Microsoft 365 • Entra ID • Cloud Access • Internal Audit • ISO 27001
Checklist: Internal Audit Questions for Microsoft 365, Entra ID, and Cloud Access
Microsoft 365 and Entra ID sit at the center of modern cloud access. If they are not reviewed properly, your ISO 27001, SOC 2, ISO 27017, and customer security evidence can look weaker than it really is.
Quick Snapshot
| Audit Area | What to Check |
|---|---|
| Entra ID Governance | MFA, Conditional Access, privileged roles, guest users, break-glass accounts, and access reviews. |
| Microsoft 365 Security | Mail security, SharePoint permissions, Teams sharing, OneDrive controls, audit logs, and retention. |
| Cloud Access | Admin access, service accounts, SaaS apps, SSO integrations, device trust, and third-party access. |
| Evidence Needed | Screenshots, exports, access review records, policy settings, audit log samples, tickets, and approvals. |
| Outcome | A practical internal audit checklist that helps prove cloud access is controlled, reviewed, and monitored. |
Introduction
Microsoft 365 is not just email.
Entra ID is not just a login tool.
Together, they often control access to email, documents, Teams chats, SharePoint sites, SaaS platforms, cloud admin consoles, customer records, internal files, support tools, and sensitive business systems.
That makes them audit-critical.
When internal audit reviews Microsoft 365, Entra ID, and cloud access, the goal is not to prove every setting is perfect. The goal is to test whether access is controlled, risky permissions are reviewed, logs are available, and users can only reach what they actually need.
Why Microsoft 365 and Entra ID Matter So Much
Most companies run large parts of their business through Microsoft 365.
That includes:
- SharePoint
- Teams
- OneDrive
- Entra ID
- Exchange Online
- Power Platform
- Microsoft Defender
- third-party SaaS SSO
- guest collaboration and audit logging
If Entra ID is weak, everything connected to it becomes weaker.
If SharePoint permissions are messy, sensitive documents may be exposed.
If audit logs are not enabled or reviewed, investigations become harder.
| Internal Audit Should Ask | Why It Matters |
|---|---|
| Who can access Microsoft 365 admin functions? | Admin roles can change security settings and access data. |
| Is MFA enforced for users and admins? | MFA reduces account takeover risk. |
| Are guests reviewed? | External users can retain access longer than intended. |
| Are SharePoint sites controlled? | Sensitive documents may be overshared. |
| Are logs retained? | Investigations and audits need evidence. |
Part 1: Entra ID Internal Audit Questions
Entra ID is the identity layer. Start here.
1. MFA and Conditional Access
MFA should be enforced for all users, especially admins. Conditional Access should support risk-based access decisions.
| Audit Question | Evidence to Request |
|---|---|
| Is MFA enforced for all users? | MFA registration and enforcement report. |
| Are all privileged accounts covered by MFA? | Admin MFA report. |
| Are legacy authentication methods blocked? | Conditional Access policy export. |
| Are risky sign-ins challenged or blocked? | Risk policy settings. |
| Are exceptions documented and approved? | Exception register. |
Red flags:
MFA is optional, admins are excluded from MFA, legacy authentication is allowed, Conditional Access has undocumented exclusions, or no one knows who approved exceptions.
2. Privileged Role Management
Privileged roles in Entra ID are high-risk. They can reset passwords, change policies, manage users, control apps, and weaken security settings.
| Audit Question | Evidence to Request |
|---|---|
| Who has Global Administrator access? | Entra role export. |
| Are admin roles assigned using least privilege? | Role assignment review. |
| Are privileged roles time-bound where possible? | PIM configuration. |
| Are admin accounts separate from daily-use accounts? | Admin account list. |
| Are admin roles reviewed quarterly? | Access review record. |
Canadian Cyber Tip: Global Administrator access should be rare, justified, reviewed, and monitored.
3. Break-Glass Accounts
Break-glass accounts are emergency accounts used when normal access fails. They are important, but they can also become hidden risk.
| Audit Question | Evidence to Request |
|---|---|
| Do break-glass accounts exist? | Account list. |
| Are they excluded from Conditional Access intentionally? | Documented exception. |
| Are credentials stored securely? | Access procedure. |
| Are they monitored for use? | Alert rule or log sample. |
| Are they tested periodically? | Test record. |
4. Guest Users and External Collaboration
Guest access is one of the most common Microsoft 365 audit gaps. Guests may include customers, consultants, vendors, auditors, partners, former employees, or temporary workers.
| Audit Question | Evidence to Request |
|---|---|
| Are guest users allowed? | External collaboration settings. |
| Who approves guest access? | Guest access procedure. |
| Are guests reviewed periodically? | Guest user access review. |
| Are inactive guests removed? | Removal records. |
| Are guests restricted from sensitive sites? | SharePoint or Teams permission evidence. |
Part 2: Microsoft 365 Internal Audit Questions
Microsoft 365 holds a lot of sensitive data. Email, files, chats, meeting recordings, and SharePoint sites often contain customer data, contracts, financial information, HR records, security evidence, and internal decisions.
