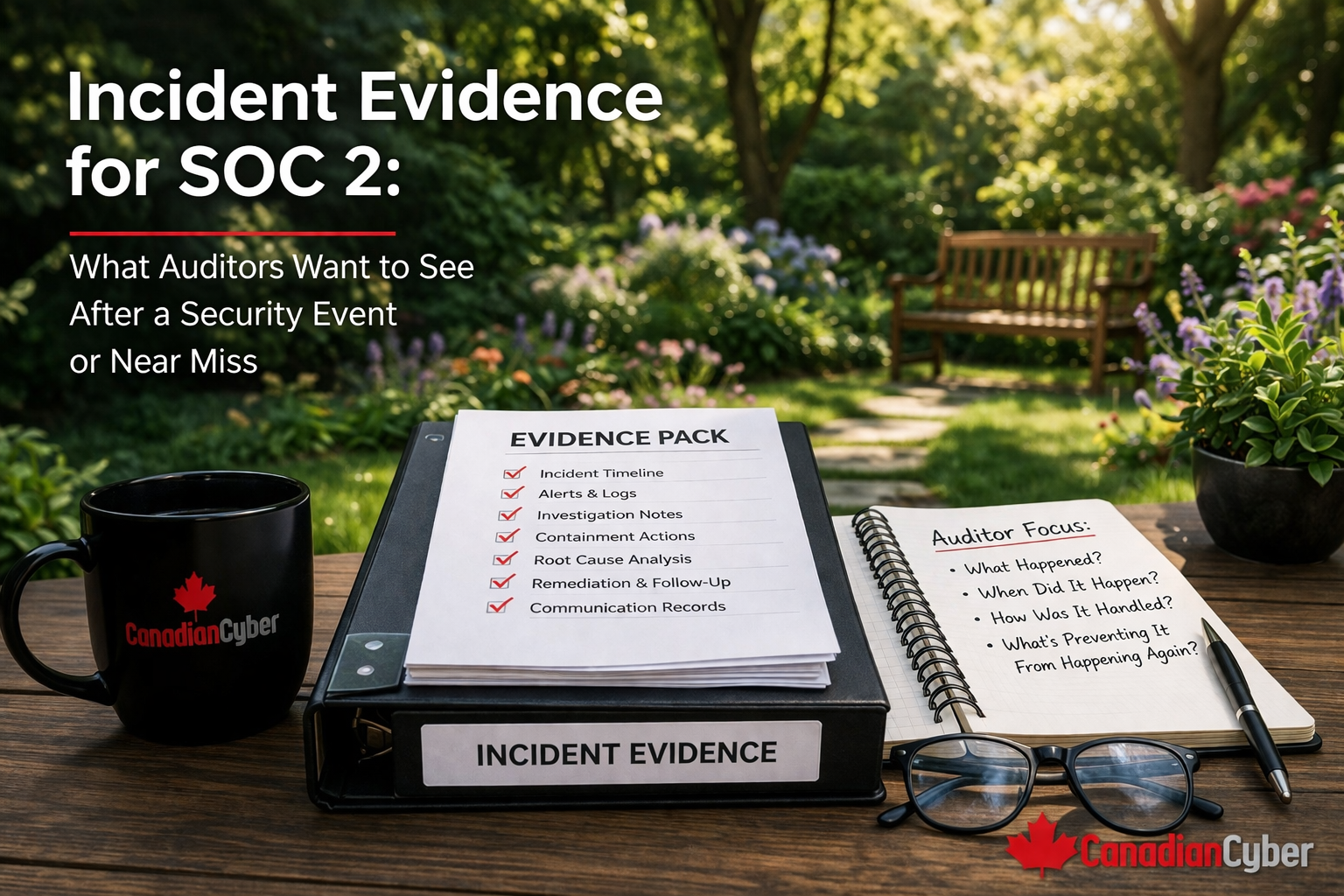
For SOC 2, strong incident evidence is usually not one file. It is a small connected package.
Incident evidence usually becomes weak in very predictable ways.
These gaps do not always mean the response was poor. But they do make it much harder to prove control effectiveness.
| Evidence item | Included? |
|---|---|
| Detection source recorded | ☐ |
| Date and time documented | ☐ |
| Severity assigned | ☐ |
| Owner identified | ☐ |
| Investigation steps logged | ☐ |
| Containment or response actions recorded | ☐ |
| Screenshots or logs saved | ☐ |
| Communication documented | ☐ |
| Final outcome summarized | ☐ |
| Closure date recorded | ☐ |
| Lessons learned documented | ☐ |
| Corrective action created if needed | ☐ |
The best time to improve incident evidence is not when the auditor asks for it. It is before the next event happens.
Many organizations respond well to events operationally but struggle to prove that response cleanly during SOC 2. The issue is rarely that nothing was done. The issue is that evidence lives in too many places.
The strongest SOC 2 incident evidence usually comes from teams that treat every meaningful event or near miss as both an operational matter and a documentation opportunity.
When the evidence is structured well, a security event does not just become a disruption. It becomes proof that your response process works.
SOC 2 auditors do not expect your company to live in a world with zero security events. They do expect you to show that when an event or near miss happened, your controls worked effectively.
That means being able to prove how the issue was detected, how it was classified, what actions were taken, who was involved, how it was closed, what was learned, and what improved afterward if needed.
The better your incident evidence is, the stronger your SOC 2 story becomes. Because in the end, auditors are not only asking whether something happened. They are asking whether your organization handled it with control, discipline, and traceable proof.