5. SharePoint and OneDrive Permissions
SharePoint and OneDrive are common sources of oversharing. Internal audit should check whether sensitive sites are controlled.
| Audit Question | Evidence to Request |
|---|---|
| Are sensitive SharePoint sites identified? | Site inventory. |
| Who owns each site? | Site owner list. |
| Are external sharing settings restricted? | Sharing configuration. |
| Are anonymous links disabled or controlled? | Link policy settings. |
| Are site permissions reviewed? | Site access review. |
Practical tip:
Start with the top 10 sensitive SharePoint sites, such as ISMS, HR, Finance, Legal, customer evidence, executive, security documentation, client project, and audit evidence workspaces.
6. Teams Access and Sharing
Teams can expose files, chats, recordings, and linked SharePoint documents. It is often overlooked during audits.
| Audit Question | Evidence to Request |
|---|---|
| Who can create Teams? | Teams creation policy. |
| Are external users allowed in Teams? | Teams guest setting. |
| Are sensitive Teams reviewed? | Team membership review. |
| Are meeting recordings controlled? | Recording storage settings. |
| Are old Teams archived or removed? | Lifecycle procedure. |
7. Exchange Online and Email Security
Email is still one of the highest-risk systems. Audit should cover access, phishing protection, forwarding, mailbox permissions, and audit logging.
| Audit Question | Evidence to Request |
|---|---|
| Is anti-phishing protection enabled? | Defender policy settings. |
| Are SPF, DKIM, and DMARC configured? | DNS and email authentication records. |
| Are mailbox forwarding rules monitored? | Forwarding rule report. |
| Are shared mailboxes reviewed? | Shared mailbox access review. |
| Are email audit logs retained? | Audit log retention settings. |
8. Audit Logging and Retention
Logs are only useful if they are enabled, retained, protected, and reviewed.
| Audit Question | Evidence to Request |
|---|---|
| Is audit logging enabled? | Audit log setting. |
| Which activities are logged? | Audit configuration. |
| How long are logs retained? | Retention setting. |
| Who can search audit logs? | Role assignment. |
| Are high-risk activities monitored? | Alert policy list. |
Part 3: Cloud Access Internal Audit Questions
Entra ID often controls access to more than Microsoft 365. It may provide SSO to SaaS apps, cloud platforms, support tools, HR systems, finance tools, CI/CD, and security platforms.
9. Enterprise Applications and SSO
| Audit Question | Evidence to Request |
|---|---|
| What applications are connected to Entra ID? | Enterprise app inventory. |
| Which apps handle sensitive data? | App classification. |
| Are app owners assigned? | Owner list. |
| Are users and groups reviewed? | App access review. |
| Is admin consent controlled? | Consent policy settings. |
10. Service Accounts and Non-Human Identities
Service accounts are easy to forget. They may power automations, integrations, scripts, monitoring tools, APIs, and legacy workflows.
| Audit Question | Evidence to Request |
|---|---|
| Are service accounts inventoried? | Service account register. |
| Does each service account have an owner? | Owner field. |
| Are permissions least privilege? | Permission review. |
| Are secrets rotated? | Rotation record. |
| Are service account activities logged? | Log sample. |
Practical rule: Every non-human identity should have a human owner.
11. Device-Based Access
Cloud access is not only about usernames and passwords. The device matters too.
| Audit Question | Evidence to Request |
|---|---|
| Are device compliance rules defined? | Intune or MDM policy. |
| Are unmanaged devices restricted? | Conditional Access setting. |
| Are devices encrypted? | Device compliance report. |
| Are inactive devices removed? | Device cleanup record. |
| Are admin actions restricted to trusted devices? | Conditional Access rule. |
12. Cloud Admin Access Beyond Microsoft
If your company uses AWS, Azure, GCP, GitHub, Datadog, Salesforce, or other SaaS tools, internal audit should test how cloud access is governed outside Microsoft 365 too.
| Audit Question | Evidence to Request |
|---|---|
| Which cloud platforms are in scope? | Cloud system inventory. |
| Is SSO enforced? | SSO configuration. |
| Are local admin accounts limited? | Local account list. |
| Are API keys and tokens managed? | Secrets inventory. |
| Are admin actions logged? | Audit log sample. |
Part 4: Internal Audit Evidence Checklist
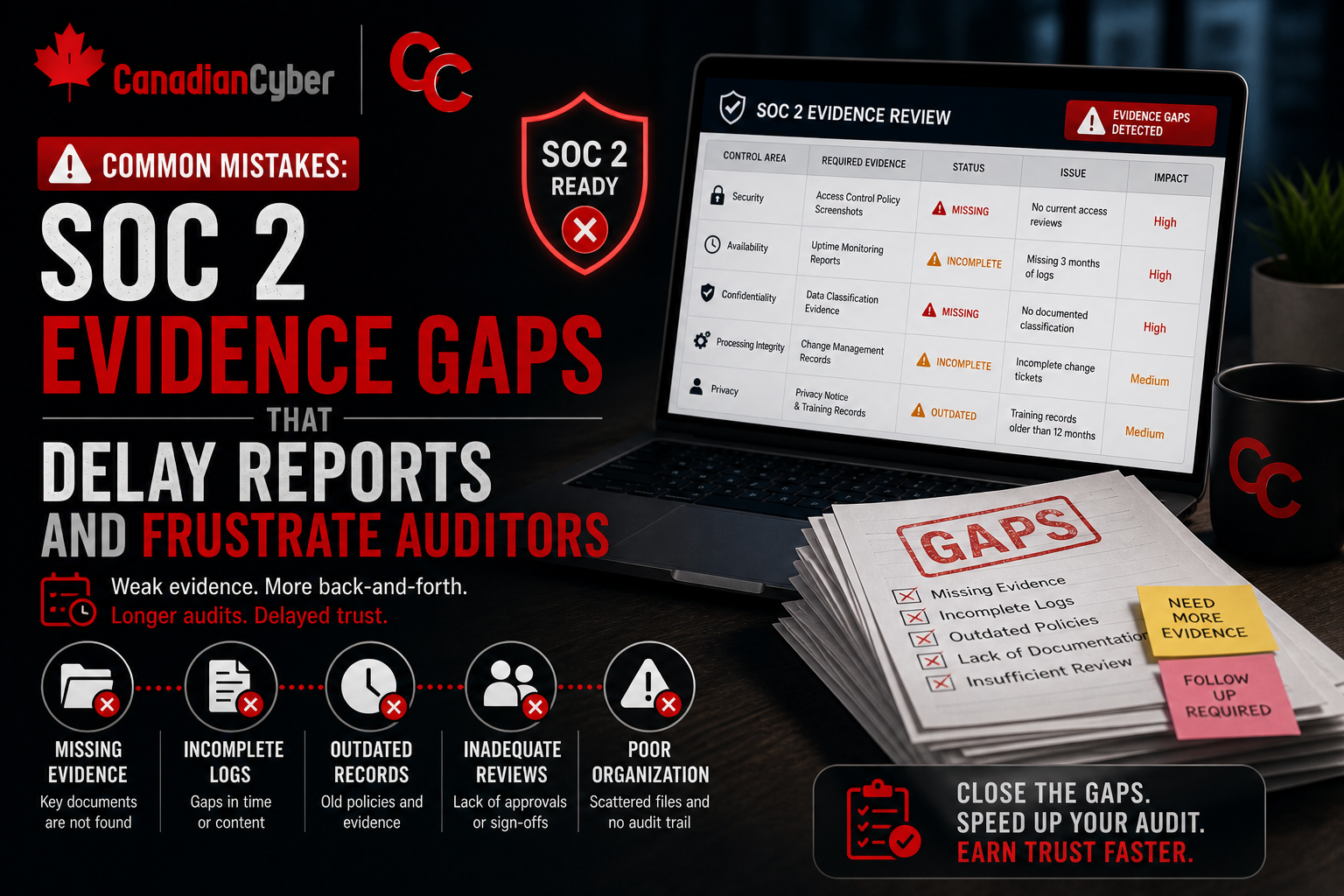
A good internal audit should end with evidence, findings, and corrective actions.
| Evidence Pack | What to Include |
|---|---|
| Entra ID MFA | MFA report, Conditional Access policies, exception records. |
| Privileged Access | Admin role export, PIM evidence, access review. |
| Guest Access | Guest export, guest policy, review record. |
| SharePoint / OneDrive | Site inventory, sharing settings, permission review. |
| Audit Logs | Log settings, retention proof, alert samples. |
| Enterprise Apps | App inventory, owners, app access review. |
| Corrective Actions | Finding log, owners, due dates, closure evidence. |
Finding Register Example
| Finding | Risk | Owner | Priority | Evidence Needed |
|---|---|---|---|---|
| Too many Global Administrators | Excessive privileged access | IT Lead | High | Role reduction and access review. |
| Guest users not reviewed | Former external users may retain access | Site Owners | High | Guest review and removals. |
| SharePoint anonymous links allowed | Sensitive data may be overshared | M365 Admin | High | Sharing policy update. |
| Service accounts lack owners | Unmanaged access risk | IT / DevOps | Medium | Service account register. |
| SaaS apps outside SSO | Offboarding may be incomplete | IT Lead | High | SSO enforcement plan. |
Internal Audit Interview Questions
Use these questions with IT, security, operations, and system owners.
For IT / Microsoft 365 Admins
How do you know MFA is enforced? Who reviews Conditional Access policies? How many Global Administrators exist? How are break-glass accounts protected?
For Security or Compliance
Which Microsoft 365 logs are reviewed? How are risky sign-ins investigated? Where is evidence stored? How are findings tracked?
For SharePoint / Site Owners
Which sites contain sensitive data? Who owns the site? Who can share externally? Are guests still needed? Are permissions reviewed?
For Cloud and SaaS Owners
Which SaaS apps use Entra ID SSO? Which apps still allow local login? Who owns each app? Are API tokens tracked?
Common Mistakes to Avoid
- Mistake 1: Only auditing Microsoft 365 licenses. Licensing does not prove access control. Review permissions, logs, policies, and evidence.
- Mistake 2: Ignoring guest users. Guest access is one of the fastest ways for access risk to grow quietly.
- Mistake 3: Treating MFA as the whole control. MFA matters, but so do Conditional Access, privileged roles, device trust, and monitoring.
- Mistake 4: Not reviewing SharePoint permissions. Sensitive files often live in SharePoint. If site access is messy, the audit will find it.
- Mistake 5: Forgetting service accounts. Non-human identities can carry serious access risk. They need owners, permissions, rotation, and review.
- Mistake 6: Assuming offboarding is complete after disabling email. Offboarding must cover Microsoft 365, Entra ID, SaaS apps, cloud consoles, API tokens, and guest accounts.
- Mistake 7: Collecting logs but not reviewing them. Logs without review are weak evidence. Internal audit should test whether alerts become action.
What Good Looks Like
A strong internal audit can show that:
- MFA is enforced
- Conditional Access is reviewed
- admin roles are limited
- break-glass accounts are controlled
- guest users are reviewed
- sensitive SharePoint sites have owners
- external sharing is controlled
- Teams access is governed
- mail forwarding is monitored
- audit logs are retained
- SaaS apps are inventoried
- service accounts have owners
- findings are tracked to closure
The goal is not to prove every Microsoft setting is perfect. The goal is to prove that access is governed, reviewed, monitored, and improved.
Takeaway
Microsoft 365, Entra ID, and cloud access should be part of every serious internal audit.
- Start with identity.
- Review MFA and Conditional Access.
- Test privileged roles.
- Check guest users.
- Review SharePoint and Teams access.
- Confirm email security.
- Verify audit logging.
- Review enterprise apps and service accounts.
- Extend the review to non-Microsoft cloud systems.
A good internal audit does not just find gaps. It helps reduce access risk before customers, auditors, or incidents expose it.
How Canadian Cyber Can Help
Canadian Cyber helps organizations audit Microsoft 365, Entra ID, SharePoint, Teams, and cloud access controls.
- Microsoft 365 internal audits
- Entra ID access reviews
- Conditional Access reviews
- privileged access reviews
- guest user access reviews
- SharePoint and Teams permission reviews
- cloud access audits
- SaaS application access reviews
- service account reviews
- audit evidence pack design
- SharePoint ISMS evidence workspaces
- vCISO support for access governance
Stay Connected With Canadian Cyber
Follow Canadian Cyber for practical guidance on Microsoft 365 security, Entra ID, ISO 27001, internal audits, cloud access governance, and vCISO support.